- Jamf Nation Community
- Products
- Jamf Pro
- Re: Big Sur: Symantec WSS Agent 7.2.1.14589
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Big Sur: Symantec WSS Agent 7.2.1.14589
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-21-2021 09:29 AM
Currently testing WSS 7.2.1.14589. Does anyone know if Symantec provides a content filter to stop pop-ups during installation?
- Labels:
-
Security Management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-24-2021 11:58 AM
bump
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-26-2021 11:23 AM
Getting ready to test this as well, I haven't seen anything.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2021 04:58 PM
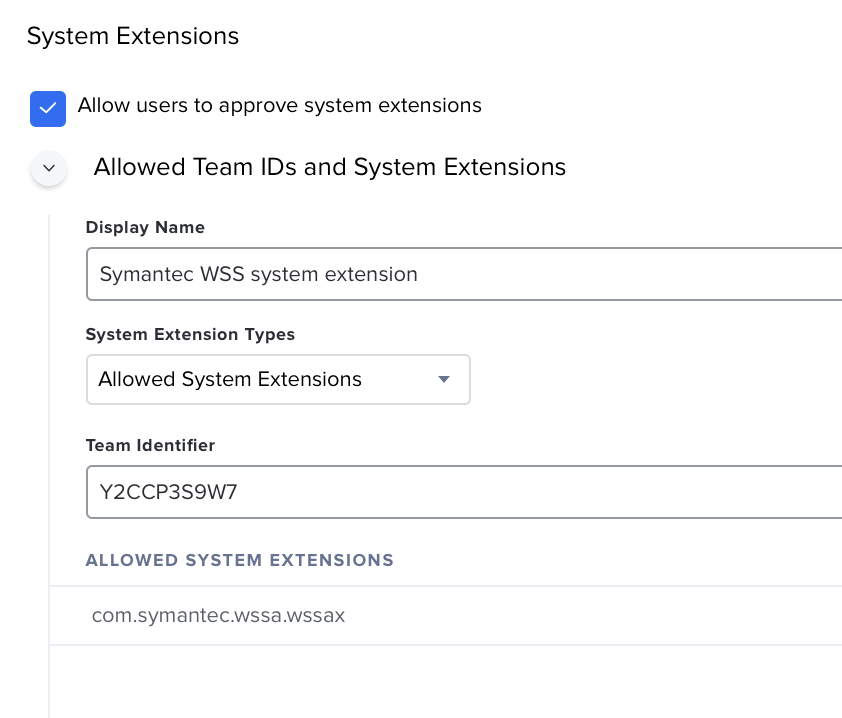
I can confirm this is the correct System extension. Works fine on macOS Catalina and Big Sur. Just need root cert payload and VPN filter?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2021 04:59 PM
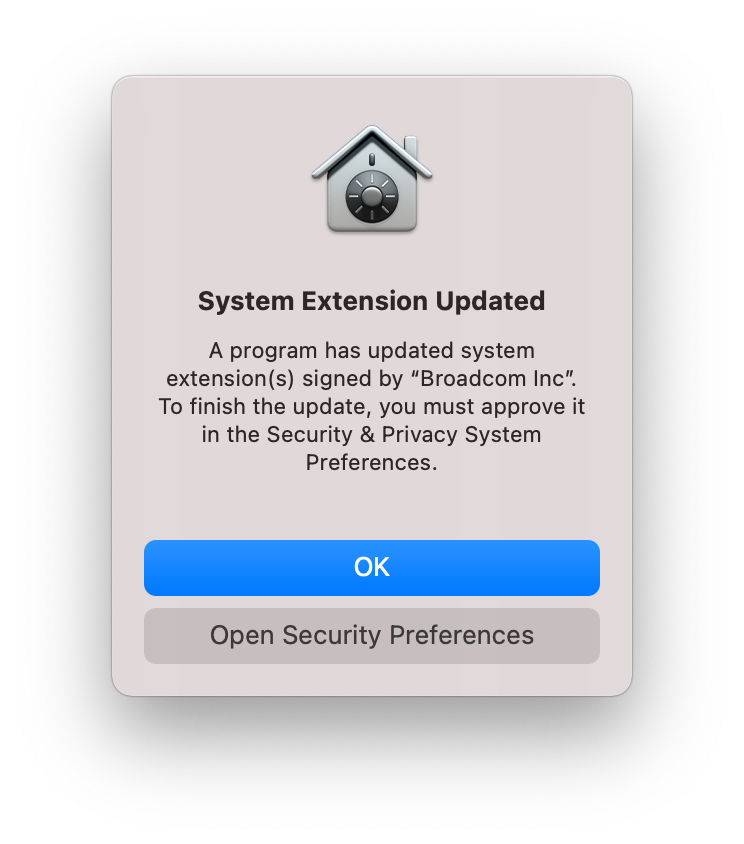
Screen shot..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2021 07:47 PM
@LaMantia Thanks for this, is the VPN content filter a generic one or org specific?
