- Jamf Nation Community
- Products
- Jamf Pro
- Re: Remove CISCO AnyConnect VPN Tunnels
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Remove CISCO AnyConnect VPN Tunnels
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-17-2022 07:14 AM - edited 11-17-2022 07:14 AM
Hello All,
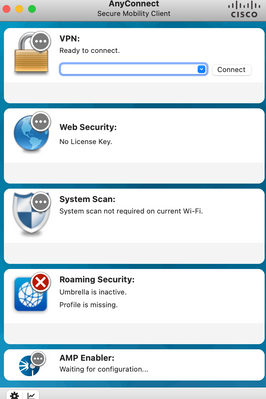
Please help me with a solution where we can hide or remove the unwanted tunnels list in the CISCO AnyConnect VPN Window.
I would like to remove/hide Web Security, System scan or AMP etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 07:27 AM
Used to run into that issue as well. It was based on the xml included in the composer package for me. Don't use AnyConnect anymore, but I'll see what I can did up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 07:30 AM
Add this script to run after you install AnyConnect (or as a post-install).
Modify as needed to your environment. May need to close and re-open AnyConnect after the script is run.
#!/bin/bash
/opt/cisco/anyconnect/bin/amp_uninstall.sh
/opt/cisco/anyconnect/bin/dart_uninstall.sh
/opt/cisco/anyconnect/bin/iseposture_uninstall.sh
/opt/cisco/anyconnect/bin/nvm_uninstall.sh
/opt/cisco/anyconnect/bin/umbrella_uninstall.sh
/opt/cisco/anyconnect/bin/websecurity_uninstall.sh
exit 0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 07:32 AM
That's much easier than what I was doing. Wish I knew this back then.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 07:36 AM
Thank you, I will check this. :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-08-2023 04:53 AM
For Cisco Secure Client (version 5), they moved stuff around and changed the name. In case this helps:
#!/bin/bash
/opt/cisco/secureclient/bin/amp_uninstall.sh
/opt/cisco/secureclient/bin/dart_uninstall.sh
/opt/cisco/secureclient/bin/iseposture_uninstall.sh
/opt/cisco/secureclient/NVM/bin/nvm_uninstall.sh
/opt/cisco/secureclient/bin/umbrella_uninstall.sh
exit 0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-09-2024 11:33 AM
Was able to remove everything except Zero Trust Access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-09-2024 12:02 PM
I am a newbie but I did figure it out. Appreciate you all.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 09:52 AM
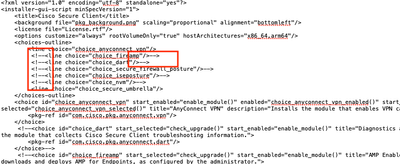
I run the "pkgutil --expand" to open the AnyConnect PKG. Then open the Distribution file. You can then action out the products you don't want to install. Once you have completed this, you can save and flatten the file. Then you only have the PKG to install, no other scripts needed. I have included the Distribution file we use. It only installs Cisco AnyConnect and Umbrella. Just be aware that this is version specific and my example only works with 5.0.00556.
<?xml version="1.0" encoding="utf-8" standalone="yes"?>
<installer-gui-script minSpecVersion="1">
<title>Cisco Secure Client</title>
<background file="pkg_background.png" scaling="proportional" alignment="bottomleft"/>
<license file="License.rtf"/>
<options customize="always" rootVolumeOnly="true" hostArchitectures="x86_64,arm64"/>
<choices-outline>
<line choice="choice_anyconnect_vpn"/>
<!--<line choice="choice_fireamp"/>-->
<!--<line choice="choice_dart"/>-->
<!--<line choice="choice_secure_firewall_posture"/>-->
<!--<line choice="choice_iseposture"/>-->
<!--<line choice="choice_nvm"/>-->
<line choice="choice_secure_umbrella"/>
</choices-outline>
<choice id="choice_anyconnect_vpn" start_enabled="enable_module()" enabled="choice_anyconnect_vpn_enabled()" start_selected="check_upgrade()" selected="choice_anyconnect_vpn_selected()" title="AnyConnect VPN" description="Installs the module that enables VPN capabilities.">
<pkg-ref id="com.cisco.pkg.anyconnect.vpn"/>
</choice>
<!--<choice id="choice_dart" start_selected="check_upgrade()" start_enabled="enable_module()" title="Diagnostics and Reporting Tool" description="Installs the module that collects Cisco Secure Client troubleshooting information.">
<pkg-ref id="com.cisco.pkg.anyconnect.dart"/>
</choice>-->
<!--<choice id="choice_fireamp" start_selected="check_upgrade()" start_enabled="enable_module()" title="AMP Enabler" description="Installs the module that downloads and deploys AMP for Endpoints, as configured by the administrator.">
<pkg-ref id="com.cisco.pkg.anyconnect.fireamp"/>
</choice>-->
<!--<choice id="choice_secure_firewall_posture" start_selected="check_upgrade()" start_enabled="enable_module()" title="Secure Firewall Posture" description="Installs the module that provides the Cisco Secure Client with the ability to identify the operating system, antivirus, antispyware, and firewall software installed on the host prior to creating a remote access connection to the secure gateway.">
<pkg-ref id="com.cisco.pkg.anyconnect.posture"/>
</choice>-->
