Hi Folks,
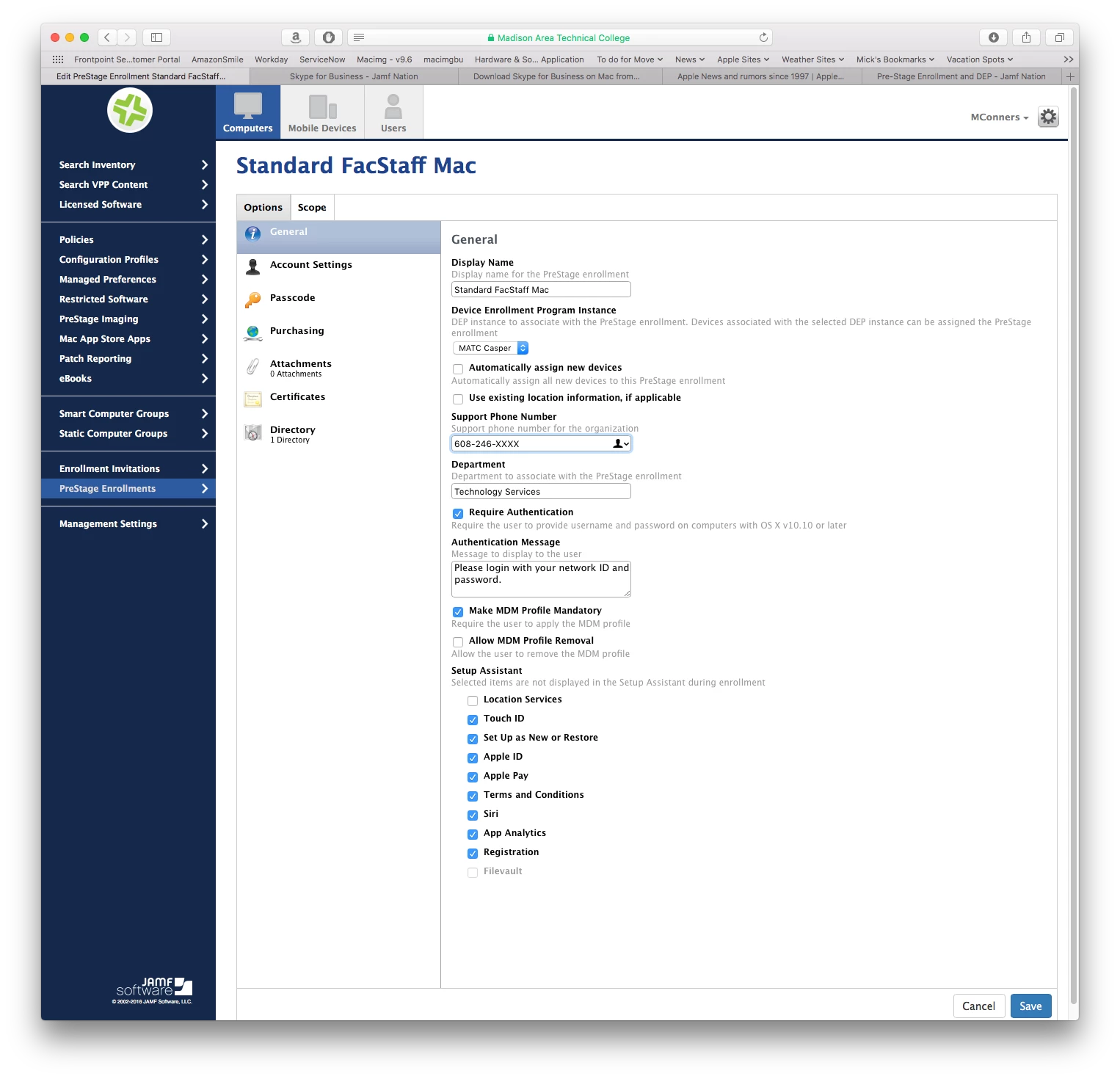
With our DEP up and running, I am trying to find a new work flow with DEP and pre-stage enrollments.
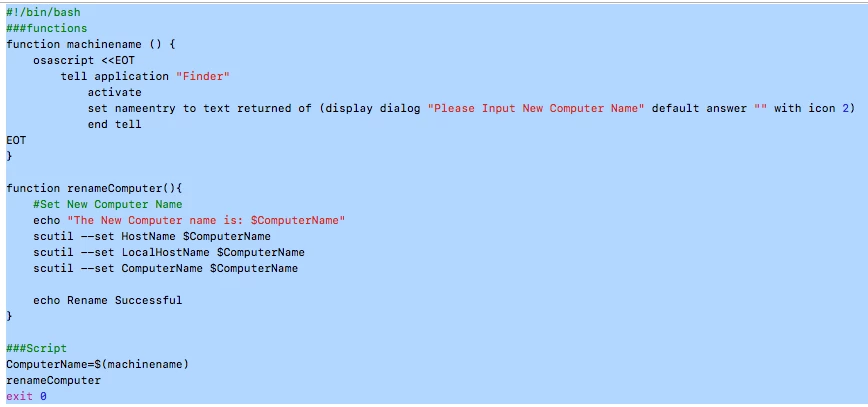
What I have is our pre-stage enrollment working fine, but I am missing a step, post flight script or something else.