If generic, would you mind sharing it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2021 07:44 AM
@LaMantia that's the system extension. I need the content filter for the network filter feature.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2021 08:03 AM
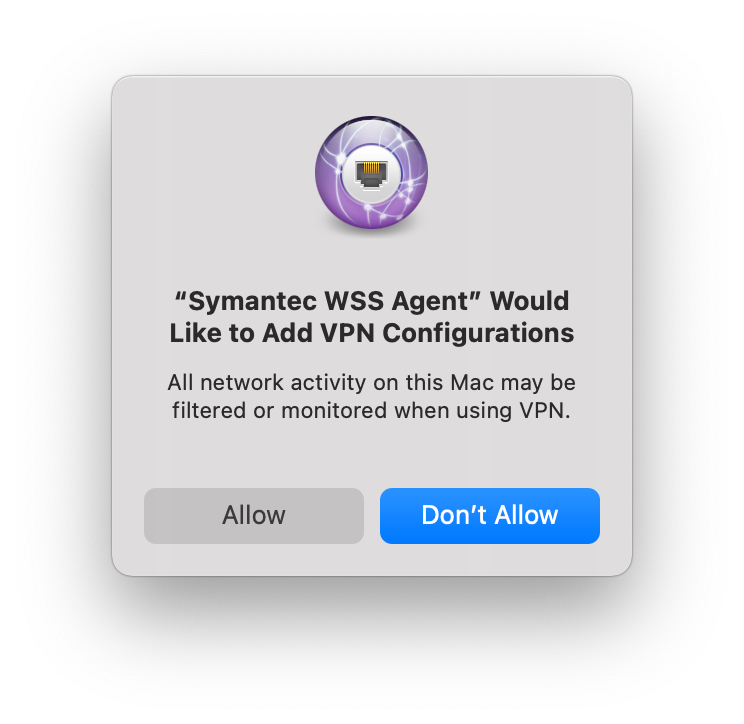
progress. wss 7.2.1.14589 with the system extension above, shows activated and I'm not getting the pop ups other than the vpn configurations. I have a message out to our team that manages symantec to see if they can find a profile or a web content filter for wss. If I find anything I'll post it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-03-2021 08:36 AM
@nsbickhart Any luck finding anything? I've been trying to figure it out as well and haven't gotten very far.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-03-2021 09:41 AM
@IamGroot nope, haven't found anything. I did find out that the new WSS agent is showing in crash reports and am getting the "your computer restarted because of a problem" message when rebooting. I wish we could just not use Symantec.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-03-2021 10:03 AM
I think Broadcom is telling us to have the user accept the content filter???
https://techdocs.broadcom.com/us/en/symantec-security-software/web-and-network-security/web-security-service/Help/Connectivity_3/conn-about-wssa/conn-wssa-jamf.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-03-2021 10:05 AM
My team has basically convinced our info sec team to get rid of all Symantec products. They have let us down in the past, but they've completely failed this year. SEP isn't working on Big Sur properly and they failed to provide a content filter for the WSS. If you can, please drop these losers as soon as possible. We're moving to Palo Alto Cortex and Global Protect.
