I asked this same question on the Clearpass forum, in case there are more people there that are doing similar things, but I'm hoping for someone with the conceptual understanding to just give me a nudge in the right direction regarding this setup.
We have been using 802.1x with Machine certificates issued by AD, with ClearPass and Windows machines for a couple years now. I understand the process that the windows machine joins the domain, get's a certificate, and then our clearpass servers are domain joined and can authenticate the machine with Active Directory using some of our various AD servers. All of that works well, and makes sense to me.
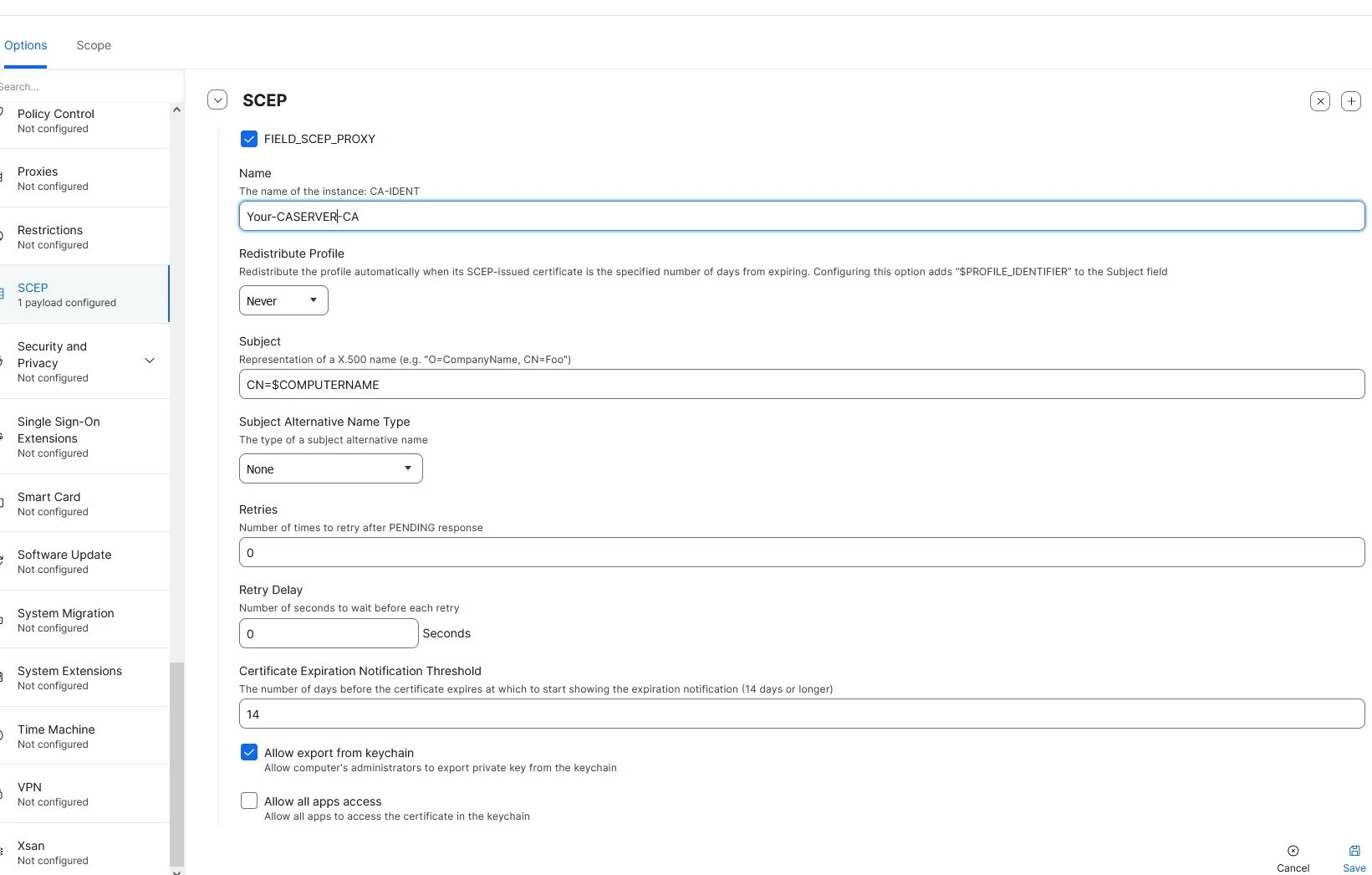
Now we're extending it to macbooks and adding Jamf, so that we can also set up certificates on the macbooks (they will not be domain joined) via SCEP/NDES integrated with our windows CA, with the goal of them also doing 802.1x with EAP-TLS.