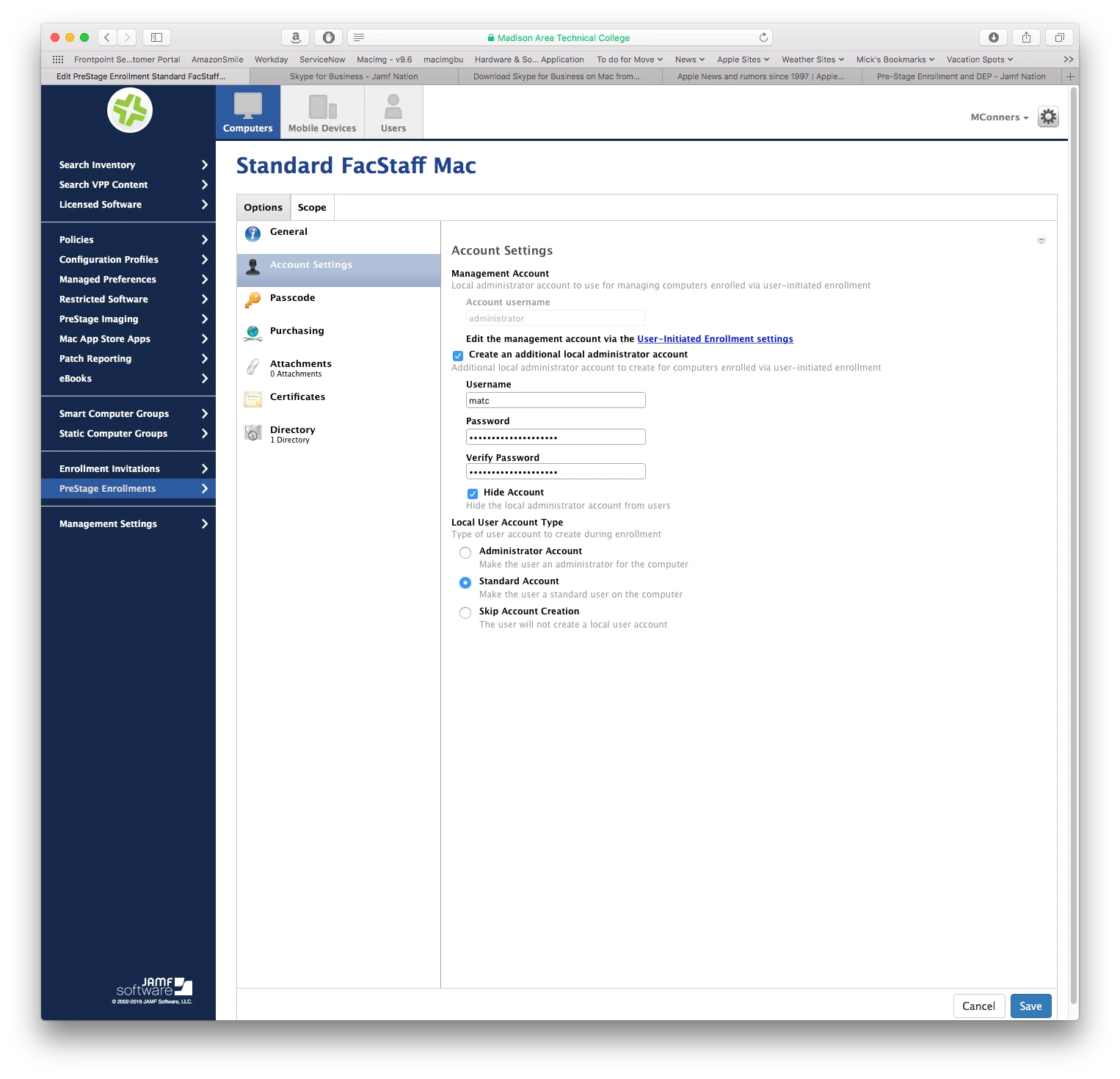
When the computer is booted, the welcome screen appears asking for a language selection. The setup continues through the next couple of screens and when I get to the "create a computer account" screen, I am wanting to skip this or remove it altogether as I don't want our users creating a separate local admin account.
Does someone have a post flight script or something that skips all of this?
I was hoping to use DEP and pre stage enrollments to skip over everything and when the user turns on their Mac, they get everything they need without any input on their end.
Thoughts?