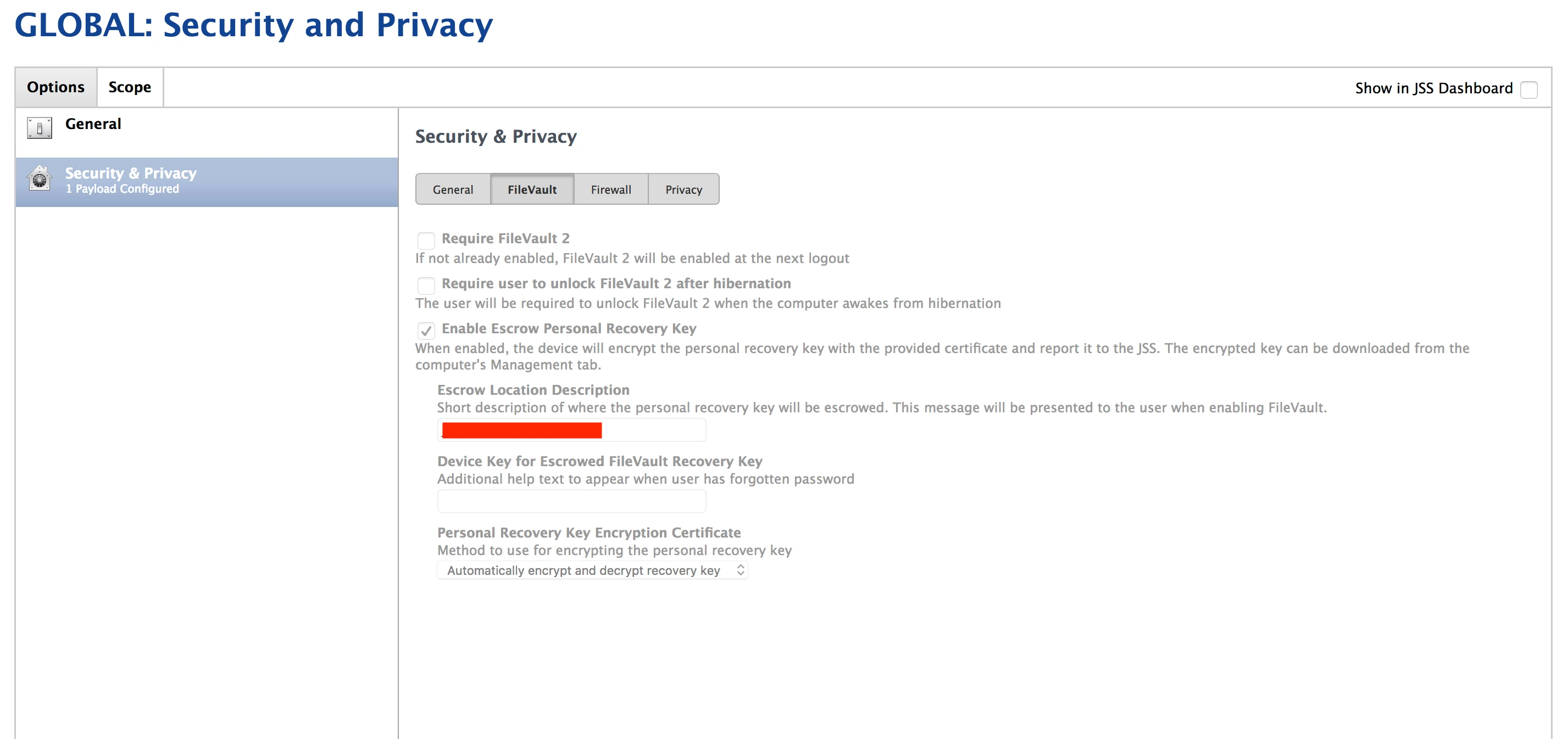
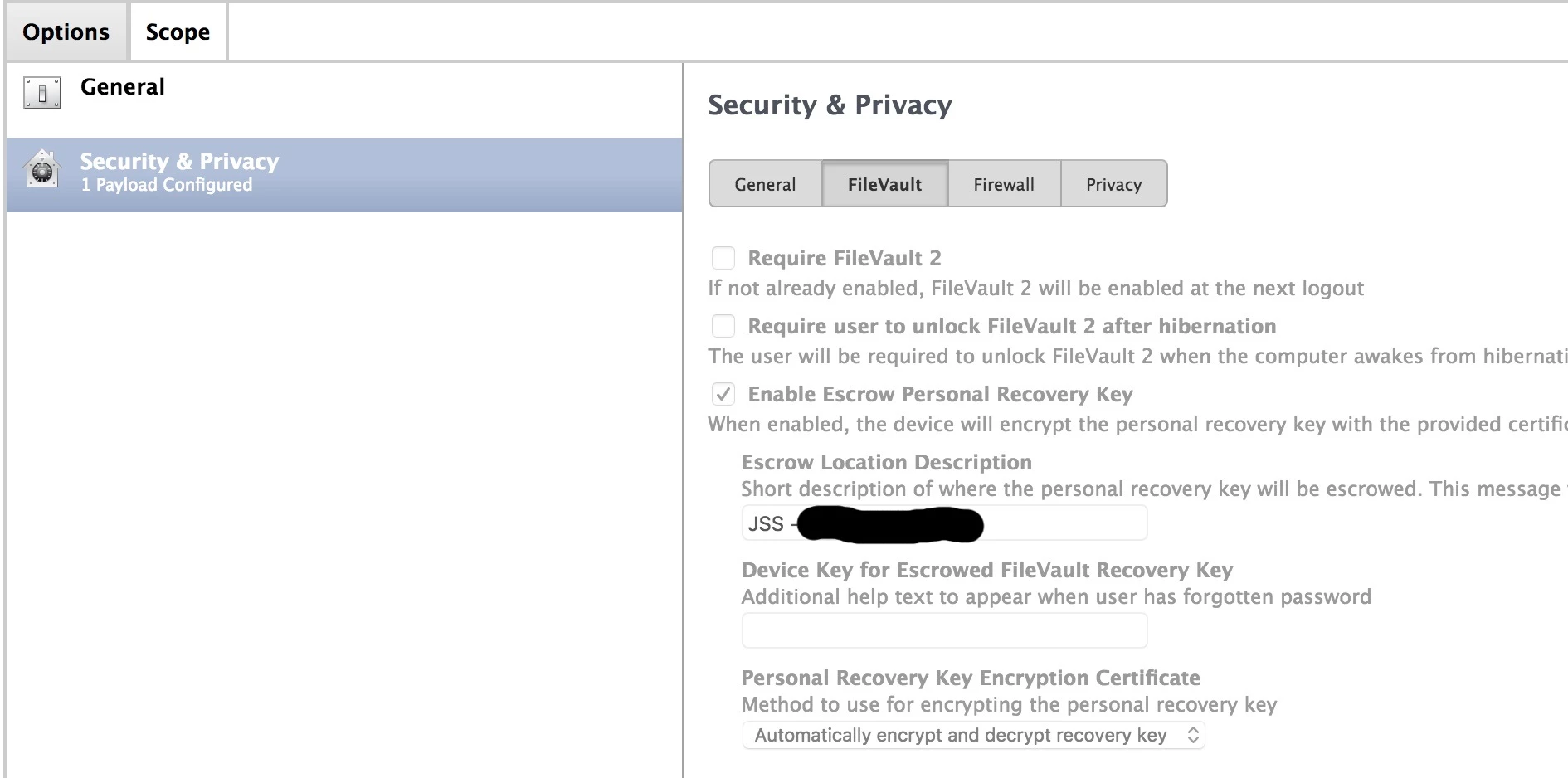
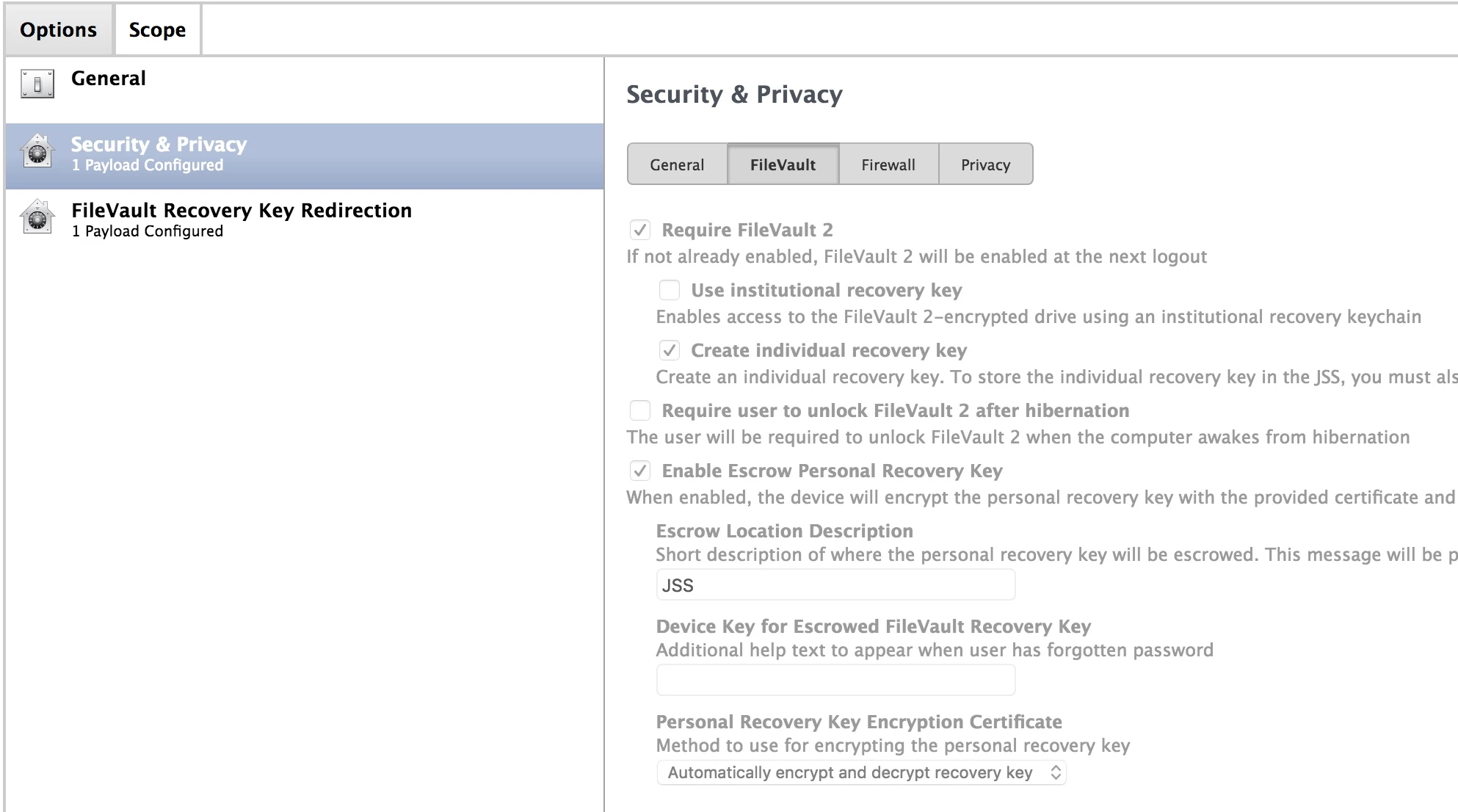
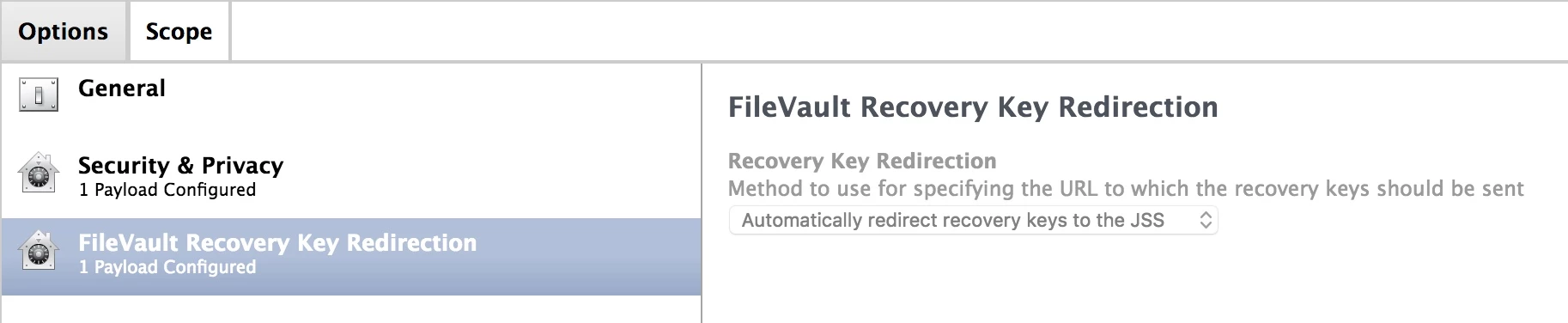
