We have a number of applications that install kernel extensions. I was told by Jamf support that the kernel extension needs to be installed via a config profile BEFORE the policy that installs the application runs. There are two ways to do this:
- Create a separate config profile for each kernel extension. Scope the policy that installs the app associated with this extension to check for the existence of this config profile before it runs. This will work but is cumbersome if a bunch of kernel extensions need to be loaded
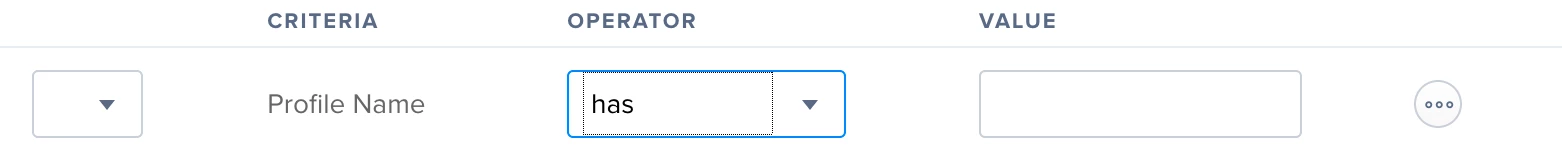
- Use an extension attribute to somehow check for the existence of a particular kernel extension. If it exists, then run the policy to install the app
Does anyone know how to check for the existence of a kernel extension?