Hello,
PROBLEM: most of our MBP pop solely use wireless network and are never getting alerted when PW is about to expire.
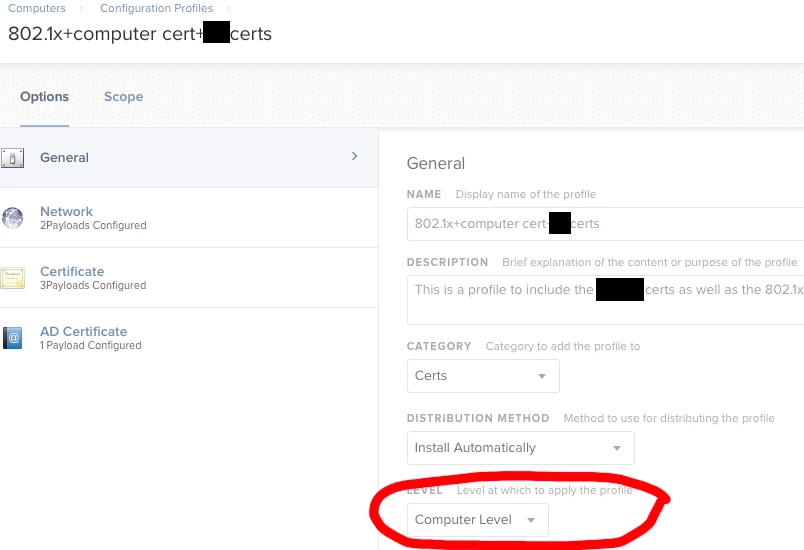
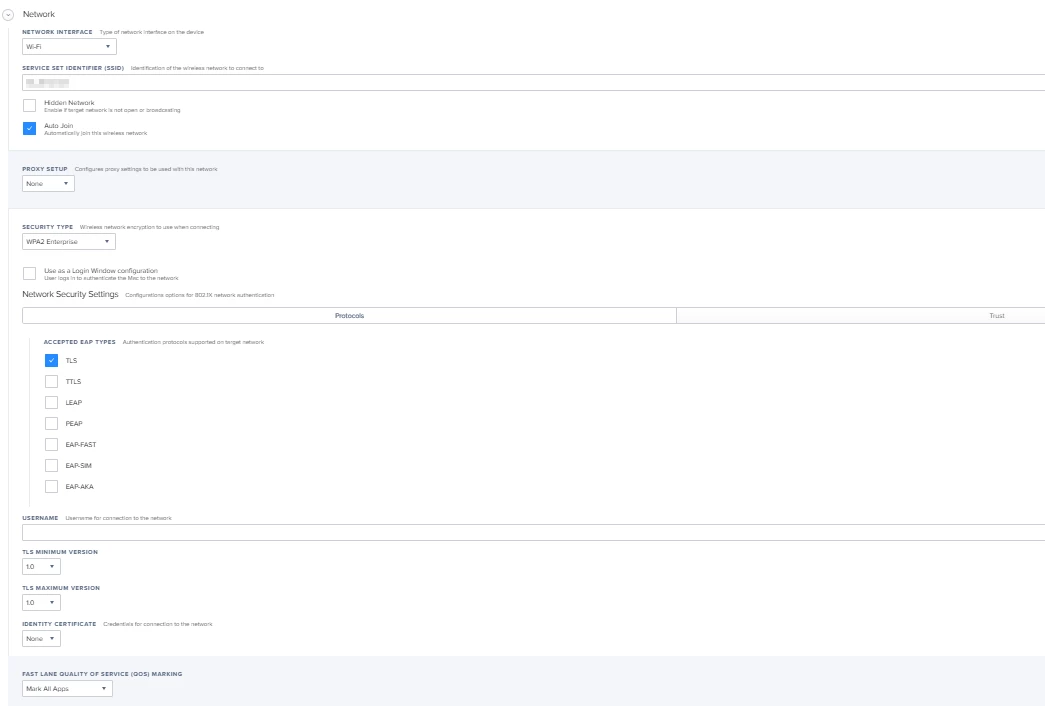
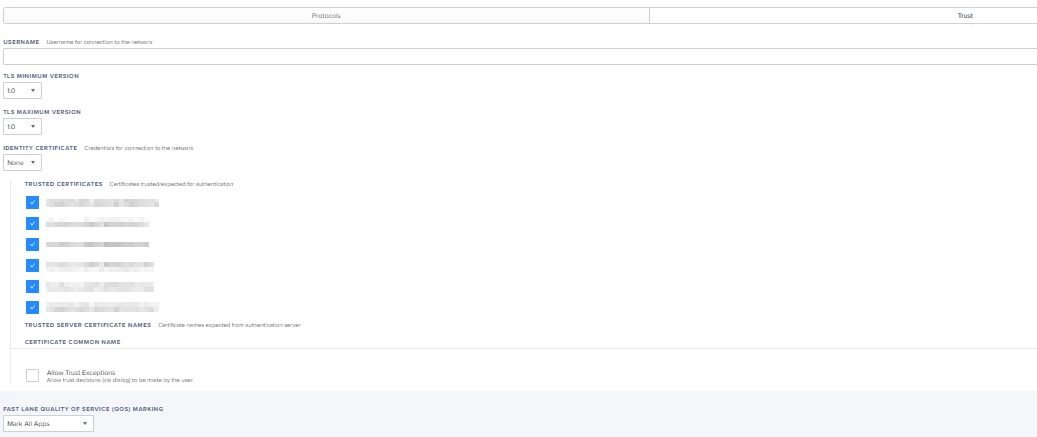
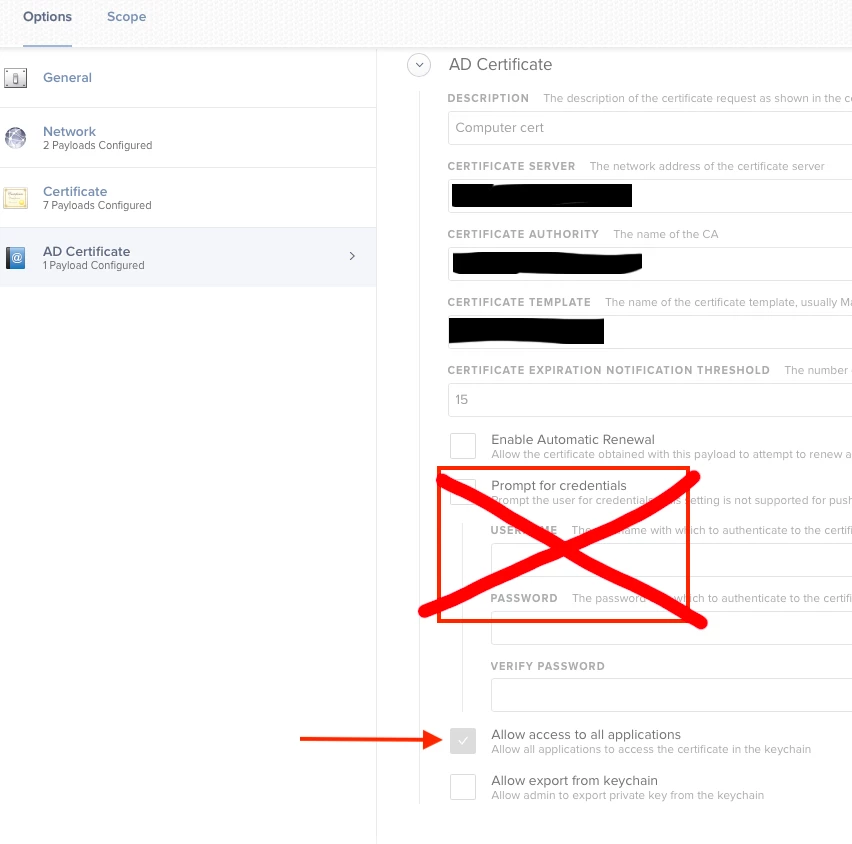
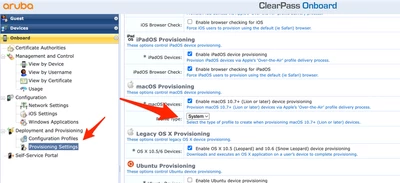
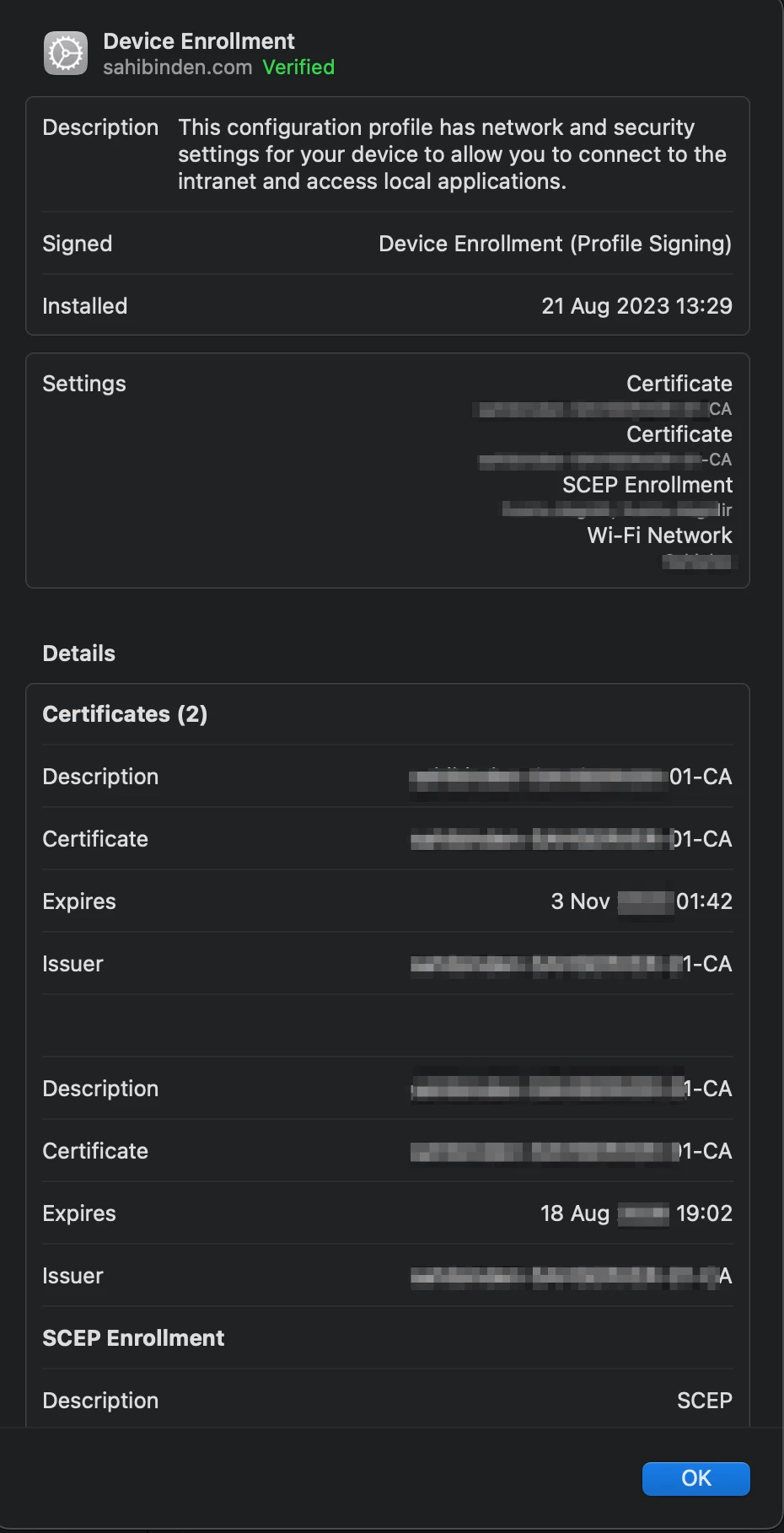
WHAT I HAVE FOUND: On a domain joined machine on our corp wired network, the machine is in a state where it is able to get to AD where it can poll password expiration for users. This is not the case when the device is on our corp wireless. The machine is not getting network access until AFTER a user logs in. I deliver an 802.1x configuration profile to the device with trusted certificates and I am to understand that this profile (which was built using Apple Configurator) installs using a "user" context rather than "system". If delivered in the "system" context, then the device can use the machine certificate for logon. Everything I have seen suggests you must hack the .mobileconfig file (shown here https://ntsystems.it/post/joining-wifi-before-login-on-mac-os-x-108). I tried this several times several ways and have had no luck getting the wireless network to connect at the OSX login screen. Has anyone tried this and had success? As shown in attachment, WiFi not connected with red dot.