Hello everyone.
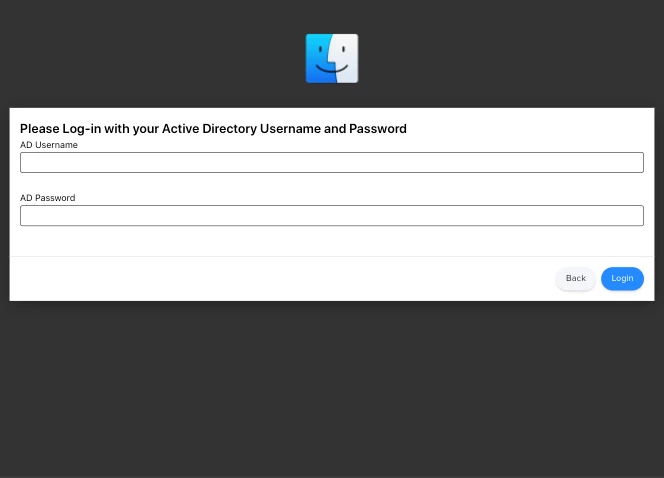
I'm integrating jamf to my company and I looking for moving on local account on all the MAC.
At the moment we using Domain account for connecting user on there Mac.
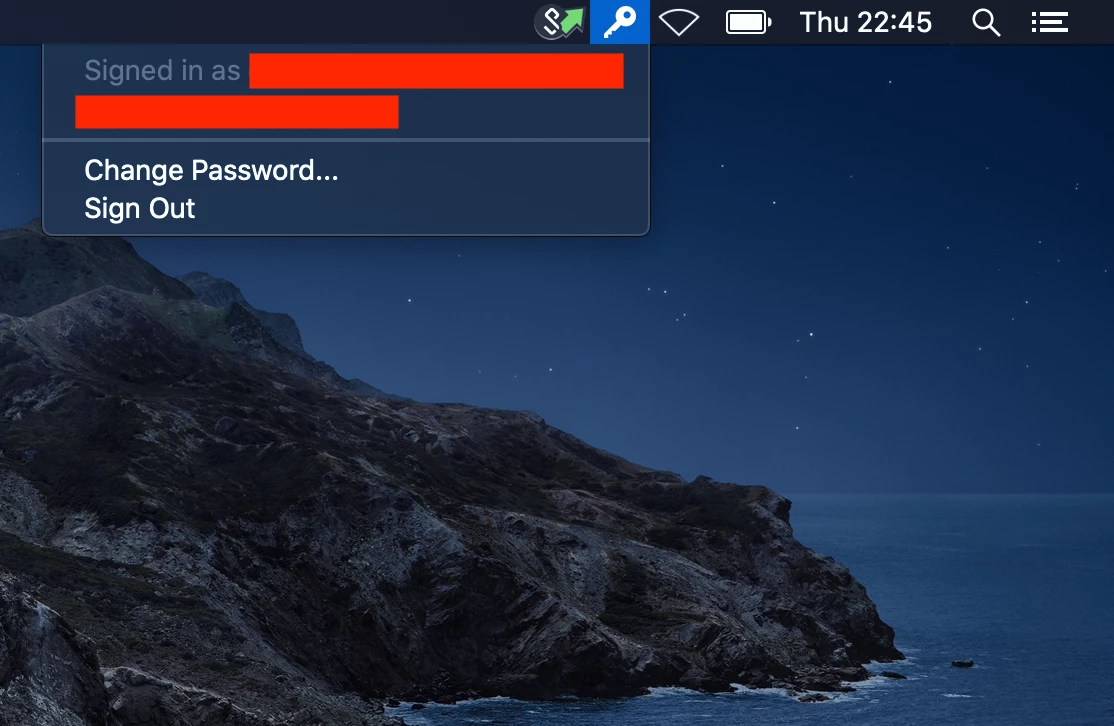
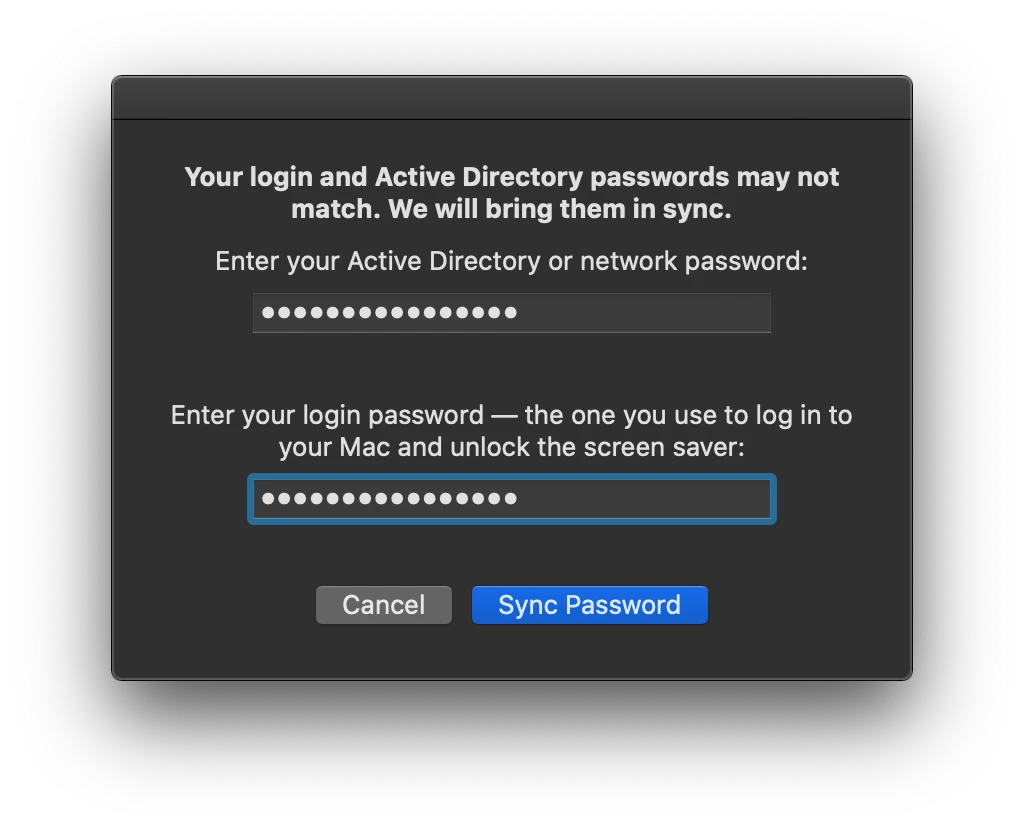
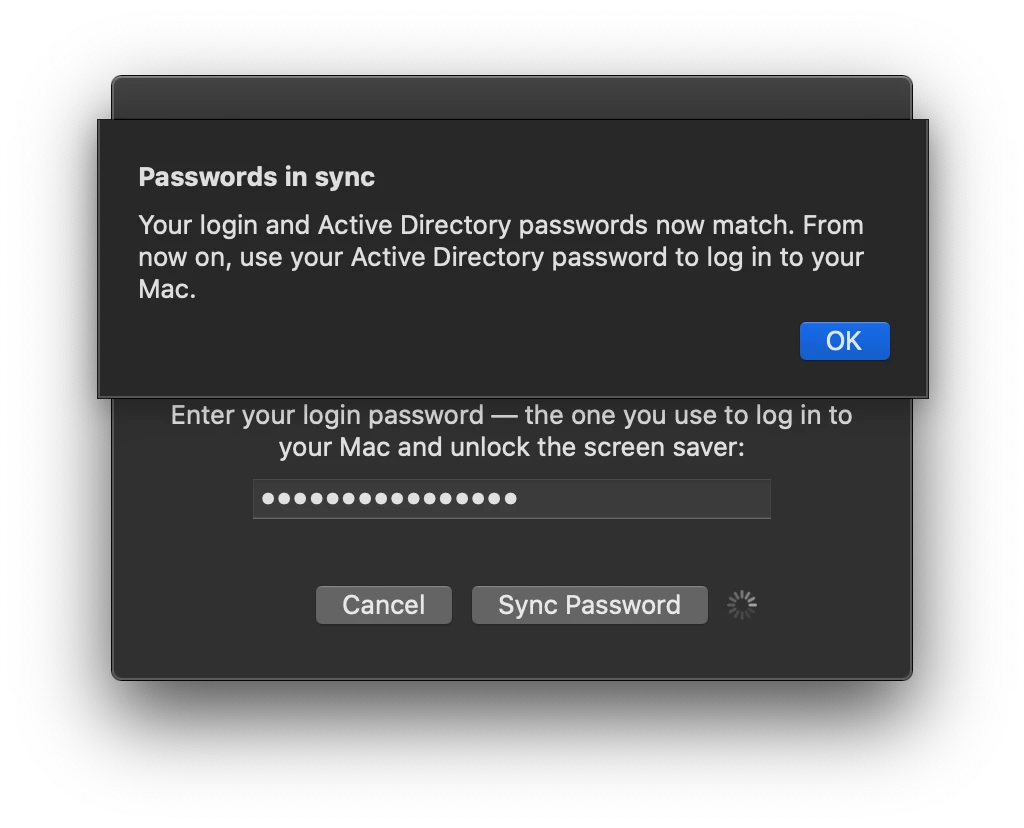
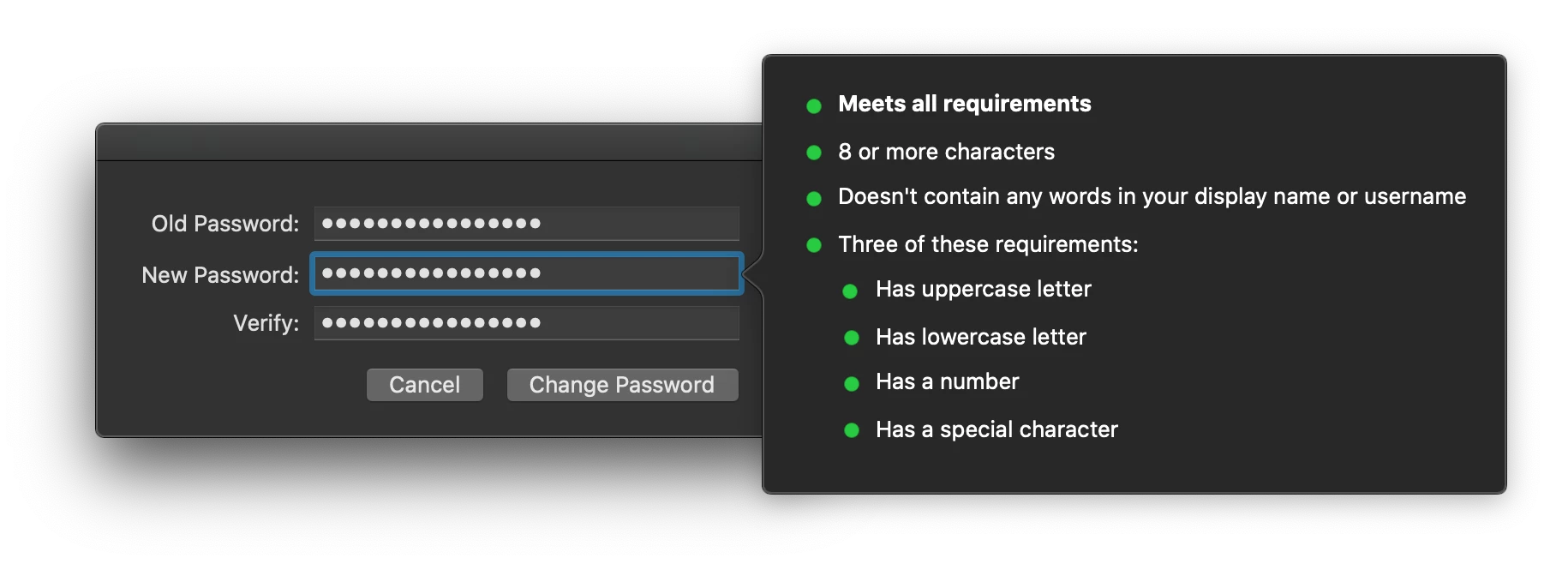
