- Jamf Nation Community
- Products
- Jamf Pro
- Re: CyberArk EPM Deployment
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
CyberArk EPM Deployment
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on
07-14-2020
08:16 AM
- last edited on
03-04-2025
08:19 AM
by
![]() kh-richa_mig
kh-richa_mig
Hey there - does anyone else use CyberArk EPM (end point management) to manage admin rights and third party app installations more easily? We're beginning to roll out a test bed in my company, and I'm working on the mac deployment.
CyberArk provides some instructions for deploying here, but I'm struggling with them. It seems to want the zip file deployed as the package, and there is no pkg, but I've never used a zip file as an installer through Jamf. Anyone got this deployed? Or have any insight on using zip files to deploy apps?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 08:25 AM
We actually did a demo with them last year and setup a test environment and will be purchasing soon. From what I remember you had to log into the EPM console and export the macOS agent install package, we then used that, and this script in a policy to do the install:
#!/bin/sh
installer -target / -pkg /Library/CyberArk/CyberarkEPMAgent.pkg- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 08:45 AM
Interesting, so getting into your EPM console gave you a pkg to install? So far my security team has just given me a zip file, I'll hit them up and see if they can pull a pkg from another source.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 08:52 AM
What's in the .zip? If you extract the .zip do you have the EPM installer .pkg?
The link you posted shows how to download the package:
"Download package
In the EPM Management Console, select My Computers and then select Download Agent Installation to display the Download Agent Installation Package window.
Select the relevant MSI installation file or macOS installation package, then enter a key of your choice and click OK. You will use this key again during installation.
Copy the relevant MSI installation file or macOS installation package to a shared network."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 12:30 PM
@rtylerdavis @brianmcbride99
From what I'm seeing, it's an app not a package. I'm in the same boat. Documentation is very limited. I'm not sure why it's asking for the admin/pass and using sudo in the command unless that is the admin/pass it is going to rotate. However, the documentation just states that's what will be used to install the app. See here:
https://docs.cyberark.com/Product-Doc/OnlineHelp/EPM/Latest/en/Content/Installation/Manually_Install...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 12:40 PM
I have scheduled the test install for next week but based on what I read so far, you download the installer via CyberArkEPMAgentSetupMacOs_11.6.0.449(the_name_of_your_set).zip. Inside this zip there is a "CyberArkEPMConfiguration.json" and an "Install CyberArk EPM.app.zip". Extract the "Install CyberArk EPM.app.zip" and you get the "Install CyberArk EPM.app".
Drop "CyberArkEPMConfiguration.json" and "Install CyberArk EPM.app" onto the target system in the same folder, then install via
"pathtoinstaller/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller" -configuration "pathtojson/CyberArkEPMConfiguration.json"If you want CyberArk to rotate local passwords or carry out other admin tasks you need to specify a local user account that has a secure token.
"pathtoinstaller/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller" -configuration "pathtojson/CyberArkEPMConfiguration.json"
-adminUser localuserwithsecuretoken -adminPassword localuserwithsecuretoken password- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-14-2020 01:55 PM
@DirkM According to this documentation, you only need to grant the CyberArk EPM user a SecureToken if the account you want to rotate already has SecureToken enabled. https://docs.cyberark.com/Product-Doc/OnlineHelp/EPM/11.3/en/Content/EPM_PET/Install_CredRotation.ht...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-15-2020 10:59 AM
I am struggling with these new releases that are a .app instead of the pkg
The requirement to pass an admin user/pass, when I am already deploying the app with a tool like jamf, is not just asinine, but asiten and asieleven.
If you read their documentation or use their scripts, they mention a command argument, -withoutPwdRotation which is supposed to get rid of these admin prompts....well, if you run with that argument, it returns an error about an unrecognized command. But it is in their documentation......
