- Jamf Nation Community
- Products
- Jamf Pro
- Re: Catalina and Symantec EP kernel extension
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Catalina and Symantec EP kernel extension
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 11:36 AM
I have a confi profile to approve the Symantec EP kernel extension. The software installs and i have no prompt to allow, so all looks good.
After reboot i go to the symantec app and the kernel extension is blocked and i have to allow it, and also i get 'full disk access is not enabled' so i click 'fix' and sys preferences opens up and i have to go into 'privacy' and allow full disk access for the 'symantec system extension'!!!
once i allow 'full disk access' SEP goes green and it says 'your computer is protected'
is anyone else getting the crazy results?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 11:51 AM
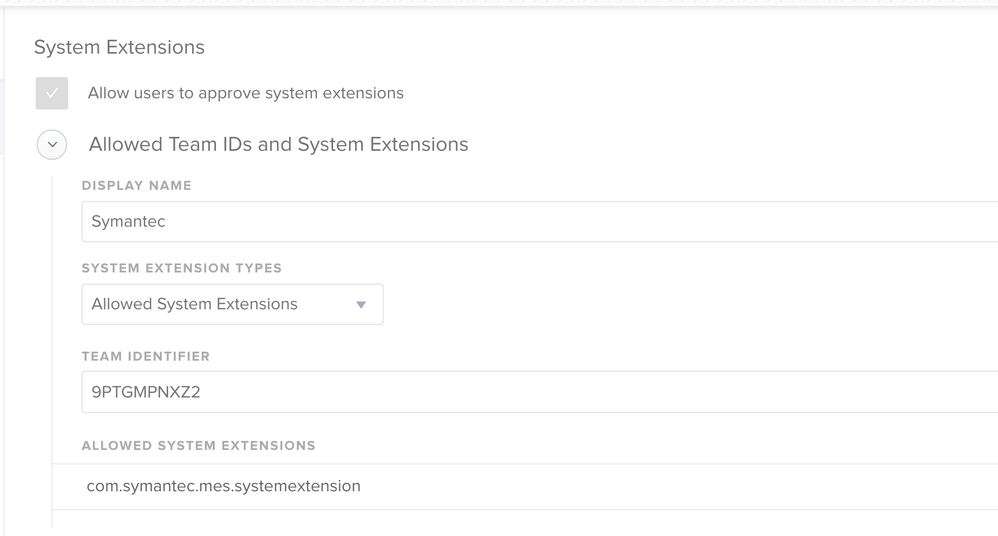
Are you whitelisting the actual system extension or just the Team identifier?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:05 PM
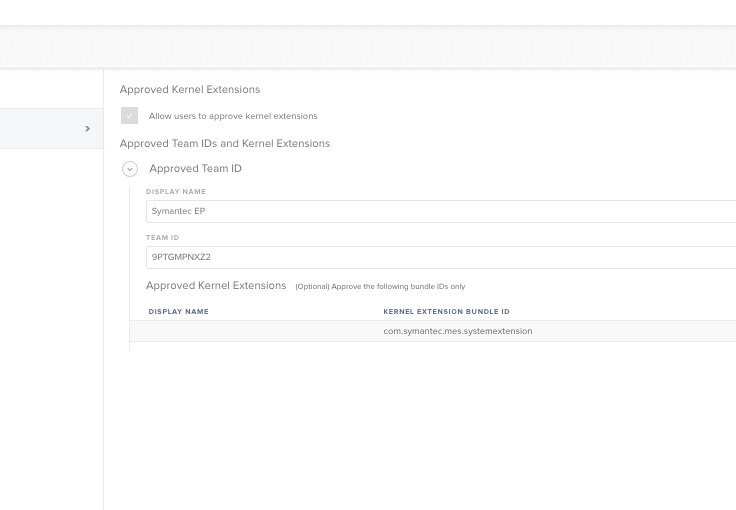
@rqomsiya i just did the 'team identifier'. So i need to add the system extension also now with Catalina?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:10 PM
Yep. That’s what fixes it :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:15 PM
@rqomsiya did i edit this correctly? looks different than yours. maybe because of version
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:18 PM
I follow the Symantec do and wasn't able to get it working...
Here is the "code" I used for PPPC part, is it correct?
identifier "com.symantec.mes.systemextension" and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6]/* exits */ and certificate leaf[field.1.2.840.113635.100.6.1.13]/* exits */ and certificate leaf[subject.OU] ="9PTGMPNXZ2"- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:27 PM
Ping me on slack.. handle is macm
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 12:48 PM
@rqomsiya @gachowski I just basically created a new Config Profile for macOS 10.15 Catalina using the settings here.
https://support.symantec.com/us/en/article.TECH256631.html
The only difference I see is that @gachowski has 'EXITS' while the URL link has 'EXISTS' I updated mine with 'EXISTS'.