So far, we have the SCEP process working fine, and the macbooks obtain their certificates from our CA via SCEP.
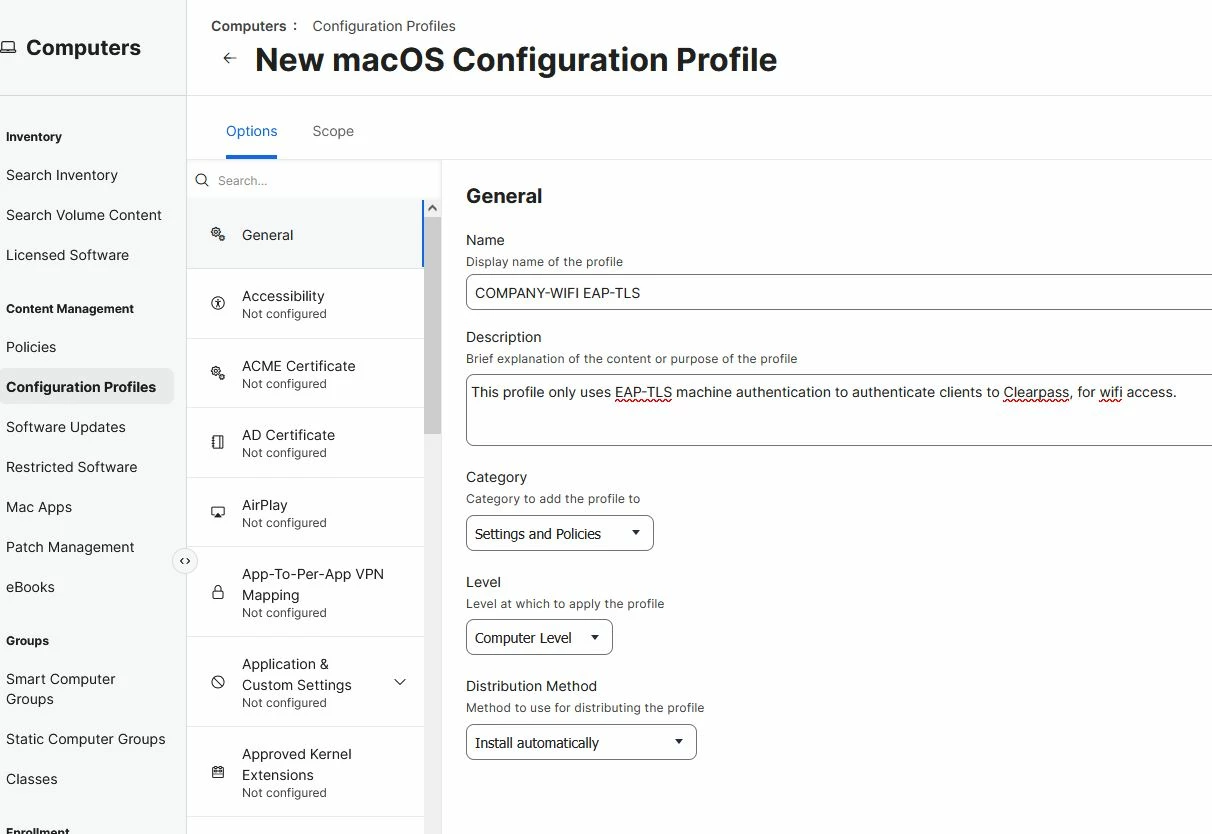
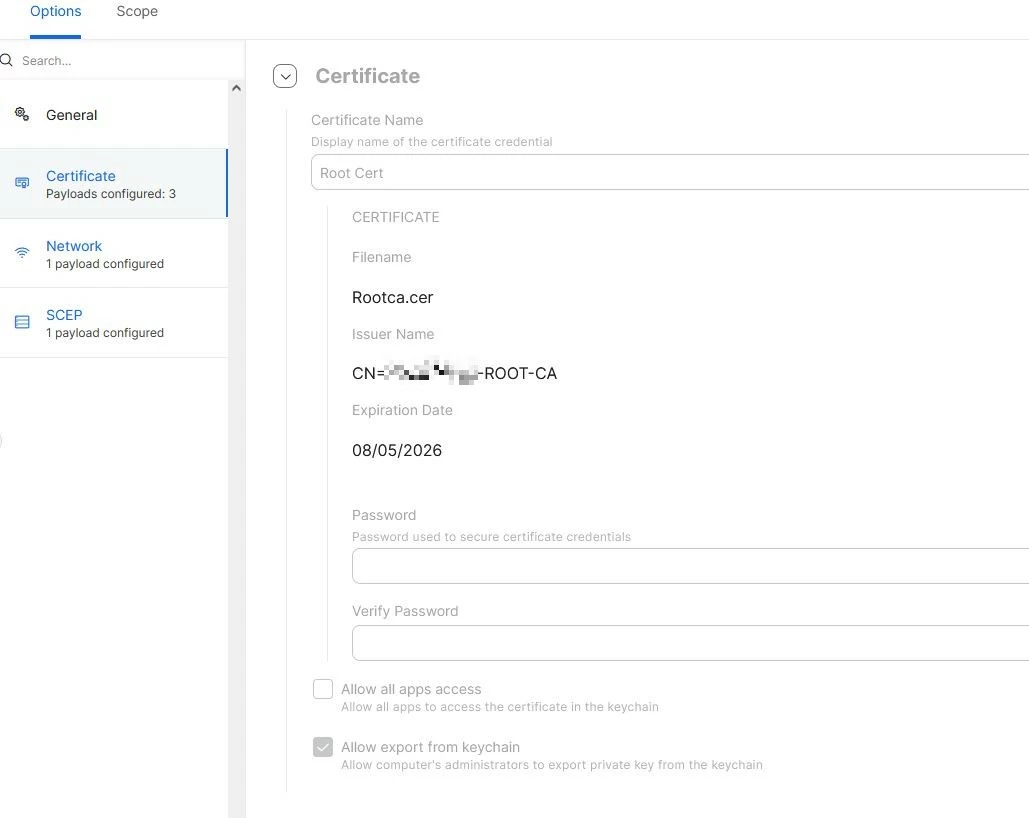
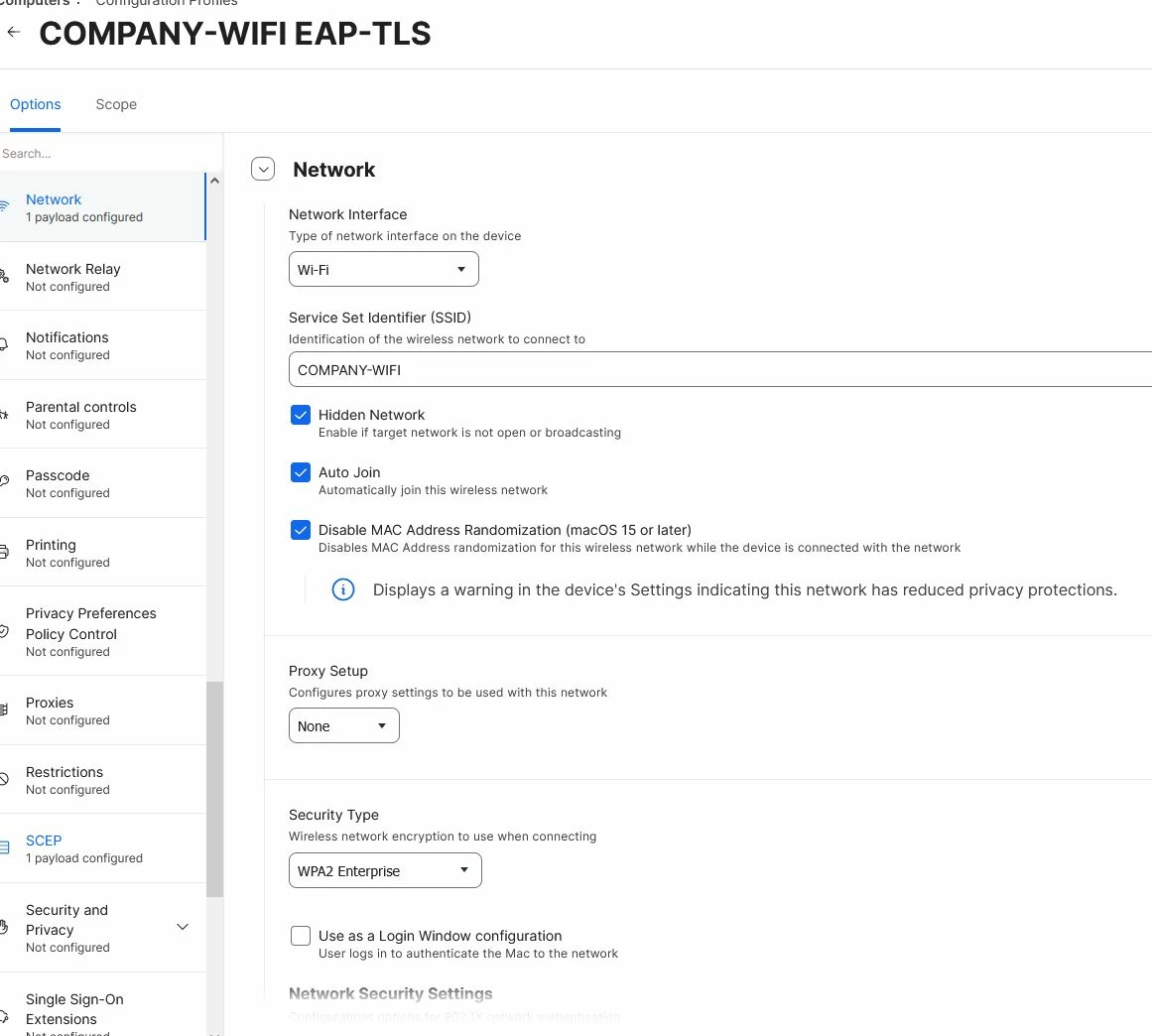
