Creating this thread for everyone to share new found knowledge, best practices & management tactics all in one place as we venture into a new Kext-Less macOS.
WWDC System Extensions Keynote
https://developer.apple.com/system-extensions/
Click Here for a Great Breakdown of System Extensions from Scott Knight
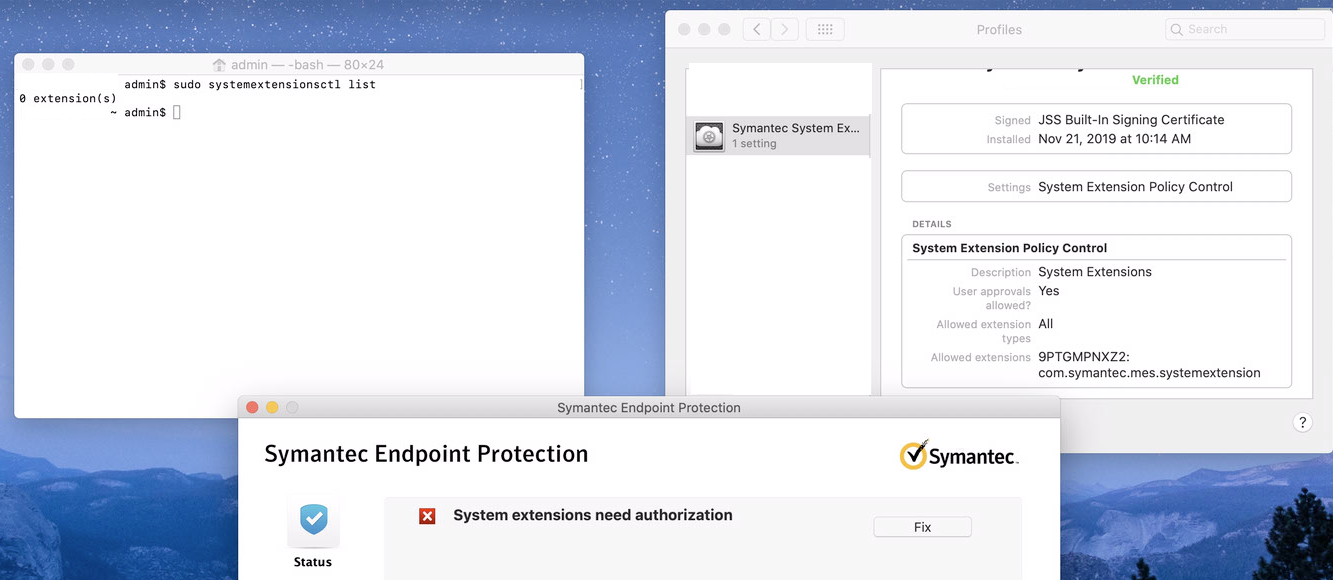
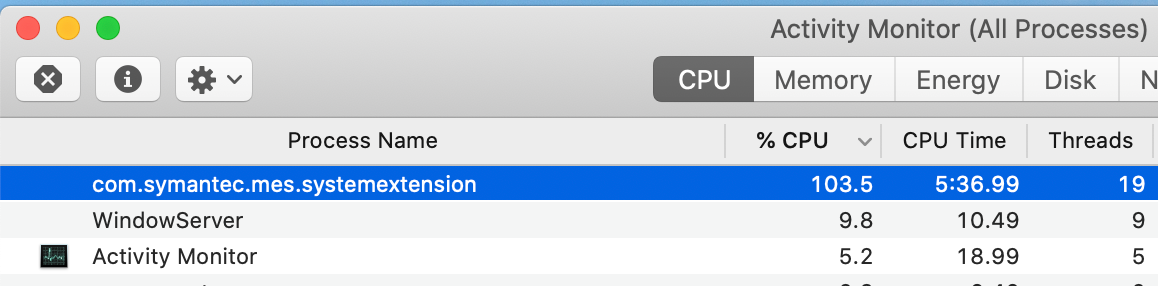
To start, the best way I know of to obtain a list of system extensions that are present on the machine via terminal is the following command.
