- Jamf Nation Community
- Products
- Jamf Pro
- FileVault weirdness on M1 macBook with 11.3.1
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
FileVault weirdness on M1 macBook with 11.3.1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on
05-13-2021
08:02 AM
- last edited on
03-04-2025
04:29 AM
by
![]() kh-richa_mig
kh-richa_mig
Hi all,
Apologies in advance if this is a numpty question - I've avoided centrally managing FileVault for as long as I've been managing macOS because of its oddities, but recently I had a rush of blood to the head (after being glared at by our CyberSecurity Architect) and thought I'd try again to introduce it into our Jamf Zero-touch workflow. Now I remember why I've avoided it for so long.
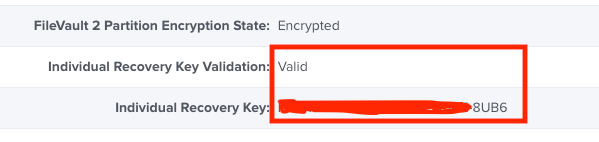
Long story short(ish): I think the Jamf stuff is working fine (I created an "Individual and Institutional" Disk Encryption configuration for "Current or Next user" and then tested it using a manually triggered policy). All seemed good, FV kicked in at next login, Jamf DB was updated with the Individual and Institutional keys. Hoorah!
Then I decided to pretend the user had forgotten their password. Got into recovery console (as mentioned, this is a new M1 macbook running 11.3.1) and it wanted me to authenticate as the user. Obviously he's forgotten his password, so that was a no-go. Clicked the "Forgot all passwords?" link which prompted me to enter the recovery key...
Say what!? I rebooted and logged back into macOS so I could run "sudo fdesetup validaterecovery recoverykey" and it came back as "true" (i.e. valid).
Am I missing something blindingly obvious, or is this yet another case of Apple being all Apple-ish and breaking stuff again?
Also, am I right in thinking that now M1 hardware doesn't have a concept of target disk mode that the Institutional Key/Certificate is useless?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-21-2021 07:42 AM
If anyone's ever interested, this issue has either been fixed by Jamf 10.29.2 or macOS 11.4 (or a combination of both) - everything now seems to work as expected on our test M1 laptop and the valid Individual Recovery Key actually does let you get to the Recovery tools.
I'm still interested to hear how much use the Institutional Key is nowadays though...