Hi there,
We are trying to raise a good pilot for the Jamf / Intune Conditional Access intergration.
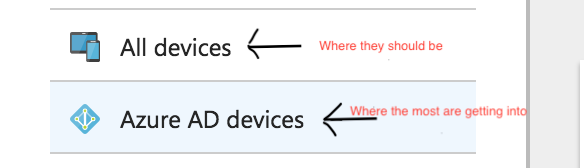
The fact is that 95% of the pilot machine's we try to enrol are enrolling as an Azure AD device and not as an Intune device.
So in this case, as they enrol as an Azure AD, they wont receive the compliance policies etc.
I see many discussions about malfunctioning of the intergration, does anyone have worked a way out for this issue?
- Pilot User have access to the Jamf Native macOS Connector enterprise application
- Connections between JSS on-prem & Intune are fine
- Compliance policies works fine, if an device is enrolled in Intune
- When successful enrolled the JamfAAD gatherAADInfo seems good.
- Tried on a fresh imaged/enrolled machine
- Tried with multiple users
- Successful log-ins reported by AAD for the users in the Company Portal
- Using Company Portal v1.7
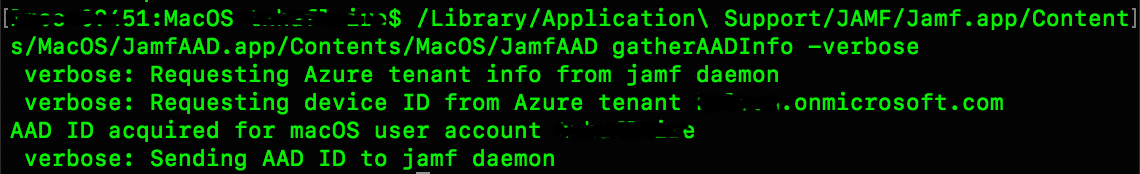
- When not successful enrolled the JamfAAD GatherAADInfo output is like ; No Azure AD Tentant found
Anyone?!
Cheers,


