- Jamf Nation Community
- Products
- Jamf Pro
- Standard user can't login - Catalina 10.15.7
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-01-2021 02:22 PM
Hey guys,
I'm working on upgrading some MBAs and I have a policy that creates a new standard user which the students can use. I have the Macs joined to an AD and I thought just to test I should try to login as the student account. It fails. I know it's not the password since I reset it. Weird thing is, is that if I make the account an administrator then it allows me to login?!?! I then remove the admin rights and reboot and it goes back to failing. Any ideas?
Thanks!
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 02:37 PM
Ok so I found the problem. It was a Configuration Profile in Jamf. Login Window Profile->Access->Local-Only users may login. Once I put a check mark in that box, I was able to login with the Local Standard Student account.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-01-2021 09:00 PM
Are you set up for Network accounts or Mobile accounts?
If you log in with some other AD account does that work?
If you log in with a different account, open Terminal and type
id username_of_problem_user
do you get anything helpful? It should show all the group memberships of the user
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 07:23 AM
Hey dlondon, thanks for replying!
Here is what I've done so far:
I removed the account and then ran the policy again on the computer (after first changing the password in the policy) to create it again.
If I create another standard user (I created one with the name TEST) it also fails to login
I booted to recovery mode and used the change password terminal command and changed it there. I also ran First Aid on the Drive and Volumes
I rest the PRAM and SMC (No T2 chip, 2015 MacBook Air)
The computers are joined to a domain, I have a student test account in the AD which works, I can login using it.
I have a local admin account also setup though Jamf and it works.
There are no Mobile Accounts.
I'll try your suggestion next and let you know how it goes.
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2021 07:29 AM - edited 09-02-2021 07:30 AM
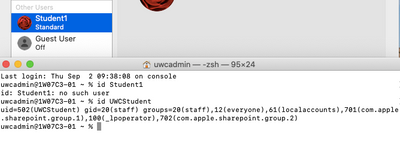
The local standard account for the students is called Student1
I ran the terminal command: id student1 and it came back with: no such user. I ran the same command on my AD student test account and it comes back with a bunch of information.
I couldn't believe that it came back with no such user so I opened Users & Groups in sys prefs and the account is definitely there.
I'm using 10.15.7 with security update 2021-004 if that helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 07:43 AM
So I tried that same command using the Account Name (UWCStudent) instead of the Full Name (Student1) and I get a different result.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 09:50 AM
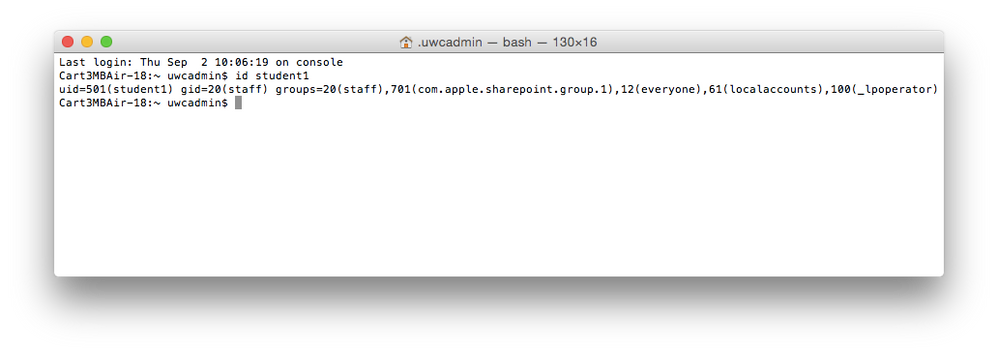
So I just checked a Yosemite system and did the same terminal command and this comes up.
