- Jamf Nation Community
- Products
- Jamf Pro
- Local Password Sync failing - Catalina and Kerbero...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Local Password Sync failing - Catalina and Kerberos SSO Extension
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-17-2021 05:27 PM
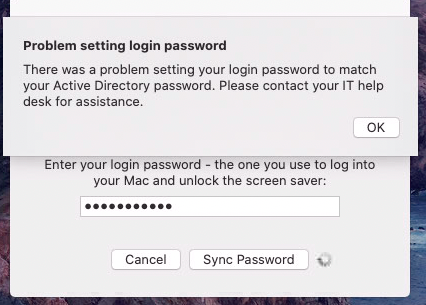
On a test Mac I converted my mobile account from mobile to local using Rich Trouton's script. This appears to have worked without issue. I've then applied a simple config profile to the test Mac to enable the Kerberos SSO Extension. I can sign in and get a solid key icon in the menu bar and all appears well. However, it realizes that the account password is different than what's defined in AD. I get prompted to put in the AD password and then the local password. It attempst to sync the local account password with the AD password but keeps failing - "Problem setting login password" "There was a problem setting your login password to match your Active Directory password." Please contact your IT help desk for assistance." I've tried this numerous times and it fails each time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-17-2021 10:31 PM
@stephanpeterson Do you have a password policy enforced on your Macs that's different than what your AD password policy is? I haven't tested it with the Kerberos SSO, but I do recall seeing this behavior with Enterprise Connect when a Mac had a password policy that required a number, but the AD password policy was configured for either number or symbol.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2021 05:27 PM
@sdagley I'm trying to track down if we have one that's hanging around in the background somewhere. I tested by enrolling a Catalina VM that's plain vanilla macOS and password sync works just fine. I tried pwpolicy -clearaccountpolicies and a restart but that didn't help. Must be lurking somewhere else...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2021 06:56 PM
@stephanpeterson What does pwpolicy getaccountpolicies show for your password requirements?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2021 08:33 PM
We found that the 'no sequential characters' setting was lingering around. Running systemextensionsctl reset sorted that out.
A way to test (if FileVault enabled) - unlock the drive using the Recovery Key, then at the Change Password field enter your new password. If you get a bunch of green dots and a single grey one - either a config profile or lingering setting in your Kerberos profile (it has a sequential characters option) is hanging around.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-20-2021 05:53 AM
@sdagley It doesn't look like anything is set as far as the pwpolicy binary is concerned:
pwpolicy getaccountpolicies Getting global account policies <?xml version="1.0" encoding="UTF-8"?> <!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd"> <plist version="1.0"> <dict/> </plist>
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-20-2021 06:43 AM
We had the issues after demobilising accounts and then using the SSO Extension. Tried with Rich's script, NoMAD even Jamf Connect all happily demobilised but then SSO Ext would fail. We thought it may be to do that the UID is a high number rather than 501, 502 etc after demobilising. Tried to raise to Apple but did not get anywhere with it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-20-2021 07:07 PM
@stephanpeterson If you don't have any policies set then you're not running into the problem I had with AD and Mac password policies being misaligned, but @MatG's post above this one does sound the same as yours.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-11-2021 08:40 AM
I've been having issues like that as well. But only a few. Not a widespread problem. But we did convert mobile accounts to local.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-20-2023 12:47 AM
Any workaround for this issue?