- Jamf Nation Community
- Products
- Jamf Pro
- "JamfAgent would like to access your contacts" Mes...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
"JamfAgent would like to access your contacts" Message After Upgrade to 10.7.1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on
10-02-2018
01:54 PM
- last edited
Tuesday
by
![]() kh-richa_mig
kh-richa_mig
Hello,
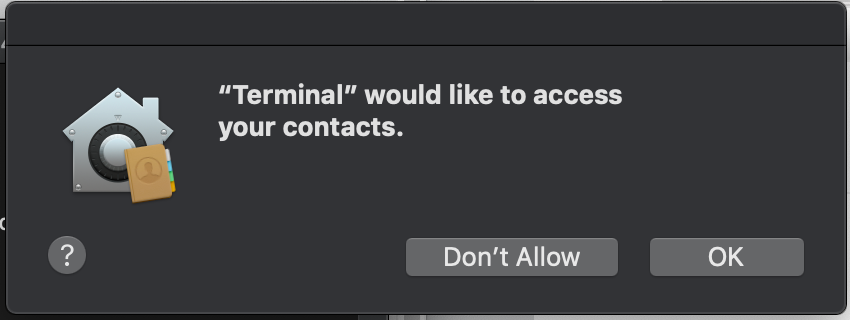
We just upgraded our Jamf Pro server to 10.7.1. After doing so, we noticed that our computers running Mojave ask the user for access to several types of data the first time inventory is updated. This includes contacts, calendar, and photos. Our users will be extremely uncomfortable with these messages, and I'd like to know how to turn that off, or else we will need to revert our Jamf server to an older version.
For the time being, I've had to turn off our policy to automatically update inventory, which obviously is not ideal.
See the screenshot below for an example of what this looks like when running "sudo jamf recon" from the terminal. When this runs as part of a policy, "Terminal" is replaced with "jamfAgent"
Thank you for your insight!
Ian
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-02-2018 02:31 PM
Just an update to this, I found the same issue after reverting to 10.4.1, but only when running the first inventory update from the terminal. It did not happen when updating inventory in the background. Does anyone have more information about what might be happening?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-02-2018 11:54 PM
Hi,
same issue on our systems (JSS 10.7.1 and Mojave). Like you said, only when starting in terminal and then only the first time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-03-2018 03:30 AM
It's got to do with the updated security policy by Apple in Mojave (https://developer.apple.com/enterprise/documentation/Configuration-Profile-Reference.pdf). Sounds like it was added last minute so things are not setup to work fully in v10.7.
The Jamf agents have been approved to run since you have v10.7.1 installed (you can verify this in sys prefs/profiles/privacy Prefs Policy) but it's very likely that you have scripts or policy's that calls individual apps (in this case Terminal) which hasn't been approved yet.
Trouton did a write up on it which seems to be the one everyone is referring to (https://derflounder.wordpress.com/2018/08/31/creating-privacy-preferences-policy-control-profiles-for-macos/).
JAMF stipulates that it will be included in a later version of JSS (https://www.jamf.com/jamf-nation/articles/553/preparing-your-organization-for-user-data-protections-on-macos-10-14)
I'm working on a similar issue but haven't rolled out any changes as yet. Jamf released a tool (https://github.com/jamf/PPPC-Utility) which allows you to roll out approved app configs but I'm trying to wrap my head around "which and what" needs to be approved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-03-2018 06:36 AM
Thanks, @tjhall! The jamfnation article you linked seems to have the most relevant information in it. It looks like we can use a configuration profile to pre-approve these permissions for 10.14 computers. I'll do some testing with that and report back on how it goes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-09-2019 11:34 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-09-2019 10:22 AM
Bump
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-09-2019 10:59 AM
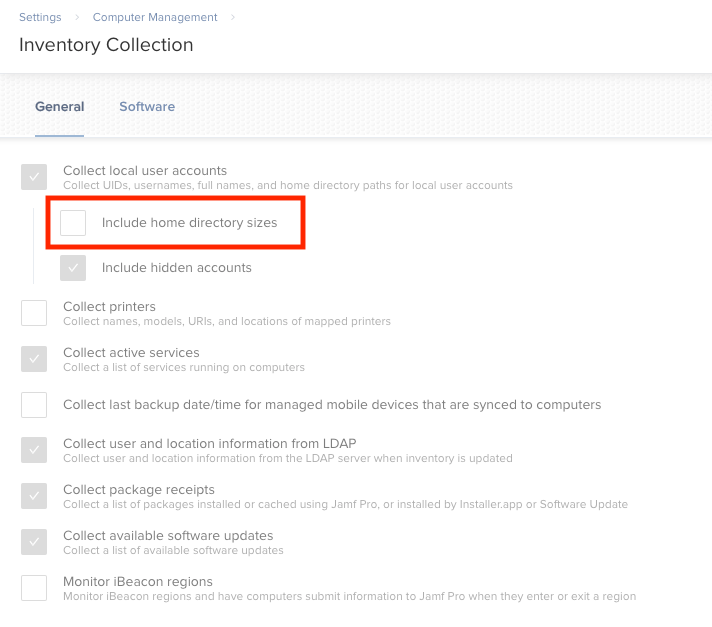
@kevin.v The quickest workaround is just unchecking "Include home directory sizes" in your inventory collection settings. Otherwise, you'll need to create PPPC profiles to whitelist this behavior so users don't get those messages.