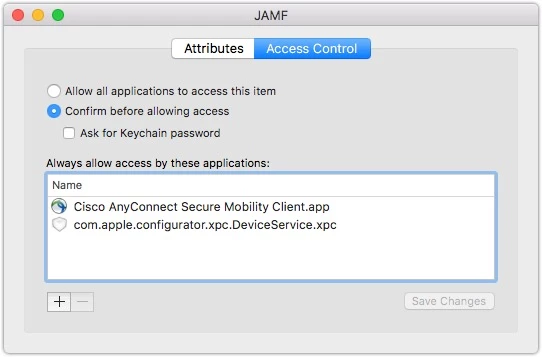
So, I'm using Composer to watch for the install and set the vpn server for Cisco AnyConnect and create a package. I can then also deploy this out to clients and it installs ok. But whenever it goes to connect, AnyConnect wants admin credentials like three times. Has anyone been able to get around this? I do use client certificates to authenticate. I've read that others who have had a similar problem can at least click deny a few times and then AnyConnect will connect. Not the case for me though. Thanks.
Question
Running AnyConnect
 +3
+3Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.