No M1 support, until Q2??? What a joke. Get it together Symantec.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-03-2021 10:35 AM
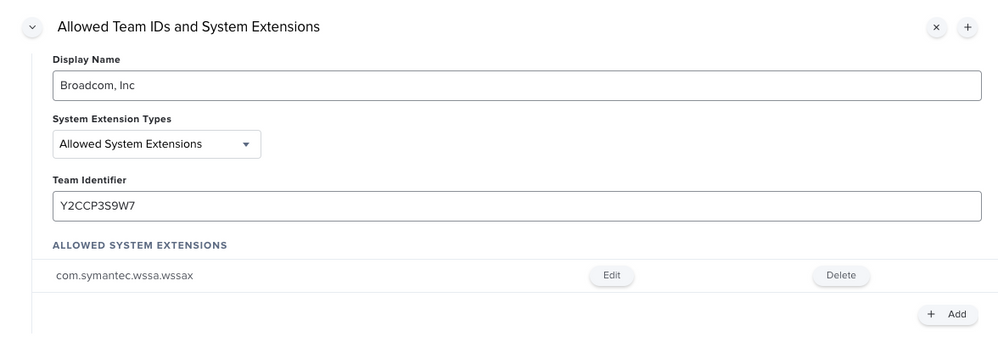
In our environment I am seeing where we need both the old Approved KEXT for macOS 10.15x:
Display Name: Broadcom, Inc
Team ID: Y2CCP3S9W7
Approved Kernel Extensions (Bundle ID): com.symantec.kext.wssa
and the System Extension for macOS 11.x:
Display Name: Broadcom, Inc
System Extension Types: Allowed System Extensions
Team ID: Y2CCP3S9W7
Allowed System Extension: com.symantec.wssa.wssax
Working with support to verify the pkg provided by SME is right, we are also getting notifications for VPN config to account for on macOS 11.x
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-04-2021 08:20 AM
@markdmatthews , Thanks for the update. I had my admin to put in a ticket to address this VPN config too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-17-2021 12:39 AM
@markdmatthews Did you have any luck getting the config profile settings for the VPN stuff in 11.x?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-18-2021 08:18 PM
@markdmatthews @LaMantia @bwoods @nsbickhart After doing some research I finally came across https://techdocs.broadcom.com/us/en/symantec-security-software/web-and-network-security/web-security-service/Help/Connectivity_3/conn-about-wssa/conn-wssa-bigsur.html. According to Broadcom the VPN prompt can't be automated per "This step in the process cannot be automated in an MDM. Currently, Apple does not support the MDM profile configuration of Transparent Proxy Providers." Considering it's Broadcom/Symantec, that's hard to believe but I'll take their word for it. I hope this information helps everyone else that's been waiting for an answer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-18-2021 10:21 AM
@IamGroot I was able to 100% automate those via:
1. Select ‘Computers > Configuration Profiles’
2. Select New
3. Select the Options tab > General payload
a. Name enter Symantec WSS Agent - VPN Profiles
b. Description enter “WSS Agent Tunnel (Packet-tunnel) and WSS Agent Proxy (App-proxy) for macOS Big Sur and later.”
c. Category choose Applications
d. Distribution Method choose Install Automatically
e. Level choose Computer Level
4. Select > VPN payload, select Configure
