We've followed all the instructions for setting up InTune integration with our Jamf Server on both sides. When I run the self service policy to get a Mac registered in InTune, it goes through all the steps until it gets to the JamfAAD.app where it basically stops. I've let it sit with the spinning gear for an hour with no progress at all. Here's the screenshot: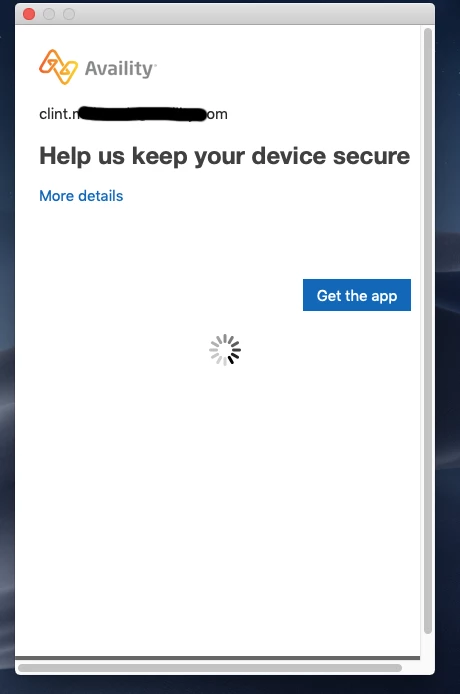
When I click on More Details, here's what it says: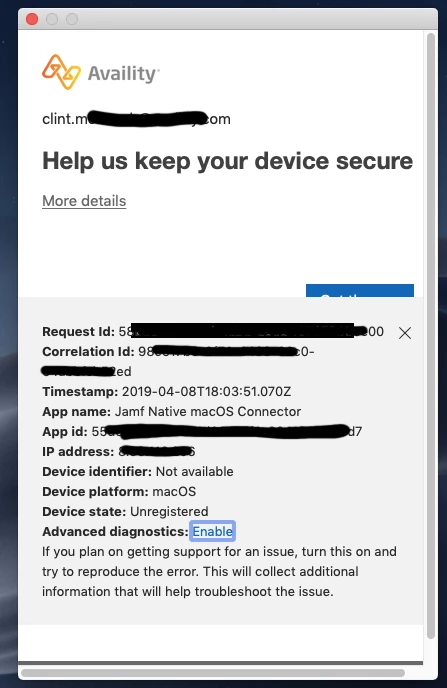
Has anyone else encountered this? What app is it trying to get? Could this window be any more vague?