- Jamf Nation Community
- Products
- Jamf Pro
- Re: An Alternative to the Jamf Intune Integration ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
An Alternative to the Jamf Intune Integration (No more jamfAAD pop-ups)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-19-2021 09:56 AM - edited 11-24-2021 06:51 AM
If any of you are tired of your users receiving jamfAAD pop-ups, I would highly recommend transitioning to device identification using certificates. This method of conditional access allows you to control conditional access directly from your Jamf Pro server. Access is simply determined by the presence of your certificate. (This does require your users to have E5 licenses)
The certificate is deployed via configuration profile...so no more manual registration either. Perfect for zero-touch deployments. To stop the pop-ups unload or delete any launchAgents related to the jamfAAD Agent.
You can read more about this process here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-22-2021 03:14 PM
This is definitely worth looking into. I wonder if an MS Defender for Office Plan 1 or Enterprise Mobility + Security E3 license is enough. Picking up E5's for everyone is definitely not cheap.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-23-2021 08:25 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-24-2021 12:09 AM - edited 11-24-2021 12:09 AM
Will look into this, thanks bwoods. We're already at that license with Defender deployed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-31-2022 06:30 AM - edited 01-31-2022 06:31 AM
#!/bin/bash
# Disable jamfAAD
# Brandon Woods
# January 2022
# This script will remove all jammADD components and disable the microsoftCAEnabled preference key
# Delete JamfAAD.app
rm -rf /Library/Application\ Support/JAMF/Jamf.app/Contents/MacOS/JamfAAD.app
# Delete JamfAAD symbolic link
rm -rf /usr/local/jamf/bin/jamfAAD
# Unload com.jamf.management.jamfAAD.agent.plist
launchctl unload -w /Library/LaunchAgents/com.jamf.management.jamfAAD.agent.plist
# Delete com.jamf.management.jamfAAD.agent.plist
rm -rf /Library/LaunchAgents/com.jamf.management.jamfAAD.agent.plist
# Unload com.jamf.management.jamfAAD.clean.agent.plist
launchctl unload -w /Library/LaunchAgents/com.jamf.management.jamfAAD.clean.agent.plist
# Delete com.jamf.management.jamfAAD.clean.agent.plist
rm -rf /Library/LaunchAgents/com.jamf.management.jamfAAD.clean.agent.plist
# Disable microsoftCAEnabled preference key
defaults write /Library/Preferences/com.jamfsoftware.jamf.plist microsoftCAEnabled -bool false
exit 0; ## Success
exit 1; ## Failure
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-30-2022 01:07 PM - edited 03-30-2022 01:08 PM
@bwoods - Thanks for the Tip. We have been getting a lot of user complaints since rolling out Intune Integration. I would love to make those go away.
I have few question:
- When you are deploying the Config Profile to install the certificate are you installing at the Computer level or User level?
- Are you enabling "Allow all apps access" for the certificate?
- Are there any special information needed in the Certificate Subject or Subject Alternative Name?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-31-2022 09:26 AM - edited 03-31-2022 09:26 AM
@TimArnold. I found that system and user certs work for macOS. I would recommend using a system cert. If your have ADCS or SCEP configured for Wireless you don't even need to deploy a cert. Just upload the Root and Intermediate cert of your ADCS/SCEP cert and the policy will use the PKI cert for conditional access.
I do have "All all apps access" enabled for the certificate.
My San is the same as my wireless cert because my wireless cert and conditional access cert are one in the same. (Let me know if this doesn't make sense.)
Reach out on the #jamf-intune-integration MacAdmins Channel. My username is brndnwds6.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-08-2023 12:30 PM
@bwoods we don't have ADCS/SCEP but we deploy CA and intermidiate cert with config profile to the endpoint which we have to update every year. So you are saying same cert need to be on Azure? And then remove JamfAAD to avoid that pop up? is that means machine don't need to register thorugh JamfAAD if both system (Azure and Jamf) has those cert? Then I guess we don't need to deploy company portal as well right? Please clarify.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-12-2022 07:39 AM - edited 04-12-2022 07:41 AM
This looks real cool. Going to add this to the POC we are doing.