<!--<choice id="choice_iseposture" start_selected="check_upgrade()" start_enabled="enable_module()" title="ISE Posture" description="Installs the module that provides the Cisco Secure Client with the functionality needed to authenticate to wired or wireless networks controlled by the Identity Services Engine, including examination and any needed remediation of the connecting host environment.">
<pkg-ref id="com.cisco.pkg.anyconnect.iseposture"/>
</choice>-->
<!--<choice id="choice_nvm" start_selected="check_upgrade()" start_enabled="enable_module()" title="Network Visibility Module" description="Installs the Network Visibility Module which collects application telemetry data.">
<pkg-ref id="com.cisco.pkg.anyconnect.nvm_v2"/>
</choice>-->
<choice id="choice_secure_umbrella" start_selected="check_upgrade()" start_enabled="enable_module()" title="Umbrella" description="Installs the module that enables Umbrella.">
<pkg-ref id="com.cisco.pkg.anyconnect.umbrella"/>
</choice>
<pkg-ref id="com.cisco.pkg.anyconnect.vpn" version="5.0.00556" installKBytes="58771">#vpn_module.pkg</pkg-ref>
<!--<pkg-ref id="com.cisco.pkg.anyconnect.dart" version="5.0.00556" installKBytes="9986">#dart_module.pkg</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.fireamp" version="5.0.00556" installKBytes="1355">#fireamp_module.pkg</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.posture" version="5.0.00556" installKBytes="67636">#posture_module.pkg</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.iseposture" version="5.0.00556" installKBytes="7965">#iseposture_module.pkg</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.nvm_v2" version="5.0.00556" installKBytes="12621">#nvm_module.pkg</pkg-ref>-->
<pkg-ref id="com.cisco.pkg.anyconnect.umbrella" version="5.0.00556" installKBytes="20522">#umbrella_module.pkg</pkg-ref>
<installation-check script="InstallationCheck()"/>
<volume-check script="VolumeCheck()"/>
<script>
var gUpgradeModules = [];
function check_upgrade()
{
var modulePkgInfo = my.choice.packages[0];
var moduleReceipt = my.target.receiptForIdentifier(modulePkgInfo.identifier);
if (moduleReceipt)
{
var comparison = system.compareVersions(moduleReceipt.version, modulePkgInfo.version);
if (comparison == 0)
{
system.log("Found an existing installed version: " + my.choice.title);
return false;
}
}
gUpgradeModules.push(my.choice.id);
return true;
}
function enable_module()
{
var moduleID = my.choice.id;
return (gUpgradeModules.indexOf(moduleID) > -1);
}
function InstallationCheck()
{
if(!(system.compareVersions(system.version.ProductVersion, '10.9') >= 0))
{
my.result.title = 'Cisco Secure Client';
my.result.message = 'This software requires Mac OS X version 10.9 or later.';
my.result.type = 'Fatal';
return false;
}
return true;
}
function VolumeCheck()
{
// version of VPN being installed has to be higher than the version already installed
var vpnReceipt = my.target.receiptForIdentifier("com.cisco.pkg.anyconnect.vpn");
var vpnPackage = choices.choice_anyconnect_vpn.packages[0];
// if the receipt is not there assume no VPN installed or pre-3.1.1 version so it is OK to install
if (vpnReceipt)
{
// there is a 3.1.1+ version of VPN already installed
// check to see if version in this package is newer
var comparison = system.compareVersions(vpnReceipt.version, vpnPackage.version);
if (comparison > 0)
{
// installed version is newer
my.result.message = 'Newer version ' + vpnReceipt.version + ' of the Cisco Secure Client is already installed.';
my.result.type = 'Fatal';
return false;
}
}
// Check if standalone NVM is installed
var nvmStandaloneReceipt = my.target.receiptForIdentifier("com.cisco.pkg.anyconnect.nvmstandalone");
if(nvmStandaloneReceipt)
{
// if version of standalone NVM installed is greater than AC package version, fail with an error message
var comparison = system.compareVersions(nvmStandaloneReceipt.version, vpnPackage.version);
if (comparison > 0)
{
my.result.message = 'Version ' + nvmStandaloneReceipt.version + ' of Cisco Secure Client - Standalone Network Visibility Module is already installed.';
my.result.type = 'Fatal';
return false;
}
}
return true;
}
function choice_anyconnect_vpn_enabled()
{
if (!enable_module())
{
return false;
}
return (!choices.choice_secure_firewall_posture.selected && !choices.choice_iseposture.selected && !choices.choice_fireamp.selected && !choices.choice_nvm.selected && !choices.choice_secure_umbrella.selected);
}
function choice_anyconnect_vpn_selected()
{
if (!enable_module())
{
return false;
}
var tSelected;
tSelected=((choices.choice_secure_firewall_posture.selected || choices.choice_iseposture.selected || choices.choice_fireamp.selected || choices.choice_nvm.selected || choices.choice_secure_umbrella.selected) || (!choices.choice_secure_firewall_posture.selected && !choices.choice_iseposture.selected && !choices.choice_fireamp.selected && !choices.choice_nvm.selected && !choices.choice_secure_umbrella.selected));
if (choice_anyconnect_vpn_enabled()==false)
{