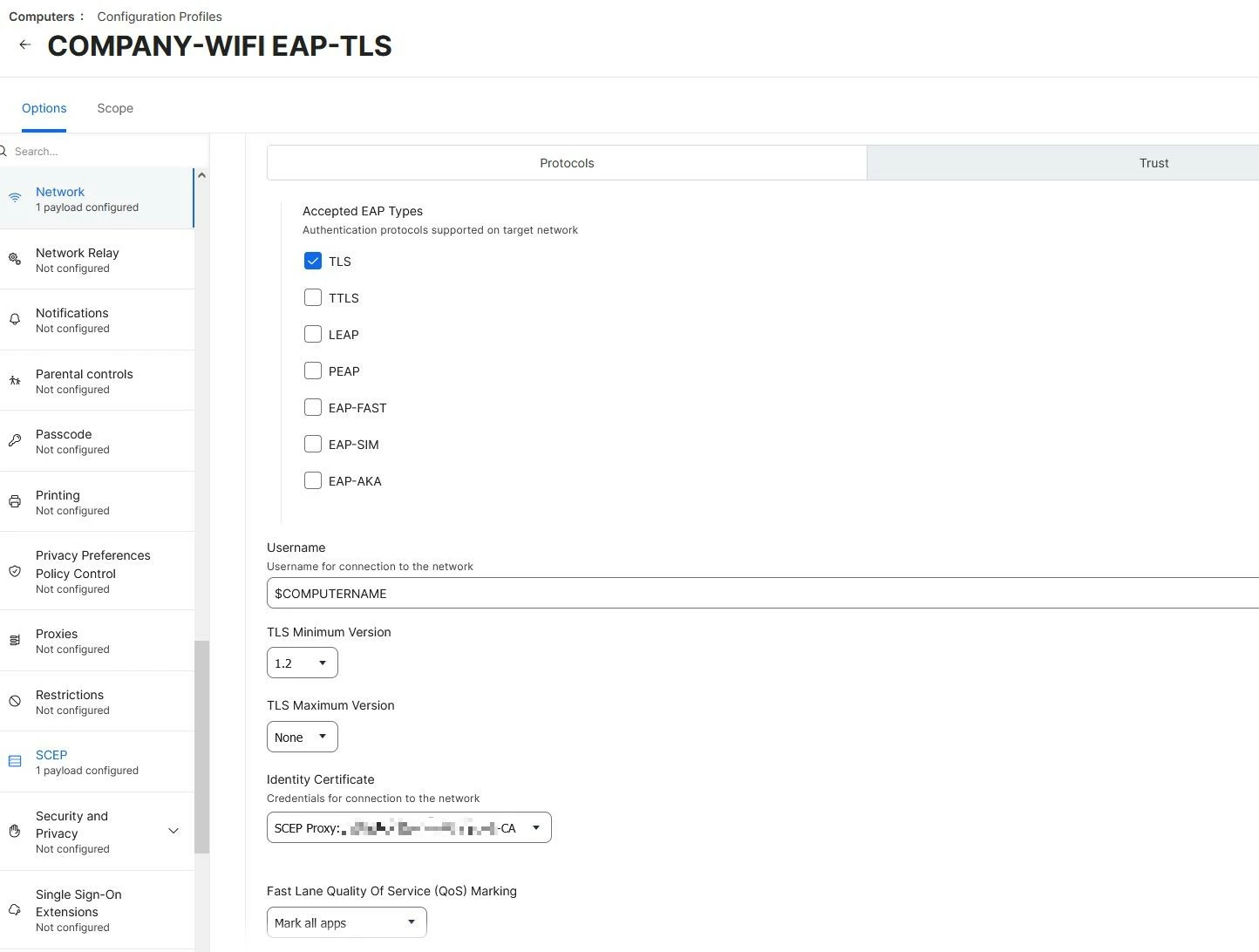
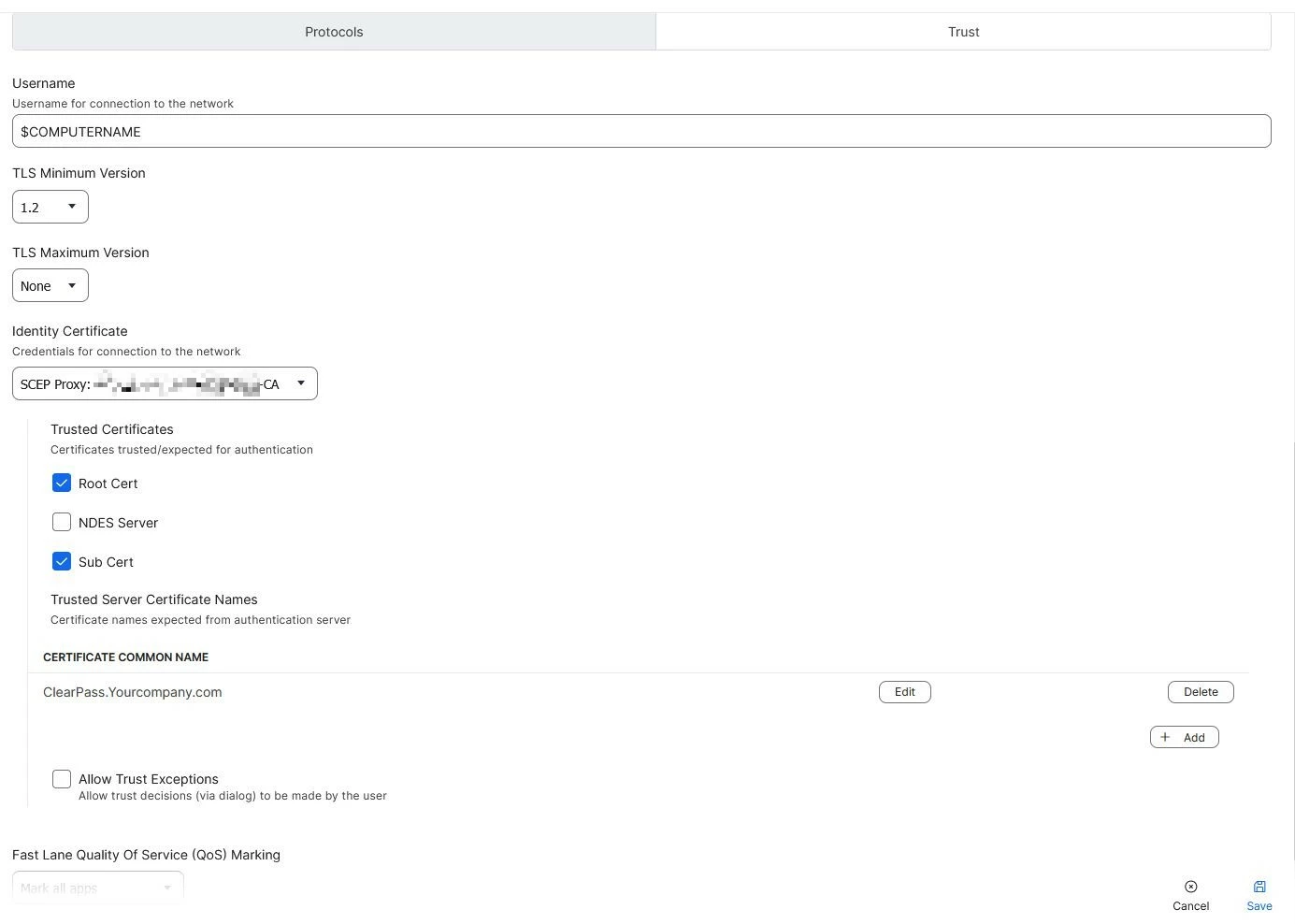
We also created a configuration profile in Jamf for our wifi network that has 1 SCEP payload, 1 Network payload, and not knowing which certs we needed, we our certificate payloads are currently our root, our NDES server, one called Sub Cert that I think is our root again (at the suggestion of Jamf), And then I added our ClearPass server certificate for RADIUS/EAP, and also just in case, the ClearPass RADSEC certificate. I'm not sure if all that is needed or if some aren't. In the network payload, I have our SCEP Proxy as the identity certificate. For "username" field, I have $COMPUTERNAME so that when it hits clearpass I see the computer name. Then on the trust tab, I have the "Trusted Server Certificates Name" set with our Clearpass certificate CN. I'm not really sure if all of this is proper, but, we did go from getting timeouts in the activity monitor on clearpass, to rejected authentications.
