Did anyone else see this during the Ignite Keynote today? It was super vague, but it caught my attention. Anyone have any details on this? Session was called: Microsoft 365: Modern management and deployment
- Home
- Community
- Get Support
- General Discussions
- Jamf Intune Integration
Jamf Intune Integration
- September 25, 2017
- 23 replies
- 135 views
23 replies
 +8
+8- Contributor
- September 26, 2017
M$ will be at JNUC where they’ll have more info about it.
 +16
+16- Honored Contributor
- September 26, 2017
And of course my travel plans got pulled for JNUC this year.
Really hope more info comes out about this.
 +16
+16- Honored Contributor
- September 26, 2017
Intune Partner Integration | Disclosure—Jamf integration
Jamf and Microsoft Enterprise Mobility + Security (EMS) announced a partnership to provide an automated compliance management solution for Mac devices accessing applications set up with Azure AD authentication. EMS provides an identity-driven unified endpoint management solution that offers a holistic approach to solve mobility and security challenges as you go through the digital transformation. Jamf is the management standard for the Apple ecosystem. Together, Jamf delivers information about the management state and health of Mac devices to Microsoft Intune’s device compliance engine, which integrates with Azure AD Conditional Access to allow organizations to identify unmanaged and non-compliant Mac devices, and remediate them.
https://blogs.technet.microsoft.com/stbnewsbytes/2017/09/25/cloud-platform-release-announcements-for-september-25-2017/
 +7
+7- Contributor
- September 26, 2017
My boss and two teammates are at Ignite. I’ve asked them to go to the breakout session where this will be talked about. Hoping for some good notes. Will post what they find.
My initial thought is that we will at least get the One Drive for Business sync to be enabled due to Azure AD being able to identify a Mac as managed and owned.
 +7
+7- Employee
- September 27, 2017
Hello everyone,
We're excited to announce our new collaboration with Microsoft EMS. There are two big takeaways from this collaboration.
First, you will now be able to share your Jamf Pro macOS inventory with Intune for a centralized view of devices. You can drill into that macOS inventory record and see the status of that device. This will be great for reporting, and is similar to our existing SCCM plug-in that shares inventory with SCCM.
Second, we can now provide Conditional Access for Jamf managed Mac devices that are trying to access applications set up with Azure AD authentication. This allows you to protect your data by ensuring that 1) your user has proper authorization and authentication and 2) the device the user is on meets your compliance requirements. For example, let’s say our user is trying to access email, but the password is not strong enough. Intune will evaluate the compliance and prevent the user from accessing email until the password is fixed. We also provide an easy interface for remediation. The user is brought into Jamf Self Service to fix the compliance issue.
