- Jamf Nation Community
- Products
- Jamf Pro
- Re: wireless certificate error
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
wireless certificate error
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-31-2016 02:04 PM
Hello Jamf Nation,
I have a configuration profile that installs an AD certificate to allow access to our corporate wifi. This is a WiFi EAP-TLS Certificate. Is there anything that needs to be addressed with windows server 2012 R2 coming from windows server 2008 R2? (ie. spaces in the certificate template name or anything like that)
The error I get when applying the config policy is:
The 'Active Directory Certificate' payload could not be installed. The certificate server did not return a request ID.
Thank you,
Mark
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-02-2016 05:46 AM
If you are facing the same setup as us, the certificate must be request from your client to your PKI.
use the tools request certificate in keychain.
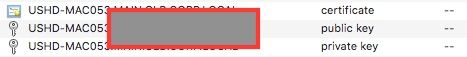
Then install the certificate in the System keychain (for all users to use). it must be compose of 3 elements the public and the private key (generated in the LOGIN keychain at time of the CA request is done) and the certificate on it own. sent back by your PKI admin. if those 3 elements are present but not in the same Keychain it will not work.
This was the only way i was able to join my wireless network, shared certificate are not valid as the EAP-TLS process requires a private key.
(the username should remain blank in the process to join your network)
this process will validate your access. you then need to build your configuration profile.