We have a ticket open with them. One of their first suggestions was to go on jamf nation for tips on deployment...not something I ever want to hear from a vendor. The Windows deployment was as easy as adding the command switches to the MSI, I don't know why they had to reinvent the wheel with this one
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-16-2020 08:44 AM
@hdsreid I had some trouble with getting this installed for the first time. I'm not using -withoutPwdRotation so I can't comment on that. Can you just leave that option out entirely since you already installed the app and you are upgrading it. Their documentation is weak at best. It's confusing, laid out poorly, and some steps like creating a Config Profile to allow installation which should be first are listed as the last step.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-16-2020 09:18 AM
@spraguga it still wants me to pass an admin user/password at the command line, and I would really not like to do this. we don't even have a token set to "protect" the set. i don't get it lol
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-28-2020 07:54 AM
Working on this as well. Instructions from CyberArk say to drop the .zip file into JAMF Admin but every time i try to add it to Admin it throws up an NilObjectException not handled error. When i try what @DirkM suggests i get errors saying invalid admin credentials even though i know the username and password are correct and my admin account has a secure token. Who's got the solution??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-28-2020 10:53 AM
@Kyuubi what version of CyberArkEPM Agent are you trying to install? We are on 11.5 and finally got an update from our ticket, apparently they are aware of the issue related to admin credentials. We were given a patch to install on the EPM server and then told to generate a new package, however the team managing Cyberark has not done this yet, so I cannot confirm if it does solve the issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-28-2020 11:18 AM
Our cloud instance is at version 11.6 and the macOS client is version 10.6.1.487. The downloadable zip contains the Install CyberArk EPM.app and a CyberArkEPMConfiguration.json which has to be in the same location as the app.
I can install the client using
sudo /pathtoapp/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller -k installKey -withoutPwdRotationwhere install key is the string entered when downloading the zip.
So far, so good. I cannot get past the "System Extension Blocked" though, even though I have configuration profile that has the Team ID DF8U2CCCD8 as approved kernel extension as well as allowed system extension. Once I approve manually it seems to be working.
Does any of you have a config profile that surpasses the System Extension Blocked on 10.15.6?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-29-2020 01:17 PM
@DirkM this is where I am at as well at this point. Looks like its time to push back on support some more...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-30-2020 07:50 AM
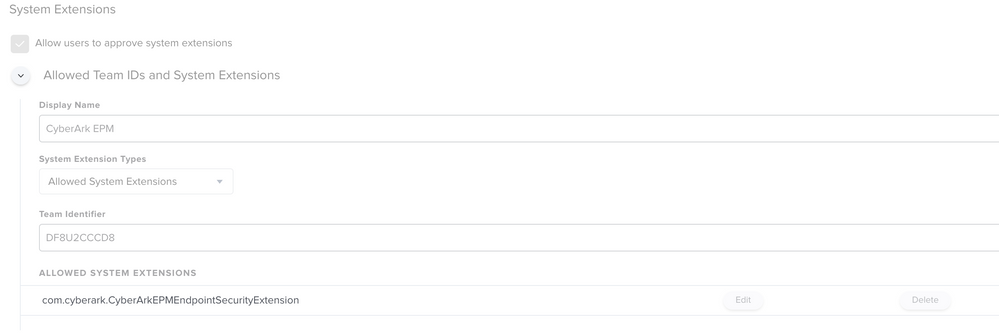
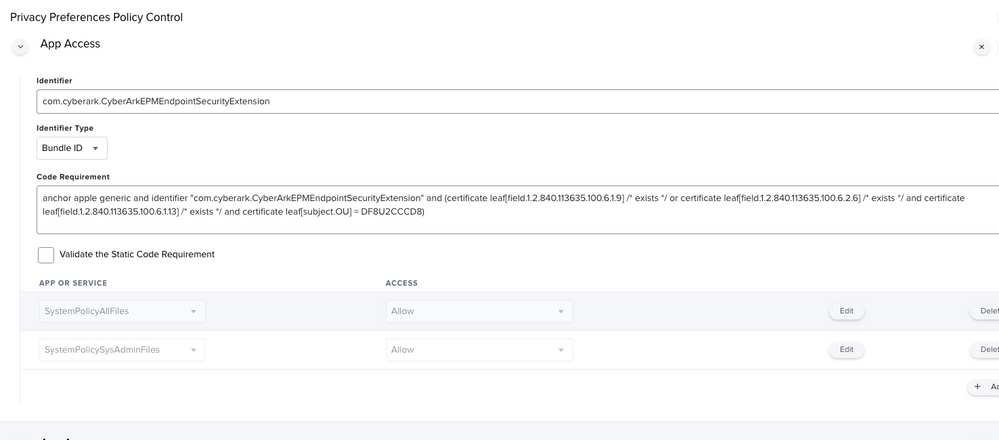
I struggled with the system blocking as well, just randomly trying things until I got it working. Their documentation is terrible. In my testing you MUST add the system extension for this to work and it's not the one stated in their documentation.