We will be providing more resources as they become available.
Here is the announcement we posted today
And here is a view of the Workflow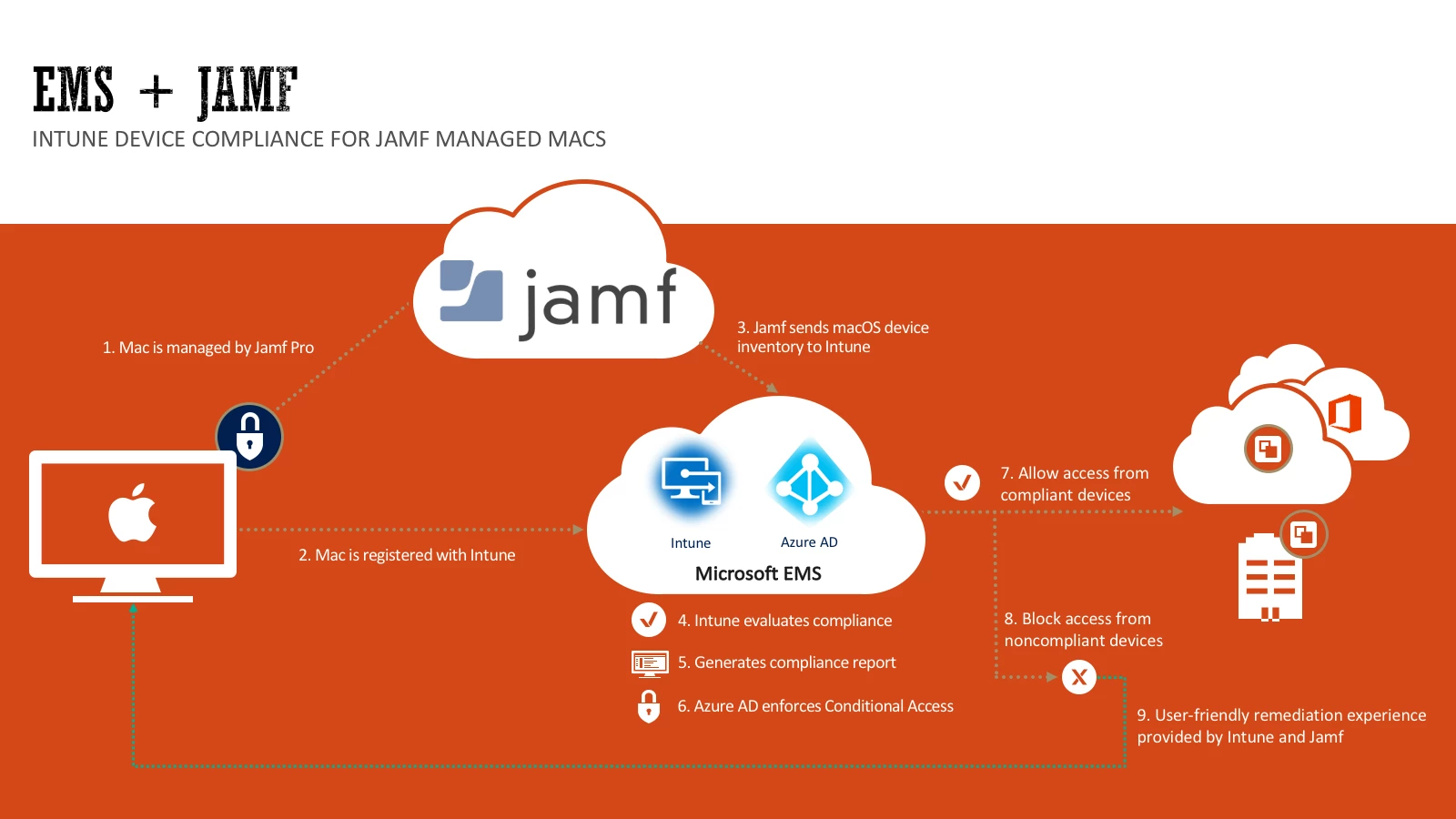
We will have more details for you in October at our Jamf Nation User Conference. A video will be available of the demo that Dean Hager gave at the Ignite Session as well.
 +3
+3- New Contributor
- September 28, 2017
Thanks for posting this as it is very interesting. When we considered Jamf as our MDM in December of 2016, we also looked at Intune and another potential MDM. Microsoft visited us for a few days and did kind of an Intune JumpStart, but at that time it did not meet our needs for things like ASM, multiple VPP tokens, or device based app assignment/management.
Being a predominantly Microsoft organization, I am interested to see where this goes but also realistic in my expectations. Kudos to both companies for working together on this and looking forward to learning more at JNUC 2017.
 +1
+1- New Contributor
- October 4, 2017
This is awesome news! We absolutely need to know everything about this feature the day it is released. We need it ASAP! Woohoo!
 +9
+9- Contributor
- October 10, 2017
Just need to understand in clear text - what does intune have to add, that jamf pro cannot do as default ?
- Jamf Heroes
- October 10, 2017
Facilitating conditional access is the big piece of the puzzle. From the above I guess that InTune can also be a single point of compliance reporting, while deriving its data from (and leaving the management to) jamf pro.
Our group is looking forward to this.
 +3
+3- New Contributor
- October 31, 2017
So, I saw one of the MS Intune presentations at JNUC, but still have a question: Is this MacOS only, or is iOS able to to the Jamf-InTune co-manigement as well?
 +7
+7- Contributor
- November 8, 2017
@JS_WWU Right now it is just MacOS, however I was told they want to add iOS as well. It may be in development and months away, or simply something they 'want' and years away if ever. I expect there is a better answer out there, but thats what I was told.
- New Contributor
- November 9, 2017
Do anyone of you know how to implement the Jamf Pro Intune integration? Didn't find any "How To" yet and would like to test it.
 +13
+13- Contributor
- November 9, 2017
@jgrowe Intune integration will be included in jamf Pro v. 10.1 and a future release of Intune. Hopefully before year's end.
 +1
+1- New Contributor
- November 27, 2017
What about JamfNow. Will there be InTune integration for those of us using JamfNow?
 +15
+15- Employee
- November 27, 2017
@paulshadwell We don't have a plan to bring InTune integration to Jamf Now at this time. Which features / workflows are most valuable to you as a Jamf Now customer?
 +8
+8- Contributor
- December 19, 2017
Just an FYI regarding JAMF Pro and Intune for iOS
(https://docs.microsoft.com/en-us/intune/app-based-conditional-access-intune)
We have not completed our Intune configuration so, I have no real time experience with the app, but I understand this method is being used by organizations currently utilizing other MDM solutions.
