So we're all remote yet may still be hiring and may need to roll out new hardware.
All of our Macs are bound to AD and all users are mobile accounts.
My question is how do I remotely have a user login to create a mobile account at login when outside our firewall. We don't have external access to our AD although we do have Azure AD if there's some way to leverage that.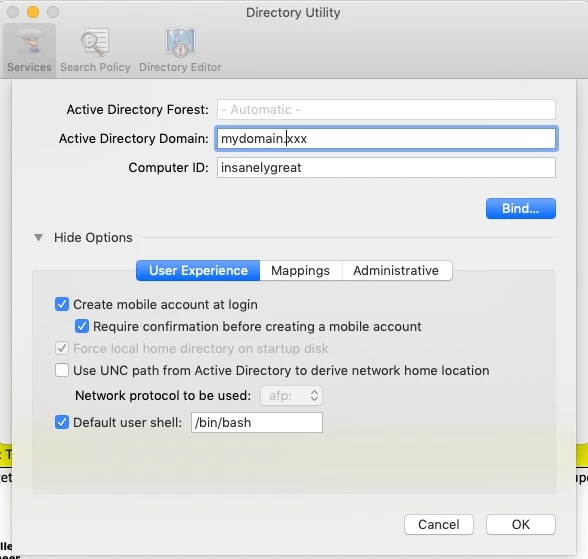
Any help is greatly appreciated.