Here is how I got it working:
1) Approved kernel extension with bundle id: DF8U2CCCD8
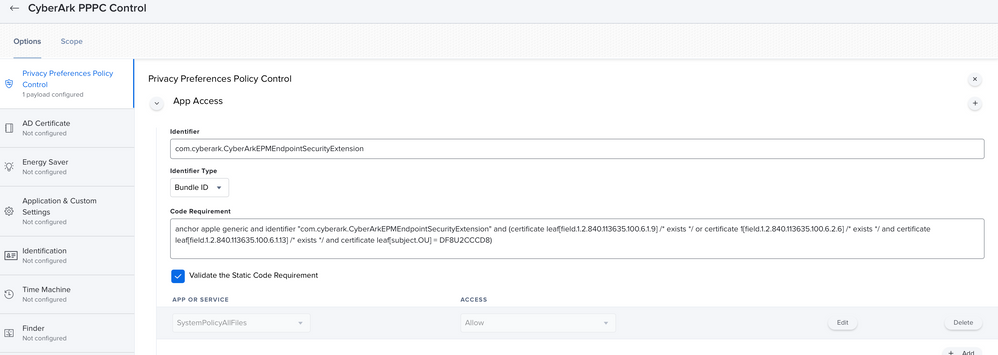
2) PPPC with the following:
Identifier:
com.cyberark.CyberArkEPMEndpointSecurityExtension
Code Requirement:
anchor apple generic and identifier "com.cyberark.CyberArkEPMEndpointSecurityExtension" and (certificate leaf[field.1.2.840.113635.100.6.1.9] /* exists */ or certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = DF8U2CCCD8)Service:
SystemPolicyAllFiles = Allow
3) System Extensions:
It will not work with the Team ID only. In my testing you must add the system extension for this to work.
Team ID: DF8U2CCCD8
Allowed System Ext: com.cyberark.CyberArkEPMEndpointSecurityExtension
Cheers!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-30-2020 08:41 AM
Excellent!
The PPPC code requirement should read as below but other than that it worked right away.
anchor apple generic and identifier "com.cyberark.CyberArkEPMEndpointSecurityExtension" and (certificate leaf[field.1.2.840.113635.100.6.1.9] /* exists */ or certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = DF8U2CCCD8)Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-30-2020 08:46 AM
@DirkM Yeah, I should have added that as code which I have adjusted so they don't get stripped out of the post.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-31-2020 06:50 AM
thanks!!! seems to be working, you are saving me a week of going back and forth with support :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-22-2020 02:49 AM
Could someone help me understand how can I distribute EPM agent through Jamf?
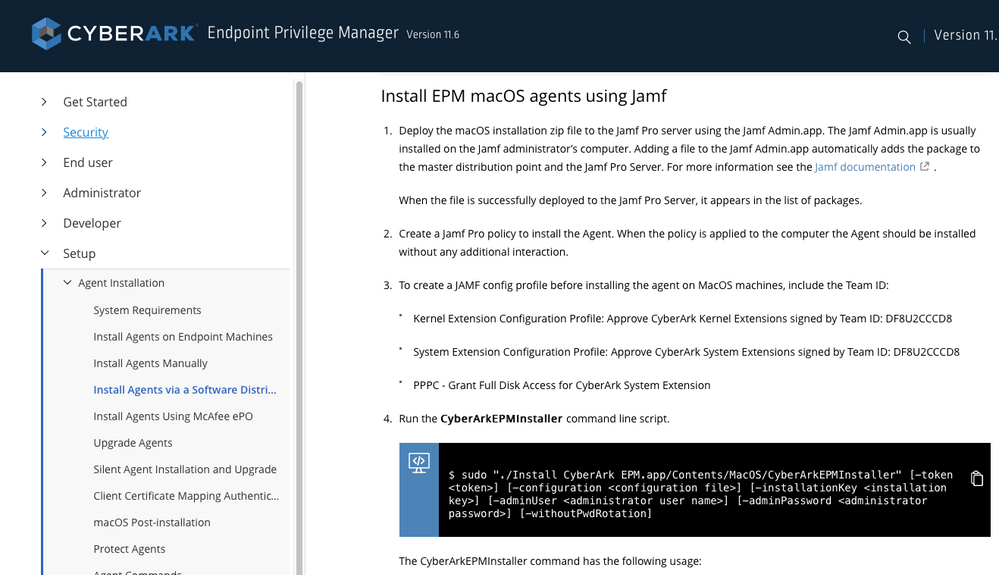
I'm following steps from this docu:
https://docs.cyberark.com/Product-Doc/OnlineHelp/EPM/Latest/en/Content/Installation/macOS-InstallAge...
ad 1. Successfuly added CyberArkEPMAgentSetupMacOs_11.5.0.4610(MacOS).zip to Jamf via Jamf Admin.app
ad 3. Kernel Extension, System Extension and PPPC profile created and applied.