Is there any documentation to create requirements to get the cert from the config policy? The link shows how to setup a CA policy in Azure that requires the presence of the cert to get access, but I do not see where we can leverage Jamf in a way that would only pass those certs to machines we deem compliant. I suppose Smart groups would be the best solution?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-09-2023 11:57 AM
I basically gave this to my security team and we began testing with a dummy certificate. I would suggest using a PKI cert because they automatically renew:
Conditional Access - device identification using certificates - ChrisOnSecurity
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2023 07:31 AM
I was checking that JamfAAD presence before removal. I just found only one location JamfAAD presence which is:
/usr/local/jamf/bin/jamfAAD. Other than that no where i found any JamfAAD presence on my test machine. But still I am getting pop up that same error. So is that will help me to run your script? And another thing for your information we are not using Jamf connect, we are using Jamf Pro. As per Microsoft JamfAAD is for Jamf connect not for Jamf pro. Any comment on this please?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-23-2023 11:57 AM - edited 02-23-2023 12:01 PM
@sharif_khan I noticed that some of my users started getting prompted again a few weeks ago. Jamf made changes to the "jamfAAD.app". They changed the name to the "Jamf Conditional Access.app".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2023 12:15 PM
@bwoods Thanks for reply. Here I make some changes which I think need to work your script.
# Delete JamfAAD.app
rm -rf /Library/Application\ Support/JAMF/Jamf.app/Contents/MacOS/Jamf\ Conditional\ Access.app
But couldnot find any plist for following commands
# Unload com.jamf.management.jamfAAD.agent.plist
launchctl unload -w /Library/LaunchAgents/com.jamf.management.jamfAAD.agent.plist
# Delete com.jamf.management.jamfAAD.agent.plist
rm -rf /Library/LaunchAgents/com.jamf.management.jamfAAD.agent.plist
# Unload com.jamf.management.jamfAAD.clean.agent.plist
launchctl unload -w /Library/LaunchAgents/com.jamf.management.jamfAAD.clean.agent.plist
# Delete com.jamf.management.jamfAAD.clean.agent.plist
rm -rf /Library/LaunchAgents/com.jamf.management.jamfAAD.clean.agent.plist
So do we need to remove these .plist or I am missing something?
Another thing is before write to com.jamfsoftware.jamf.plist, we can add a check point as below
# Disable microsoftCAEnabled preference key
if [ $(defaults read /Library/Preferences/com.jamfsoftware.jamf.plist microsoftCAEnabled) != 0 ]; then
defaults write /Library/Preferences/com.jamfsoftware.jamf.plist microsoftCAEnabled -bool false
else
echo "No change required"
fi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2023 12:33 PM
Ah yes the script, I found that just using a jamf restriction works much better.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-15-2023 02:43 AM - edited 03-15-2023 07:04 AM
Hi, I'm currently setting up and evaluating MCAS for Conditional Access. We've set up the policy as described and it blocks app login when the certificate is not present. When the certificate is present, it doesn't block... but it the (office) apps is failing to authenticate the user.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-15-2023 09:28 AM
I don't know if this helps, but we had to create an exception group in Azure AD that excludes members from all other conditional access policies. Now we just add them to the group during imaging.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-20-2023 05:08 AM
I have a question regarding Jamf and Intune integration. What is actual benifit with that besides Inventory information? Can any one give me some detail informaiton what other benifit we can gain with that integration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-24-2023 05:53 AM
Conditional access and compliance monitoring in Azure and Intune, which enables risk-based sign-in management.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-12-2023 07:21 AM
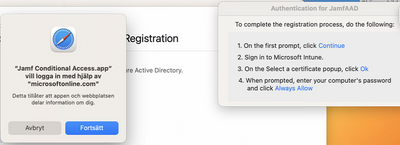
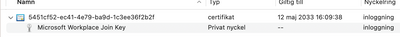
We have just setup "Device Compliance" (the new way) according to the documentation here: https://learn.jamf.com/bundle/jamf-pro-documentation-current/page/Device_Compliance.html in Jamf and are testing it. And for some reason, this (picture below) part doesn't come up sometimes and when it doesn't we have no clue on how to trigger it again. I noticed when i reinstalled one of my test machines, it didn't appear upon registering with Company Portal, another time it appeared and all was working perfectly fine. Now it doesn't matter if we delete the MS-Organization-Access certificate and the key Microsoft Workplace Join Key and then rerun registration with company portal. Any help is much appreciated!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-12-2023 07:30 AM
