- Jamf Nation Community
- Products
- Jamf Pro
- AppleID Best Practices
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2021 09:34 AM - edited 07-22-2021 09:49 AM
We have Macs and iOS devices in use by developers and they periodically need to enter an AppleID to install or update apps from the app store or Self Service. Is there a way to bypass this with Jamf Pro? If not, I would like to know how others handle this type of thing on your instance? Like, would it be better to lock down iCloud and any sharing and allow users to use there personal appleids in app store only? Or would it be best to create an appleid for each device and assign it to the user? OR... Would it be easier to create one appleid for every 5 computers or 1 for every 10 ios device?
Really hope someone can help here. Device deployment and App management is, I assume, supposed to be far simpler than what I am making things out to be, LOL
Thanks in advance,
Cooley
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-22-2021 10:40 AM
To the best of my knowledge, there's no way to bypass it for anything installed through the Apple App Store, whether its installed directly from there or if you have VPP licensing and are pushing it through self service (which just redirects to the app store anyway).
We handle it by having our users set up an apple account with their work email address, and leverage Jamf policies/profiles to make sure most iCloud features and backups are forcibly disabled. That way we don't end up with any unexpected activation locks on hardware or company files being backed up to iCloud.
It's not perfect from a security/identity management perspective but it's the best we can get with the way Apple handles app updates. It's ultimately up to the individual app developers whether or not they release in a way we can package ourselves for self service or *only* distribute through the App Store.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-22-2021 03:45 PM
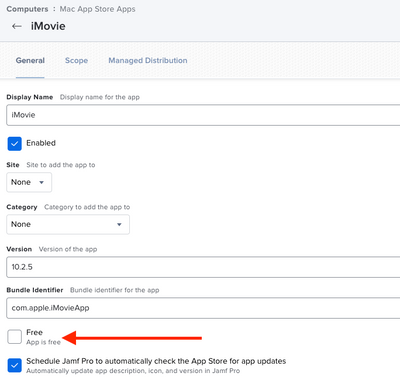
If you are deploying VPP apps through Jamf, and are assigning apps to devices instead of users -
Make sure you have ticked "Assign Content Purchased in Volume" in Managed Distribution, and un-ticked "Free - App is free" on the General tab. We do this for all apps whether they are paid or not. No AppleID required.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-22-2021 10:40 AM
To the best of my knowledge, there's no way to bypass it for anything installed through the Apple App Store, whether its installed directly from there or if you have VPP licensing and are pushing it through self service (which just redirects to the app store anyway).
We handle it by having our users set up an apple account with their work email address, and leverage Jamf policies/profiles to make sure most iCloud features and backups are forcibly disabled. That way we don't end up with any unexpected activation locks on hardware or company files being backed up to iCloud.
It's not perfect from a security/identity management perspective but it's the best we can get with the way Apple handles app updates. It's ultimately up to the individual app developers whether or not they release in a way we can package ourselves for self service or *only* distribute through the App Store.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-22-2021 01:21 PM
Thank you quip_MDavison! Not sure why I didn't consider the Devs just using their work emails. I also have locked down any icloud features so I'm not worried about that. Appreciate you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-22-2021 03:45 PM
If you are deploying VPP apps through Jamf, and are assigning apps to devices instead of users -
Make sure you have ticked "Assign Content Purchased in Volume" in Managed Distribution, and un-ticked "Free - App is free" on the General tab. We do this for all apps whether they are paid or not. No AppleID required.