@gachowski did you also grab that line from the URL?
so far macs running 10.14 and earlier i'll just keep using the other Config Profile 'Approved Kernel Extension' with just the TeamID
gonna test it and update you with results
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 01:15 PM
Yep but I had to hand type it from the screenshot and obviously I screwed up !! :) Thank you for catching that a few people I had double check missed it too!! : ) I'll update and test and then post here..
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 04:20 PM
I added the two "s"s, : ( no change still not working )
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-27-2020 05:10 PM
@gachowski is the config profile applying? What part is not working?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2020 05:10 AM
check out @NoahRJ s post here: https://www.jamf.com/jamf-nation/discussions/33964/how-to-system-extension-in-macos
I can confirm, that Symantec Endpoint Protection (given the most current build) installs properly given this post. I'm not found of how much CPU it is taking up though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2020 08:53 AM
@tcandela I still have to approver the kernel extension manually ..
@blackholemac thanks I'll give that a try..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2020 09:02 AM
@gachowski looks like i got it to work by using the 3 payloads.
1 - PPPC
2 - Approved Kernel Extensions -----> did not enter any kernel extension bundle IDs, just entered the Team ID
3 - System Extensions
going to test again, this time on a 10.14.6 upgraded to 10.15.2. I uninstalled the previous SEP version from 10.14.6, now its upgrading to 10.15.2
Will install the SEP 10_15 Config Profile then run the self service policy that installs 14.2 RU2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-28-2020 04:12 PM
yep I got it working follow NoahRJ big post at the end of this thread https://www.jamf.com/jamf-nation/discussions/33964/how-to-system-extension-in-macos
Like blackholemac said !!!
Thank you everyone!!!
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-29-2020 06:31 AM
@gachowski it works following that post but I talked to @NoahRJ and he's not comfortable deploying it yet given it's high CPU consumption. I have a case open with support, but I'm still in the "hey I can't run a .exe file on a Mac to help you get what your engineers are asking for" phase. I have a good support contract with them, but the people I get on the other end of their phones are fairly useless. One comment earlier in the case was "don't worry about this article here (https://support.symantec.com/us/en/article.TECH256631.html). Instead, you should use an MDM solution to push the software out to your clients." <Sighs> Anyway, feel free to keep me in the loop with your travels on Symantec. I am going to try to test NoahRJ's technique against 10.15.3 today and hope it either helps or at least didn't break anything. There also is a new build of SEP that dropped two days ago, BUT it didn't list anything in the release notes relevant to the Mac.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-30-2020 06:46 AM
I am seeing 50% CPU use most of the time and many times closer to 80%
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-30-2020 09:08 AM
I have a case open with Symantec right now on the issue...They had me collect spindumps today... Of course when I go to collect them they aren’t hogging resources until I’m not paying attention and don’t think to open activity monitor and capture. I’ve got one machine that I did capture a good dump on and I’m gonna send them that today. Do you have a case number open on the same issue with them? My case number is 31638747
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-16-2020 08:04 PM
Just curious. Whats the difference between Kernel Extension and System Extension? Tried to google it but not much luck. They seem roughly structured the same way. Or is Kernel before Catalina and System for Catalina?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-25-2020 05:35 PM
Classic race condition:
Endpoint Protection re-prompts user to authorize system extensions after macOS upgrade to 10.15
If macOS has already been upgraded to 10.15 with SEP installed, without taking precautions above, then remove and re-apply the JAMF configuration policy for Symantec. You must do this BEFORE the SEP GUI is opened for the first time after the macOS upgrade, otherwise you will get a warning about the extensions and they will be stuck in "awaiting user authorization".
If the SEP client GUI has already been open and the extension warning displayed then removing/re-applying the configuration policy will not help. You will need to uninstall SEP by using the Uninstall command in the client's "Symantec Endpoint Protection" menu. Do not use RemoveSymantecMacfiles—it does not properly remove the new system extensions. Then re-install SEP and the configuration policy should be properly recognized.
https://donmontalvo.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-27-2020 07:57 AM
I must say this thread was super helpful when I deployed Symantec to 70+ Macs. That being said, I was to emphasize how crappy Symantec is. The update required two reboots to get protection working again. Big fan of Malwarebytes + Cylance or Jamf Protect. SEP SUCKS!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-09-2020 06:56 AM
@jared_f been looking at jamf|PROTECT for auditing, but curious since you mentioned, are you using it for antivirus/malware?
https://donmontalvo.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-25-2020 10:48 AM
Adding com.symantec.mes.systemextension in the allowed system extensions field seems to have fixed my issue.