Has anyone had any experience in deploying Fortinet's FortiClient to computers? I get a DMG from our on-prem controller but that doesn't install when I use Jamf Pro to install onto client machines
- Home
- Community
- Get Support
- General Discussions
- Deploying FortiClient
Deploying FortiClient
- June 4, 2020
- 49 replies
- 448 views
49 replies
 +13
+13- Honored Contributor
- June 5, 2020
You will need to repackage ALL of the installer files contained in the dmg and add a post install script that calls the pkg file provided so that it reads the config file correctly. You can just copy all to a folder in /tmp and then have the post install script use
installer to run the pkg and then mop up the installer files.
- Author
- Contributor
- June 11, 2020
@andrew.nicholas So what do you use to repackage all the installer files?
 +13
+13- Honored Contributor
- June 11, 2020
There are multiple tools available but Composer has always been tried and true for me.
- Contributor
- July 24, 2020
I just opened the DMG and dragged the Install.mpkg to another folder.
Uploaded it to Jamf to create a package.
Next push it with a policy (together with a config package) to the clients
 +3
+3- New Contributor
- July 27, 2020
I just use a script which also works if you create a upgrade policy.
#!/bin/bash
cd /tmp/
curl -O https://ems_server:10443/installers/version/FortiClient_6.2.7.dmg
hdiutil attach FortiClient_6.2.7.dmg
cd /Volumes/FortiClient/
sudo installer -pkg Install.mpkg -target "/"
cd /tmp/
rm FortiClient_6.2.7.dmg
hdiutil detach /Volumes/FortiClient/- Valued Contributor
- January 13, 2021
This worked with FortiClient 6.2.6, only issue is it doesn't seem to pick up the custom.conf and default.conf settings until after a reboot.
Anyone know what launchagent/launchdaemon to reload to get that to be picked up without a reboot? Or maybe some commandline on it's own to get it to reload the config? It loads up initially unconfigured and unlicensed.
Apparently this is normal as per the documentation. Fun.
- Contributor
- January 26, 2021
FortiClient 6.4.2 uses an app to download and launch the installer and there's no obvious way to get the .pkg file to use in a Jamf package. How do I go about deploying this? I can't find any help from the FortiClient site. The talk about silent installs via the command line but only for windows. No mention of the Mac.
- Contributor
- February 4, 2021
@dan.berlyoung I am working through this as well for 6.4.2. I've been working with Packages as we use School, but now the KB is updated to suggest Composer, which seems referenced far more (from Pro users) here in the forums. I sent a request for access to it and am waiting so I can try working with this instead of Packages. For single *.app deployments, Packages has worked well but for anything with like an mpkg linking to other stuff or data deployed to nested folders, plug ins, etc. we haven't had success. I'm hoping that a supported utility like Composer will allow us to break through some challenges with apps like Forticlient.
If you have Forticlient EMS, your EMS deployments should include a dmg when you build them. You can pull the pkg from this by mounting the dmg then just dragging or copying our the pkg. However, as mentioned, the .conf files need to be deployed another way. I don't know how to get the configurations for autoreg host, etc. installed along with the app yet. Will share once I've tested some!
 +3
+3- New Contributor
- February 22, 2021
@MasterNovice I'm having trouble deploying Forticlient 6.4 as well. I made a snapshot of it so I can configure the app with the proper connection settings, but no matter which way I deploy it (.dmg or.pkg), once the app opens up it is just a blank screen. I tried taking a few snapshots to try to get it to work, but each time was the same issue. I also attempted to make the package via Drag and Drop (with no configured settings), but still got a blank screen on the app once it was deployed.
Any advice? Thanks!
- Valued Contributor
- February 22, 2021
@jknopp Just out of curiosity, have you tried rebooting post-install? I've seen Forticlient be dumb and not work right until you reboot...