My concern is regarding point 2. How to create policy to install an Agent? Just adding zip file is not a solution. Such policy is doing nothing because it should be pkg.
Any hints?
And could someone explain me point 4.? What is it for? As I understood it's only when I'm trying to install agent manually. But I'm lost here...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-22-2020 07:27 AM
EDIT: This ONLY works on macOS 10.14 and below. For 10.15 systems it appears the System Extension needs to be trusted too as others have pointed out above.
We utilized Composer to create a package which includes the CyberArk Install.app and the .json file required. The composer package just copies this over to a temp directory on the machine (/private/tmp). We then created a policy which runs the package first(to copy the installer down) then runs a script which calls the installer to perform the install.
#!/bin/sh
sudo /private/tmp/CyberArk/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller -k TOKENHERE -withoutPwdRotationObviously the TOKENHERE is the token which is unique to your account when you exported the installer from EPM.
Hope this helps, if you need clarification on anything just let me know.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2020 07:19 AM
@brianmcbride99 I'm going to give this a try.. b/c I'm currently struggling to make this work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2020 07:46 AM
record scratches to a halt
Wait, WHAT?
You have to install this thing with a local admin account that has secure token by passing it's credentials in clear text to an app bundle? No no and HELL NO. That's a security breach waiting to happen.
We were talking about this at work. My recommendation is now going to be to drop this like it's hot. That's not a security product, that's an insecurity product.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-18-2020 01:33 PM
@franton I want to say that with the -withoutPwdRotation argument on your install script you don't need to pass the username and password of a secure token account. I'm working on this tomorrow and Friday so I guess I'll find out, but from reading this thread it seems like that can now be avoided.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-19-2020 03:03 PM
@rtylerdavis Maybe so, but the fact that's even asked for is a giant red warning flag to me.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-20-2020 01:24 PM
@franton I totally get that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-04-2020 03:41 PM
Been struggling with this for a bit, especially on Big Sur. This is how I got it working(mostly). Some of this also came from their support.
Things needed
- DMG created by files from Cyberark
- Script that they gave me, which I'm giving you
- Whiteboard to try and make sense of all of this
1a. Download the zip from the Cyberark server. In the zip grab your .json and the .app(also in another zip file), from there make a DMG with those two files where you want to stick them, so /tmp/ or in the case of what they told me, /Library/Application Support/JAMF/Waiting Room/. (basically what you normally do with Composer). Name it what you want, I named mine CyberArkEPMAgentSetupMacOs.dmg just to follow their instructions.
Once made, upload that DMG to your JAMF server, stick it in a policy and tell it to cache the DMG. Add a payload for the script attached. At
CYBERARKEPM_INSTALL_DMG=type in what your package is called.
From there in the script payload, set to run after and in the parameters values, stick the file name of the dmg in #4, your URL to the server (using the example they gave me) if it is
https://na115.epm.cyberark.com/then use
https://na115.epm.cyberark.com/VFAGT/vfagent.asmxfor #5.
For our location ours has the Agent Self Defense enabled so we needed to add our token in #6. You can generate that by going to the console > My Computers > Upgrade or Uninstall Agent > Action > Generate Secure Token for all Computers.
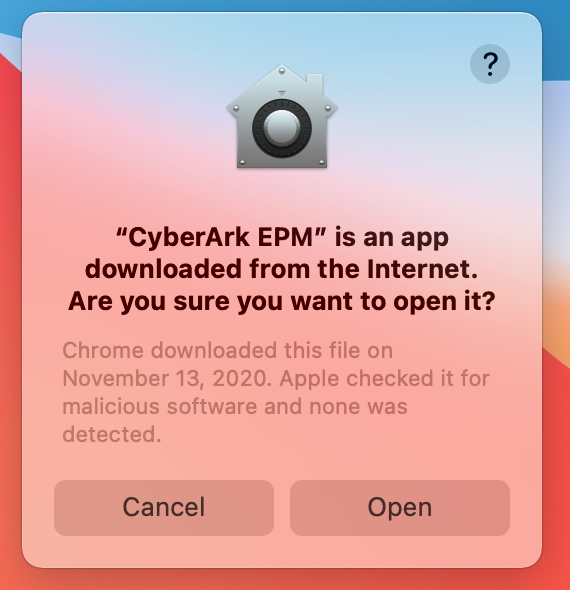
One thing that did take me a bit, was the System Extension. Their instructions only talk about adding the Team ID which was still causing prompts on install. I also had to add
com.cyberark.CyberArkEPMEndpointSecurityExtensionAfter that, I finally got it to install and report back to our Cyberark server. Only "hang" up now is on Big Sur after a reboot it has a pop up saying it downloaded from the internet and asking if you want to run it
The script they gave me
#!/bin/sh
####################################################################################################
#
# ABOUT THIS PROGRAM
#
# NAME
# jamfCyberArkEPMInstallFromDMG -- Install CyberArkEPM version 11.5 from DMG with configuration file
#
# SYNOPSIS
# sudo jamfCyberArkEPMInstallFromDMG <mountPoint> <computerName> <currentUsername> <dmgName> <protectionToken> -- if set is protected
