Shifting compliance checks left—giving control directly to end users via Self Service
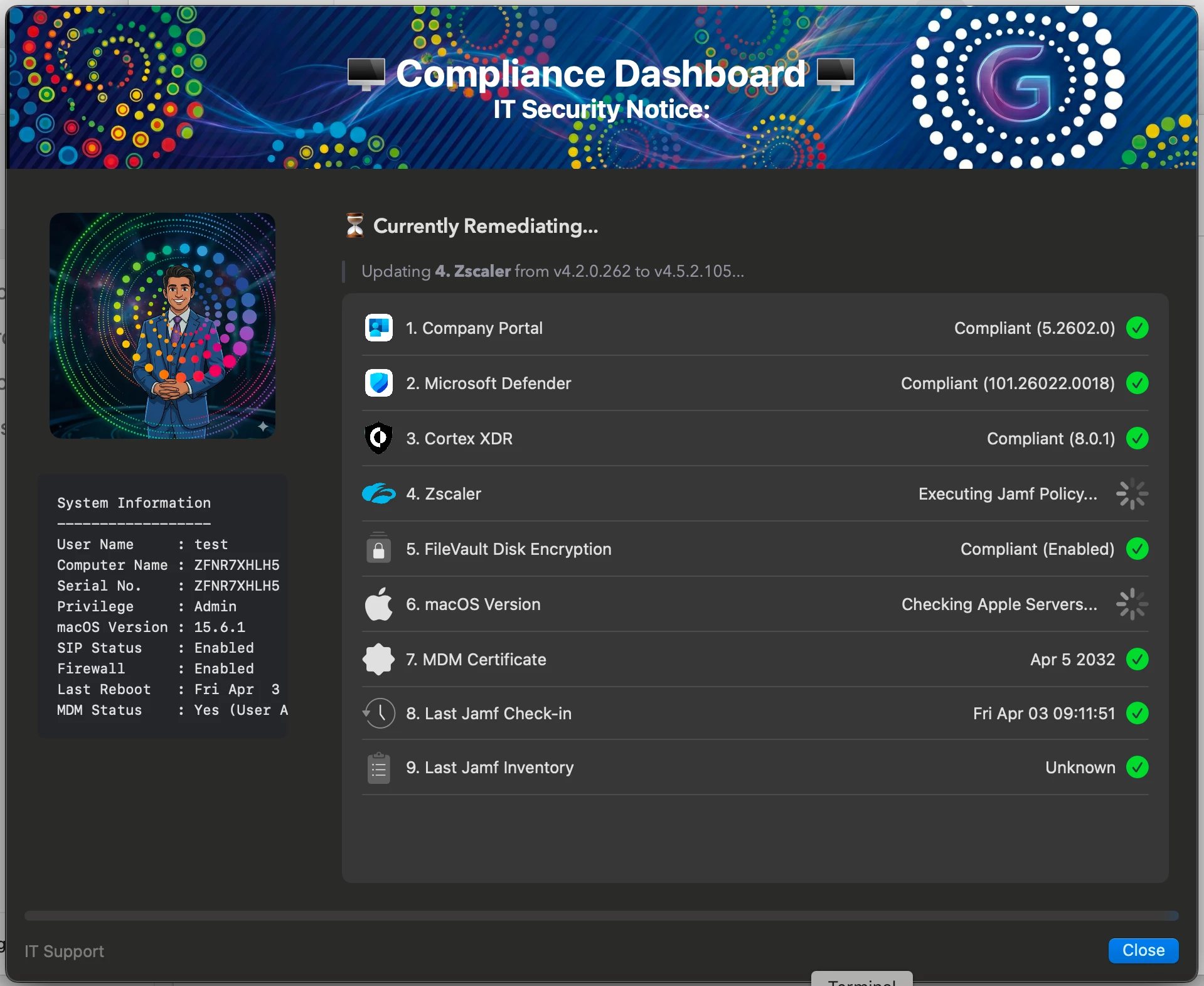
As part of improving endpoint security and reducing operational overhead, I built a macOS compliance dashboard using SwiftDialog and Jamf, available to users via Self Service.