- Valued Contributor
- December 21, 2017
I've been working with our MS Server team and we have managed to get a test device into Azure AD.
As we use network accounts on the Mac I'm looking for a way to pass their credentials to the Company Portal to 'hide' this step from the user rather than making them log in twice.
http://docs.jamf.com/10.1.0/jamf-pro/release-notes/What's_New.html
[b]View Azure Active Directory ID information in Jamf Pro[/b]
When a computer is registered with Azure Active Directory, you can view Azure Active Directory information for a user and a computer in Jamf Pro. To view Azure Active Directory ID information, navigate to the General tab in inventory information of a computer.
This isn't showing for the Mac, does this feature need the device to be compliant for it to show in Inventory -> General?
@tharr00 For iOS it looks like we are going to have to stick with App Based Conditional Access until the iOS version of Company Portal no longer requires the MDM profile from an Intune Server.
 +1
+1- New Contributor
- February 20, 2018
On this moment you can only use Microsoft Intune compliance policies with Azure Active Directory conditional access to ensure that MacOs devices in your organization are compliant. For IOS devices (IPAD en IPhone) it is not possible to use the Intune integration from Jamf. Is this MacOS only, or is iOS able to to the Jamf-InTune co-management as well?
 +1
+1- New Contributor
- February 20, 2018
On this moment you can only use Microsoft Intune compliance policies with Azure Active Directory conditional access to ensure that MacOs devices in your organization are compliant. For IOS devices (IPAD en IPhone) it is not possible to use the Intune integration from Jamf. Is this MacOS only, or is iOS able to to the Jamf-InTune co-manigement as well?
 +7
+7- Employee
- February 21, 2018
@Dvanhuizen The current Intune + Jamf integration is currently macOS only. Jamf manages the device and sends necessary information to Intune for the compliance checks.
There is a feature request for iOS here that I would encourage people to comment on and vote for.
 +1
+1- New Contributor
- March 14, 2019
@Tad Basically the same as Jamf Pro. We would be using Jamf Pro if the entry point wasn't so expensive and I didn't have to have a minimum quantity of 50.
We're a small shop of 15 users and I'm an IT professional but can't justify the expense of Jamf Pro. Jamf Now is ok but needs more functionality so we can use it alongside InTune. We have InTune as part of Office365 and Azure AD but Microsoft's lack of good macOS management has us looking elsewhere. Jamf Now is starting to limit us so I am looking around. At the moment I am testing SimpleMDM.
 +7
+7- Valued Contributor
- March 15, 2019
I have some general questions about the Intune Integration and maybe somebody has more know-how about this.
