Wanted to share some work I was doing as a proof of concept in preparation for staff working from home and students transitioning to remote learning at my University. This can be adapted to any organisation and I'd love to hear what others are doing to empower their users and help them gain access to software and services.
With Jamf's announcement to provide extra licensing at no cost, you could do this now and not have to worry about seeking financial approval for more licences. Some of us are about to ask 1000’s of users to start using their own devices without knowing what kind of state they are in. Self Service is a great tool to help IT and users through this period.
What I wanted to achieve:
- Onboard users quickly with access to software, knowledge and training.
- Address issues relating to unsupported macOS versions and software behind in patching.
- A mechanism to publish updates and notifications to new software as they became available
- Reduce tickets to my service desk for common software requests and setup.
- Identify personal machines for easy removal from Jamf later on.
The changes i made:
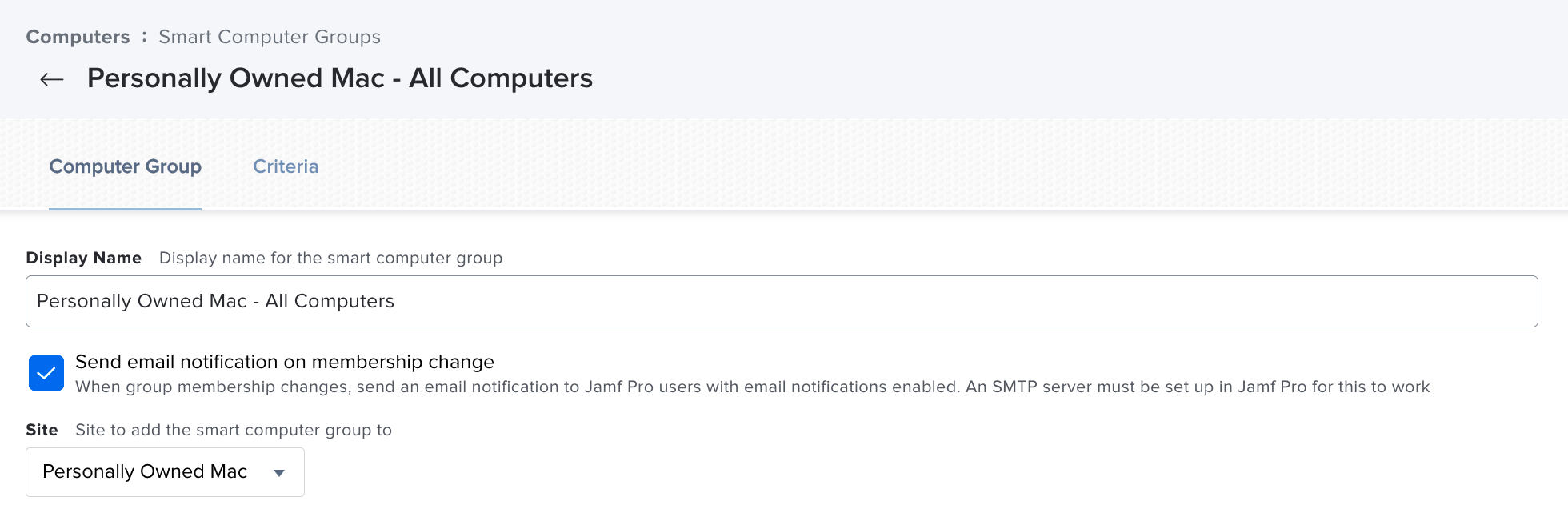
- Made two Sites - University Owned and Personally Owned Macs
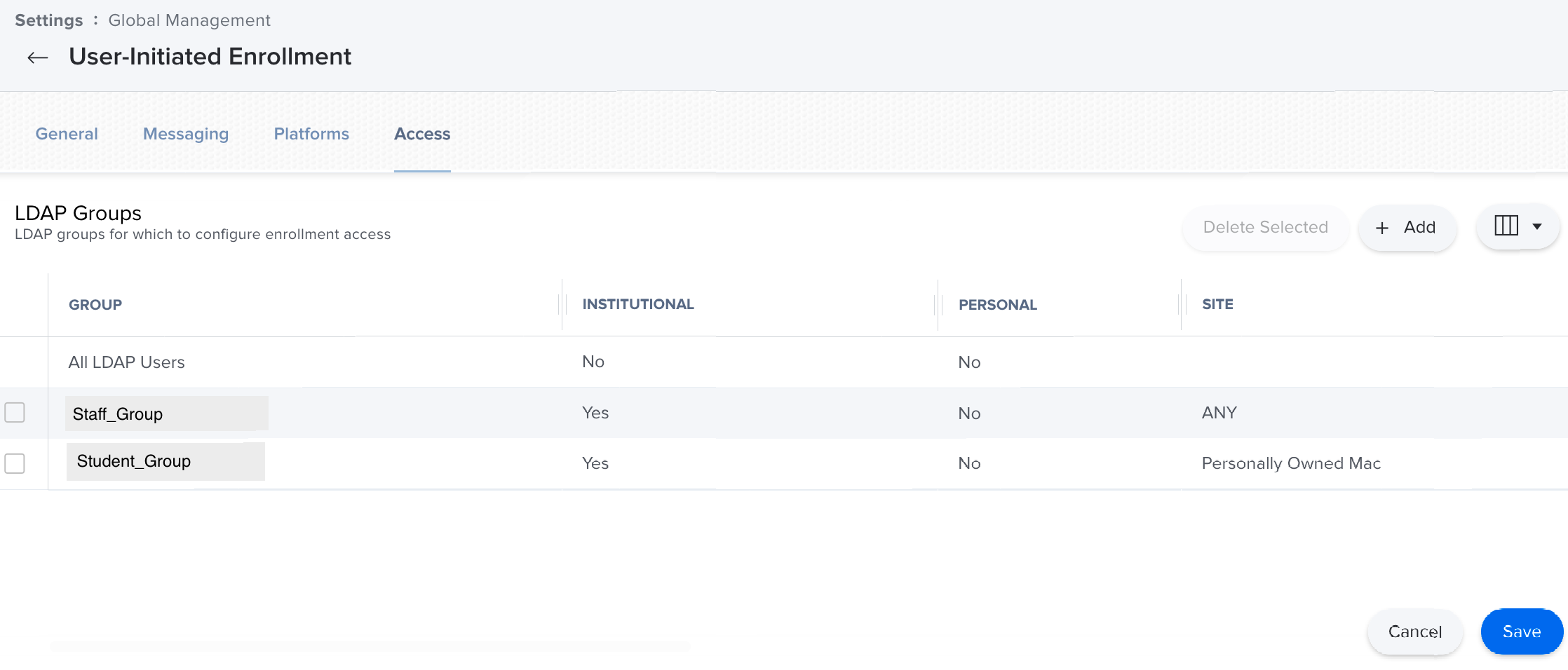