 +9
+9- Valued Contributor
- February 22, 2021
@jknopp We've been experiencing that same behavior in lots of Macs recently. No pattern here in terms of operating system or any other software installed that might be interfering . You just open FortiClient (Either VPN or Full) edition and screen goes blank. Tried rebooting, reinstalling, clean installing, you name it, with no use. We are still waiting for Fortinet to introduce some update to the VPN clients.
 +3
+3- New Contributor
- February 22, 2021
@rstasel yeah, I've tried every combination of the like. The process usually goes like: 1) take snapshot 2) install Forticlient, configure app, reboot 3) open Forticlient, confirm everything works 4) take post-install capture, then build the .pkg or .dmg. Any way I seem to do it no dice.
- Valued Contributor
- February 22, 2021
Would definitely open a ticket with Fortinet. I know the 6.2.x series works fine.
According to their docs, you should just have to have your EMS admin create a custom installer (just like 6.2...)
https://docs.fortinet.com/document/forticlient/6.4.1/ems-administration-guide/757497/deploying-initial-installations-of-forticlient-macos
 +12
+12- Valued Contributor
- March 5, 2021
In my case the enSiloClient I am having issues with. I extracted the .pkg
enSiloInstallerOSX_3.1.0.201_FortiEDR_Connect_3.pkg
