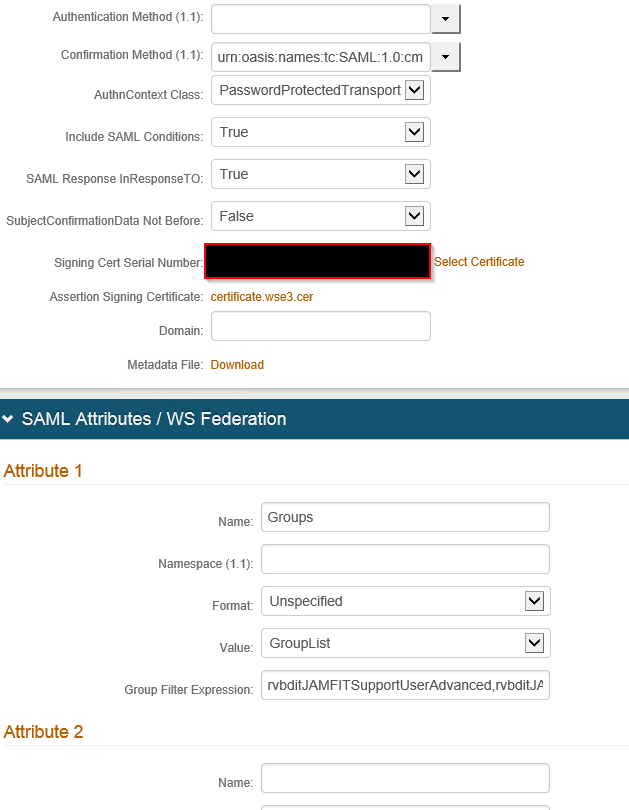
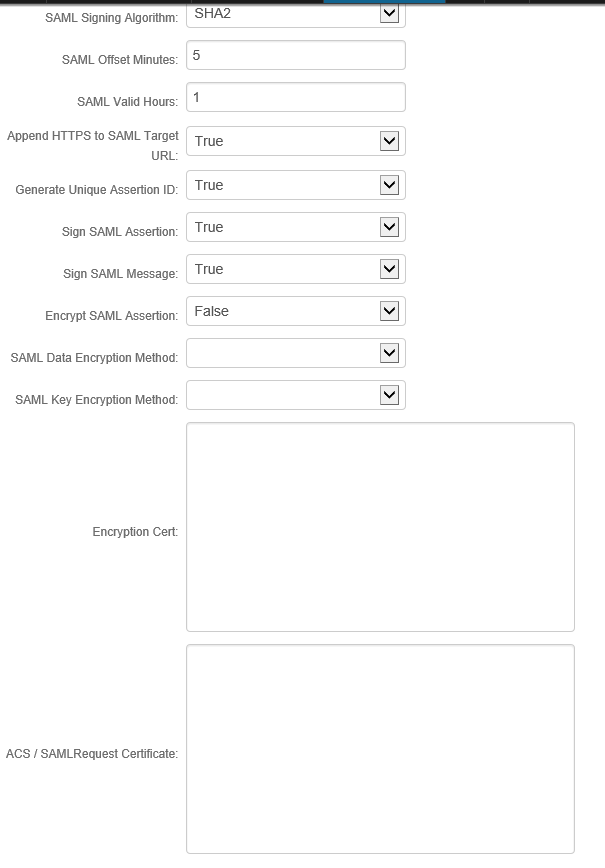
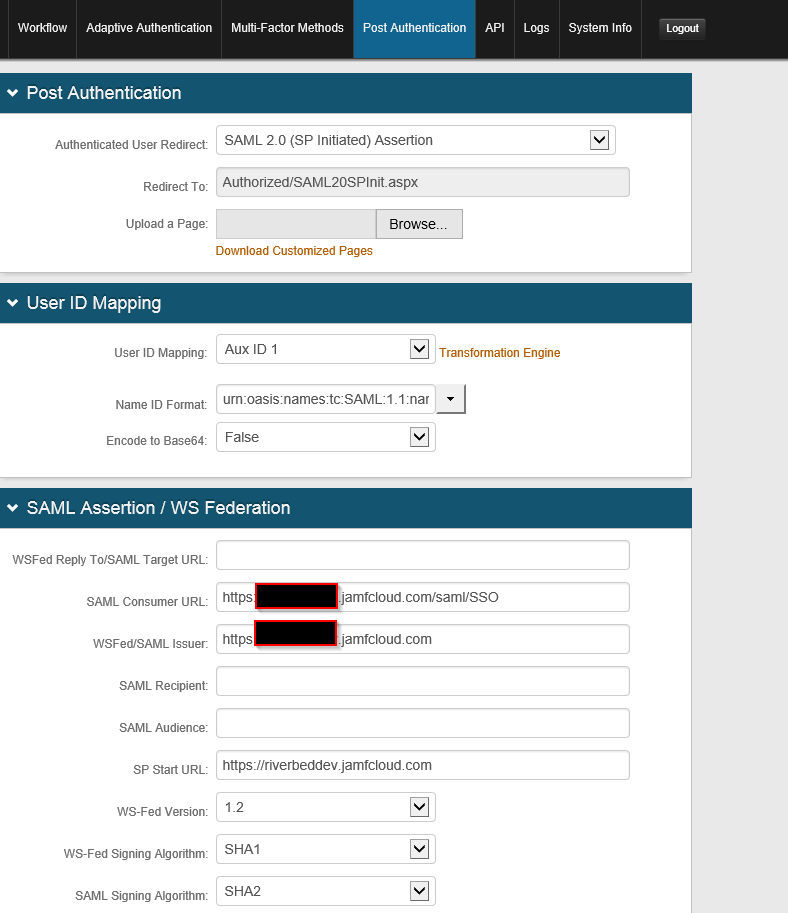
Anyone have any luck with SecureAuth SSO integration with their Jamf Pro Software Server? I am not our SecureAuth engineer but I have been advised that they followed the Ping Identity (https://www.jamf.com/jamf-nation/articles/439/configuring-single-sign-on-with-ping-identity) guide for configuring SecureAuth as closely as they could and then I took care of the JSS side. When enabled, I am getting SSO error when hitting our instance. Here is the log information-
Caused by: org.opensaml.common.SAMLException: Response doesn't have any valid assertion which would pass subject validation
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:229)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 46 more
Caused by: org.opensaml.common.SAMLException: Assertion invalidated by subject confirmation - can't be confirmed by the bearer method
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.verifySubject(WebSSOProfileConsumerImpl.java:400)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.verifyAssertion(WebSSOProfileConsumerImpl.java:296)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:214)
... 47 more
Would be willing to start from scratch if anyone has had luck setting up SecureAuth with JSS. TIA!