- Jamf Nation Community
- Products
- Jamf Pro
- CrowdStrike Configuration Profile | BigSur
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
CrowdStrike Configuration Profile | BigSur
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-01-2020 03:17 PM
If you have to install version 6 and above of crowdstrike on bigsur, have to install their unsigned profile first. This profile only be uploaded and distributed with MDM solutions.
In order to upload to MDM, that profile needs to be signed first.
Original location of the profile --- > https://supportportal.crowdstrike.com/s/article/Tech-Alert-Preparing-for-macOS-Falcon-Sensor-6-11
1 - Follow Steps explained here,
https://www.jamf.com/jamf-nation/articles/649/creating-a-signing-certificate-using-jamf-pro-s-built-in-certificate-authority
If jamf freezes during generate of pem, ignore it & refresh the page
2- After it is generated under keychain, please locate the certificate and look for "Subject Key Identifier" Value. Copy it to clipboard and remove spaces.
3- Generate signed version of the mobile config profile following below command at terminal
sudo /usr/bin/security cms -S -Z SubjectKeyIdentifierValue -i ActualPathofUnSignedProfile -o OutPutWhereYouLiketoSaveSignedProfile
- Labels:
-
Configuration profiles
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-01-2020 06:08 PM
After configuration is in place, please create policy to push the install package with a below bash script
either you can place CID in the script or add as a parameter to jamf script options part
!/bin/bash
if [ -f "/Applications/Falcon.app/Contents/Resources/falconctl" ] ; then
sudo /Applications/Falcon.app/Contents/Resources/falconctl license Your CID Here
fi
echo "Crowdstrike installed successfully"
exit 0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-02-2020 08:30 AM
After it's been created, what is the best way to deploy the new .mobileconfig file out to machines within JamF?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-02-2020 10:44 AM
