I have recently worked with a team to deploy a new NAC solution in our company. We are using ForeScout's CounterACT. http://goo.gl/Og4iEv
One thing that CounterACT has noticed is that many of my Macs will randomly scan other Macs for port 3283 (ARD). They do this across subnets/VLANs (i.e. this doesn't appear to be part of a Bonjour localized discovery process, etc). No other ports/services appear to be sniffed (SSH, AFP, etc)
I have asked the owners of these specific Macs if they are using Screen Sharing/ARD/VNC/ etc but they are not.
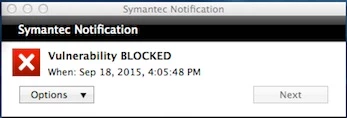
Most of my Macs have the OS X ALF firewall enabled. Most of the time incoming traffic is blocked except ICMP, ARD & SSH.
We use ARD here in IT for the usual tasks of running remote UNIX scripts, deploying packages, etc.
All of my Macs have ARD enabled for basically everything except Observe and Control. My IT Dept standardized on the cross-platform commercial tool TeamViewer when remote assistance is needed)
If I understand the behavior of ARD...
TCP & UDP port 5900 is used for screen Observe & control (VNC)
TCP & UDP port 3283 is for functions such as installing packages, scripts, getting reports, etc.
TCP port 22 is used for encrypted file transfers (SSH tunnel)
Im wondering why some of my Macs are sniffing around port 3283 for (seemingly) no apparent reason. Im going to do a deeper dive and start looking at each host in the CounterACT logs to determine a pattern, etc.
Any thoughts on this behavior?