#
# DESCRIPTION
# Sample script to install CyberArkEPM version 11.5 with preconfigured set
##############################
#
# 0. Download CyberArkEPMAgentSetupMacOs.zip from EPM server console.
# 1. Unzip CyberArkEPMAgentSetupMacOs.zip to the directory.
# 2. Rename the directory for something like ./CyberArkEPMAgentSetupMacOs-setX
# 3. Create DMG file by running:
#
# hdiutil create -volname CyberarkEPMAgentSetupMacOs -srcfolder ./CyberArkEPMAgentSetupMacOs-setX -ov -format UDZO ./CyberArkEPMAgentSetupMacOs-setX.dmg
#
# 4. Upload CyberArkEPMAgentSetupMacOs-setX.dmg to the Jamf server
# 5. Add CyberArkEPMAgentSetupMacOs-setX.dmg to the Policy's pkg payload
#
# Use the attached "jamfCyberArkEPMInstallFromDMG" script in the Jamf policy.
#
# You have to provide two parameters to this script
# 1. name of dmg file. As it is named on Jamf
# 2. protectionToken for the set, if the set is protected
#
####################################################################################################
#set -x
# Provide local admin user to enable macOS secure token
CYBERARKEPM_INSTALL_DMG="CHANGE THIS"
# OPTIONAL PARAMETRES STARTS FROM 4
if [ "$CYBERARKEPM_INSTALL_DMG" == "" ]; then
if [ "$4" != "" ]; then
CYBERARKEPM_INSTALL_DMG="$4"
fi
fi
PROTECTION_ARG=""
protectionToken=""
if [ "$protectionToken" == "" ]; then
if [ "$5" != "" ]; then
protectionToken="$5"
fi
fi
if [ "$protectionToken" != "" ]; then
PROTECTION_ARG=" -token $protectionToken"
fi
JAMF_CACHE_LOCATION="/Library/Application Support/JAMF/Waiting Room"
echo "Check if dmg file exists."
if [[ ! -f "$JAMF_CACHE_LOCATION/$CYBERARKEPM_INSTALL_DMG" ]]; then
echo "File $JAMF_CACHE_LOCATION/$CYBERARKEPM_INSTALL_DMG not found"
exit 2
fi
CYBERARKEPM_INSTALL_TMP=$(mktemp -d -t ci-XXXXXXXXXX)
rm -fr $CYBERARKEPM_INSTALL_TMP
mkdir -p $CYBERARKEPM_INSTALL_TMP
sudo /usr/bin/hdiutil attach -nobrowse -mountpoint $CYBERARKEPM_INSTALL_TMP/dmg "$JAMF_CACHE_LOCATION/$CYBERARKEPM_INSTALL_DMG"
ditto -xk $CYBERARKEPM_INSTALL_TMP/dmg/Install CyberArk EPM.app.zip $CYBERARKEPM_INSTALL_TMP
cp -a $CYBERARKEPM_INSTALL_TMP/dmg/CyberArkEPMConfiguration.json $CYBERARKEPM_INSTALL_TMP/CyberArkEPMConfiguration.json
xattr -d $CYBERARKEPM_INSTALL_TMP/Install CyberArk EPM.app
sudo /usr/bin/hdiutil detach $CYBERARKEPM_INSTALL_TMP/dmg
#Cleans Up the dmg so it doesnt take up space on machine
rm -f "$JAMF_CACHE_LOCATION/$CYBERARKEPM_INSTALL_DMG"
rm -f "$JAMF_CACHE_LOCATION/$CYBERARKEPM_INSTALL_DMG.cache.xml"
cat "$CYBERARKEPM_INSTALL_TMP/CyberArkEPMConfiguration.json"
echo "Installing..."