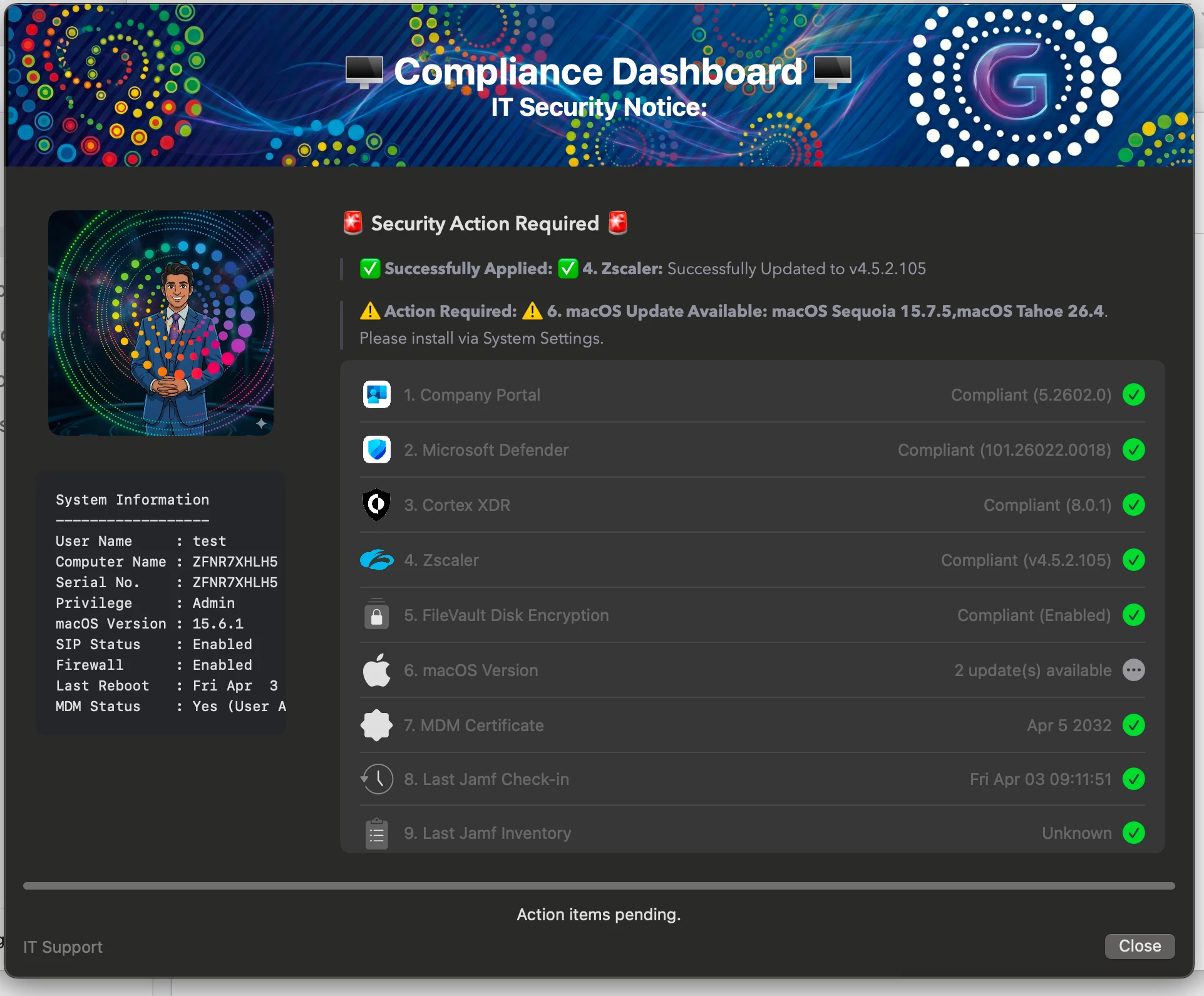
This solution focuses on managing third-party vendor applications that are not updated through Jamf VPP/App Catalog or Installomator. These apps are maintained using internal PKG deployments, with the script enforcing organization-defined required versions.