Has anyone found documentation for the new "Enable Escrow Personal Recovery Key" option in JSS 9.101.0 in order to support Recovery Key escrow in macOS 10.13 High Sierra? It looks like Jamf hasn't updated the documentation to report best practices for the "Escrow Location Description" or "Device Key for Escrowed FileVault Recovery Key" variables:
Question
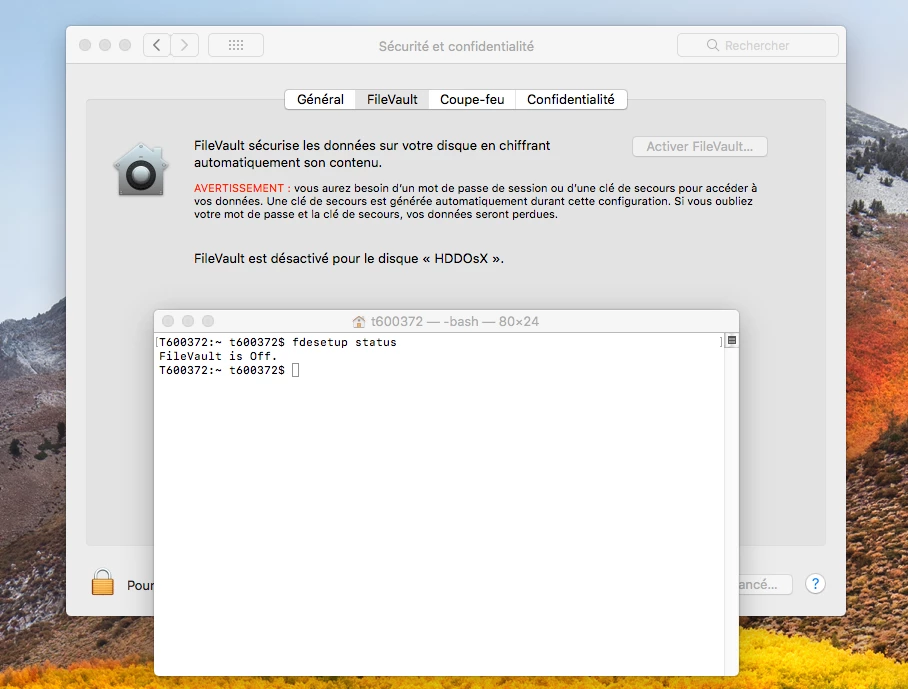
macOS 10.13 High Sierra and Filevault Recovery Key Escrow in JSS 9.101.0
 +8
+8Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.