I've been working on an issue that I've seen quite a bit, but unfortunately haven't been able to quite get resolved just yet, so I thought I'd turn to the brilliant folks here to see if I can maybe get closer to a resolution than where I have been.
For a couple of months now, all of our Mac users have begun experiencing the dreaded "Proxy Authentication Required" prompt: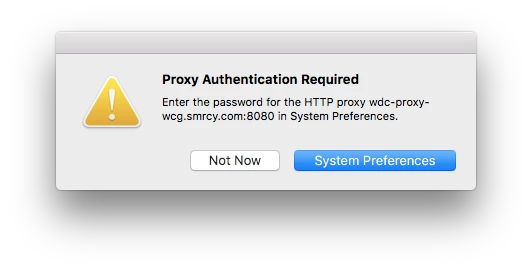
We used to see proxy authentication prompts a lot over a year ago, but I eventually convinced our Security team to enable Kerberos authentication on our WebSense proxy servers, which all but eliminated the proxy prompts through Safari for the longest time. Unfortunately, we've started seeing the system level Proxy prompt interrupting users more and more recently (mainly when the computers return from sleep, but sometimes just at random). For the more technical folks, we can tell them to just ignore the prompt and everything will work fine, but a lot of the users hate being interrupted, especially by a prompt that usually doesn't do anything from their perspective.
For reference, most of our users are not in JAMF yet. We are planning on moving them to JAMF in the next couple of weeks, but for now I'm just trying to get the issue resolved on my machines that are in JAMF so it makes it even more enticing for our users to move over.
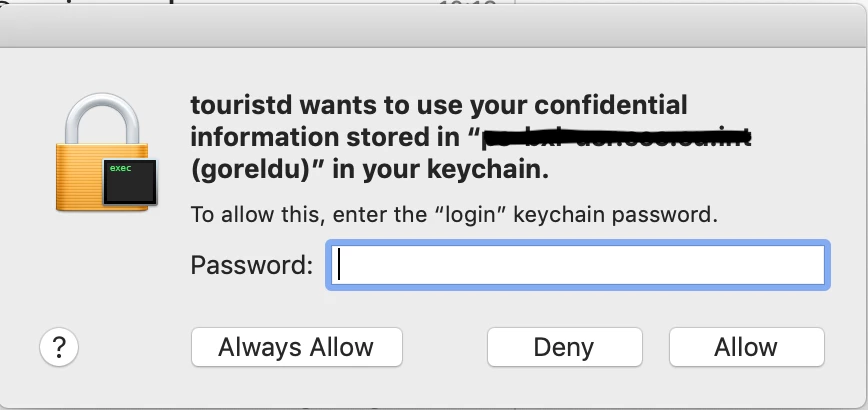
Here's what I'm seeing on my Macs enrolled in JAMF:
User can login to their Mac via cached AD credentials (wireless user) after the computer has been asleep for 15-20 minutes - Note - This doesn't seem to affect our machines when we login / authenticate live via Ethernet. The Mac has NoMAD installed and configured, so the standard Kerberos ticket (krbtgt/domain.com) gets pulled without an issue immediately after the Mac connects to the internal wireless network. The Macs are using a proxy.pac file that is distributed on the proxy server. Sometimes (not every time, unfortunately) the user will see the above prompt when the background apps attempt to connect to internet resources. If the user enters their credentials or hits "Not Now" twice, the prompt will go away and the device will eventually pull a Kerberos ticket for the proxy server automatically (sometimes only after Safari is launched). From that point forward, the active Kerberos ticket for our Proxy server will usually take effect and provide the appropriate authentication, however we have seen the proxy prompt appear even with a valid kerberos ticket for our proxy server.
I'm looking to prevent the users from having the joy of seeing the proxy prompt multiple times a day. From what I can tell, there are two possible reasons we're seeing this prompt. 1 - A background service is attempting to access internet based resources before the Mac has a chance to pull a Kerberos ticket from the proxy server. The proxy server is prompting for authentication, and since we don't have an active / valid ticket, is defaulting back to NTLM - hence the password prompt. 2 - If we have a valid ticket but see the prompt, it's likely because the Mac is using one of the three possible DNS names for our proxy server and the name the Mac chose to utilize does not match the name of the issued Kerberos ticket. Since the kerberos ticket name doesn't match what the server is expecting, it fails the Kerberos authentication prompt and falls back to NTLM.
Here's what I've tried so far:
Configured NoMAD for our Macs. Though we now pull our standard Kerberos tickets automatically, it hasn't seemed to help the proxy issue.
Configured a script that adds the proxy.pac configuration to system preferences on user login. This same script also adds the IP address and preferred DNS name of our Proxy server to the hosts file, as our proxy server (10.x.x.x) resolves to 3 different DNS names.
Verified with our security department that Kerberos authentication is working fine for the Windows clients, and it does work well on the Mac once we have a matching Kerberos ticket for the proxy server.
Does anyone have any further ideas that I could try to suppress this prompt?