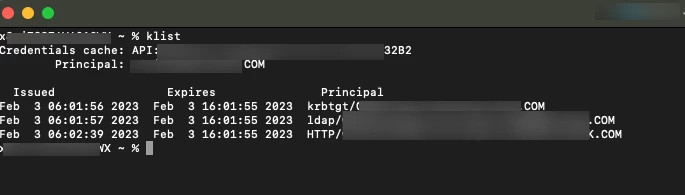
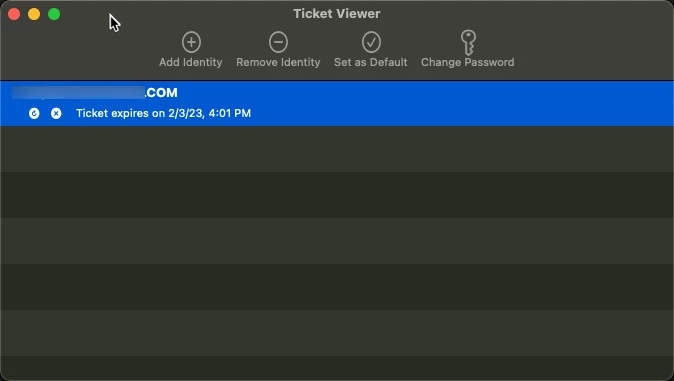
I'm new to this so I'm sure I making mistakes. We recently setup Jamf and Jamf connect. Now users can log into their Mac using their AD credentials. When a user is added to Jamf our installer set Jamf up to convert that users from a mobile user to a standard user. The problem is that as a standard user if you open terminal and use the id command it will only report back local groups not AD groups. The users access to certain network shares is based off of AD groups. If I force the user to stay as a remote user then all their groups are retained. However if the remote user changes their password it does not automatically sync. I feel like I'm missing something basic. I would like users to be able to login with the AD credentials and have all their AD groups and be able to change their passwords and have it sync. If anyone can point me in the right direction I would appreciate it.