Jamf - computer - configuration profile (after signed file is uploaded to jamf above process, it will create for you)
You can push configuration profile to all or dedicated smart groups within jamf
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-02-2020 10:45 AM
Jamf - computer - configuration profile (after signed file is uploaded to jamf above process, it will create for you)
You can push configuration profile to all or dedicated smart groups within jamf
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-02-2020 10:54 AM
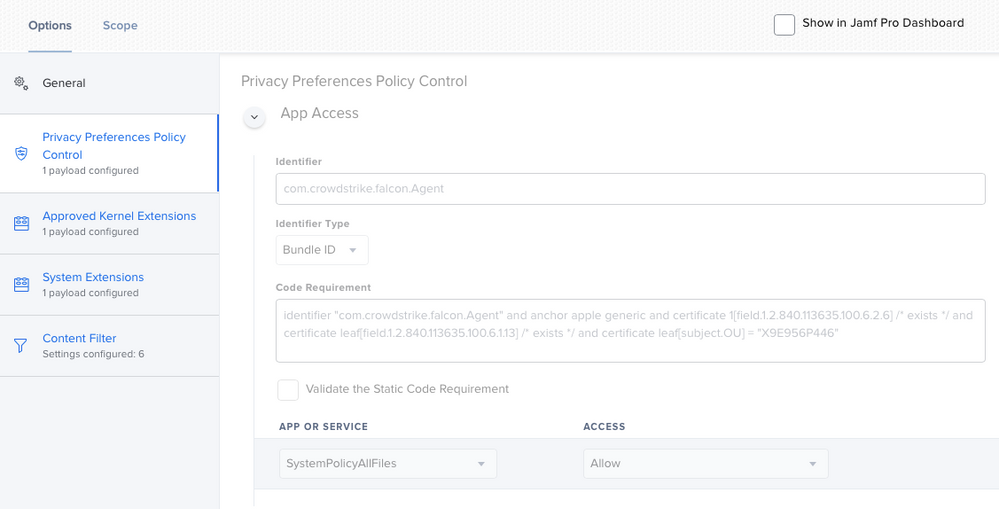
You should also be able to manually enter the info rather than uploading a .mobileconfig file.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-03-2020 10:14 AM
@VintageMacGuy Thats is possible. As per Jamf Technician, creating that profile manually could cause issues to whitelist all stuff crowdstrike requires on their raw profile.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-03-2020 12:45 PM
Just curious - if I sign the mobile config does it have to be renewed yearly? I see that the certificate expires in a year, but no mention of that for the mobileconfig.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-07-2020 09:40 AM
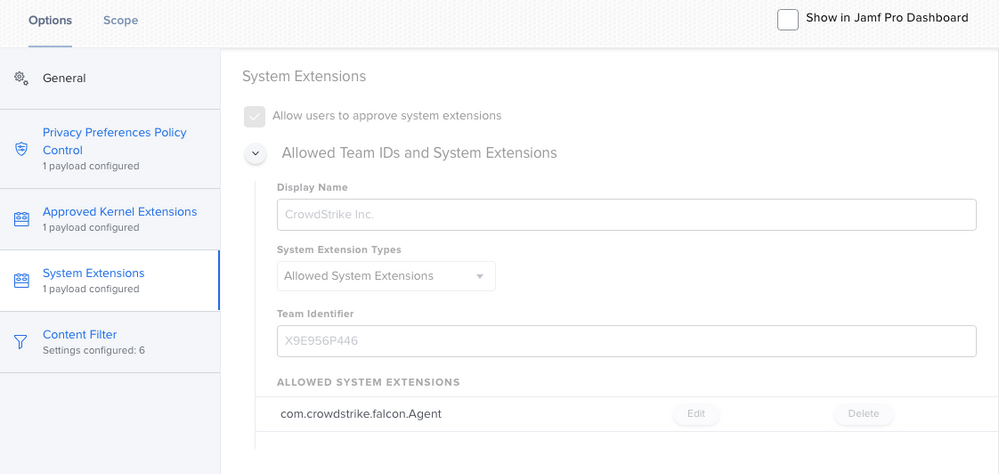
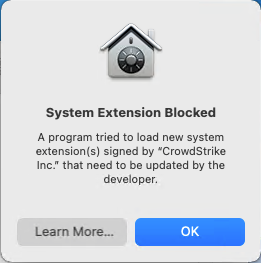
Thanks for this but I'm still having issues getting CrowdStrike working, specifically the System Extension. Any advise would be great. I've signed the provided profile from CrowdStrike and still no go. I've also built a clean profile from scratch best guessing the system extension section from the download config. No matter what I've tried after installing CrowdStrike in a clean VM I'm always prompted to approve the System Extension.
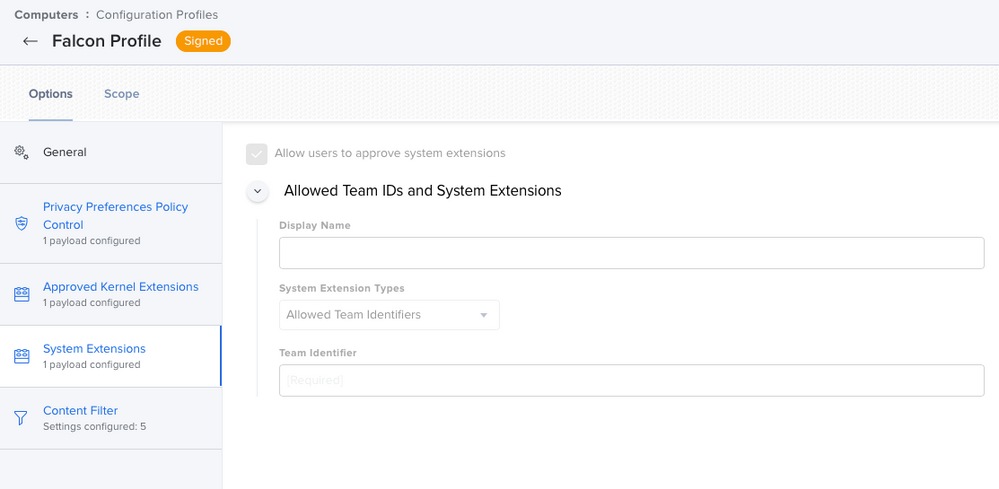
Signed profile from Crowdstrike, System Extension is blank??
