Stupid question time. I suspect the answer is you can't, but i know there are much smarter people than me out there
We run a fleet of ~800 iPads mostly in the hands of students with individual needs, some of which really don't handle change very well
Can anyone recommend any options on how to maybe delay automatic rollout of iOS 10 in the next 24 hours so we can stagger our rollout to those classes who are better suited to a change and then slowly introduce the idea to those who can't.
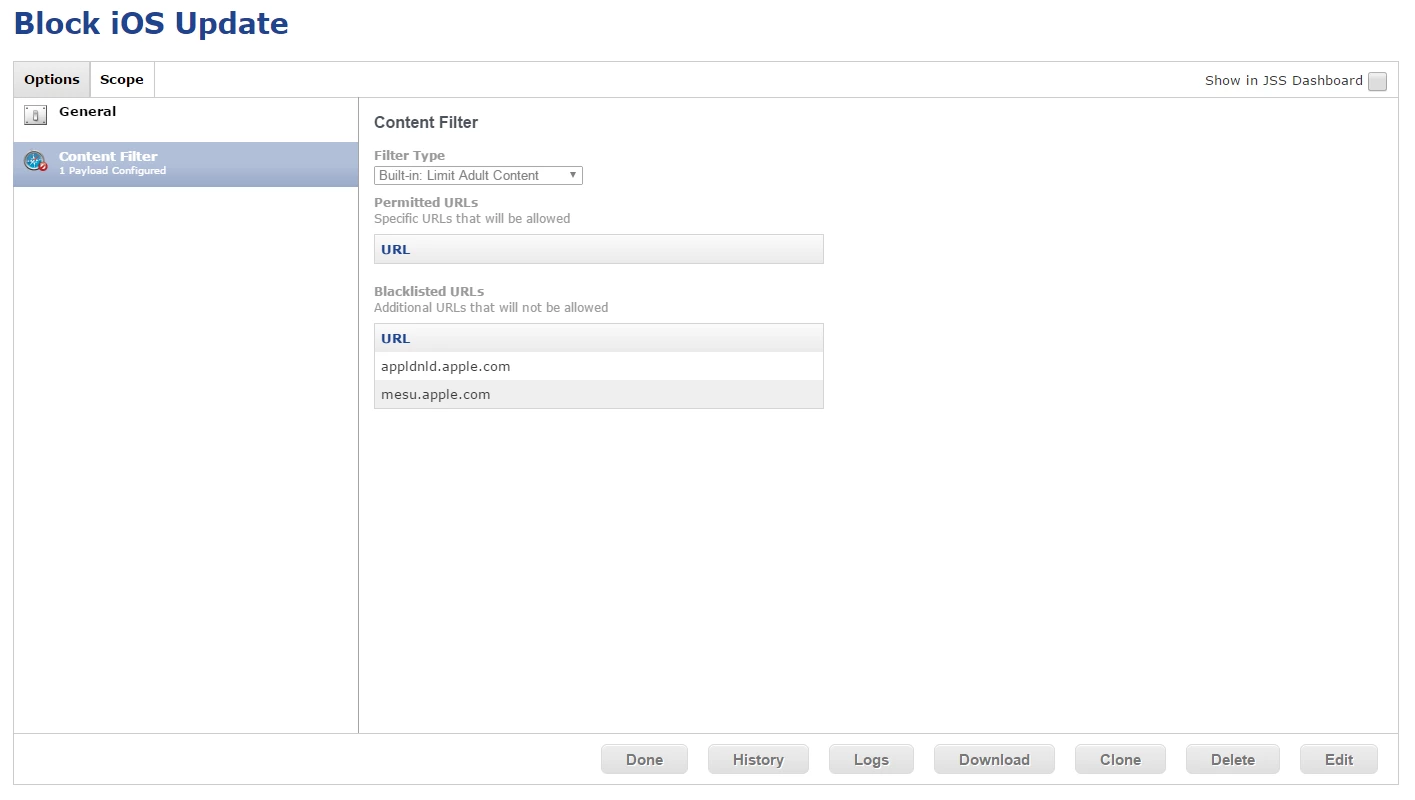
My initial idea was just to block the Update Services, but i'm pretty confident this would cause issues down the track with Apps updating etc.
If it helps, all iPads are supervised and managed
Thanks