- Jamf Nation Community
- Products
- Jamf Pro
- Re: JamfAAD - Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
JamfAAD - Issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-31-2021 05:25 AM
Hi All,
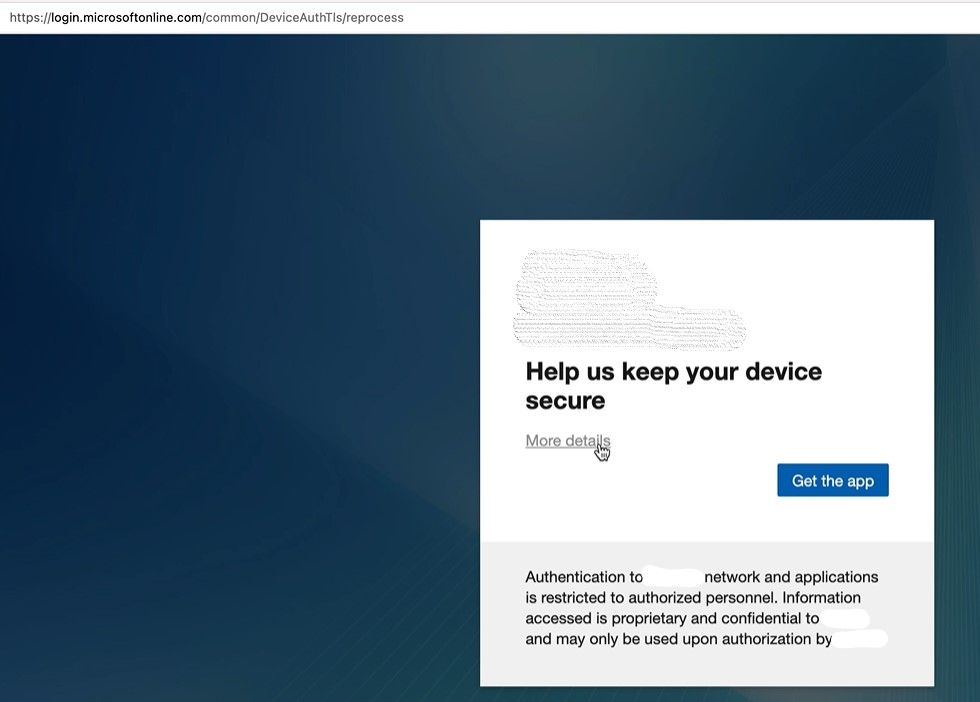
One of my user is getting the below pop up and after clicking on Get App it is redirecting to a weird broken link. This user is already registered in Intune/Azure AD and it just randomly started to happen. I am mostly curious about the link. Any ideas where this is coming from?
- Labels:
-
Microsoft Intune
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-24-2022 08:29 AM
With the Webview config profile & the Microsoft Enterprise SSO plugin together deployed, we haven't received one complaint since. Works really well!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-24-2022 10:51 AM
Sorry, I haven't tested Microsoft Enterprise SSO plugin yet. Will review Microsoft doc and try it next week. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-27-2022 09:24 AM
Sounds like a dream come true!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-18-2022 10:00 AM
@vcherubino Thank you for the tip!
For those unaware, there is a documentation from Jamf about how to build the Configuration Profile (Jump to the 'Configure JamfAAD to use WebView' section):
https://docs.jamf.com/technical-articles/Troubleshooting_Microsoft_Azure_Login_Using_JamfAAD.html
I'm trying it out and see if it works. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-19-2022 06:54 AM
I can confirm webview is working with device registration when utilizing this config profile with the custom settings. The big question i have is if i deploy this config profile out to my fleet now will that suffice for when JamfAAD goes nuts after a pw change or inactivity etc, or does the device have to be completely re registered first?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2022 07:10 AM - edited 07-19-2022 07:12 AM
From my experience, deploying new profile will be suffice. Existing enrolled Macs won't be impacted. New users will have better experience registering their device. I would recommend two additional things to minimize JamfAAD prompts:
-Increase inactivity in macOS Connector to max (120 days)
-Plan schedule cleanup for macOS devices in Azure. Support case was lodged Microsoft where Intune compliant was not able access company resources. We had to delete old Mac devices (associated to users in Azure) which helped. Here is link to doc from Microsoft [Cause 6] - Troubleshooting Jamf Pro integration with Microsoft Intune - Intune | Microsoft Docs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-19-2022 07:19 AM
That increase of the inactivity in the macOS Connector to 120 Days sounds perfect, can you provide any documentation on where to set this(or is it in the Microsoft Doc you linked previously)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2022 07:32 AM - edited 07-19-2022 07:33 AM
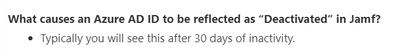
You may set in Jamf portal by going to Settings > Global Management > Conditional Access. Scroll down to bottom and there should be an option for Allowed Duration Of Inactivity. I believe, default value was 14 days.
This doc from Microsoft has helpful information for troubleshooting - Support Tip: Troubleshooting issues with macOS devices when using Jamf/Intune integration - Microsof.... I would recommend bookmarking it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-11-2022 12:50 AM
Sorry to resurrect an old thread, but since we all shared this experience, this is the perfect place to share a related revelation. The original problem is more or less solved by now, with the webview option and both Edge and Chrome being much updated since, and in macOS 13 SSO integration with Company Portal.
However, I still have a few users, five as far as I know, whose computers will occasionally lose conditional access and when I check, their devices are removed from Intune, but present in AzureAD and Jamf (of course!). The temporary solution is to re-register them in Jamf Self Service with the special launch of Company Portal.
However, here's the interesting parts: They are all still using 13-inch Retina MacBook Pro with TouchID (Mid 2017). Five or six users with this model of Mac, in an environment with 85 Macs total, out of which only 15 active devices are this model. The devices are user-enrolled, no prestage or DEP/ADE. Affected devices were all enrolled with Jamf in 2019: Three in January, one in March and one in May.
I haven't figured out the significance, but the correlation is too strong to be random chance, so I wanted to check if any of you are still having this issue, and if you have the same models in use.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-06-2023 02:03 AM
Hi Everyone,
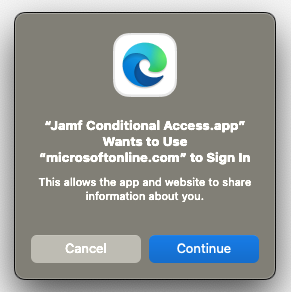
My default browser right now is Chrome. but I don't have a problem with that. However, the following screen appears in some of the users I have installed Company Portal. When it approves this, it redirects to a page and asks the user to login to Microsoft. This happens randomly and is very disturbing for us. Does anyone know why this is happening and how to fix it?