One of the challenges that we often face is having a need to remotely access a workstation. Though Jamf offers this via Jamf Remote, its largest short coming is that it requires SSH access via a local network. So if your remote or in another office (with no Site to Site VPN) you end up being out of luck and have to rely on using LogMeIn or TeamViewer or one of the other platforms.
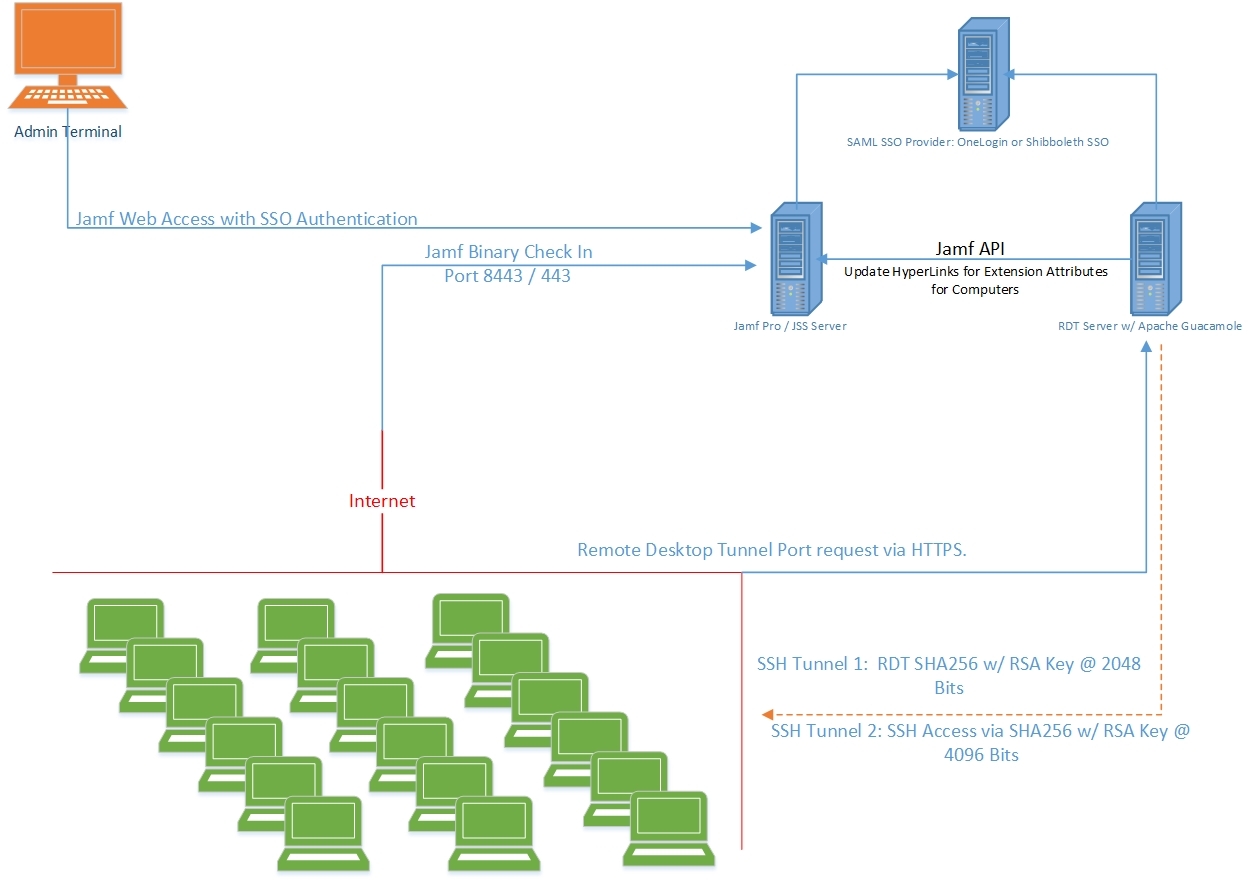
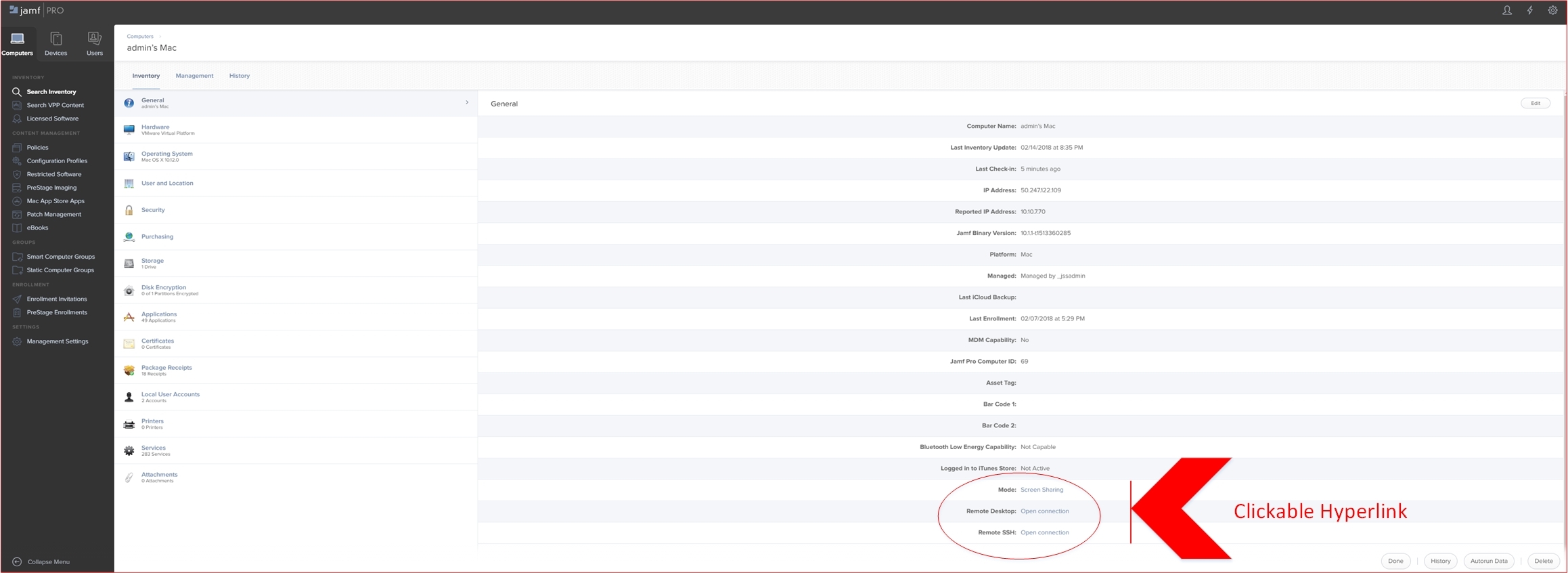
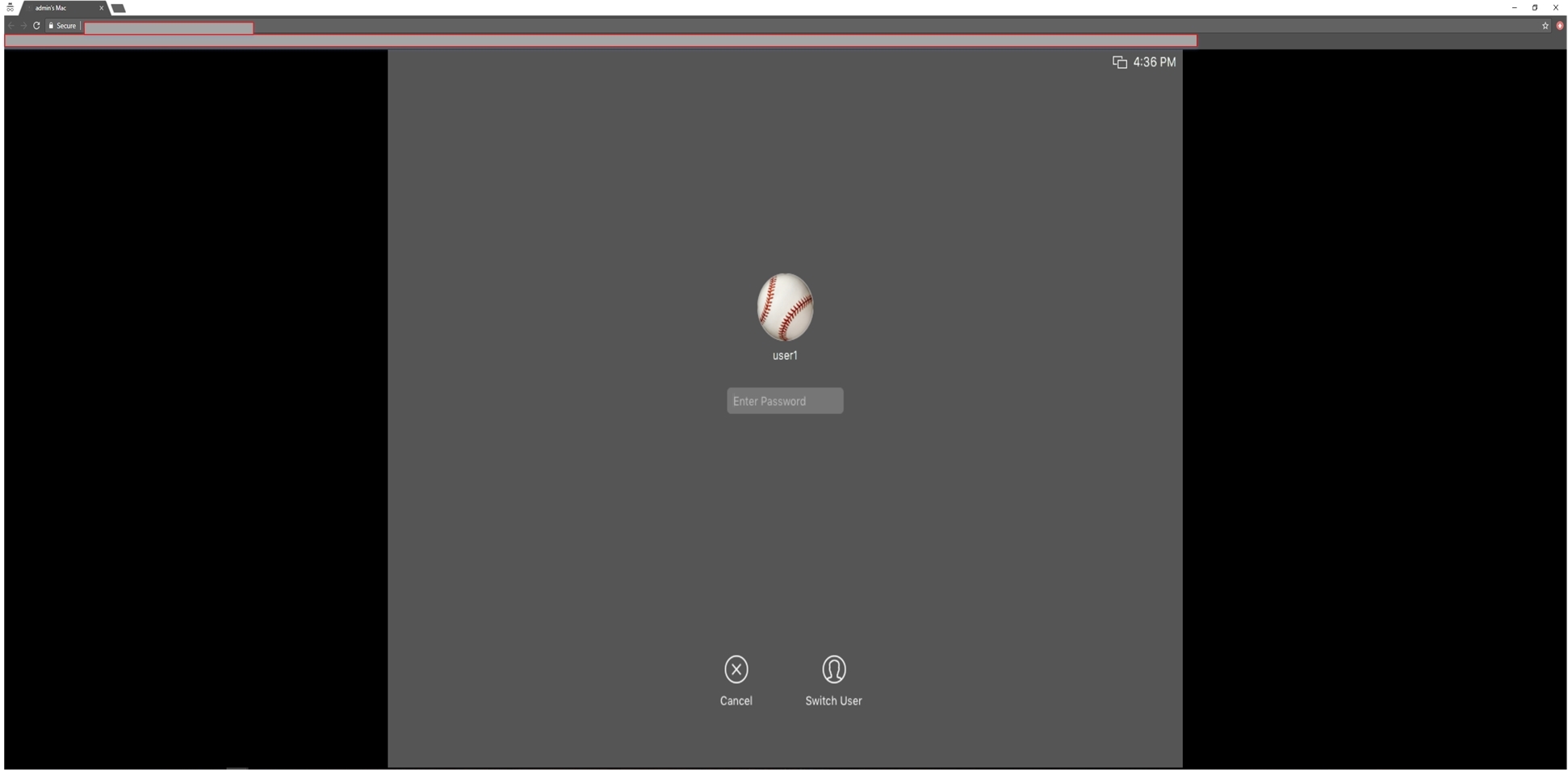
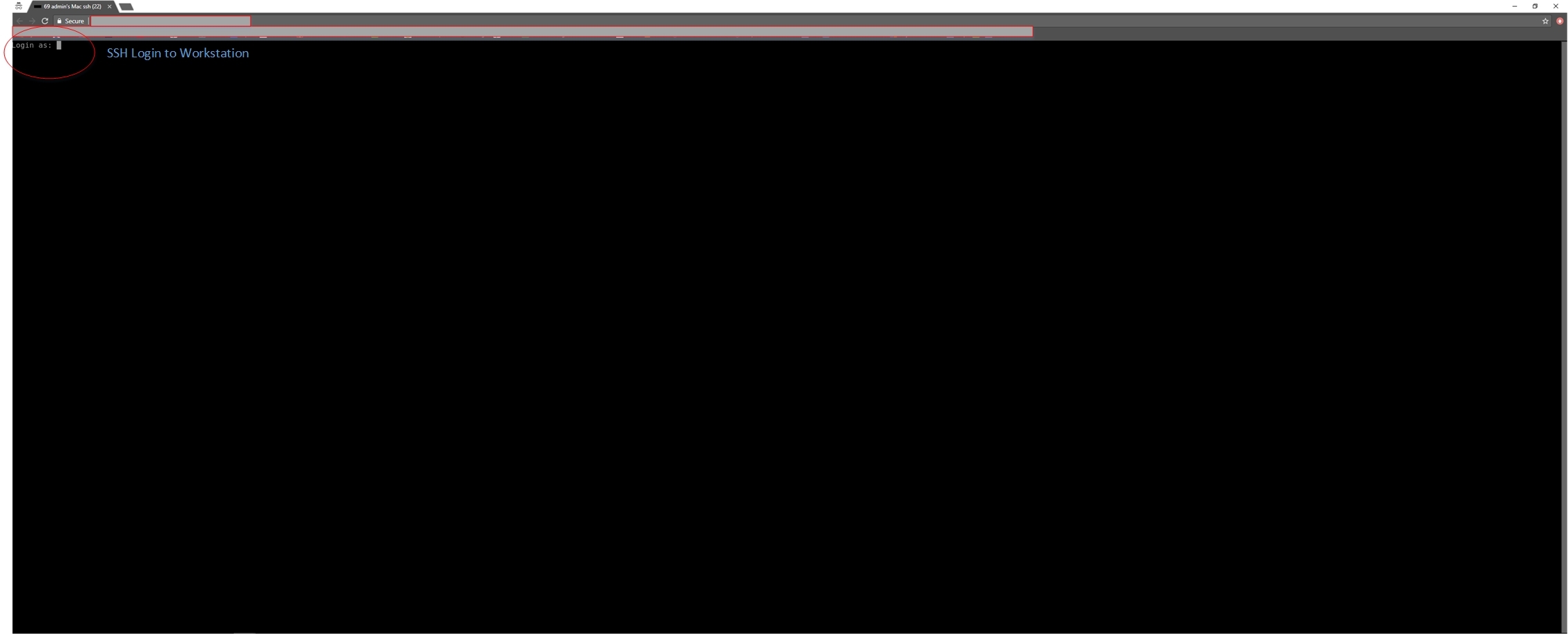
To combat this large issue, we created a dedicated server for Remote Desktop Access to endpoints using Apache Guacamole. We then coupled it with a SAML SSO interface and linked it to our Jamf Instances. We could then remote into