Hi everyone! I'm struggling with getting this to work. Any input/advice would be greatly appreciated.
Goal: Create an LDAP group in AD, add AD users who do not have individual admin user accounts created in JAMF, and grant access in JAMF per the AD group's user memberships.
Issue: Users receiving "access denied" when launching JAMF Pro from SSO.
Steps taken:
-Created LDAP group "JAMFexample"
-Added a test user (a coworker) to the group
-Added the LDAP group to JAMF
-Granted necessary privilege's in JAMF for the test group
Troubleshot:
-Navigating to JAMF Settings>System Settings>LDAP Servers>Mappings and then testing User Mappings, User Group Mappings, and User Group Membership Mappings all give instant successful results.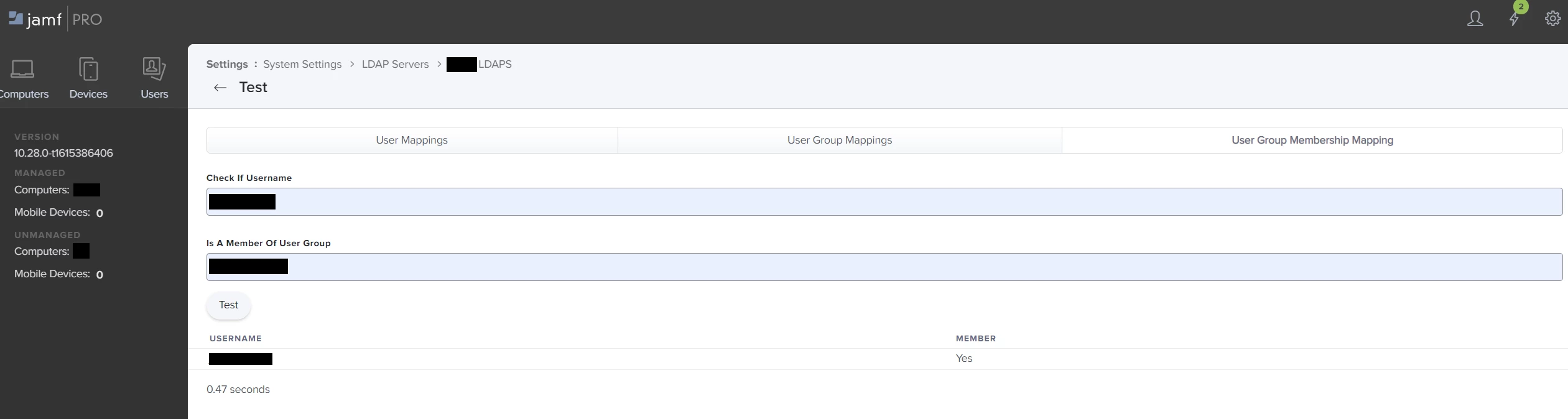
If all the tests work, what could be holding me up on this? I can provide any extra info that might be helpful.
Thanks for reading!



