Hey folks,
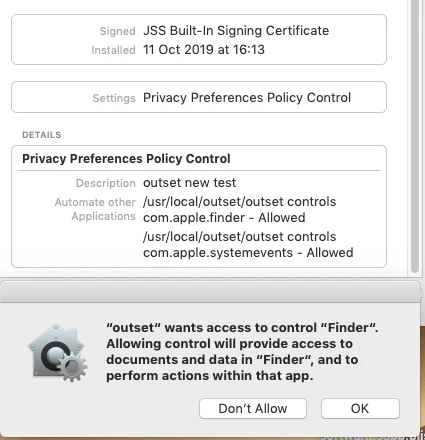
I'm having real problems getting PPPC to work with outset.
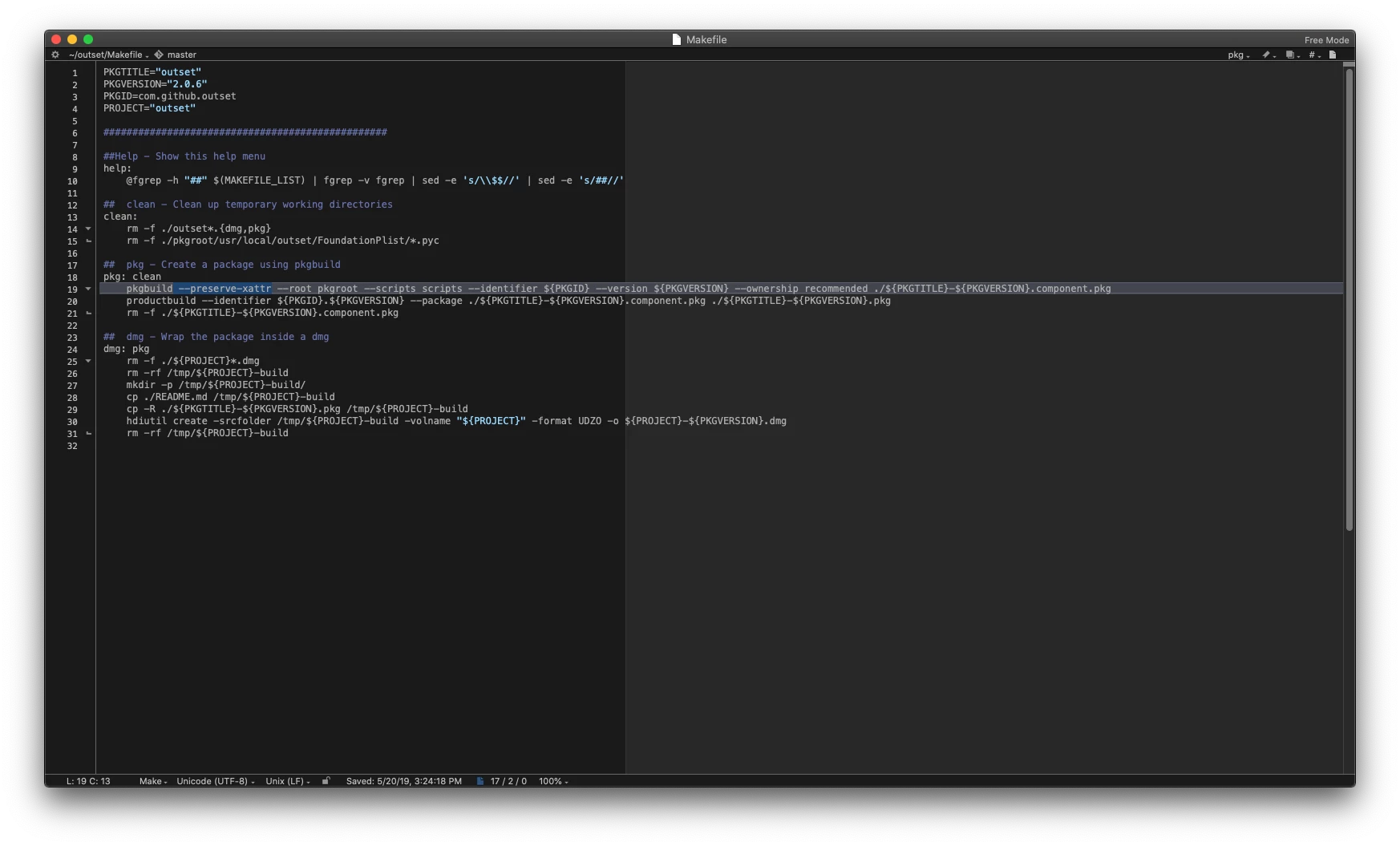
I've followed guides here: https://carlashley.com/2018/09/23/code-signing-scripts-for-pppc-whitelisting/
Everything seems good/signed on my outset script, and I've managed to package it up and deploy it still signed. Various commands on terminal verify this.