- User-Initiated Enrollment - Defined my Staff LDAP group to choose any Site. My Student LDAP group to enrol in Personally Owned Macs.
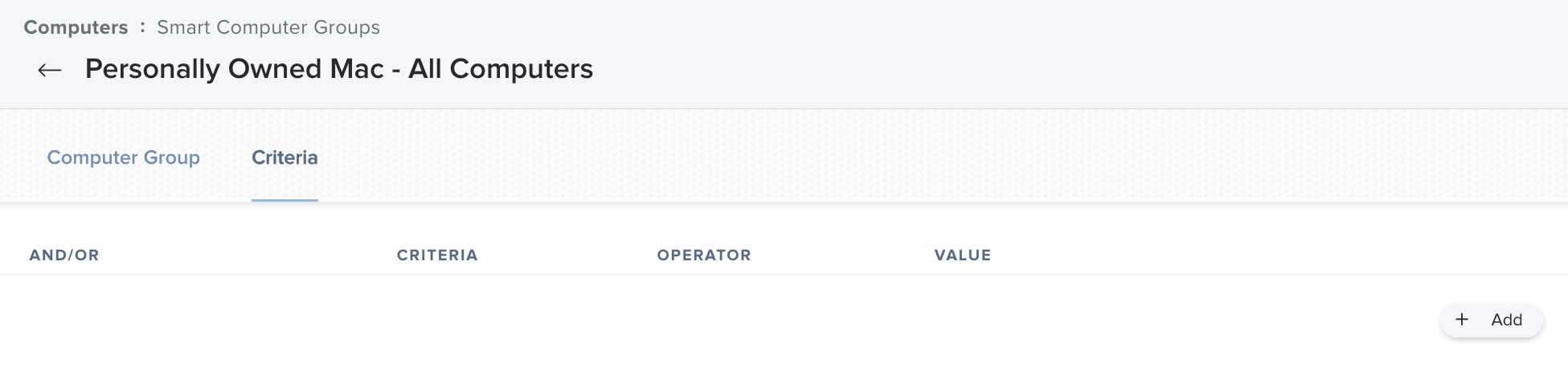
- One Smart Group - Site is Personally Owned Macs, no criteria. All machines enrolled to that option will be used for Scoping policies.
- Policy Exclusions - I reviewed each policy that had a software licence or action not applicable to personal machines, and excluded it using the Smart Group.
Video of enrollment process here.
I haven't communicated this as being available, but i've already had 8 people enrol Personal devices. I interviewed 2 of them today and got some great feedback, here is how it’s going so far:
- Our automatic patching updated browsers and other at risk software.
- One user reported that installing software fixed an issue our Helpdesk were having issues troubleshooting.
- One user had to borrow their parents iMac and found Self Service easy to use and got setup with our working-from-home apps quickly.
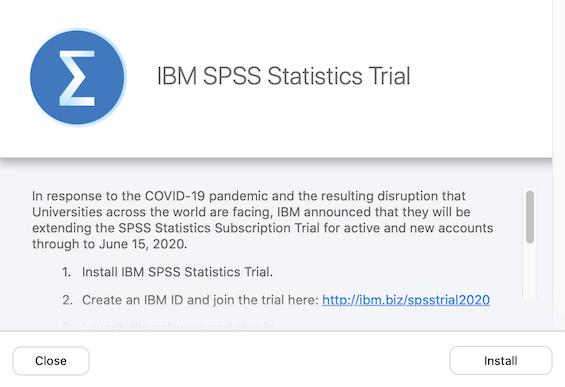
- We have already packaged and made available vendor supported extended trials for two software titles and advertised them to Personally Owned Macs.
If you have other workflows, suggestions or things to share to help other admins, please feel free to share. Cheers!