How is everyone securely disposing or destroying their own Apple SSD storage units?
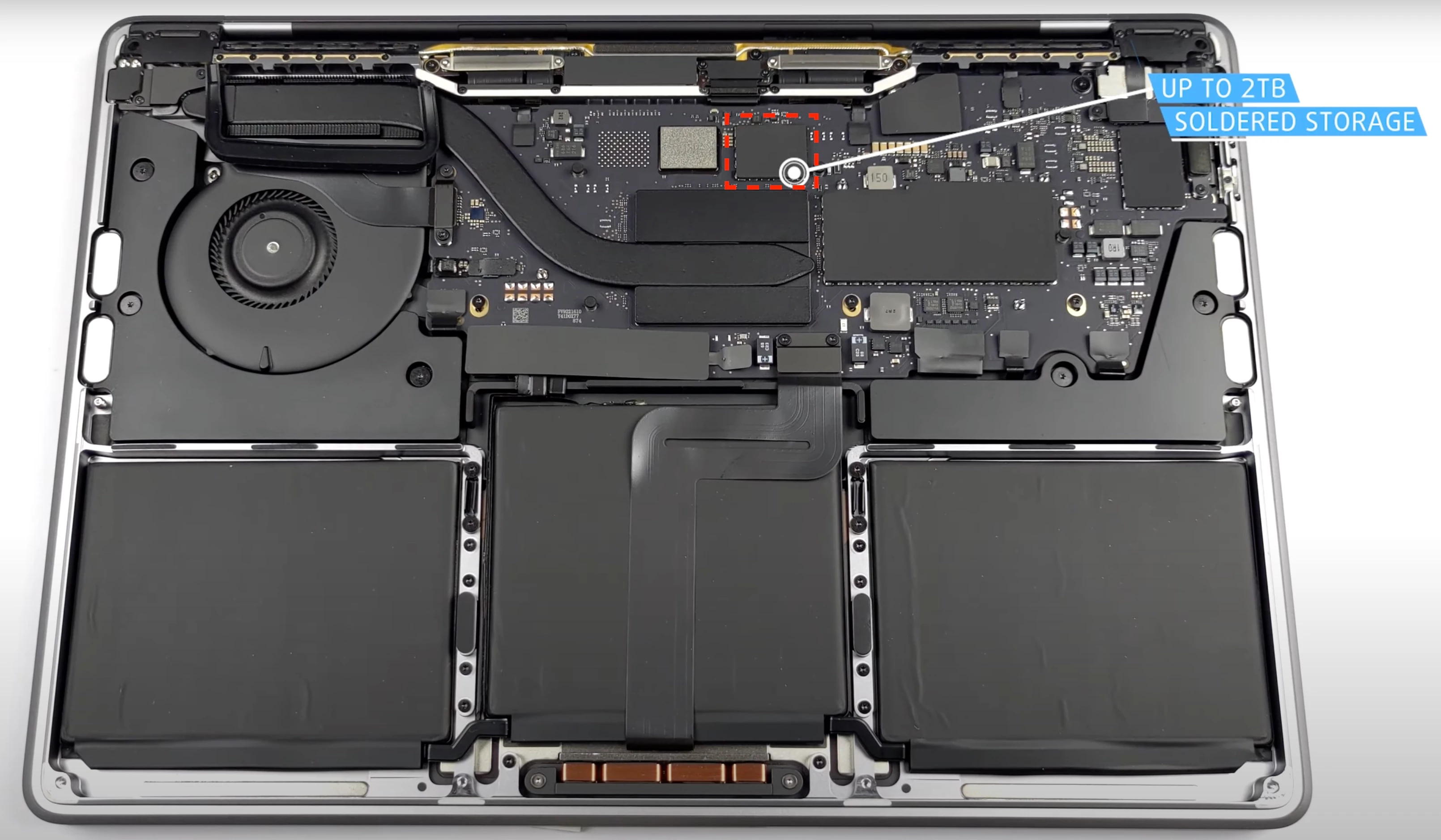
Considering that MacBooks from 2016 to 2022 have an SSD (NAND storage) that is not upgradeable,
and it is not replaceable either, since it is soldered onto the main board:
If a company has decommissioned a MacBook and the device reaches its end-of-life,
the NAND storage cannot be extracted and re-used on a different device.
Also:
- How can businesses assert that their data is securely wiped before device disposal?


