- Jamf Nation Community
- Products
- Jamf Pro
- Re: Bypassing Restricted Software
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Bypassing Restricted Software
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 04:59 AM
I am having an issue with users being able to copy an application to another location on the local machine and to run application such as Mail, Messages, Facetime, Terminal, and some others. I have created entries in Restricted Software for Mail.app, Messages.app, Facetime.app, etc and set to kill the application each time it is launched, however I was able to copy the file, rename it to Taco in another location, and it ran with no issue. The name of the process in Activity Monitor never changed, so what am I missing? I need to be able to make several applications restricted to students for use, however I do not want to remove them entirely from the MacBook.
If the applications stay in the default Applications folder, the Restricted Software works, we get the app killed and our message pops up.
JSS 9.65
OSX 10.10.3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 05:03 AM
Are the users administrators? If not, use config profiles to whitelist/blacklist folder locations where apps can run. If you only whitelist folders that users don't have write access to, you are limiting what apps they can run (whatever they copy on their desktop won't run). You can use the black list on top of the whitelist to kill apps like facetime, terminal, etc that live within Applications. Way more secure... but only works if users aren't admins.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 06:56 AM
Like it or not, your district has (perhaps voluntarily?) entered into the arms race so common in Education Technology.
While I understand this, and I even understand that, as a tech, your hands are probably tied in this matter, it does explicitly set up an arms race between the providers of the technology and the users of the technology. And so you're left trying to engineer a technical solution for what is really a social/human problem.
Were I tasked with setting up a "locked down" OS X environment, I'd actually look at something like Faronics DeepFreeze. Or I'd build a modified OS X installation that doesn't even contain the Apps that are being problematic for you (Mail, Messages, FaceTime), and the machines would stay completely static for the full school-year and be re-imaged each Summer. Yes, you can do a lot with Restricted Software in Casper and MCX/Managed Profiles to limit Application launching, but it's a patchwork fix that your barbarian students will likely find routes around.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 07:09 AM
What you're missing is you need to check the "Restrict exact process name" box for each of your Restricted software items. Renaming the app bundle name is or was, a common way around the Restricted Software block, but checking that box means it ignores the .app bundle name and looks for the process running, which can't, incidentally be renamed, or more accurately, it can be renamed, but the app won't work afterwards. So they can rename the app in the Finder all they want, but when the app launches it will still be seeing the
Taco.app/Contents/MacOS/Mail
process, or whatever it is you're looking to block.
You could also look at the whitelist/blacklist folder location setup that @CasperSally mentions, as this will stop them from even running the app from any locations other than what you specify in your whitelist. But test it out very thoroughly before deploying it. A lot of folks have run into problems with it due to the fact that some applications like to have processes that run from strange locations, which you may not have in your whitelist and the students will see errors when that occurs. Ultimately, if you do the whitelist/blacklist stuff, you may end up in a game of whack-a-mole as you try to plug up holes or enable locations where some developers like to run processes essential to their software from.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 09:58 AM
Thanks for the responses everyone. I do use DeepFreeze also on some of my Macs, we were just trying to find a way with Casper as I want to minimize my management. Trying to keep down on the piece work of some things here some things there. It is a constant game of Cat and Mouse with the students as you know. I do not want to remove the applications completely because we do have some use for them at times with certain classes that can be trusted. I would make a local admin at that point and allow them to run the application.
As far as checking off the box for "Exact Name", I have done so already and am still able to run the applications as a standard user after copying the messages.app, mail.app and facetime.app to the desktop and renaming them. Even with the process name not changing, we are still able to run all of the applications we created entries for under restricted software. The setting works fine when the app is tried to run from the applications folder so I know my JSS is doing something. I get my custom message as well. It is only once it is moved out of the applications folder.
I was going to try the white/black list method, but was trying to see if I could do it this way first.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 10:09 AM
@rfjhulse Are your Restricted Software items set up like "Mail.app" or just "Mail"? I believe it would need to be the latter and not the former, especially if using the restrict exact process name option. Just use "Mail" or "Messages" for example. No .app at the end of the process name.