to my local downloads folder and then uploaded it to JAMF Pro for the install. At first glance it was refreshing seeing nothing pop up at me requesting permission for anything and it looked that it had installed as I saw the icon on my menu bar. When returning to the Admin console the machines state is "Degraded" with the following information.
Warnings: Please approve Fortinet Endpoint Protection and Response Platform Kernel extension in the device.So back to the drawing board when I run the uninstaller I notice that "enSiloCollector" wants access control to my system preferences and finder. And immediately following the uninstall I am hit with "Please Approve enSilo Kernel Extension in System Preferences and then Security Panel.
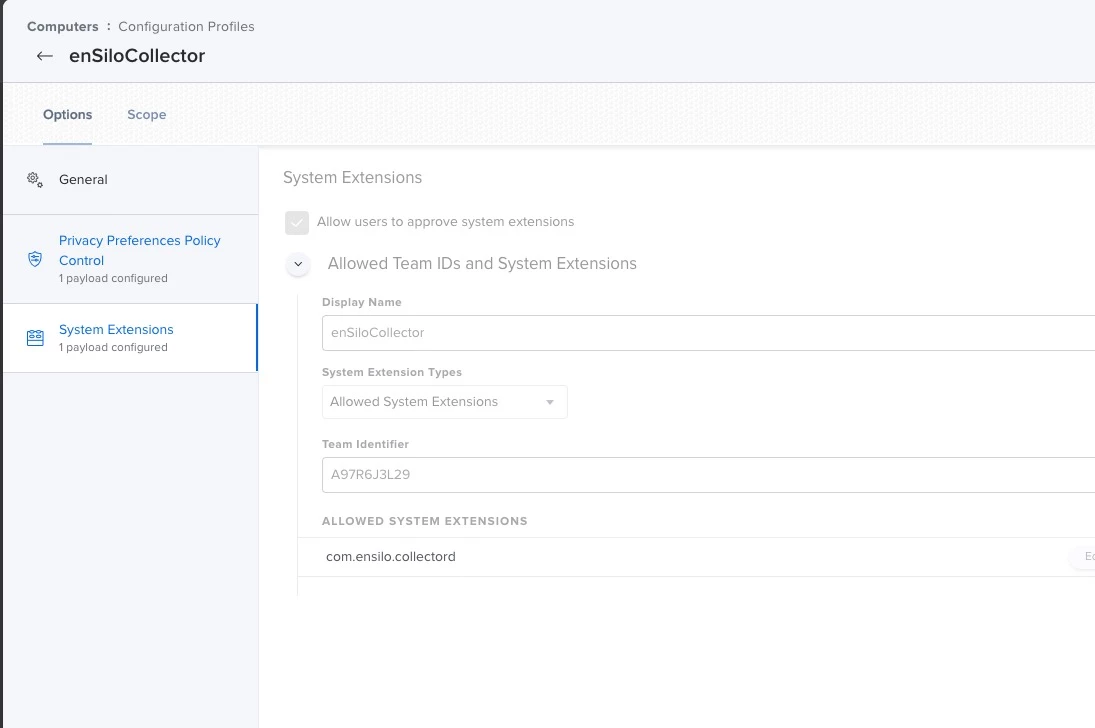
From this information I gathered I was able to locate "enSiloCollector" and attempted to create a Configuration Profile using the PPPC Utility.app (I have not been having much success with this app since Big Sur) Since I am on Big Sur I toggled the compatibility toggle and proceeded to add the required Privacy Settings
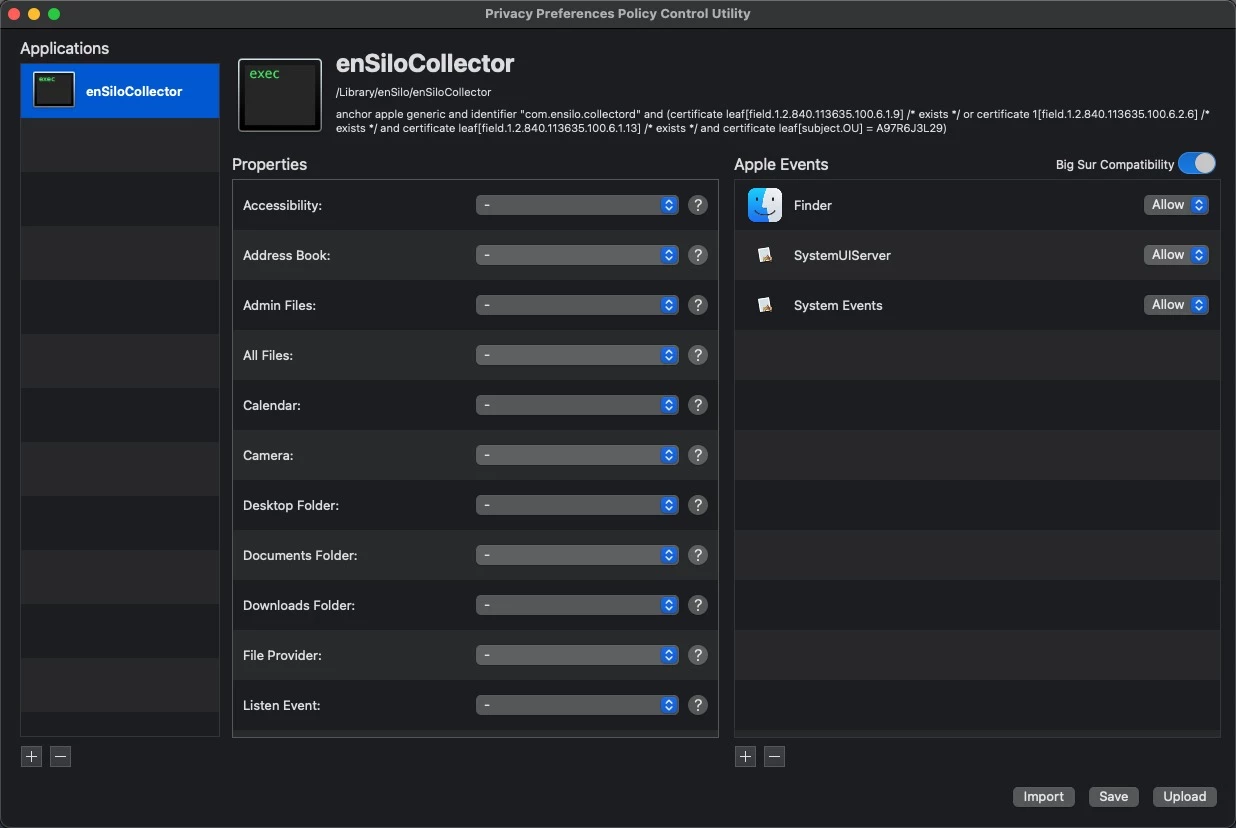
From the information gathered here I now know the following:
Identifier : com.ensilo.collectord
Bunde ID: A97R6J3L2
I deploy the configuration with no success and failure each time:
In the payload (UUID: BC074ED4-9CFA-47DE-BE63-10B973280A90), the key 'Authorization' has an invalid value.I reached out to their support but have not heard back yet anyone have any input that could possibly assist me on this. I would greatly appreciate it.