$CYBERARKEPM_INSTALL_TMP/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller -withoutPwdRotation -configuration "$CYBERARKEPM_INSTALL_TMP/CyberArkEPMConfiguration.json" $PROTECTION_ARG
epmVersionFull=$(/usr/local/bin/CyberArkEPM --version)
echo "Cleaning up"
rm -fr $CYBERARKEPM_INSTALL_TMP
if [[ ! $epmVersionFull ]]; then
echo "CyberArk EPM installation failed"
exit 2
fi
echo "$epmVersionFull was successfully installed"
exit 0- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-04-2020 07:45 PM
@KCouture - this is essentially how I was able to get this to function in our environment as well, with one exception, we also added the PPPC settings that @spraguga provided above, I believe this will solve your app downloaded from the internet prompt(though don't quote me on that as I've only tested on 10.14 and 10.15 machines.
Interestingly enough, on a handful of 10.15 machines the install is failing with the below:
Executing Policy CyberArk EPM Agent v.11.8.0.722 Caching package CyberArkEPMAgentSetupMacOs-setX.dmg... Downloading https://use1-jcds.services.jamfcloud.com//download/25bf2928931e4f1fa129b89da4dfb751/CyberArkEPMAgentSetupMacOs-setX.dmg?token=d076ef6da9174490a4ed1add33e0fc887vytaz1rkvnube7vd831z5l5yyyurh82... Verifying DMG... Running script CyberArk_Install_From_DMG... Script exit code: 2 Script result: Check if dmg file exists. expected CRC32 $08F7B48B /dev/disk2 GUID_partition_scheme /dev/disk2s1 Apple_APFS /dev/disk3 EF57347C-0000-11AA-AA11-0030654 /dev/disk3s1 41504653-0000-11AA-AA11-0030654 /private/var/folders/zz/zyxvpxvq6csfxvn_n0000000000000/T/ci-XXXXXXXXXX.8AhCZhik/dmg "disk2" ejected. {"url":"https://login.epm.cyberark.com/VFAGT/VfAgent.asmx","setID":"ce250d0a-e3f1-4b1e-89ea-06b9738c345d","certificateCommonName":null,"registerToken":"dioP2qnSmvxvIntbJdZWSDPpjkqjOY20EvWvPVbqnyQ+TDdD83lFogSv4w79scPeHfg8fDcZEZIdpS1JcKPmkwvvechpJxtnHgRTz0gG9ptrA5BF0FATsaMG0yz7iWuTWfE6OJghmjPeAl+DWgSEyzWV24Lc6v3CrbNRu9XnBJwZxP0uITVUmhudDmAj5kk4yXVlLpIEVgEikEjBBo6UfBo+PdsiYVL8AbSPf5bXZrdtrSOMFKdghjpFD1wqrJRkJdZlEOA7w9dEXLxgwkE0+BWM712Bfcu5ZT5HCU0V8t/IZ1Kxtq3voYiyk1pT4QCEtDLwjZpsfSsf/iOmsbS5Mcz5D+jpi/dV/Aw4UcnZPYM/nzkHaGCtIkwOCwSMbygH+NGVzXzC+d9BPmBK4pRaTSeMZzffUNAu26Jr6z43SUJu4VwHRBfdh94q9g2KQYUTWq1tO7d+mjSTXyP6rIcvycpnuTT8Mi9OrKcZN1NTPhGxjITyIwhqXAthor5x2qh7fANB2qLKCVaEIU2Bc4aN2Yz55MK0gDYbzEYhrGwi3vVCjuhccCqWuQPqOKCct1IeW2tUYnOfkW0KIb/GuNpGT9rxMCcmXD9oNwpxnGKNGCDuuTYn6Sa//Q8elbShqEUB9poO9q144cmw04PpoFpByvYnu8TTI69SdM6zeXa0nxMxP7I7JBAAx1whVMAYhpmqj8m4CPLOU53EglgtRVIhZ4cWRtB/ttAbcCDoA+Pw2XboD9RmC5DNGuWhaWzP0L7lDKYsU0ozsjVqVM0sUvfXnSIRuyg3MiLHQUUtF6d8MZPhBFo+we2azEPez09d5+9Bc2a47YEBzhdCvxFOPuaWY0B6ele7xv/osQojbUWP2wNq5Zd7LW+mLT4ayzSLdriUZGoFbt8MttidmQK636c16jgL/Xy/A3a46rmxD16aE8XSiwfX4yk7dw8MriZvvNiY5vMOsJqRCc8L5+cCdBX1pg==","registerTokenExp":"2004457654"}Installing... Failed to check self-defense status: Error Domain=NSCocoaErrorDomain Code=4 "The file “CyberArkEPM” doesn’t exist." UserInfo={NSFilePath=/usr/local/bin/CyberArkEPM} /Library/Application Support/JAMF/tmp/CyberArk_Install_From_DMG: line 98: /usr/local/bin/CyberArkEPM: No such file or directory Cleaning up CyberArk EPM installation failed Error running script: return code was 2.