any workstation directly from the Jamf Interface, while all the security handshakes occur in the background. This allowed us to not just have Remote Desktop Access to any workstation anywhere in the world, that we managed - but also the ability to have Remote SSH access to any workstation. We then took this a step further, and created the ability to switch dynamically from Remote Sharing to Remote Desktop. So that we can log in as additional users to the macOS GUI.
One caveat is that in order to get the seamless interface of clicking a link created by a Extension Attribute, we had to place a Proxy Server at the front of our Jamf Pro instances. This looks for the EA id and converts it to a hyperlink. It would be awesome if EA's can be updated as HyperLinks or better XML content (thus specifying a hyperlink). We are going to update this method for now, so Jamf Cloud instances can use the platform via a Chrome / Firefox Java plugin that looks for the EA id's and converts them to a Hyperlink (this eliminating the need for a Proxy Server). There is a feature request for this already - here: https://www.jamf.com/jamf-nation/feature-requests/2576/hyperlink-in-extension-attribute.
The installation process would ideally be a dedicated Remote Access Server anywhere (we have ours in AWS). 1 Server can handle about 10,000 or so dedicated connections simultaneously with enough resources (we are stress testing this later in the year). But I dont know how many IT firms or clients access 10,000 workstation desktops at 1 point in time. Once you add in the API username of your Jamf Server (API write commands), the scripts on the RA server will POST the hyperlinks to the dedicated port. When you click on the link it goes through the SAML SSO provider (we integrated OneLogin and Shibboleth SSO) passes the IT user creds from Jamf / SSO to the Guacamole Server and then opens the remote access to the workstation.
The install of the Remote Access binaries was setup as a Policy which executes on Enrollment to every workstation. Once installed it communicates to the RA server within 1 minute. The tunnels are established using SHA256 @ 2048 bits and 4096 bits.
We will be publishing our binary for additional testing in sometime in March. As well as methods to integrate it with Jamf and setting up a dedicated server.