We are trying to fine tune our SSO experience on our macOS devices.
Our JAMF Connect application is working fine but we are unable to get SSO working for Safari/Chrome/Edge etc.
We have found the following article:
https://docs.microsoft.com/en-us/azure/active-directory/develop/apple-sso-plugin
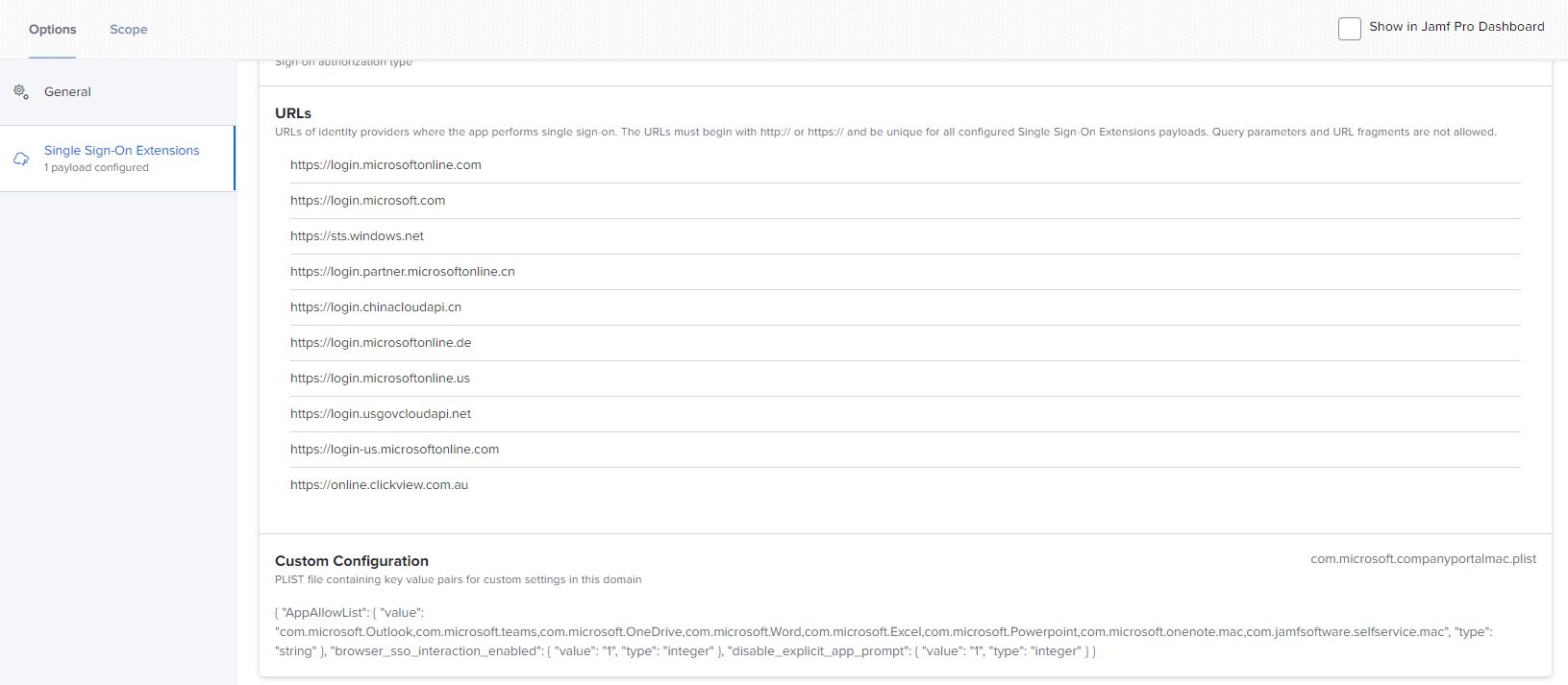
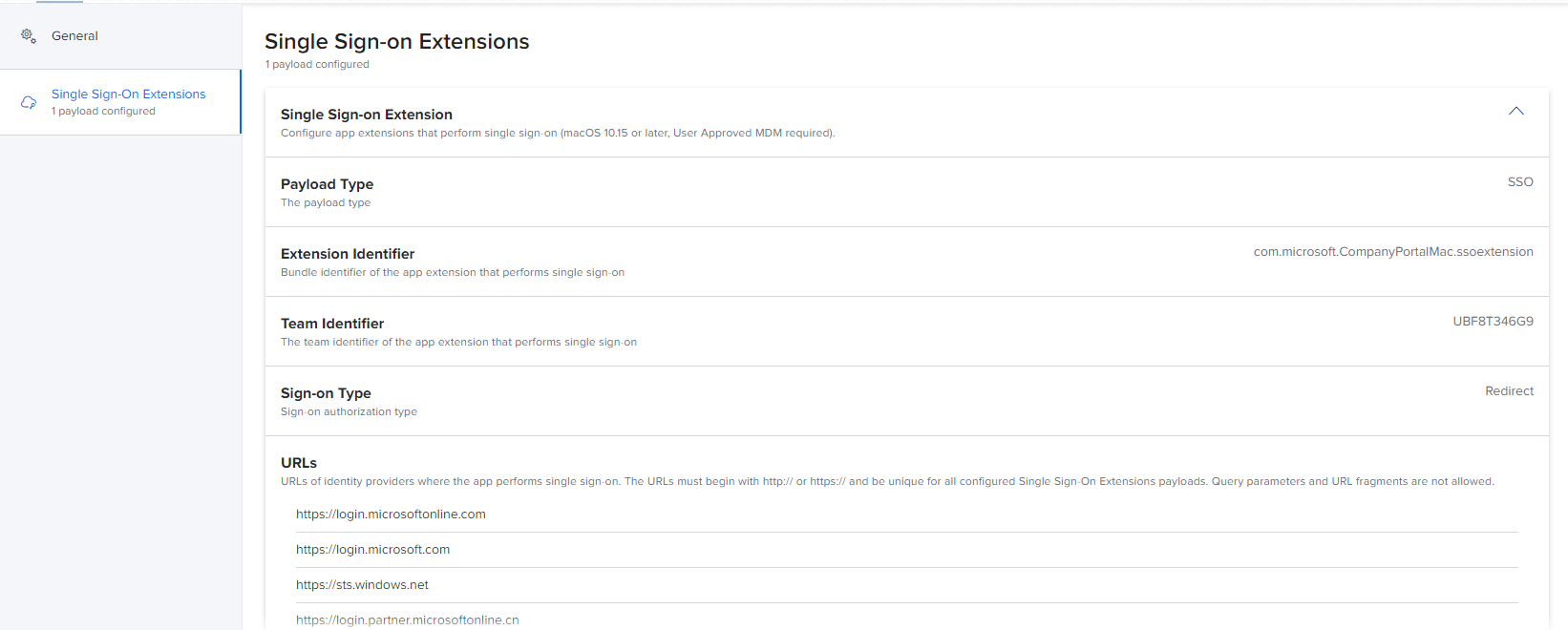
We have installed the Microsoft company portal app on our test device and deployed a Single-Sign On Configuration Profile to the test device and configured it as per Microsoft documentation in the above link.
We are not sure if the required custom configuration is applying correctly as the documentation states we need to add the following key pairs for it to work.
