Just to share the chaos caused by the Security Update 2019-001 (Mojave) released by Apple on the 29th. Once it is installed, the OS build is 18G1012.
We've had a number of machines basically bricked as a result of installing this update. There are others reporting the same problem on Slack. It is likely the direct cause is the user/network interruption during the installation.
This is what we see on our affected machines. When they start we only see our generic support local admin account login but the usual password is not working. These machines are all relatively new with the T2 security chip and default start security setting that stops the machine from external disk booting. I saw people reporting on Slack that the machines with T1 chip are also affected.
So we boot into the recovery mode and found out the disk utility couldn't mount the volume container. In the end, we had to start into internet recovery mode, reinitialise the disk to rebuild the OS. This is a bit stuff-up from Apple as this OS update together with their new OS security protection features is the cause of potential data loss at the user's end.
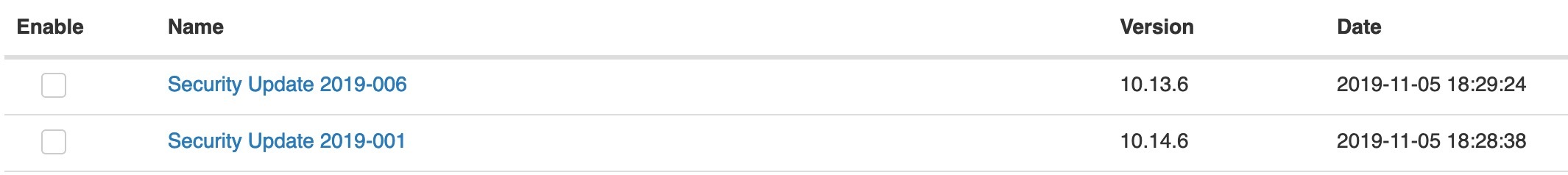
Currently, we've deployed the policy for 10.14 machines not already on this built to ignore the Security Update 2019-001. It could be an overreaction. I probably should only target the 10.14 machines with T1 or T2 chip.