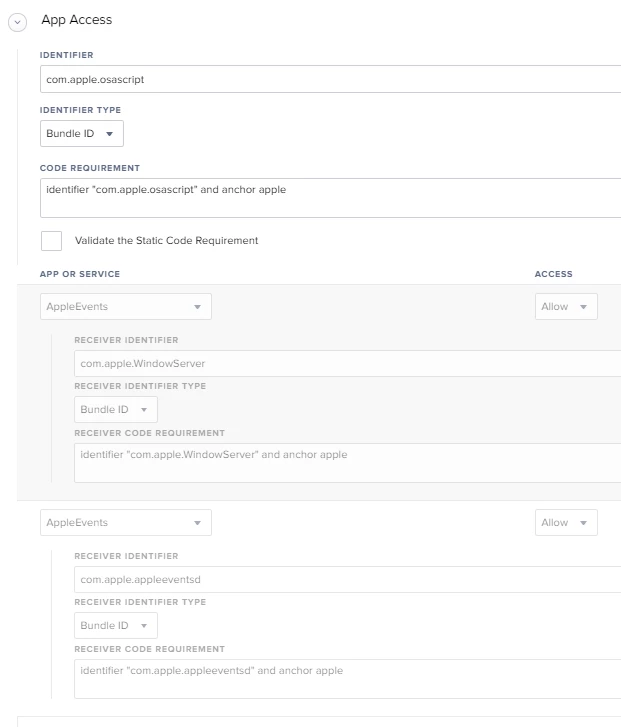
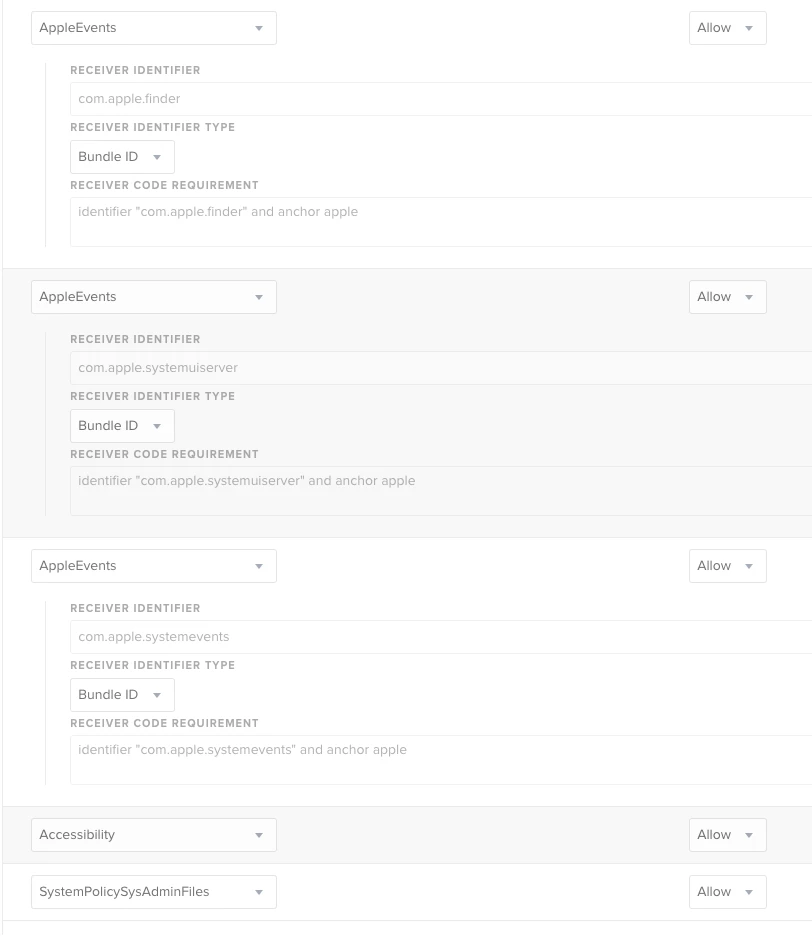
It seems to be the Configuration Profile that I can't get to work correctly.
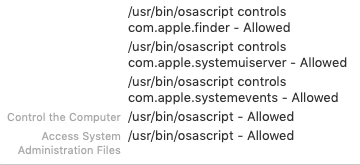
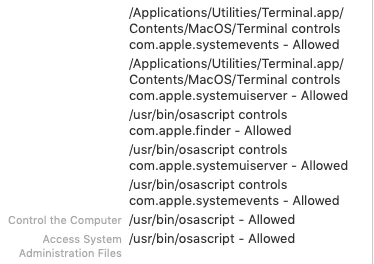
- I used the PPPC Utility to make sure I was creating the settings correctly.
- I allowed FINDER
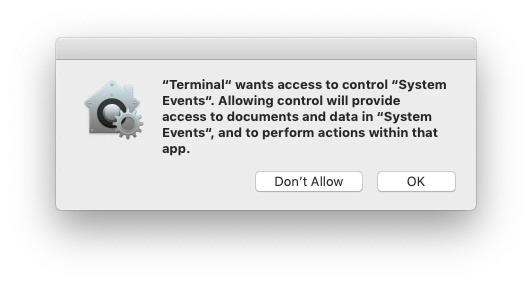
- I allowed SYSTEM EVENTS
Still I am prompted - am I missing something?