We already have a working configuration with an INTERNAL Jamf pro server and Intune Integration. This Jamf pro server is our productive system and contains about 800 enrolled Mac devices. About half of these devices are already registered in Intune and conditional access is working.
Now we want to replace this Jamf pro server with a new Jamf pro server which is accessible from the internet too. So the management URL will change to a public URL.
Our new server will now be installed and configured, so we want to do some tests (including Intune integration). As we have no test server, we would like to run these both servers simultaneously as long as the new server is not ready for production.
And here comes the question:
Is it possible to configure TWO Jamf pro server (at the moment with different databases) to the same Intune Application ID?
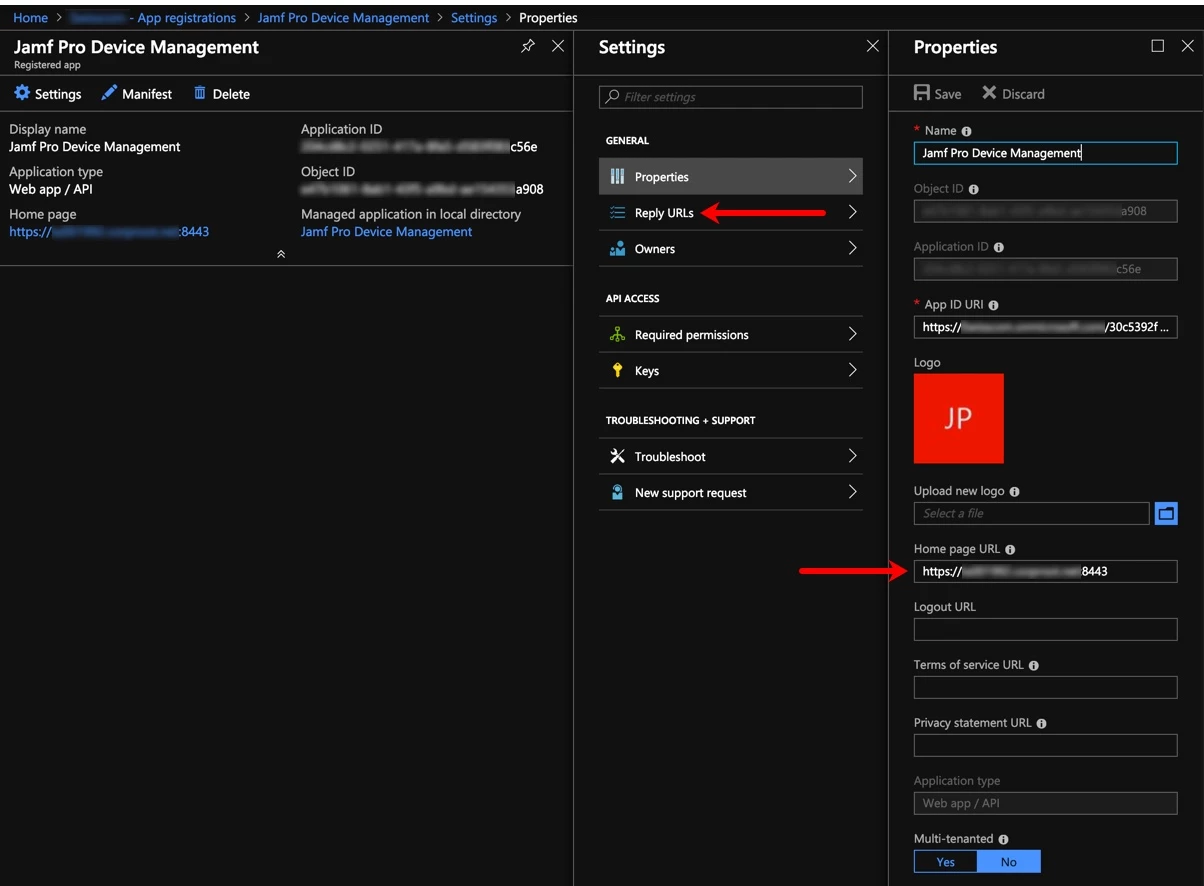
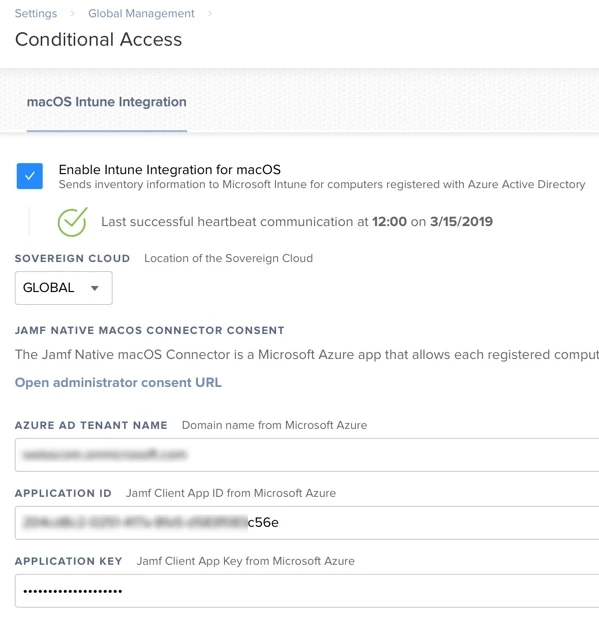
As long as we have the valid tenant name, application id and application key, I don't see why this should not be possible.
There's only one issue: the home page and reply URL, which is configured in Intune and links to our internal server at the moment. (But could be changed in Intune)
So, what is the technical meaning of this URL? Is it only used during the device registration (as the company portal app will be started from Self service and redirects to the Jamf pro server)? As far as I know, Intune will not directly access our JSS (it's even not possible with our current internal server). So only JSS will send the device inventory data to Intune and that's it?
So it should be possible to connect two different JSS to the same Azure tenant? Even if they have different URL.
And what happens to the already registered Mac devices from the old server? Does a new connector affect the state of these registrations? On the Azure AD / Intune portal device list I only see an Azure Computer device ID and an Azure User device ID. But both should not change, if the device will be re-enrolled to a new server, right?
There are not many information available, what will broke an already registered device, if nothing will be changed on the device itself (same device id, same user id, same tenant id, same conditional access rules still compliant....just a new JSS server and so a new MDM profile with an different management URL).
Of course we need to change the home page and reply URL in Intune, before we can test some registration from devices on the new server. But it should be possible to change this URL back after the test.
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.
Scanning file for viruses.
Sorry, we're still checking this file's contents to make sure it's safe to download. Please try again in a few minutes.
OKThis file cannot be downloaded
Sorry, our virus scanner detected that this file isn't safe to download.
OK