- Valued Contributor
- March 9, 2021
Is there any chance to make a pkg, drop the install files in a tmp folder an start a silent install?
- Contributor
- March 9, 2021
Just pinging back to say that @jeroenkahle solution to this helped move me forward with delivery and installation from Jamf school for Forticlient 6.4.2. For some reason I had to run curl with sudo or I'd get a permissions error. I also had to run installer with the -allowUntrusted, presumably because of something with the EMS host certificate I don't undertsand.
I did use the custom dmg created in and hosted on Forticlient EMS, however the install isn't propagating the configuration, specifically for the host management, so the app doesn't auto connect to management. This does not resolve with a reboot. The dmg includes a folder with two config files, custom.conf and default.conf; I verified that these files are configured with the expected data in the dmg that makes it to the client. The custom.conf data looks like it makes it to a custom.plist file used to reference those items, but the management server url and some startup settings are in the default.conf and don't appear to be making it where they should/modifying what they should.
- Valued Contributor
- March 9, 2021
Ah yes, I have heard of this. I've also heard in Windows the EMS alters the installer msi and results in the cert being broken and not installing without overriding.
 +13
+13- Honored Contributor
- March 10, 2021
I've been fighting much the same with the 6.4.3 installer. Repacking the installer works as expected but it is the configuration of the associated web filter that has been overly problematic. I've gotten a test config that is able to create a mirror of the config that is installed at the apps first run but always sits as "not running" and refers to the agent as null, where as the one post install without the profile lists as "running" as specifically cites FortiClientNetwork. FortiClient support has been less then helpful and we're also still seeing a random issue seemingly related to the webfilter that drops all network traffic until the agent or computer is killed/restarted which they stated 6.4.3 was supposed to resolve.
 +12
+12- Valued Contributor
- April 8, 2021
