Hi All,
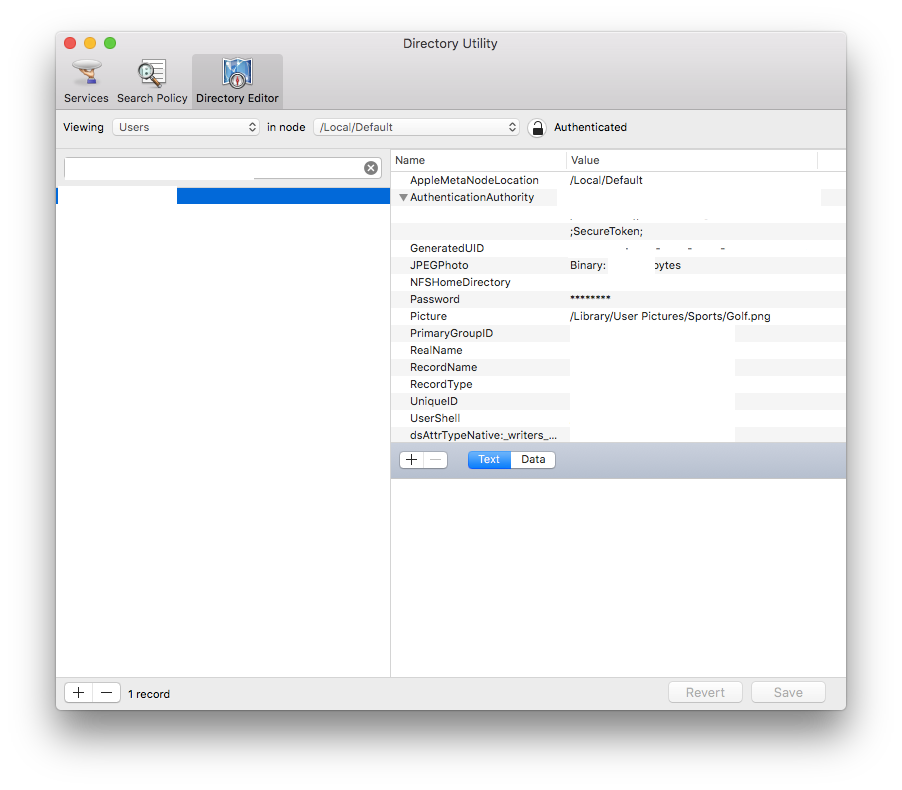
I'm running into an issue where for a subset of devices, I am unable to enable the SecureToken for a standard mobile user. I have a local admin account on these machines with a valid secure token. When attempting to grant a SecureToken from the local admin to the standard mobile user, I receive authentication errors on the commands. I've tried both formatting methods below.
bash-3.2$ sudo sysadminctl -adminUser local.admin -adminPassword PASSWORD -secureTokenOn mobile.user -password PASSWORD
2018-03-20 17:25:08.036 sysadminctl[8666:724459] ### Error:-14090 File:/BuildRoot/Library/Caches/com.apple.xbs/Sources/Admin/Admin-674/DSAuthenticator.m Line:94
2018-03-20 17:25:08.037 sysadminctl[8666:724459] ----------------------------
2018-03-20 17:25:08.037 sysadminctl[8666:724459] No clear text password or interactive option was specified (adduser, change/reset password will not allow user to use FDE) !
2018-03-20 17:25:08.037 sysadminctl[8666:724459] ----------------------------
2018-03-20 17:25:08.037 sysadminctl[8666:724459] Operation is not permitted without secure token unlock.bash-3.2$ sudo sysadminctl interactive -secureTokenOn mobile,user
2018-03-20 17:51:32.467 sysadminctl[10440:783432] setSecureTokenAuthorizationEnabled error Error Domain=com.apple.OpenDirectory Code=5000 "Credentials could not be verified, username or password is invalid." UserInfo={NSLocalizedDescription=Credentials could not be verified, username or password is invalid., NSLocalizedFailureReason=Credentials could not be verified, username or password is invalid.}I have confirmed that I am passing correct passwords and not making any mistakes. My initial suspicion was that this was an issue with escaping special characters or spaces however the issues persist when using passwords that don't contain either.
One thing that is unique about the configuration of the machines is the local admin account was recreated after it was initially created via the setup assistant (we used the jamf create user payload in order to recreate this). This was previously a method we used to allow our local admin account access to unlock the FileVaulted disk as the payload included the option to enable this recreated account for FileVault. Despite of this I have verified that this user is still considered user 501.
If anyone has any insight I'd be super grateful. AppleCare's solution was to wipe & restore which based on the scale and location of these devices, will prove very difficult.
Thanks,
Jon