I notice that the Yosemite is a uid=501 and Catalina is uid=502. Not sure if that is an issue or not.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2021 07:36 AM - edited 09-02-2021 07:38 AM
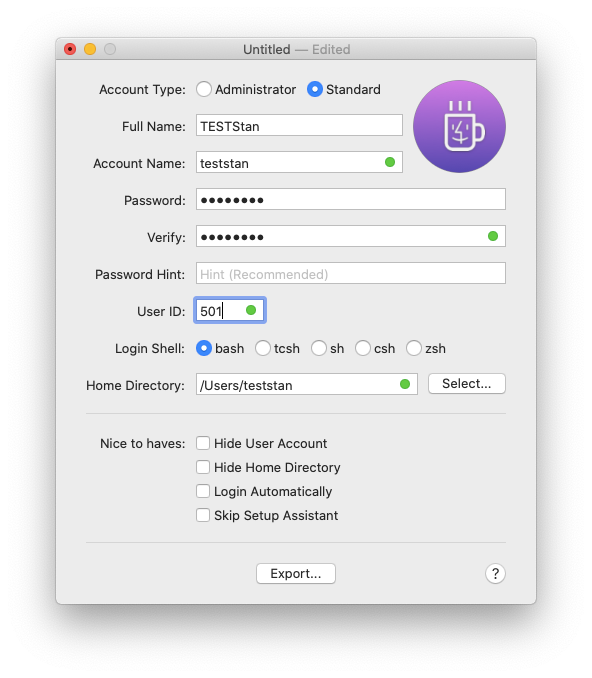
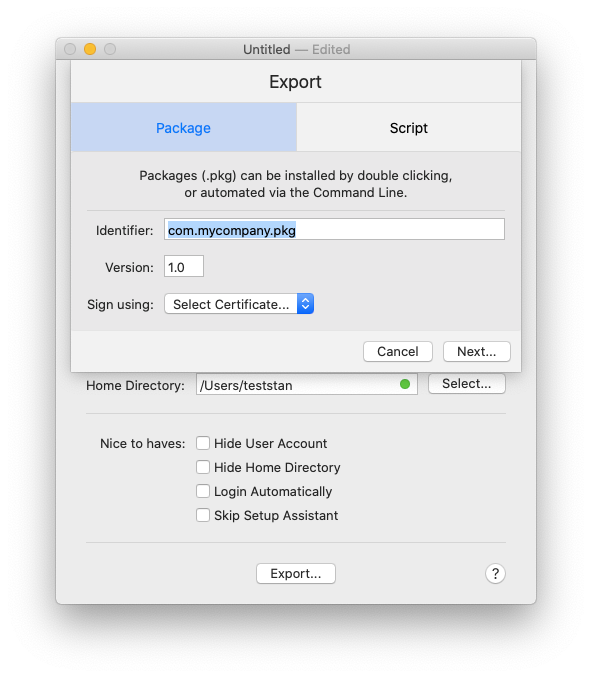
You might check out this great little app that I use for tricky tasks like creating mac accounts. It successfully creates non-domain local users (admin or standard), gives you advanced settings on them, and works well. You can then just push out the user as an install package:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 08:54 AM
Hi SGill, thanks for that. My problem is not creating accounts, it's allowing standard accounts to be able to login.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 09:31 AM
The standard accounts I've created with MacUserGenerator don't have any trouble logging in here in my testing in case it helps resolve the issue your are seeing with creating them with other methods
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 09:53 AM
Hey, so I tried out the MacUserGenerator and I'm not sure if it's part of my problem or I'm not doing it right. I created a pkg and but it fails when I install.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2021 10:05 AM - edited 09-02-2021 10:08 AM
Make sure you're using an available User ID (UID). You can show the existing visible local ones (not AD) with this:
dscacheutil -q user | grep -A 3 -B 2 -e uid:\ 5'[0-9][0-9]'
You could lower the UID number if you need to look at the built-ins, and UIDs below 500. First admin accounts usually start with 501.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 01:14 PM
Thanks man.
So I created a new account with that tool and still no dice. The system still only allows Admins to login.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 01:25 PM
Wow--well you might try retesting on a fresh nuke/pave then...we use the it often with 10.15.7 so I can vouch for that it works normally. The app GUI is just to make it easier to see what UID you are creating....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-02-2021 02:37 PM
Ok so I found the problem. It was a Configuration Profile in Jamf. Login Window Profile->Access->Local-Only users may login. Once I put a check mark in that box, I was able to login with the Local Standard Student account.