Curious if anyone else has seen this and knows what may be happening? It appears that perhaps the cached DMG is not being mounted/extracted properly? I'm not a scripting guru so am not sure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-12-2021 12:33 PM
I know this thread is pretty old by now, but curious if you found a solution to the "Failed to check self-defense status" error. Getting the same thing on a few MacOS 11.5 machines.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-12-2021 01:46 PM
Resolved - this happened because BigSur doesn't play well with "Approved Kernel Extensions". Removing that from the configuration policy resolved the issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-07-2020 07:29 AM
I do have a PPPC made up for it, but mine looks different than yours. I did make mine with the old version of Cyberark installed so I'll give that a go
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-07-2020 08:01 AM
Sadly no change when I change my PPPC full disk. Maybe it needs to be compatible with Big Sur? My version of PPPC has a button for that
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 11:11 AM
Have you tried checking the "Validate the Static Code Requirement" checkbox? That's the only difference I see between yours and ours.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 11:21 AM
So after digging around, it looks like it was gate keeper so I added
sudo xattr -rd com.apple.quarantine /Applications/CyberArk EPM.appto a script to add to the payload which seems to do the trick although for some systems it give an error saying Operation not permitted and some it doesn't. I haven't been able to narrow down whats causing it for some systems
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-11-2020 02:04 PM
Hey Everyone!
I am having some issues with CyberArk and I feel everyone's pain in this thread. IDK if this is helpful but I neutered one of the scripts that CyberArk pre-built and made my life easier. What I did was I used Composer to build a pkg that put The CyberArk app and the json in /private/tmp. It had the contents in a folder called /CyberArk.
So path where I put my files is /private/tmp/CyberArk and within it was the app and the json.
I then just used this script,
Now I built my PPPC profile for Mojave and it was a dream, my install and script still works on Catalina but I am on the struggle bus for the PPPC. Everyone's suggestions above have still not worked for me. But wanted to share a super clean script that I struggled to work for and works great.
#!/bin/bash installationKey="youKeyGoesHereDontLookAtMine" PROTECTION_ARG=" -installationKey $installationKey" CYBERARKEPM_INSTALL_TMP="/private/tmp/CyberArk" cat "$CYBERARKEPM_INSTALL_TMP/CyberArkEPMConfiguration.json" echo "Installing..." $CYBERARKEPM_INSTALL_TMP/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller -withoutPwdRotation -configuration "$CYBERARKEPM_INSTALL_TMP/CyberArkEPMConfiguration.json" $PROTECTION_ARG epmVersionFull=$(/usr/local/bin/CyberArkEPM --version) if [[ ! $epmVersionFull ]]; then echo "CyberArk EPM installation failed" exit 2 fi echo "$epmVersionFull was successfully installed" exit 0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-22-2021 11:23 AM
Hi All,
I have created the CyberArk config profile with below info and it got installed successfully.
1) Approved kernel extension with bundle id: DF8U2CCCD8
2) PPPC with the following: Identifier: com.cyberark.CyberArkEPMEndpointSecurityExtension
Code Requirement:
anchor apple generic and identifier "com.cyberark.CyberArkEPMEndpointSecurityExtension" and (certificate leaf[field.1.2.840.113635.100.6.1.9] / exists / or certificate 1[field.1.2.840.113635.100.6.2.6] / exists / and certificate leaf[field.1.2.840.113635.100.6.1.13] / exists / and certificate leaf[subject.OU] = DF8U2CCCD8)
Service:
SystemPolicyAllFiles = Allow
3) System Extensions:
It will not work with the Team ID only. In my testing you must add the system extension for this to work.
Team ID: DF8U2CCCD8
Allowed System Ext: com.cyberark.CyberArkEPMEndpointSecurityExtension
I was executing the installer via below cmd as a script:
sudo /private/tmp/Install CyberArk EPM.app/Contents/MacOS/CyberArkEPMInstaller -configuration /private/tmp/CyberArkEPMConfiguration.json -installationKey XXXXXXXX -adminUser XYZ -adminPassword XYZ -nonAdminEPMUser
But the policy got failed and received below error in logs:
Script result: Could not complete installation on this computer: ExecutionError(executablePath: "/usr/sbin/installer", arguments: Optional(["-pkg", "/private/tmp/Install CyberArk EPM.app/Contents/Resources/CyberArkEPM.pkg", "-target", "LocalSystem"]), terminationStatus: 1, errorMessage: Optional(""))
Remove Endpoint Security extensions Remove launchd agents Remove launchd daemons Remove kext Remove authorization rights Failed to restore authorization right 'com.apple.system-extensions.admin': SecurityError(status: -60005 ("The authorization was denied."), additionalInfo: ("")) Remove PAM modules Remove sudoers settings Remove files and directories Remove users and groups
Can anyone please suggest to sort out this issue?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-22-2021 02:19 PM
@Kapil - this is what did the trick for us: CyberArk_JAMF_Deployment
With the exception of an outstanding issue with the config profile(PPPC settings cause the profile to fail to install, when those are removed, it installs) I have an outstanding Case open with CyberArk support on this.