return tSelected;
}
return (tSelected && my.choice.selected);
}
</script>
<pkg-ref id="com.cisco.pkg.anyconnect.vpn">
<bundle-version>
<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.gui" path="Applications/Cisco/Cisco Secure Client.app"/>
<!--<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.uninstaller" path="Applications/Cisco/Uninstall Cisco Secure Client.app"/>
<bundle CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.vpndownloader" path="opt/cisco/secureclient/bin/vpndownloader.app"/>-->
<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.macos.acsock" path="Applications/Cisco/Cisco Secure Client - Socket Filter.app"/>
<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.notification" path="opt/cisco/secureclient/kdf/bin/Cisco Secure Client - Notification.app"/>
</bundle-version>
</pkg-ref>
<!--<pkg-ref id="com.cisco.pkg.anyconnect.fireamp">
<bundle-version/>
</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.dart">
<bundle-version>
<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.dart" path="Applications/Cisco/Cisco Secure Client - DART.app"/>
<bundle CFBundleShortVersionString="5.0.00556" CFBundleVersion="5.0.00556" id="com.cisco.anyconnect.dartuninstaller" path="Applications/Cisco/Uninstall Cisco Secure Client - DART.app"/>
</bundle-version>
</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.posture">
<bundle-version/>
</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.iseposture">
<bundle-version/>
</pkg-ref>-->
<!--<pkg-ref id="com.cisco.pkg.anyconnect.nvm_v2">
<bundle-version/>
</pkg-ref>-->
<pkg-ref id="com.cisco.pkg.anyconnect.umbrella">
<bundle-version>
<bundle CFBundleVersion="1.7.0" id="com.opendns.OpenDNS-Diagnostic" path="opt/cisco/secureclient/bin/UmbrellaDiagnostic.app"/>
</bundle-version>
</pkg-ref>
</installer-gui-script>
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-17-2022 10:15 AM
There are a few ways to do this.
- The one I recommend is to just get the web deploy package off your ASA. That will only have the modules you guys use enabled.
- The way Cisco recommends is to repackage the AnyConnect package and something called the choices xml. You then run the AnyConnect package that is "cached" on the system from CLI with a switch to use the choices.xml to configure theAnyConnect install.
- The sloppy was is to just install everything, then have a post install script remove what you don't need.
I strongly recommend just using the web deploy package. The custom.xml randomly breaks for no reason, and uninstalling stuff means it was on the system to begin with.
Choices.xml once over.
As with anything Cisco their documentation sucks and is horribly out of date.
Customize Anyconnect Module Installation on MAC Endpoints - Cisco
TL;DR:
- Put the Cisco AnyConnect package in a directory on your Mac, lets use /tmp/AnyConnect
- Make a choices.xml file and place it in /tmp/AnyConnect also
- Use JAMF Composer and package /tmp/AnyConnect directory containing the coices.xml and theAnyConnect package
- Add a post install script to the package, it should look like: Sudo installer -pkg {path to AnyConnect package} -target / -applyChoiceChangesXML {path to choice.xml}
sudo installer -pkg /tmp/Cisco_AnyConnect/Cisco_AnyConnect.pkg -target / -applyChoiceChangesXML /tmp/Cisco_AnyConnect/choice.xml
- Deploy with a JAMF Policy.
- The package will place the AnyConnect.pkg and the choice.xml in the /tmp directory, then run theAnyConnect package with the command in the post install script which tells the AnyConnect package to install and customize the options with the configuration of the choice.xml
An example of what the choice.xml should look like.
1 = install
0 = do not install
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<array>
<dict>
<key>attributeSetting</key>
<integer>1</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_vpn</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>0</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_websecurity</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>0</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_fireamp</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>1</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_dart</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>1</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_posture</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>0</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_iseposture</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>1</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_nvm</string>
</dict>
<dict>
<key>attributeSetting</key>
<integer>0</integer>
<key>choiceAttribute</key>
<string>selected</string>
<key>choiceIdentifier</key>
<string>choice_umbrella</string>
</dict>
</array>
</plist>
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-18-2022 08:27 AM
This seems to work pretty well.