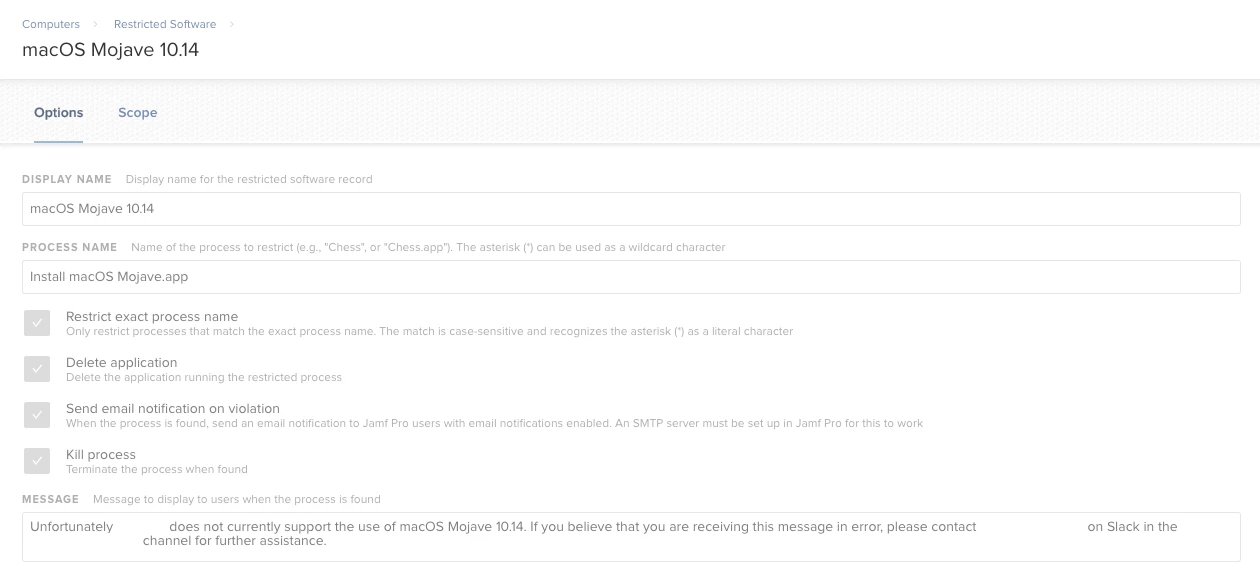
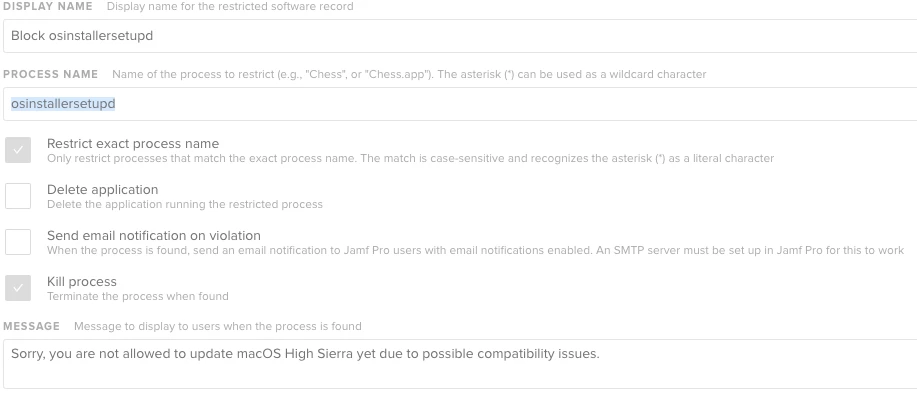
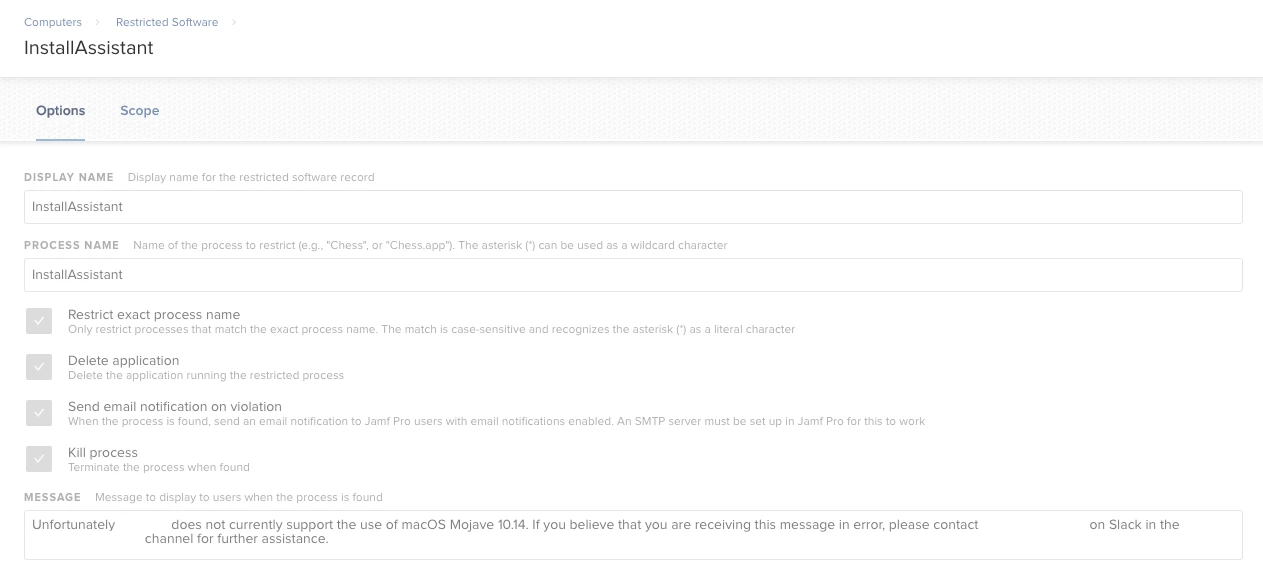
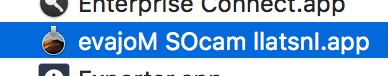
Greetings, all! We're using "Restricted Software" to prevent unwanted in-place upgrades to Mojave when it is released next week. Since this'll be in testing for a few weeks or so before our organization approves the use of the new macOS, I wanted to use this restriction workflow. I just wanted to take a moment and verify the accuracy of the process name that I am using. What're your thoughts? Is this a good educated guess based on previous naming conventions for macOS installers that Apple has used?