Key: browser_sso_interaction_enabled
Type: Integer
Value: 1 or 0
and
Key: browser_sso_disable_mfa
Type: Integer
Value: 1 or 0
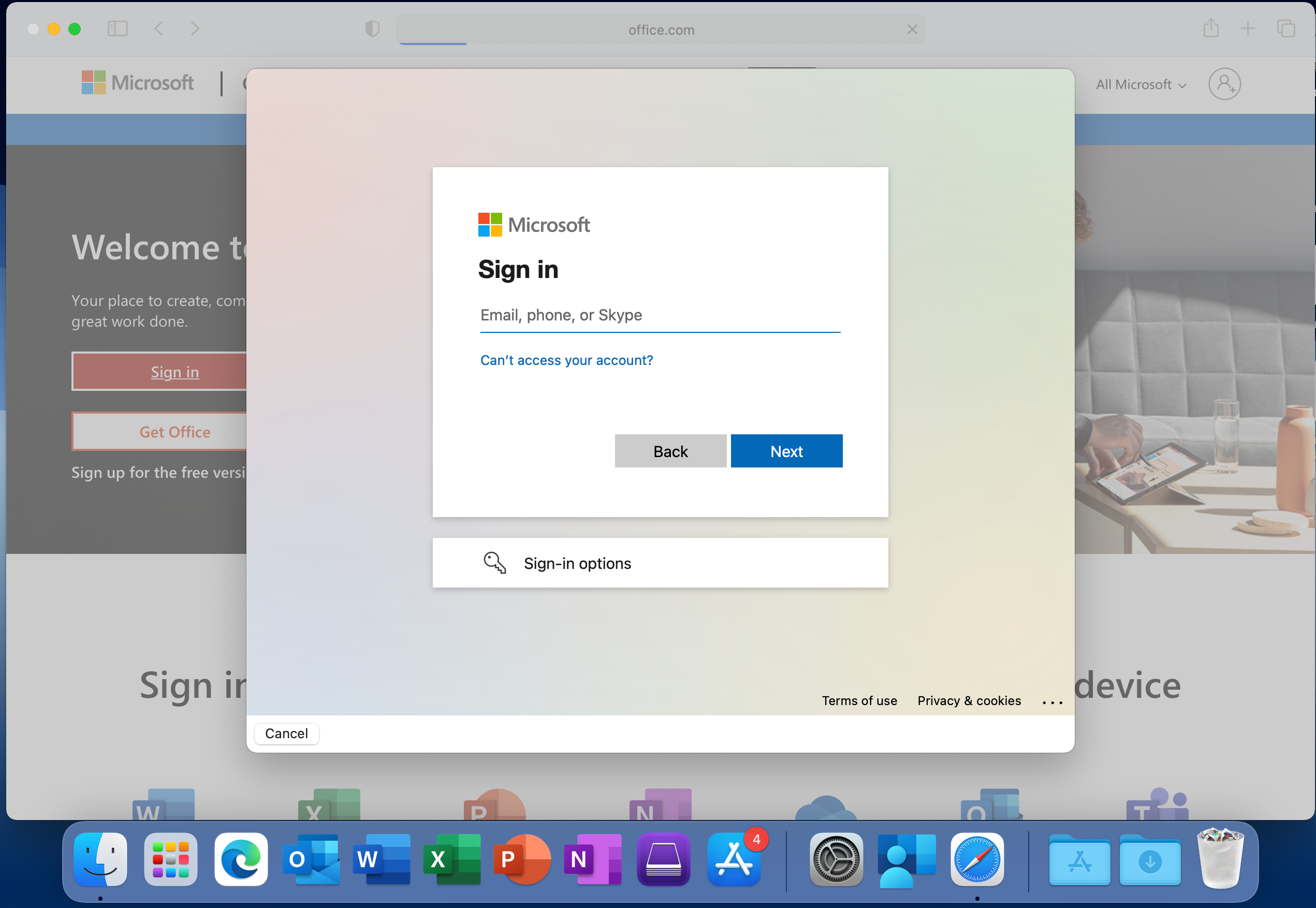
We have done a test on mac which is Intune enrolled only and have used Intune to deploy the Single Sign On config profile and it works a treat.
Opening Safari and going to office.com automatically shows the user signed in and we can simply click on it to log on.
On our JAMF enrolled device we still get prompted for a username and password.
We are using pure Azure AD and not using kerberos.
Any advice or information would be greatly appreciated.