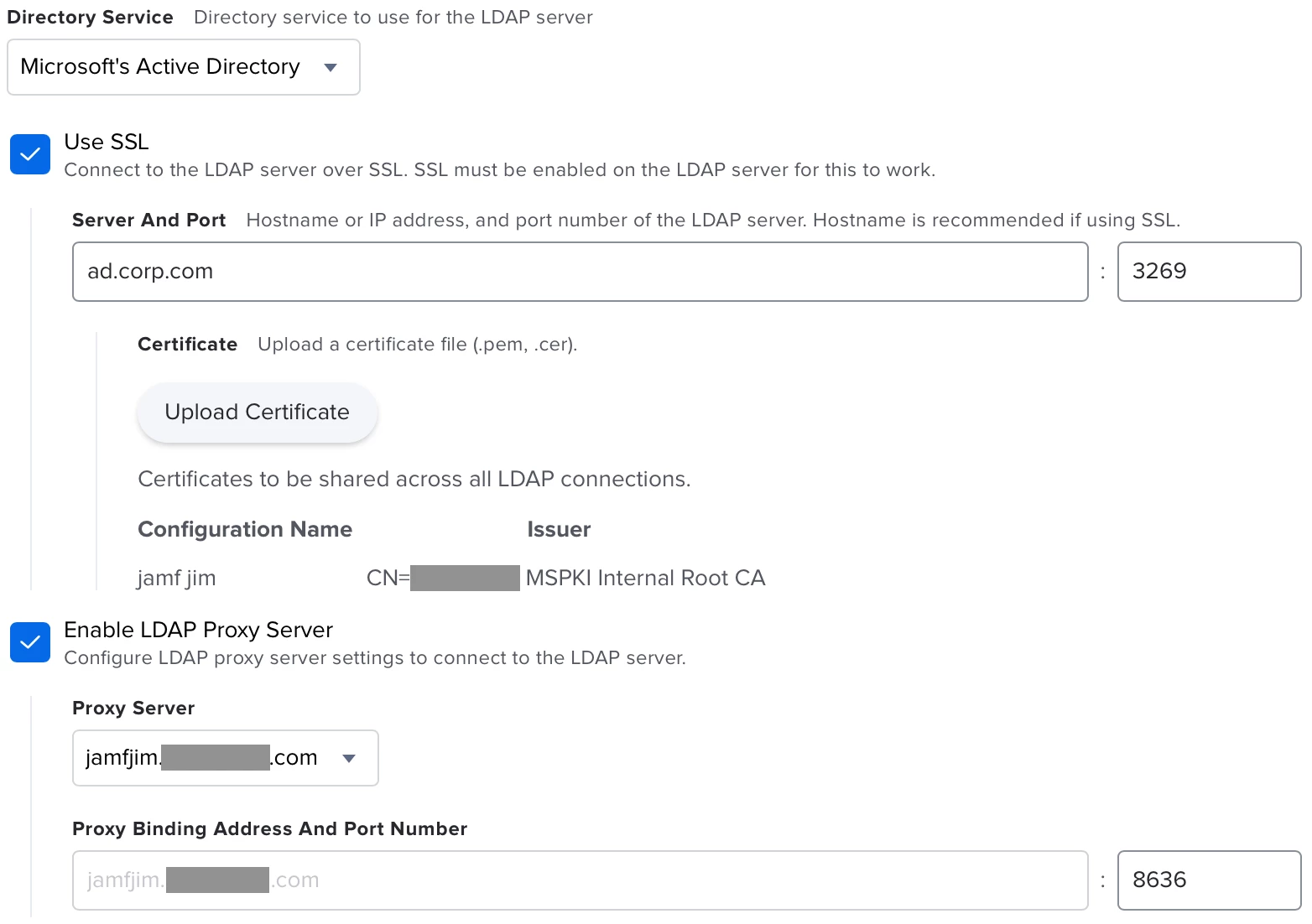
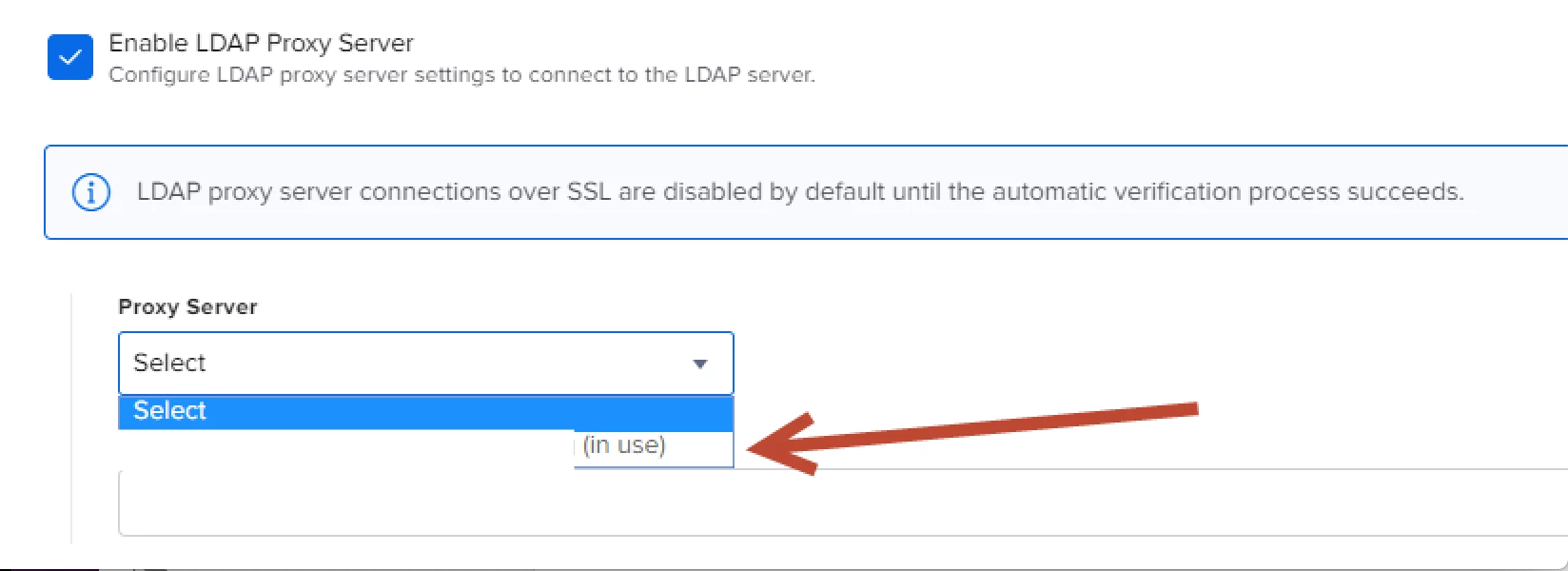
Has anyone figured out any successful workarounds on getting Infrastructure Manager (JIM) on the same Windows Server to proxy to more than 1 domain for LDAP? According to Jamf support, it only supports 1 domain per JIM per server and I got 3 domains in my University's AD forest to deal with. I also created a feature request in https://www.jamf.com/jamf-nation/feature-requests/9333/feature-request-jamf-infrastructure-manager and hopefully you all can help with that by upvoting it.
Question
Multi-domain environment and Infrastructure Manager on Windows Server 2016
 +12
+12Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.