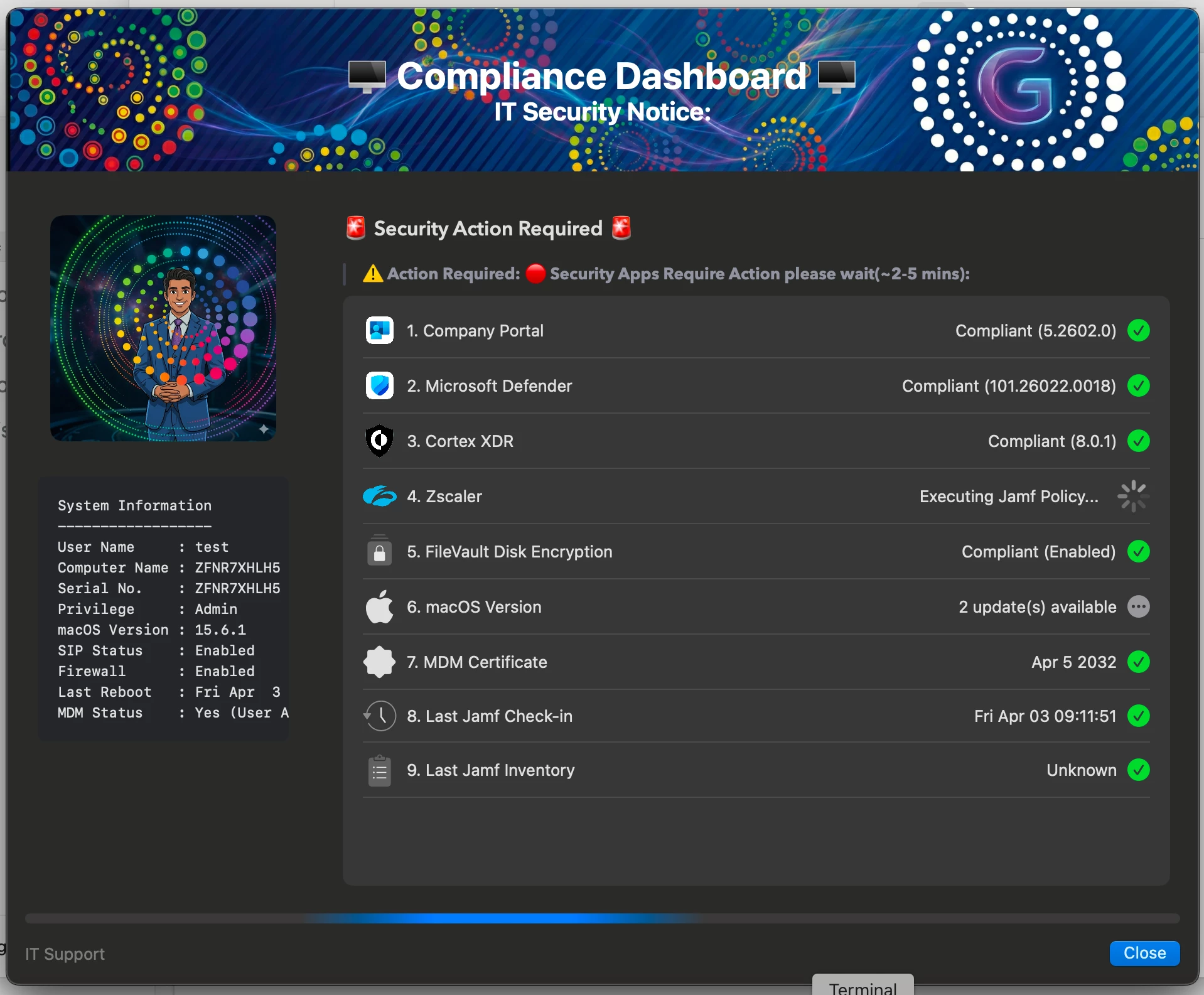
From an admin perspective, the key objective is to eliminate dependency on service desk tickets for compliance. Users can proactively check their device status and remediate issues themselves, without needing to raise a ticket.
The script performs real-time validation of critical security controls such as FileVault, Firewall, SIP, and MDM enrollment, along with verifying that required security applications are installed and up to date.
If any application is missing or outdated, remediation is automatically triggered via Jamf policies. The interactive dashboard provides live updates, clearly showing compliance status, ongoing fixes, and any required user action.
Any suggestions or feedback from the admin community would be really helpful to enhance this further. 👍
Thanks


