- Jamf Nation Community
- Products
- Jamf Pro
- Filevault Config Profile vs Policy
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Filevault Config Profile vs Policy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-06-2022 01:06 PM
What would be the difference between the policy way the configuration profile way? What way do you use it in your environment? Any direction would be appreciated, thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-06-2022 01:13 PM
We still use a policy, only because I need to be able to control when FileVault enablement kicks in during the setup of a new system. Using a profile is a little less precise, though still possible if you set up your Smart Groups correctly. But with a policy and a custom trigger, I can kick it off exactly when I want it to.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-06-2022 02:49 PM
We use a profile. The main reason is it prevents a user from turning off encryption.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-06-2022 03:04 PM
We also use the Profile method, but it also depends on what rev's of macOS/hardware etc you're running...Profile seems to be the best route for Big Sur+ but I think we still have policies for some older setups...would have to look.
Also, some FV2 stuff has been deprecated, so try things and test like crazy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-07-2022 04:01 AM
Policy and profiles since we have older macOS running in environment. I would like to only deploy via Profiles once the devices are updated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-19-2022 10:01 AM
Hey Guys,
Looking through here there seems to be a strong preference for the configuration profile over a policy and I'm curious if someone can go into more detail about why that is. I'm currently using the configuration profile method myself and preventing turning FV2 off also with the config profile. I'm looking at enabling the firewall on all my macs with a configuration profile but I do not want to have Filevault 2 and the Firewall on the same configuration profile, I would like to have them separate.
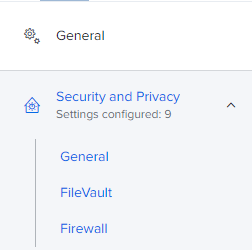
I know you shouldn't have two of the same configuration profile on devices, but the Firewall and FileVault 2 settings are on the Security and Privacy section of the configuration profile template.
I downloaded the configuration profile and I don't see any keys for the Firewall on the Filevault 2 profile, which makes sense as I haven't enabled anything for the Firewall so I should be okay. Is anyone currently deploying a configuration profile for firewall and FileVault 2 like this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-19-2022 10:12 AM
@Levi_ ,
I have mine separated. Just config the piece (FileVault) and not the others. Same for the Firewall Profile.
The thing about this type of question is that if you ask 20 admins, you'll likely get 20 answers. Some answers might be "better" and some might be less good. Do what works for you and is easy to keep running.
I just setup a pair of Profiles just for this - one Firewall, one FileVault. Seems to be working, so if I can provide further info, please ask.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-19-2022 10:35 AM
Thank you @scottb for confirming it does work. One thing I've noticed with the Filevault enablement by configuration profile is if the user does not enable Filevault when prompted at login or logout, it doesn't seem to prompt again. I've been having to remove the profile and reassign it. Have you seen this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2022 10:42 AM - edited 01-19-2022 10:43 AM
Might depend on how it's scoped? I use smart groups and if it's eligible and non-encrypted, it gets the prompt. But yes, I have seen on occasion a Mac not getting FV2 enabled and we have to flush logs or otherwise figure out why...the hard part for a lot of them is just getting them TO reboot! I create a report that shows Macs that have not rebooted in more than 10 days, and send that to the leadership. I'm still surprised at how little folks want to reboot and update the OS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-19-2022 11:09 AM
Right now I am scoping devices individually, yeah. I have more mac's than I want to admit where the administrator account does not have a secure token, just the user of the mac. It has been kind of a nightmare dealing with issues arising because of it especially after demobilizing accounts. These machines I have not enabled filevault yet and won't until I can correct the secure token problem which I have not been able to correct without reinstalling the OS. Once I get the last machines sorted out I am going to be using a smart group.
Users not wanting to restart their machines is something I'll never understand. Especially after they've noticed a significant sluggishness in performance or random application hangs/crashes. Closing the lid is the new shutting down or restarting. *climbs up wall*. What I've done to fight this is run a script once daily against people's machines that checks the uptime and if it exceeds the uptime you set it will notify them to restart their machine.
I'm sure you can set it to an extension attribute and then run a smart group off it to execute on reoccurring check-in for those who have exceeded. Check it out here https://github.com/UoE-macOS/jss/blob/master/coreconfig-restart-reminder
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-19-2022 11:18 AM - edited 01-19-2022 11:26 AM
Yes, all but two of the non-encrypted Macs in one instance have not rebooted since 2021!
I setup a nice little app called "Support.app" which has this info as well as other good stuff. One of my colleagues is using "Nudge" to help with this. I have not tried it yet, but supposed to be pretty good.
Nobody seems to want to get Catholic Nun on users who don't reboot/update, so if they don't care, I have to let it go...
Have a look at it - has some great features and is updated regularly.