a. Connection Name enter WSS Agent Tunnel
b. Verify VPN Type is VPN
c. Connection Type select Custom SSL
d. Identifier enter com.symantec.wssa.ui
e. Server enter 127.0.0.1
f. Enable Provider Bundle Identifier
i. Provider Bundle Identifier enter com.symantec.wssa.wssax
g. Provider Type select Packet-tunnel
h. Enable Provider Designated Requirement
i. Provider Designated Requirement enter “anchor apple generic and identifier "com.symantec.wssa.wssax" and (certificate leaf[field.1.2.840.113635.100.6.1.9] / exists / or certificate 1[field.1.2.840.113635.100.6.2.6] / exists / and certificate leaf[field.1.2.840.113635.100.6.1.13] / exists / and certificate leaf[subject.OU] = Y2CCP3S9W7)”
5. Scroll up and choose Add +
a. Connection Name enter WSS Agent Proxy
b. Verify VPN Type is VPN
c. Connection Type select Custom SSL
d. Identifier enter com.symantec.wssa.ui
e. Server enter 127.0.0.1
f. Enable Provider Bundle Identifier
i. Provider Bundle Identifier enter com.symantec.wssa.wssax
g. Provider Type select App-proxy
h. Enable Provider Designated Requirement
i. Provider Designated Requirement enter “anchor apple generic and identifier "com.symantec.wssa.wssax" and (certificate leaf[field.1.2.840.113635.100.6.1.9] / exists / or certificate 1[field.1.2.840.113635.100.6.2.6] / exists / and certificate leaf[field.1.2.840.113635.100.6.1.13] / exists / and certificate leaf[subject.OU] = Y2CCP3S9W7)”
** Scope to Big Sur (or later i.e. Not Like 10.5)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-18-2021 10:24 AM
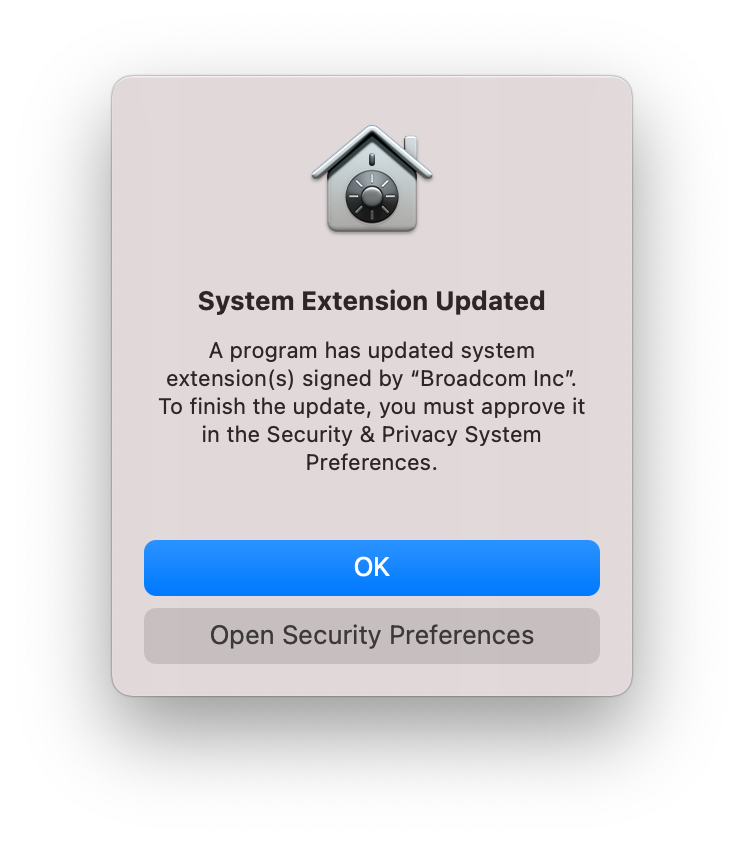
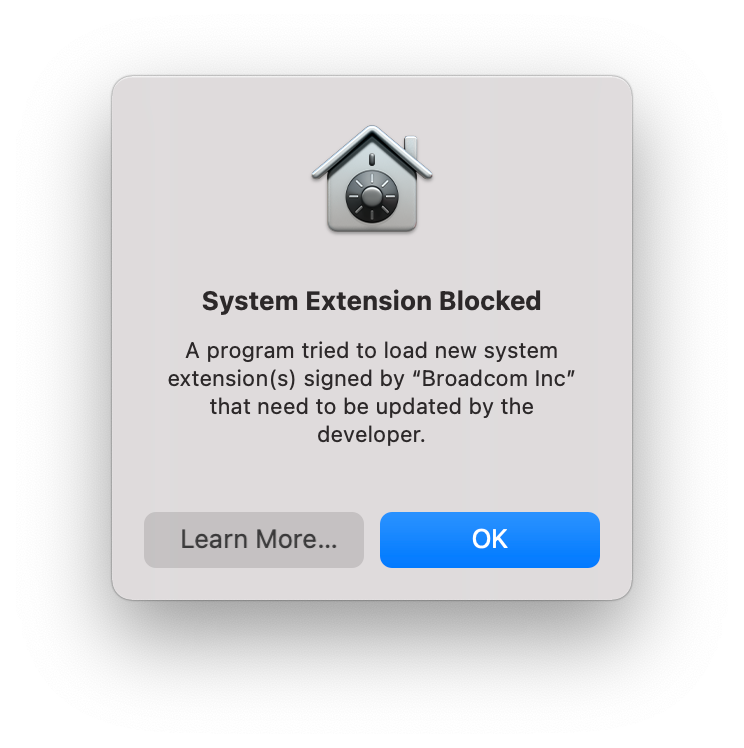
Now seeing issue with Big Sur on the System Extension (even though it is on the device already prior to WSS installation)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-18-2021 01:13 PM
@markdmatthews Thank you a ton! You just saved me so much frustration that I've been dealing with. I really appreciate that. Something I've noticed is that it installs two proxy filters, WSS Agent Tunnel and WSS Agent Proxy. When I Allow them to be installed it appears the internet connection on the endpoint completely cuts off until I uninstall WSS Agent. However, when I ignored the Allow or Don't Allow and simply logged out and back in, it only installed the WSS Agent Tunnel adapter and the internet connection is fine. Have you ran into that at all?