Team does any one have an updated Extension Attribute to share for the new FortiEDR collector trying to collect as many FortiNet Extension Attributes as I can.
- New Contributor
- April 13, 2021
Hi, I'm at the stage when i create a package with composer, and just install it (without jamfpro) on a test device, it started with just blank app. It seems to be installing just fine, but with no success. is there anything that i'm doing wrong? I'm not even trying to load custom settings, just want to remotely install forticlient alone.
- Valued Contributor
- April 13, 2021
@Fevo I believe I've seen that before (not installing via Composer), have you tried a reboot after installing?
- Valued Contributor
- April 14, 2021
@Fevo I simply took the install.mpkg and included it as a package in my Jamf policy. Works for me. If you want to include preferences in the installation, I created a PKG with all preferences files and included them in the policy. It is recommended to install the preferences first and then the install.mpkg. Looks like the picture.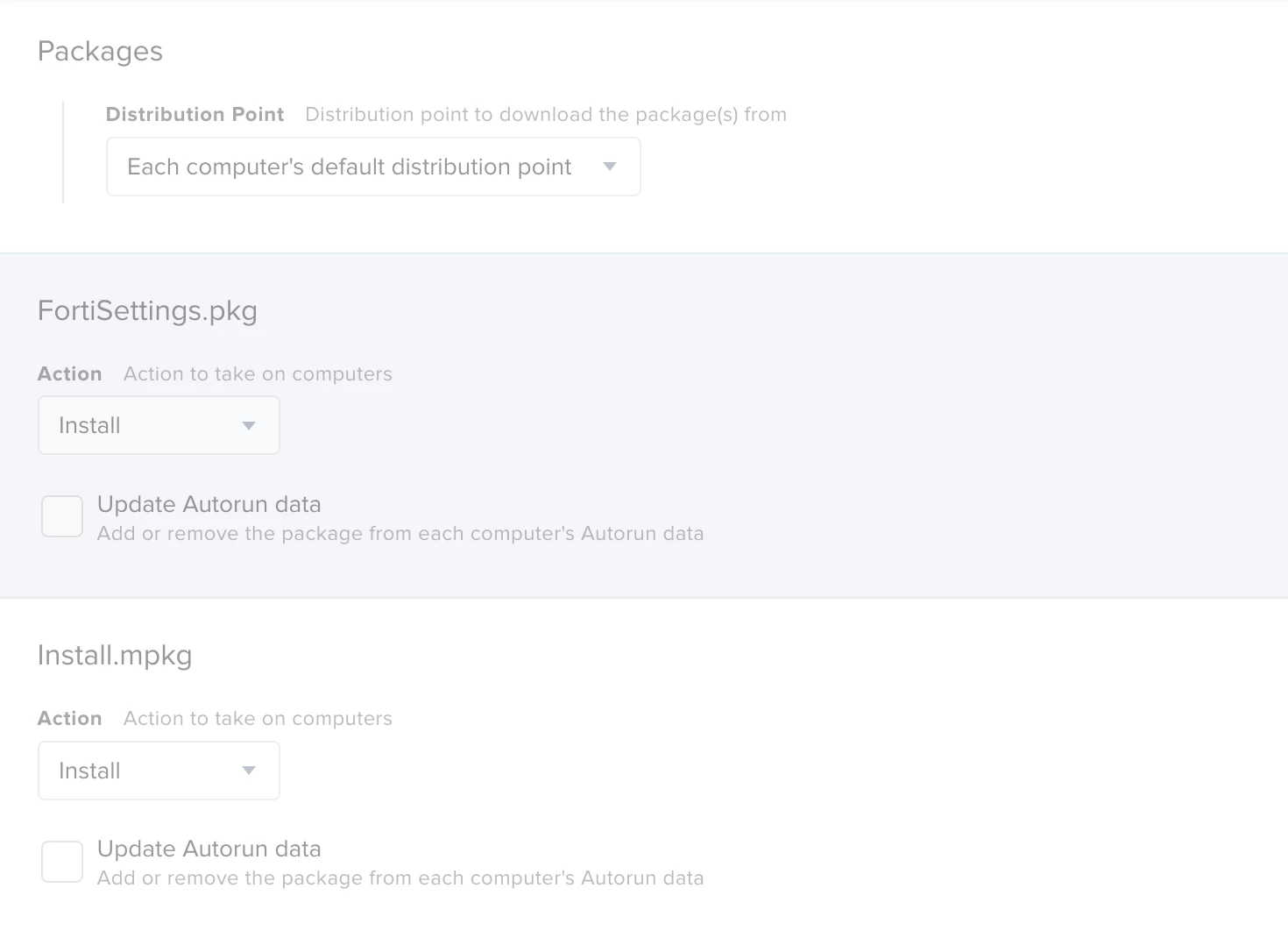
 +1
+1- New Contributor
- April 21, 2021
@mickl089 How did you get the preference files to create that pkg? I'm having a hard time finding where the forticlient stores those files. Did you just use Composer and do a before/after snapshot while configuring the app?
Thanks
- Valued Contributor
- April 22, 2021
@JonWVC Yes, you´ve got it! I used the composer, with before/after snapshot, so i could find out where the files are located.
Hopefully you can also find the files here: Library / Application Support / Fortinet. I have transferred the complete fortinet folder into the package. Attention: make sure that the settings are also installed first. Afterwards the FortiClient is installed via the install.mpkg, so the client also takes the settings and you don't even need a reboot of the system.
I just remembered that I wrote a tutorial.
Deploy FortiClient
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.
Scanning file for viruses.
Sorry, we're still checking this file's contents to make sure it's safe to download. Please try again in a few minutes.
OKThis file cannot be downloaded
Sorry, our virus scanner detected that this file isn't safe to download.
OK



