Hi all
I am new to Jamf.
I am looking to start enrolling our mac fleet into Jamf Pro. (we have v 10.26).
We have AD on prem and bind Macs to a domain.
I have some questions:
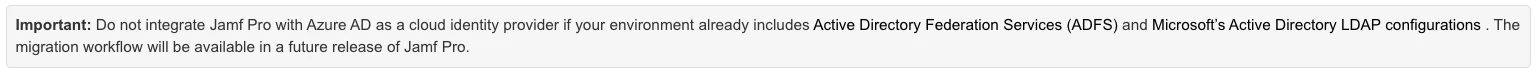
Is it recommended to connect to Azure AD before or after enrolling our fleet?
Is there any downside to connecting to azure AD before enrolling the fleet?
Where does LDAP come in? (I understand version 10.27 is released this week which allows integration into Azure AD. Does this mean it will replace LDAP?
thanks