As for the System Extension, what happens if you leave the Display Name blank? I have mine blank and the rest of the same configurations you have and it appears to be installing fine right now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-22-2021 08:02 AM
@IamGroot not ran into that at all; I am currently testing upgrades and new installs for 10.15.x and 11.x on Intel and M1 based devices.
At this point I would be willing to try anything – although I feel like they are missing an "Identifier" in the documentation. They also do determine based on macOS version IF they "need" KEXT or System Ext (breaking out the pkg pres/postinstall scripts and installvars); not sure why they didn't kill off KEXT entirely.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-24-2021 02:33 PM
I'm running into some strange issues as well. If I add the VPN payload to the config profile, WSS agent doesn't load properly. It seems like the SYSEXT is blocked even if it is MDM approved and I don't get any prompt asking me to manually approve it.
If I remove the VPN payload, the agent works fine but I get the VPN prompt which is what I'm trying to avoid...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-05-2021 05:13 AM
https://techdocs.broadcom.com/us/en/symantec-security-software/web-and-network-security/web-security-service/Help/Connectivity_3/conn-about-wssa/conn-wssa-bigsur.html - In following this, deployment of this config profile pre macOS upgrade to BigSur works fine, the WSS agent is functional. However post upgrade we are seeing the prompt to enable the System Extension. Has anyone here been able to automate this approval? Relying on our end users to approve this is simply not an option.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-05-2021 04:40 PM
I had both com.symantec.wssa.wssax and com.symantec.wssa.ui listed in the allowed System Extensions payload, removing com.symantec.wssa.ui seems to have fixed it.
FYI, I've also been testing WSS 8.0 and seeing some major improvement with the whitelisting process. MS Teams was giving us a lot of grief but v8.0 can use wildcards with .app which has done the trick.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 10:08 AM
Symantec finally updated their documentation for wss agent on Big Sur. I added the vpn profiles as stated in the article and no more popups on Big Sur from the first device I loaded.
https://techdocs.broadcom.com/us/en/symantec-security-software/web-and-network-security/web-security-service/Help/Connectivity_3/conn-about-wssa/conn-wssa-bigsur.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 10:54 AM
@ooftee Is this on Big Sur? Still seeing issues on Big Sur (new deployments) with Pkg deploying KEXT (Kernal Extension) in Symantec WSS Agent 7.2.1.14589.pkg; once installed rebuilding AuxKC as a System Extension.
This requires user approval and a restart... anyone else seeing this?
I wouldn’t expect a ‘Kernel Extension Update’ in that instance (on a brand new zero touch Big Sur deployment) and from a Broadcom perspective the ask is for a Pkg for macOS 11 or later that ONLY includes a System Extension at deployment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 11:25 AM
@nsbickhart - in following those instructions from Broadcom I am still seeing a user prompt that the System Extension was Updated when upgrading a machine from 10.14 or 10.15 to Big Sur. I haven't tested a clean Big Sur install then JAMF enrollment and installation of the config profile and the WSS agent. I have a case open with Broadcom on this and am awaiting a response.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 03:50 PM
@markdmatthews Yes I've been testing on fresh installs of Big Sur, Catalina has been fine all along.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 04:23 PM
@brianmcbride99 working pretty good on new installs of big sur. Still seeing popups when upgrading. I believe the profile has to be installed on the device before the application or you will get the popups. I am seeing wss hose up internet browsing, but that could be something that our symantec team needs to fix. If I find out why that's happening, I'll post it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-08-2021 04:54 PM
@markdmatthews I'm seeing what you're seeing but with Blackmagic Inc. Design Software as Per: https://www.jamf.com/jamf-nation/discussions/38634/kernel-extensions-big-sur-blackmagic.
They are still using KEXTs under Big Sur.
But I don't know if this is due to the Software being installed prior to the Configuration Profile being loaded as per @brianmcbride99 . I need to test on a fresh install.
