Hi Jamf Nation,
On June 15, 2021, we were made aware of a URL redirect vulnerability, affecting Jamf Pro customers who host their environments on-premises and less than 1% of Jamf Cloud customer environments. We have not discovered any evidence of malicious use of the vulnerability.
CVE-2021-35037 has been reserved. Additional technical details will be included in the CVE once our on premises customers have had a reasonable interval to patch.
The vulnerability allows for arbitrary URL redirection using a very specifically-formatted Jamf Pro URL. This is assessed to be a CVSS 6-7 (medium - high) severity issue affecting Jamf Pro versions: 10.30 and earlier
We have pushed out a configuration change to all affected Jamf Cloud customers to address the vulnerability. No further action is required from these customers. For Jamf Pro customers who host their environments on-premises, Jamf Pro 10.30.1 has been made available and a notification has been sent to these customers. We strongly recommend they upgrade their environment to Jamf Pro 10.30.1 as soon as possible. No other customers are affected by this vulnerability. If you have any questions, please reach out to Customer Success for more assistance or post a comment here. We will update this post with information as it becomes available.
How is the vulnerability exploited?
An attacker may craft a URL that appears to be for a customer's Jamf Pro instance, but when clicked will forward a user to an arbitrary URL that may be malicious. This is commonly used as part of a phishing campaign.
What is the potential impact of the vulnerability?
Your users may trust a URL due to the Jamf Pro context and provide an attacker with information, access or even install malware.
If your Jamf Pro instance uses https to communicate, note that any malicious URL being redirected to that does not have a valid certificate would result in warnings from common browsers to any users that may click an exploited URL.
Is it remotely exploitable?
An attacker can craft an exploited URL without any connection to your devices or services. They only need to have the URL to your Jamf Pro instance. Victims are exploitable if they can reach a Jamf Pro server and are presented with this malicious URL.
Does a device have to be enrolled in Jamf to be vulnerable?
Since the attacker only leverages a Jamf Pro instance as an intermediary to trick a user into visiting a malicious URL, the user and device do not have to be enrolled or associated with Jamf in any way. As long as the user has access to the Jamf Pro instance and clicks the exploited URL, they are vulnerable.
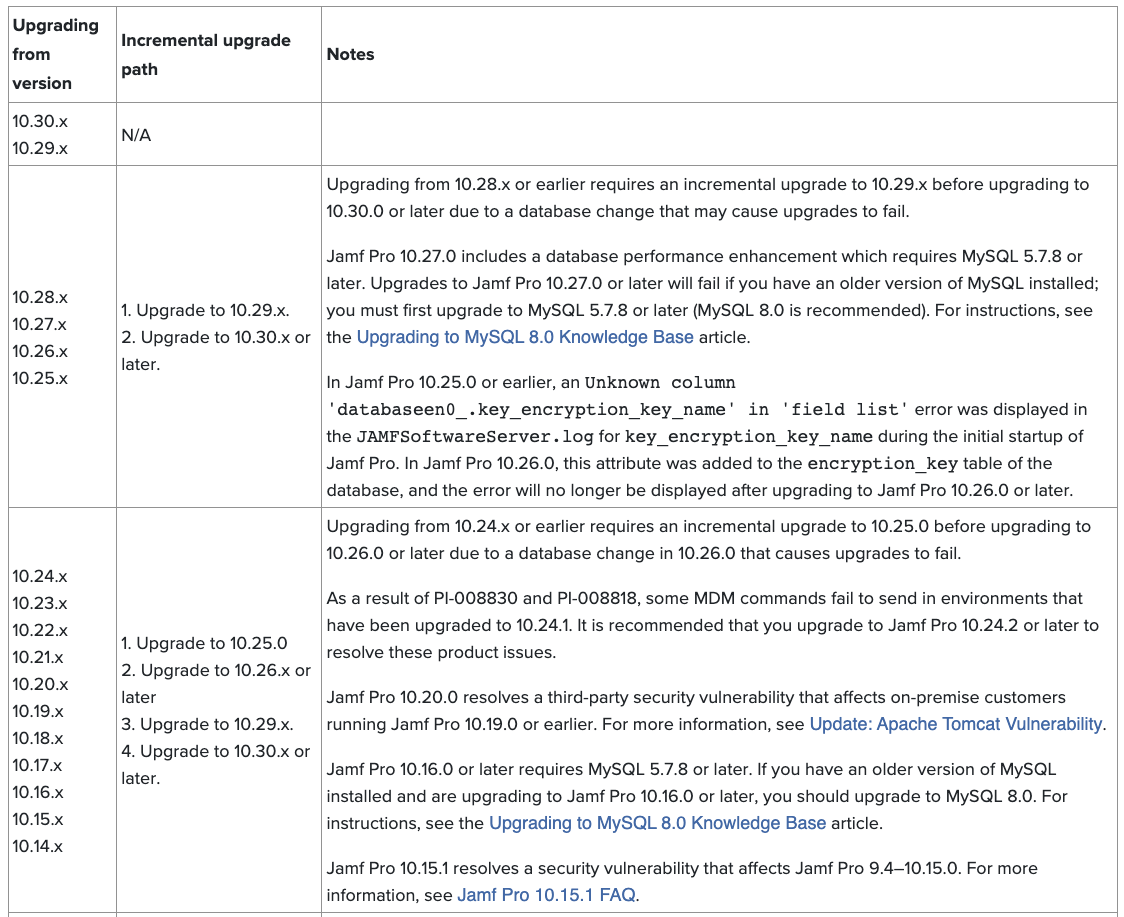
Important Notice: Upgrading from 10.28.x or earlier requires an incremental upgrade to 10.29.x before upgrading to 10.30.0 or later. Please reference this document on incremental-upgrade-scenarios for more details
We apologize that some customers experienced an issue accessing Jamf Account subpages. As of 9 am CST, June 21, this issue has been resolved and everyone should have access to all Jamf Account pages.
Aaron Kiemele
Chief Information Security Officer, Jamf