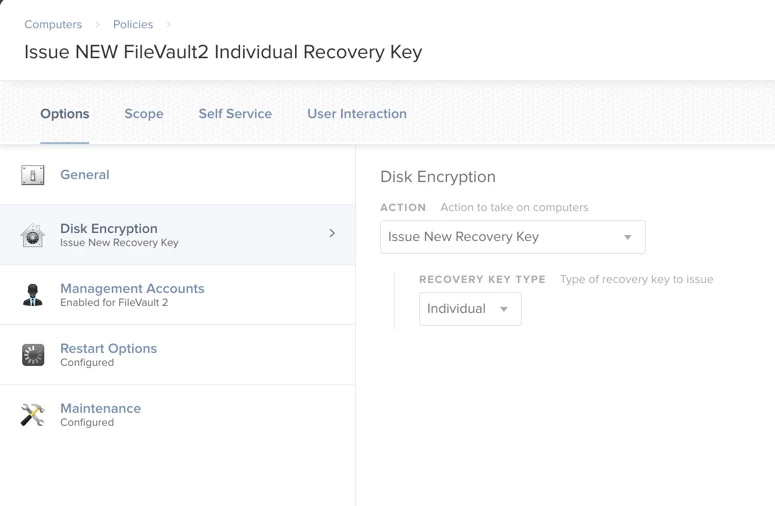
I have a simple policy setup that when used, use to issue out a new recovery key when the old was was used I would add a specific computer to that policy that would need a new recovery key and JAMF use to take care the rest. This is no longer working, I tried some of the scripts out there and could not get anything to work properly or would take a very long time to end up failing in the end. A while back ago, when I first set this up it was working without a problem.
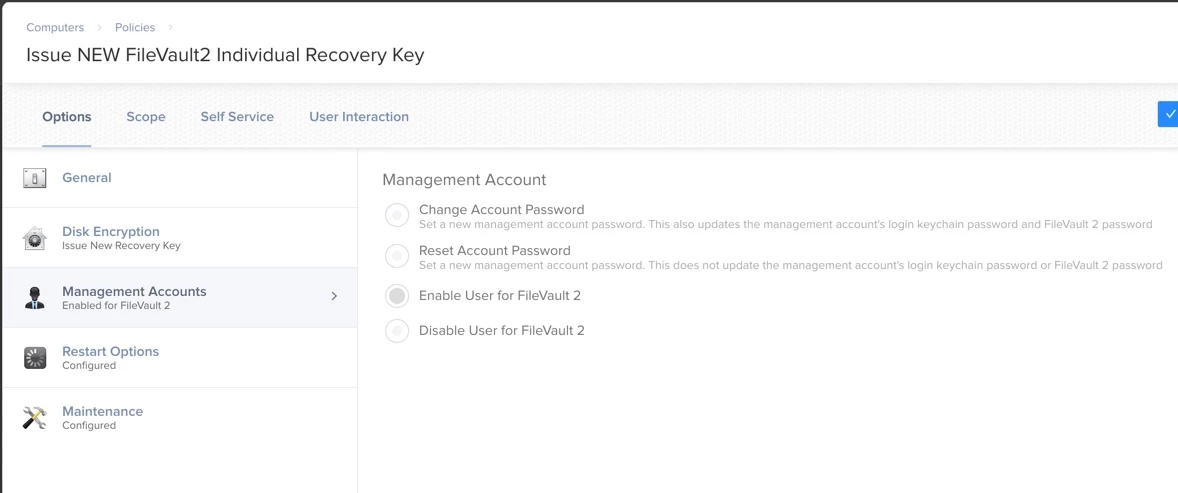
My Current setup: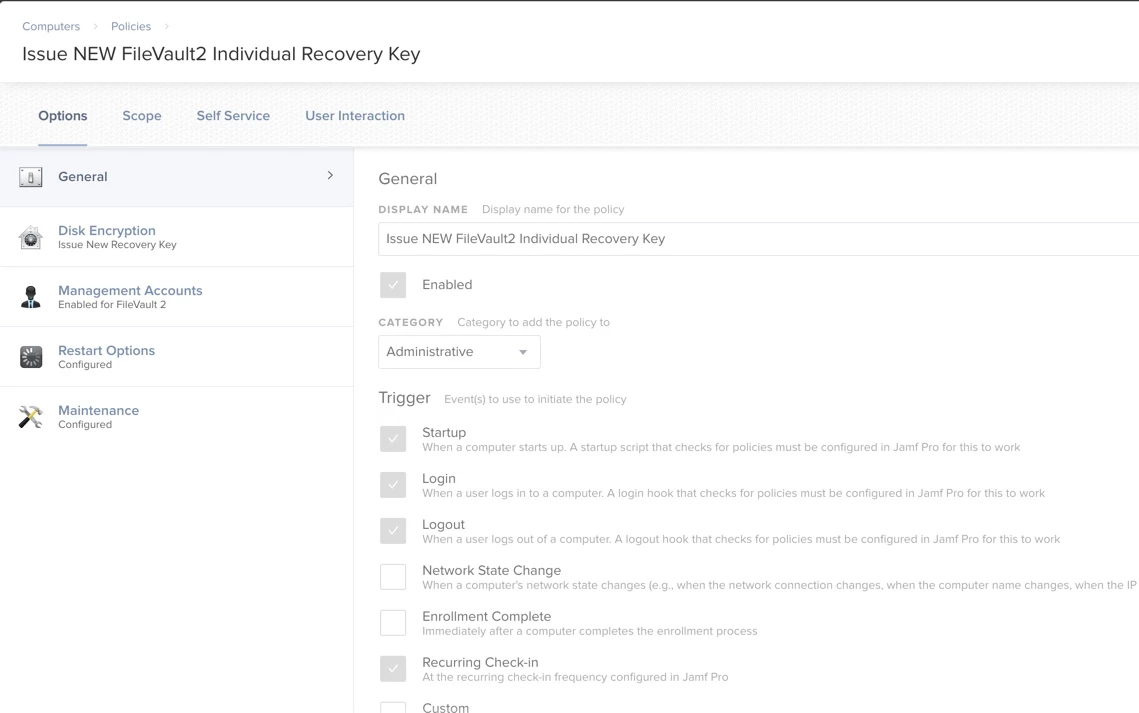
Error I am getting now:
Executing Policy Issue NEW FileVault2 Individual Recovery Key
Adding user JSSAdmin to filevault
Error: Added users failed error.
Error adding user to FileVault: Added users failed error.
New personal recovery key = '(...)'
Running Recon...
Retrieving inventory preferences from https://mycompnay.jamfcloud.com/...
Locating package receipts...
Locating accounts...
Searching path: /Applications
Locating software updates...
Locating printers...
Locating hardware information (Mac OS X 10.14.5)...
Gathering application usage information...