Will update when that comes to resolution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 03:12 AM
@brianmcbride99 Thanks for your update Brian, Sure keep me posted.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-24-2021 01:57 AM
I have tried the below document from Cyberark and that too got failed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-04-2021 09:11 AM
@brianmcbride99 Any Update on how to have the PPPC Config not fail after scoping?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-04-2021 09:26 AM
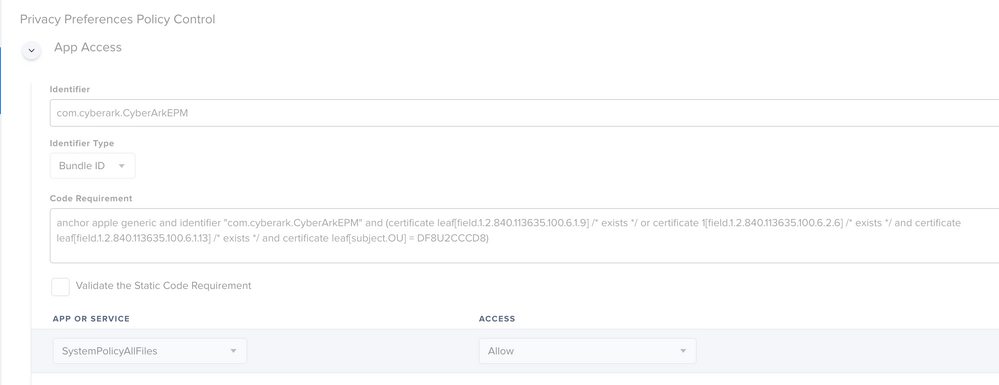
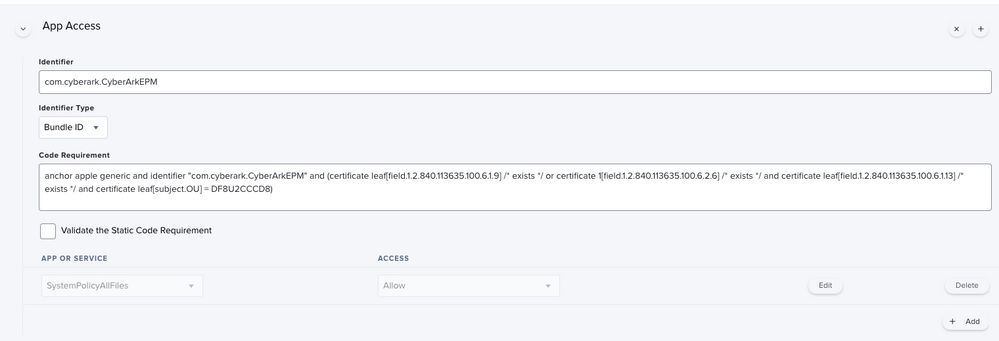
@tvargas - yes - apologies i meant to update this thread and forgot....there was actually a formatting issue in the PDF published by cyberark, it took a support call and digging into it to find out...an extra whitespace if i remember correctly. I was copying/pasting the PPPC code. i would have expected them to update their PDF by now, but if not here is the PPPC section of the config profile we are using:
The code requirement for this identifier 'com.cyberark.CyberArkEPMEndpointSecurityExtension' is:
anchor apple generic and identifier "com.cyberark.CyberArkEPMEndpointSecurityExtension" and (certificate leaf[field.1.2.840.113635.100.6.1.9] /* exists */ or certificate leaf[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = DF8U2CCCD8)The code requirement for this identifier 'com.cyberark.CyberArkEPM' is:
anchor apple generic and identifier "com.cyberark.CyberArkEPM" and (certificate leaf[field.1.2.840.113635.100.6.1.9] /* exists */ or certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = DF8U2CCCD8)EDIT: The screenshots are reversed from the order i uploaded them, sorry about that, but you should get the gist.