I'm seeing the pop-up even after entering all of the suggested Bundle IDs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-12-2021 07:36 AM
I did find out that the new WSS agent is showing in crash reports and am getting the "your computer restarted because of a problem" message when rebooting. I wish we could just not use Symantec.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-13-2021 05:03 AM
We are on 7.2.1 of WSS, and are having a ton of issues in Big Sur as well @user-kGyZmDeZOD Some of which are below:
- Teams direct calling does not work
- NAT issues in Windows VMs, internal vpn traffic does not appear to be routed correctly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-13-2021 08:58 AM
@brianmcbride99 We're seeing similar issues. Our Split Tunnel VPN's don't work with WSS and our full tunnel one does. Everything is configured properly on the WSS Management console too. It's very odd.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-13-2021 11:35 AM
@nsbickhart on new installations of Big Sur you aren't being prompted "System Extension Updated"?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-13-2021 12:17 PM
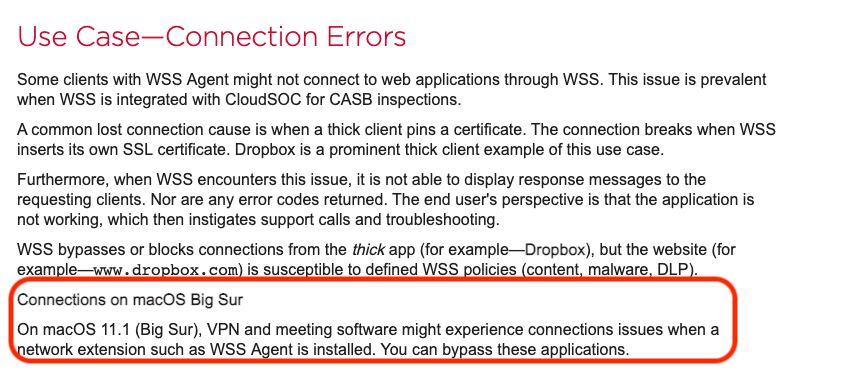
Just came across this @IamGroot https://techdocs.broadcom.com/us/en/symantec-security-software/web-and-network-security/web-security-service/Help/Connectivity_3/conn-about-wssa/conn-wssa-bypassapp.html
So something that worked without issue in previous WSS agent versions and macOS versions now suddenly we have to identify ourselves and create bypasses for??? Is Broadcom literally trying to force users to a different product.(
)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-14-2021 08:36 AM
@brianmcbride99 I didn't even notice that on there, thank you! This seems to be the new thing for vendors. We recently introduced another product into our environment that made us add app bypass filters as well for these kinds of things. It's a very tedious process as you have to identify each and every application you want bypassed. I agree with you, some vendors are really trying their hardest to lose their customers. I'll try this out today and let you know if I have any luck. Fingers crossed!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2021 08:50 AM
No one else seeing "warning" on new Big Sur (macOS 11) deployments?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2021 11:07 AM
@markdmatthews - we are seeing something similar to this when upgrading to macOS 11, only stating something to the effect of the system extension being updated and needs to be approved. I'm assuming you are pre deploying the config profile approving the system extension and setting the VPN settings as they mention here
I did, and still get the approval prompt similar to yours. I have an open case with Broadcom, with zero movement in over a week.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-20-2021 04:25 AM
I've been working with Broadcom support on this. We use falcon and anyconnect. Bypassed both, running 7.2 and it still seems to be fighting with anyconnect. I grabbed some more pcap logs and sent to support but haven't heard anything back since last week. The profiles for system extension/vpn seem to be taking care of the popups on new loads, but the issue remains with navigating to anything via a browser, it just won't allow anything out. Sometimes, if you click disconnect on the wss tunnel, it'll let you out, but it's all random.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-28-2021 04:50 AM
Good news. I was provided with wss agent 7.3.5.15179. I tested briefly on Big Sur and it is no longer locking up web browsing and I'm no longer seeing disconnects in the logs. Lots more testing to do, but it's looking good.
I believe 7.3.5.15179 is being released on Friday.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-28-2021 01:39 PM
@nsbickhart Thanks for the update. I tried reaching out to our WSS admin but he stated he doesn't see it in the download portal. Is that something you had to reach out to Symantec to get?