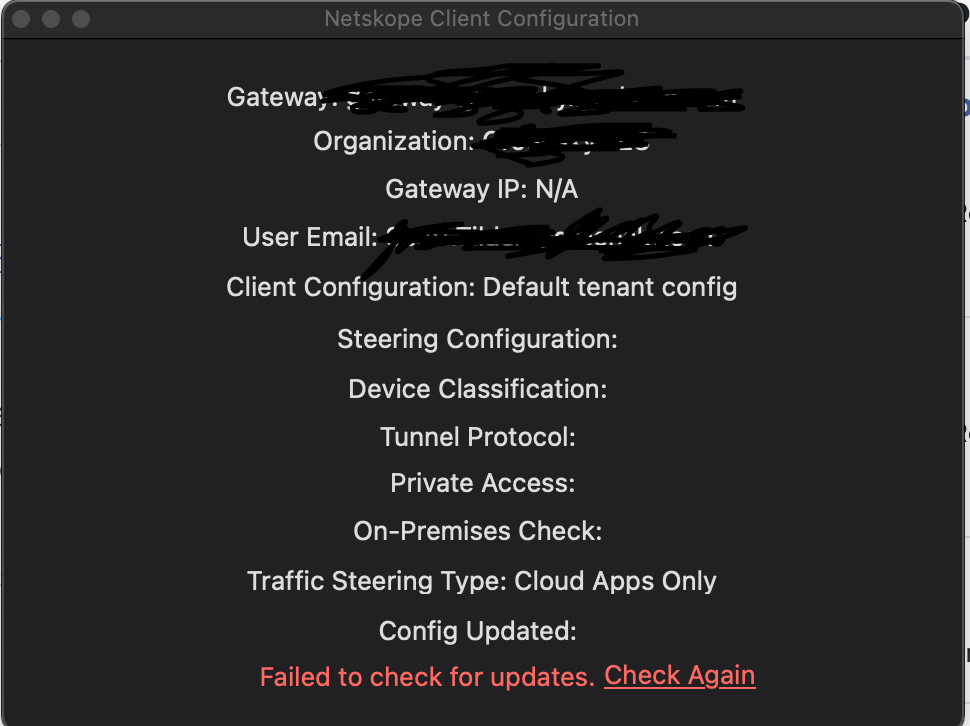
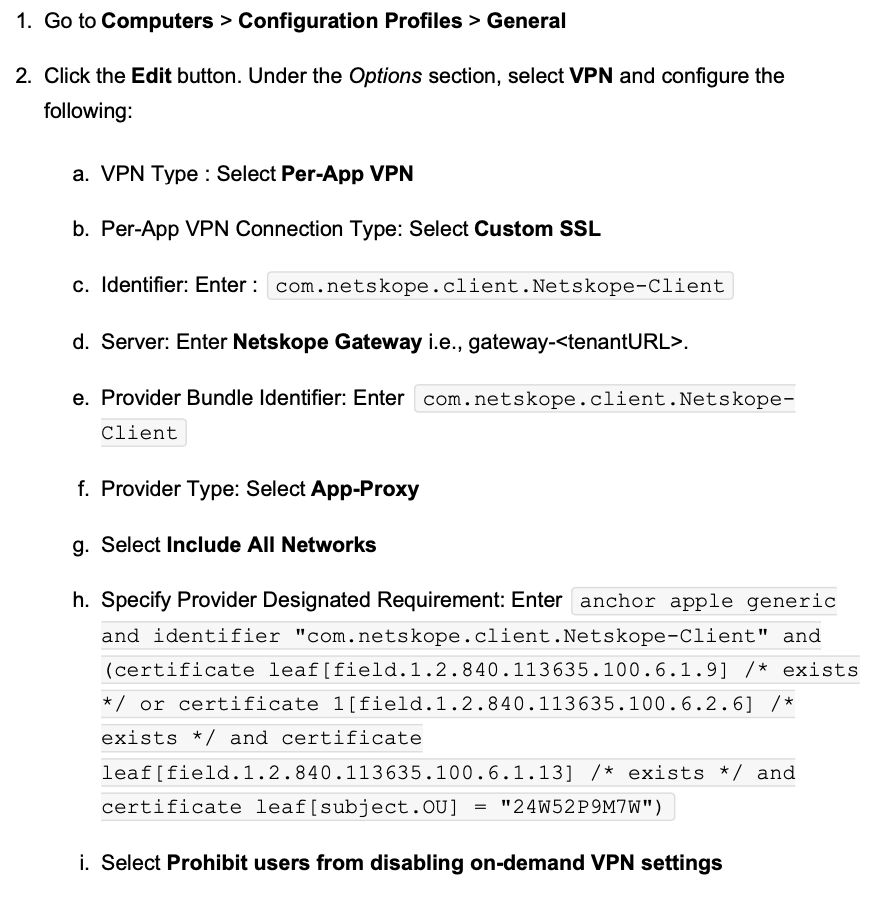
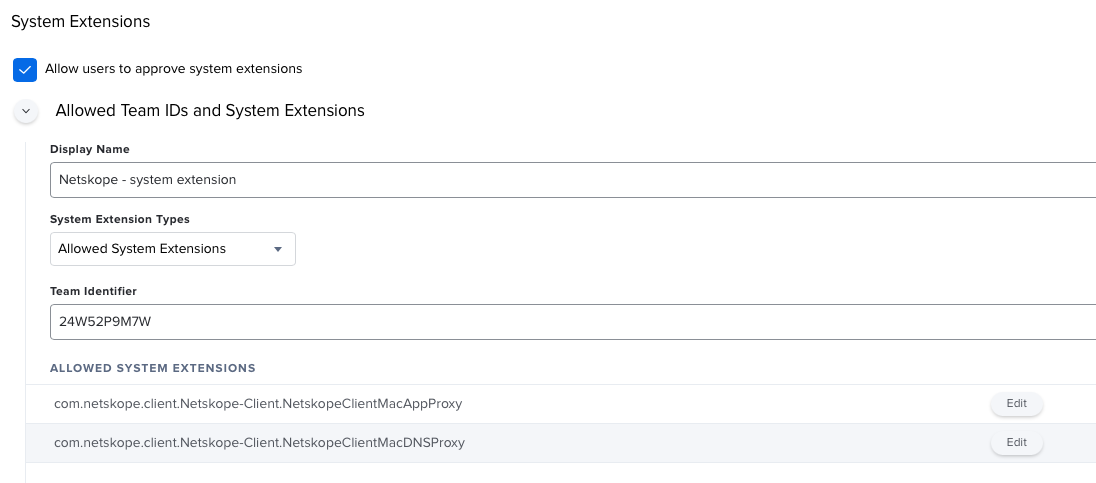
Has anyone seen any issues with deploying Netskope on Big Sur with intel Macs? We have tried both with Kext and Network Extensions and the agent is greyed out and the configurations do not appear. Currently have a ticket with Jamf engineering. We are using the latest version of the deployment script but are having no success. Netskope keeps directing using to their support page for the answer.