systemextensionsctl listThis command will produce the following information regarding system extensions.
enabled active teamID bundleID (version) name [state]for a full example, using symantecs release for macOS 10.15, the following is populated
Hugonaut$ systemextensionsctl list
1 extension(s)
--- com.apple.system_extension.endpoint_security
enabled active teamID bundleID (version) name [state]
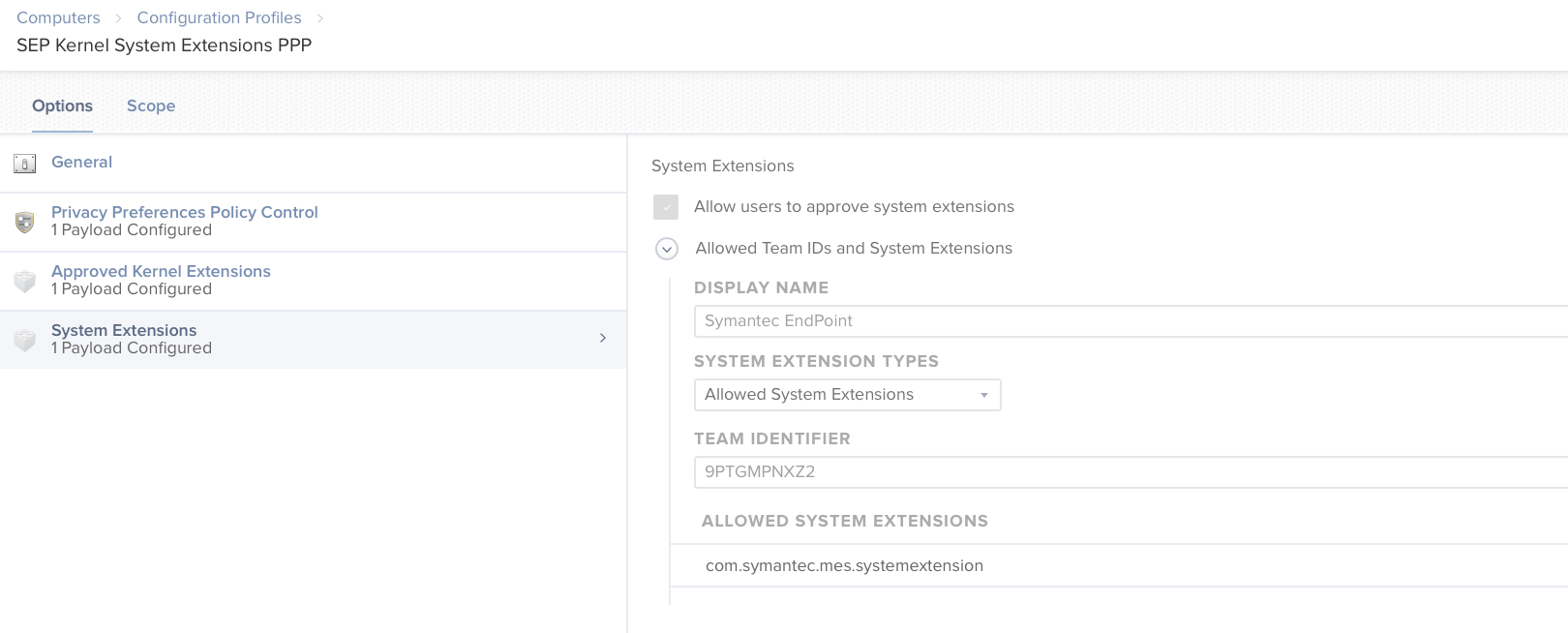
* * 9PTGMPNXZ2 com.symantec.mes.systemextension (10.0.0/10.0.0) Symantec System Extension [activated enabled]