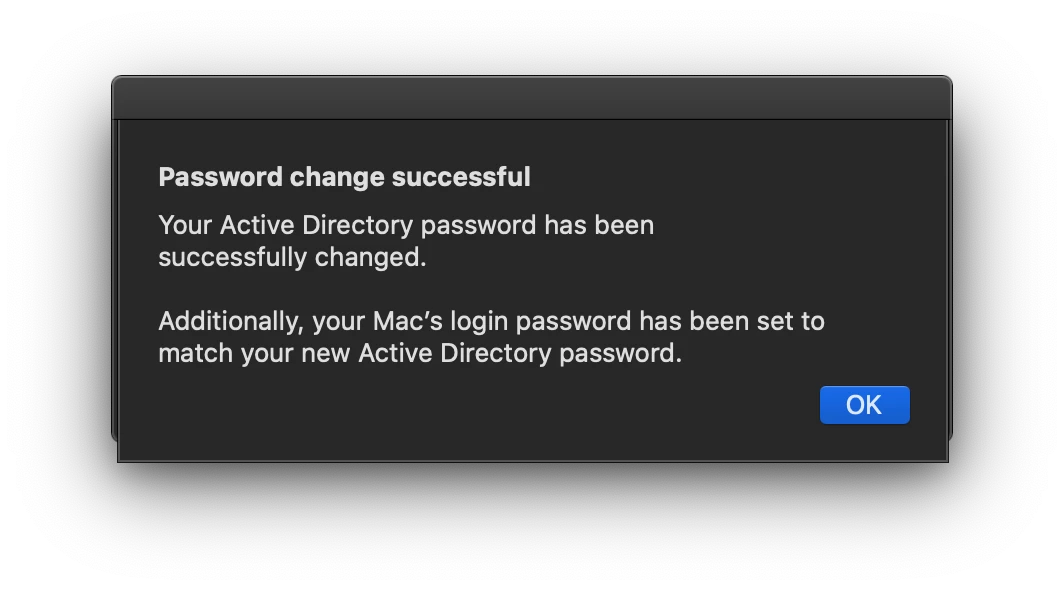
Im looking for a solution to use LOCAL account but to keep the password sync with AD password MASTER.
When a user call our Hotline for missing password (usually after holiday :) ) the technical support change the password directly on active directory, at the moment if the Mac is connected on the company building the user can connect with the new password.
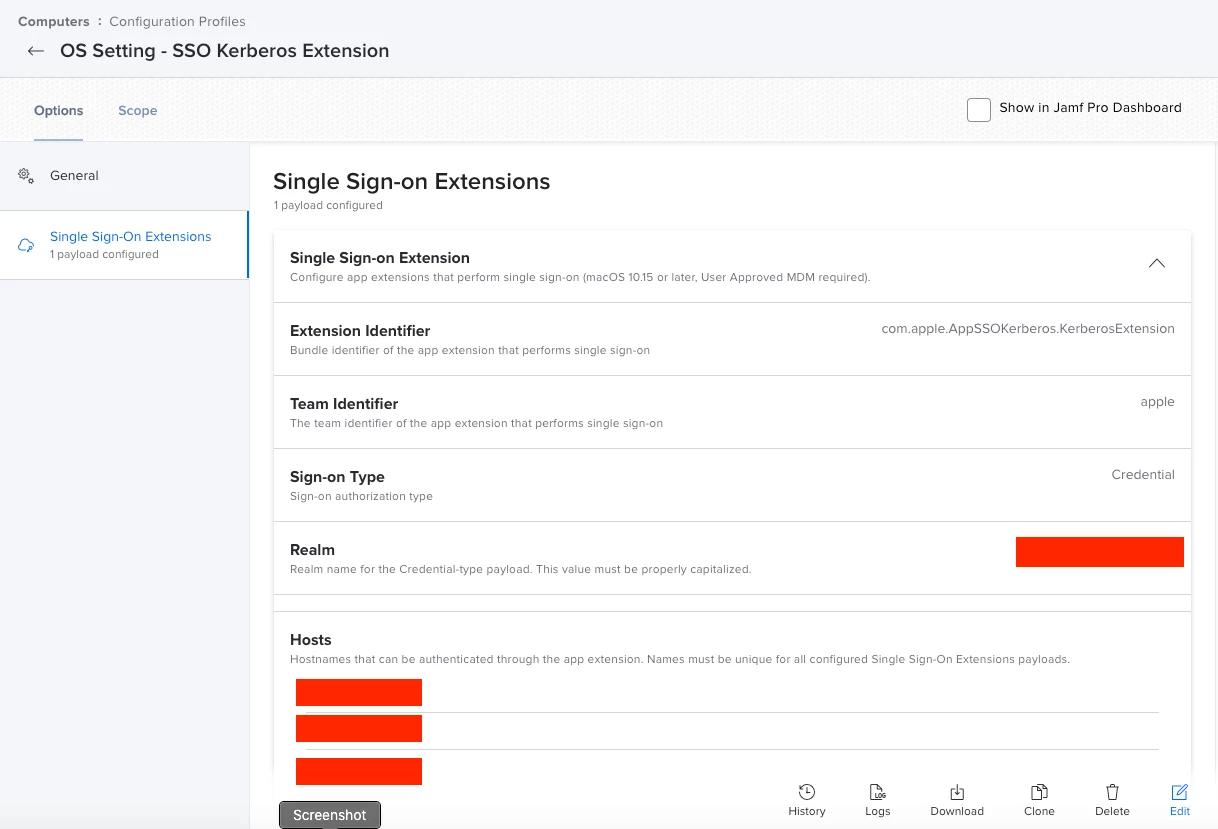
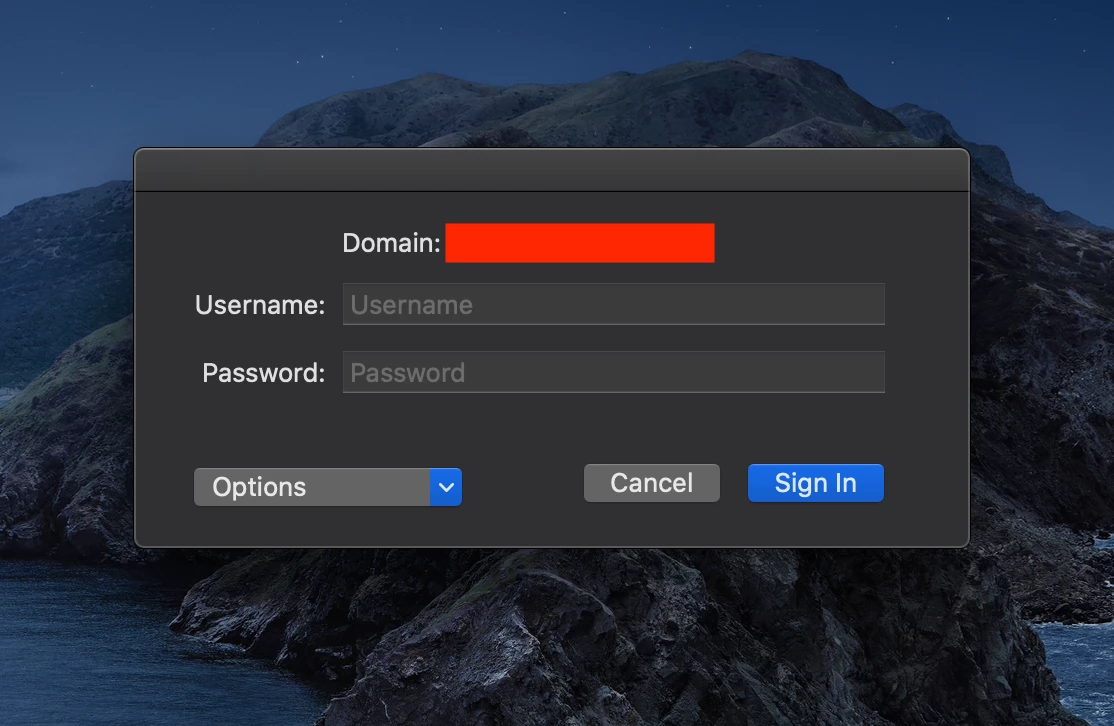
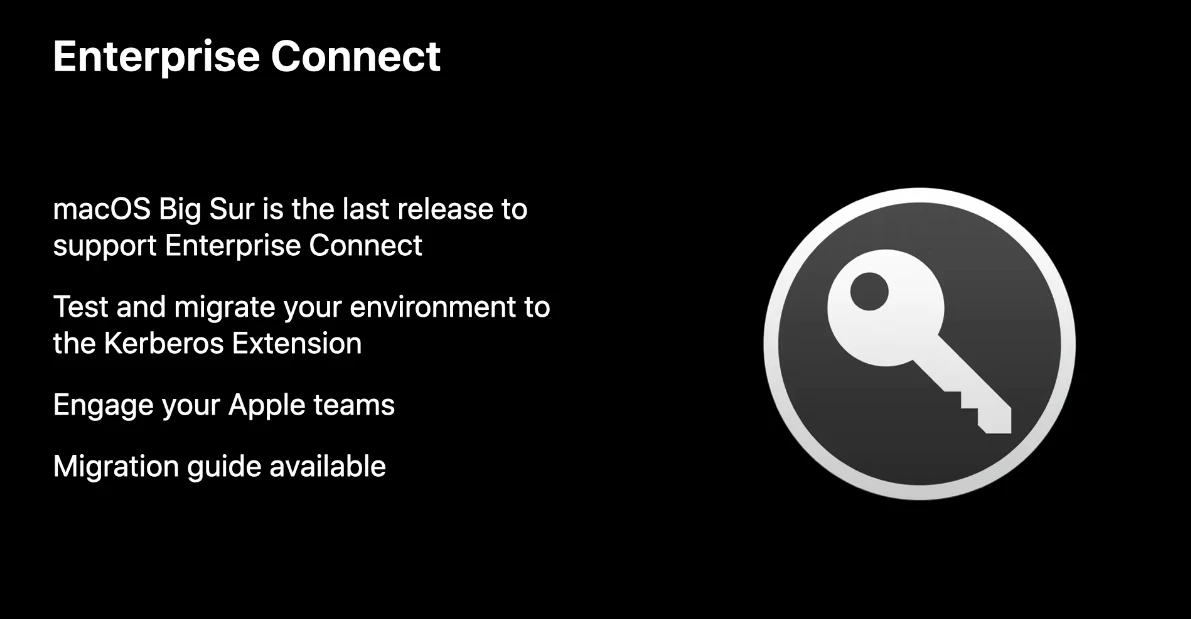
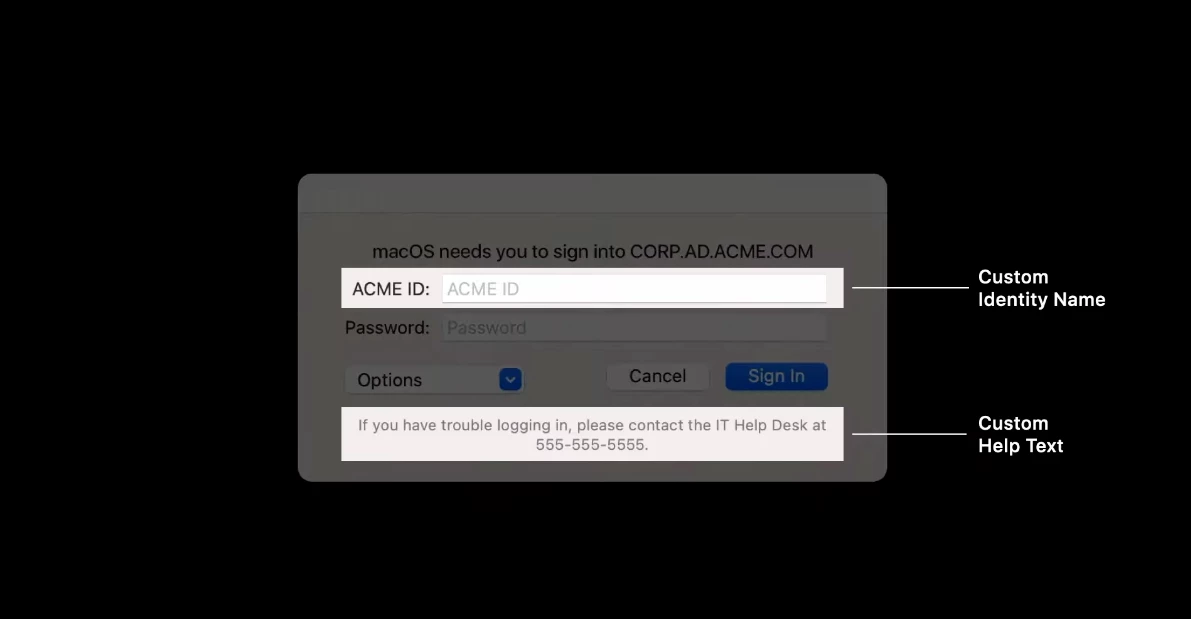
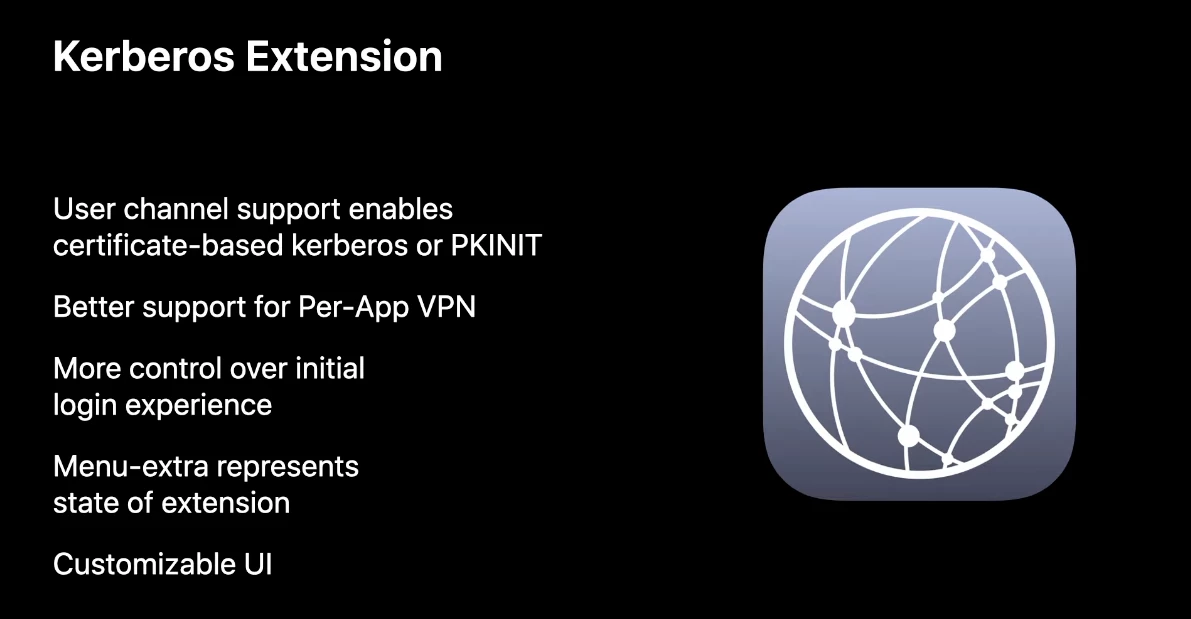
The two solution I know is Nomade and Kerberos SSO Extention but is look like the master password is the local password. So if we need to change an user password on our ActiveDirectory I think the session password not going to change.
Did you know any solution for stop using mobile account but keeping the password sync with AD password as a master password. I think the solution have to work with closed session