Also don't use a path, such as "/Applications/Mail", but that's probably obvious and I doubt that's what you're doing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 10:30 AM
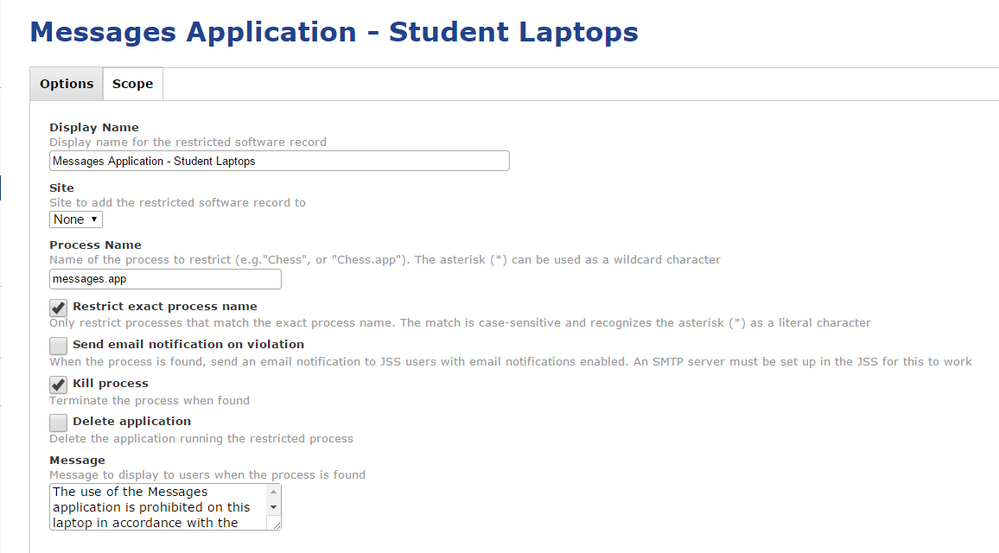
I was using .app after each as I thought since it said "exact" name I would have to do so. Here is a screen shot sample of my settings.
It is the exact same for Message, Mail and Facetime, just with the names obviously changed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 10:42 AM
Try them without the .app extension as I mentioned. The problem with using something like Mail.app is that this would only be true if the application name in the Finder remains the same. Activity Monitor and/or the command line don't see the .app part when its running. Since you said the students are renaming them, this bypasses the restriction. It no longer sees, for example, Mail.app running, but sees Taco.app (using your example) so of course it doesn't stop the application.
Think of it this way, the difference between Mail.app and just Mail is the following-
Using "Mail.app" it only sees:
/Applications/Mail.app(or any path leading up to "Mail.app")
If this is renamed it then only sees:
/Applications/Taco.appand as such doesn't get blocked.
Using just "Mail" along with the Restrict Exact Process Name box it sees:
/Applications/Mail.app/Contents/MacOS/Mail(or any path leading up to "Mail")
Renaming it in the Finder it still sees:
/Applications/Taco.app/Contents/MacOS/Mailand it gets blocked.
Does that make sense now?
Remove all the .apps in them and see how they operate then. Make sure to do a sudo jamf manage from Terminal on your test Mac to make sure its pulling down the adjusted restriction before doing any tests though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 11:18 AM
Makes perfect sense.
I actually had tried it that way as well. I just did it again and now I am able to launch the messages app from the Applications folder as well as the Taco.app on the desktop using a standard user login (non admin).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 11:23 AM
@rfjhulse Sorry, I'm confused. You are able to launch them from any location or not able to? If the former, then something is broken, or may still need some adjustment. If you meant the latter, then its working.
We use the process name or the executable inside the app bundle all the time and it works to block things we need to, regardless of where they are run from or how the app bundle is named in the Finder.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 11:38 AM
Sorry for the confusion, I am able to launch the apps now from anywhere, so yes, it appears something may be broken. I left the .app after the mail, and changed messages and facetime for testing to see if it made a difference. Now I am able to launch all three of them with no issue from either location. It is odd because nothing else was changed. My group and its membership for the scope is still the same, I ran the sudo jamf manage command as well. I am going to reboot my JSS and my macbook to see if that fixes anything
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 12:33 PM
That's really strange. As I mentioned, we have several Restricted Software items with just the process name in them (no .app) and they work fine. Not sure why they aren't working for you.
If you're not able to get it to work I'd suggest getting with your JAMF account manager to see if they have any ideas.
Out of curiosity what version of the JSS is this being tested on?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 12:52 PM
Hey @rfjhulse,
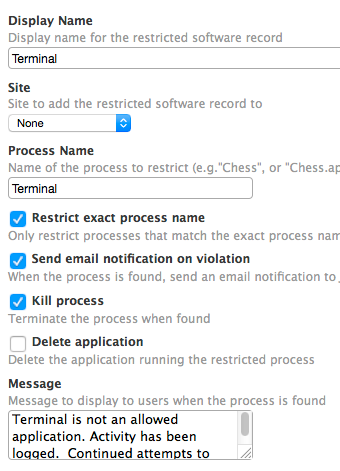
We use Restricted Software for Terminal, Facetime, Messages, etc. We use similar settings:
We just performed some testing on a 10.9.5 client. We copied Terminal out of Utilities and pasted it into the Users Applications folder. We ran it as Terminal to ensure our policy was still working, it was. We then renamed it to Taco and attempted to open it again. Same result, the application was closed and the message was displayed.
The only difference in our environments is you are using 10.10.3.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-10-2015 02:26 PM
@rfjhulse Have you tried using "Messages" instead of "messages"? I noticed in your screenshot that the case-sensitivity might be causing issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-18-2019 11:46 AM
I'm taking another stab at blocking this. Looking at the activity monitor for messages.app, I see: com.apple.iChat as a potential keyword to home in on. So I'm trying to block this as well as messages. It looks promising from my test machine.