Now here's where my knowledge is falling real short and I need the guidance the most:
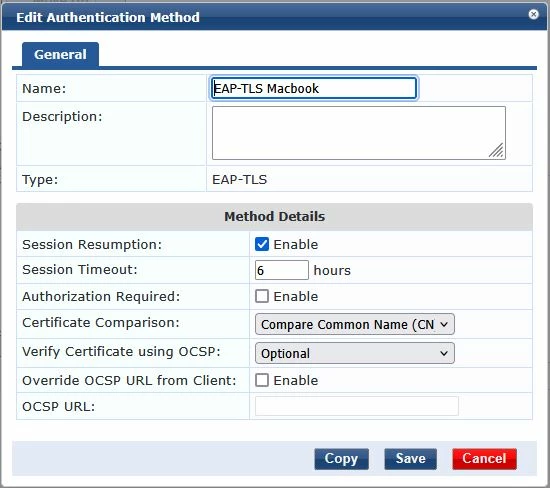
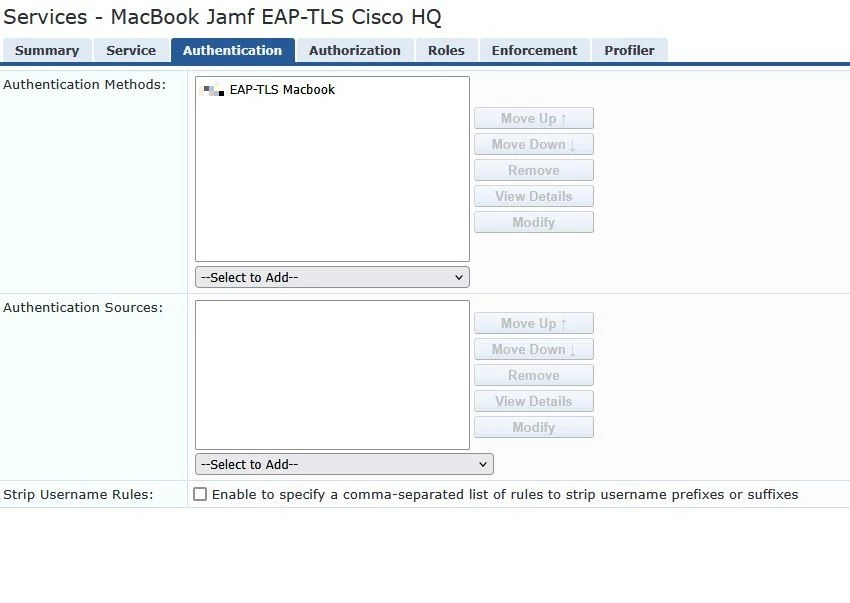
On the Clearpass side, our normal windows machines basically authenticate with an authentication method of "EAP-TLS", and the authentication sources are 3 of or domain controllers, and clearpass is joined to them in AD. That all makes sense.
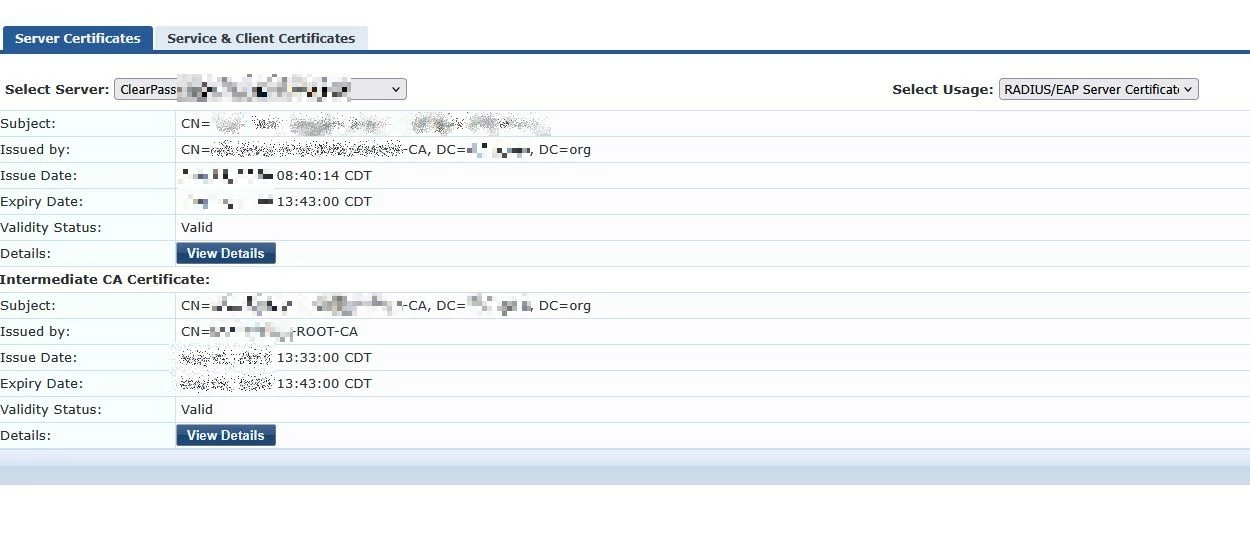
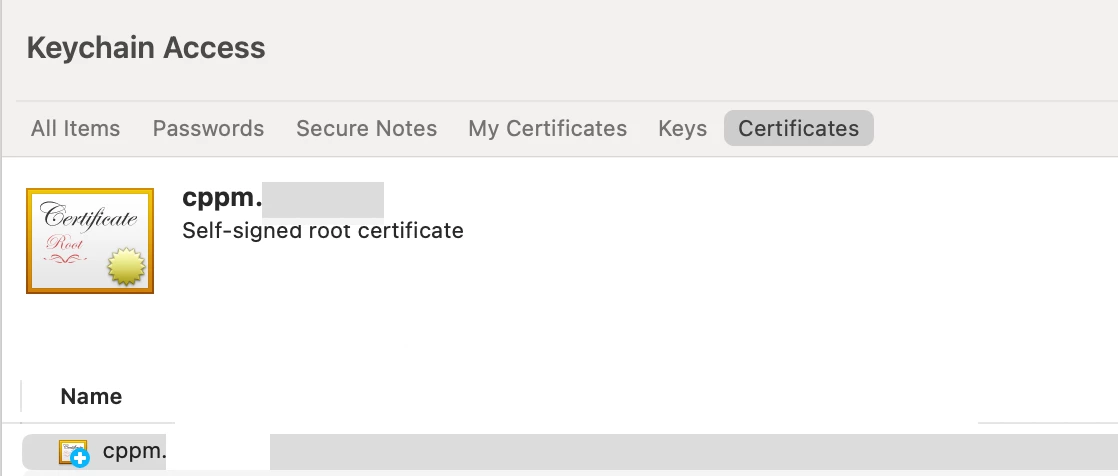
But, when authenticating these Macbooks, I get failures because it can't authenticate via the domain controllers. That makes sense, because as far as I know, although our certificates are issued to the macbooks by our windows CA, since the macbooks aren't domain joined, it's not like our AD servers will HAVE knowledge of our certificates that get presented by the macbooks. So I'm trying to understand exactly what the Clearpass would look like, to do this authentication. Do I need to perhaps import our NDES cert into clearpass? I can see that being a possibility but then what would my "authentication source" be? It would have to be local somehow then, right? Or, am I supposed to be trying to get these non-domain macbooks' certificates somehow into AD so that when we bounce the auth off of our AD servers, it knows how to do that?
We're currently on 6.9.13, and are in the middle of renewal of our support contract. Once that's done, we'll be upgrading to 6.11, and at that point we can probably install the Jamf Clearpass connector, but I don't know if that's a required feature, or just gives some nice abilities.
Can anyone paint me a picture of what I'm really looking to do, on the Clearpass side, to get these authentications working, given the above? If I knew the concept well enough, I think I could move forward and maybe have some luck, but right now the clouds are just too thick to see what I'm looking to do.
Thanks for any guidance you can provide.