Hi @nadsad
You can create a EA to confirm that JamfAAD installed or not with the following
#current logged in user variable
currentuser=`stat -f "%Su" /dev/console`
#variable for current logged in user AAD ID cert. and WPJ key
AAD_ID=$(su "$currentuser" -c "security find-certificate -a -Z | grep -B 9 "MS-ORGANIZATION-ACCESS" | awk '/\"alis\"<blob>=\"/ {print $NF}' | sed 's/ \"alis\"<blob>=\"//;s/.$//'")
echo "<result>$AAD_ID</result>"
exit 0
If that is showing and ID then you should check another thing which you have to be full Azure Admin AD and authenticate Jamf Pro instance from Azure AD by login from here
Settings -> Global -> Conditional Access -> macOS Intune Integration -> Jamf Native MacOS Connector Consent and click on Open administrator consent URL
That will take you to Azure AD and login there and approve Jamf pro. That should resolve your JamfAAD pop up issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-12-2023 07:42 AM
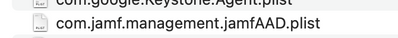
Well that's the thing the consent is done and it's successful (see below picture) and we are using the Settings -> Global -> Device Compliance and not Conditional Access. So it worked first time then i reinstalled my computer and this time the JamfAAD thing didn't show up when i ran the registration with company portal, and you can see i have the key. But what i don't see which usually is created when JamfAAD pops up is /Users/$loggedInUser/Library/Preferences/com.jamf.management.jamfAAD.plist but i don't see this. I also see the device under User -> Devices in Azure. But without the JamfAAD authentication it wont work and iv'e been trying to figure out how to trigger it again but can't figure it out :(
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
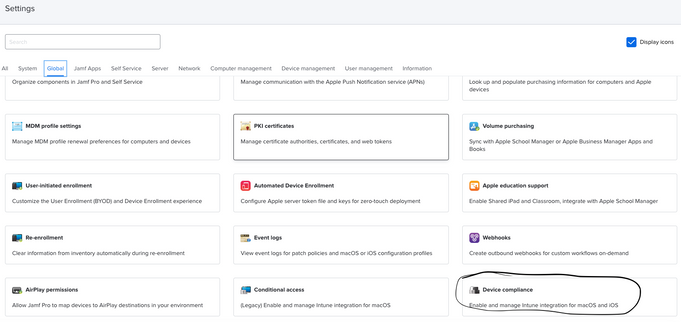
Posted on 05-15-2023 05:23 AM
Hi @nadsad
I have no idea where you got device compliance? In my case Jamf pro (V: 10.46.0) show settings -> Conditional Access. Couldn't find Device Compliance. Can you please direct me how you got that?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 05:28 AM
Here:
But i am back again with the issue. So I have 2 test computers, I reinstalled both of them. Did the registration via Self-Service with the policy and payload "Microsoft Device Compliance" but the JamfAAD authentication never shows up which is supposed to show up once you press "Done" after the registration is done... anyone have any ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 05:31 AM
Gotta add though that our instances are not upgraded yet to 10.46, we have 10.45 still. They will be upgraded between may 19-20.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 05:33 AM
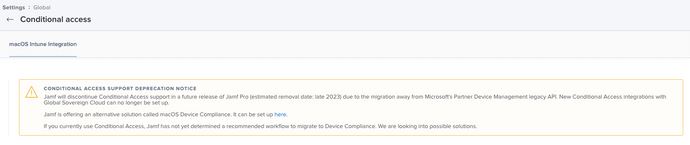
And btw, I would assume you're aware that the "Conditional Access" will be discontinued in the future?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 05:50 AM
I guess your one is Jamf cloud that's why you guys are getting device compince instead of conditional access but our one is on prem Jamf pro and Device Compliance don't support yet on prem. Jamf support still working on that migration. last time when I talked with support team they said they are working on that migration and from 10.46 conditional access will depricated. That's what i am testing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 06:01 AM
Oh i see. And yes we are running Jam Cloud.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-12-2023 07:51 AM
Ok just randomly I just reran registering with company portal and now the JamfAAD popped up and now this was also created. But i tried registering many times, no clue of why it worked now... pretty random and really bad if it happens in production.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 12:49 PM
You should move away from that workflow. Support will end by the end of the year.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-15-2023 11:30 PM
But we are not running conditional access (meaning Settings -> Global -> Conditional Access) we are running Device Compliance which is the new way (meaning Settings -> Global - Device Compliance) this option is there on Jamf Cloud. But anyhow I found another thread about exactly my problem. There is a workaround to run "sudo jamf manage" before running registration with intune via self-service. But it also seems Jamf will solve the issue on version 10.46.
Link: https://community.jamf.com/t5/jamf-pro/jamf-device-compliance-intune-azure/m-p/287327
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-30-2024 09:30 AM
This is a great solution. However, how do you handle BYOD devices? do you deploy certificates to BYOD devices as well or just block all access to devices without the certificate installed?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-30-2024 01:20 PM
We block all devices without a certificate. My org doesn't utilize BYOD.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-30-2024 01:50 PM
Got it! oh, how I wish I could do that too 😅