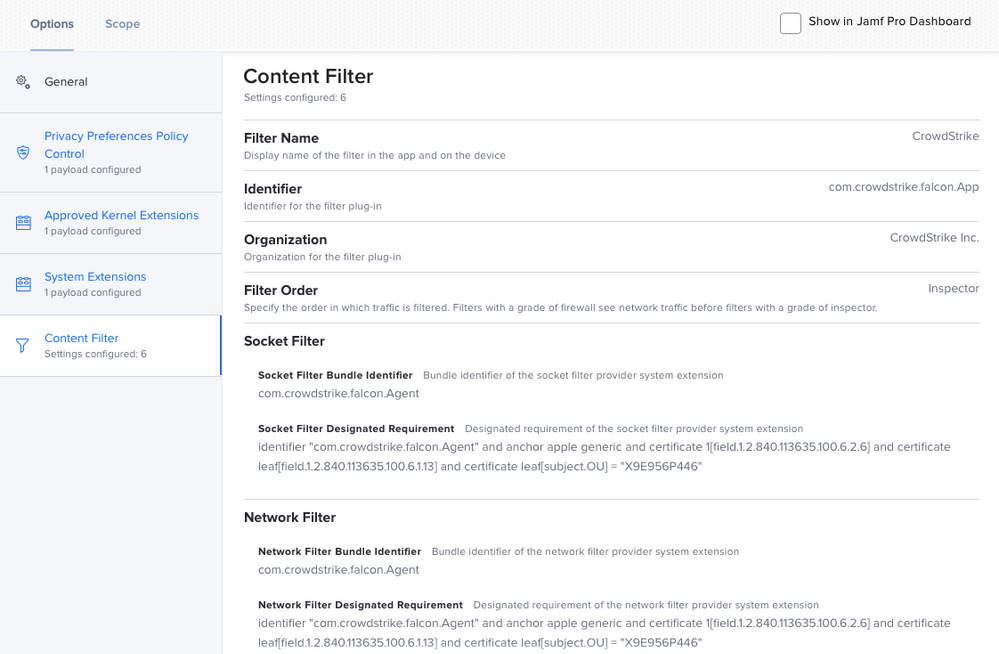
Configuration profile I built based on the provided CrowdStrike profile
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-07-2020 03:04 PM
I tried the original method exactly but still came up with this error:
"IMXXX-X0:~ root# /usr/bin/security cms -S -Z "SubjectKeyIdentifierwithnospaces" -i /Users/xxx/Desktop/Falcon Profile.mobileconfig -o /Users/xxx/Desktop/Signed Falcon Profile.mobileconfig
security: failed to find identity with subject key ID: "SubjectKeyIdentifierwithnospaces": The specified item could not be found in the keychain.
security: could not find signing identity for subject key ID: "SubjectKeyIdentifierwithnospaces"
security: problem signing
I tried searching on that error message but to no avail. Any guidance/troubleshotting steps I can take to help would be appreciated
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-07-2020 03:06 PM
@inflicted Move the certificate from login to system and try again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 01:26 PM
@ubcoit Moving it from login to system and trying again still does not work
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 02:21 PM
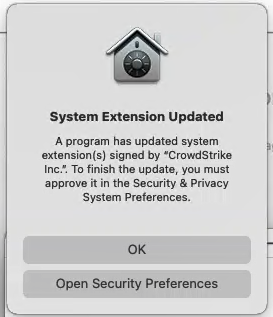
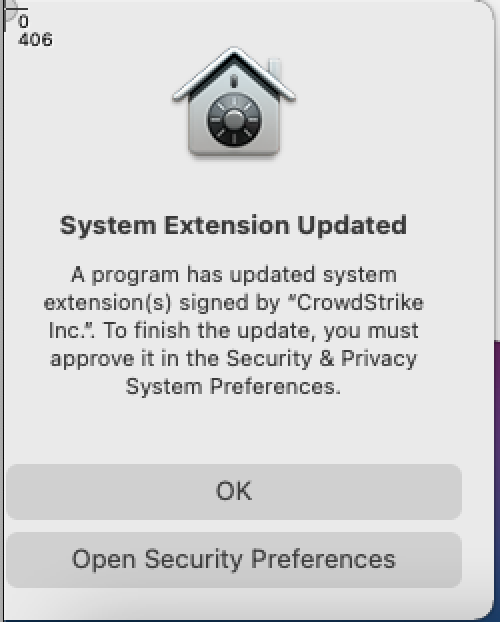
@inflicted I'm not certain I'm doing this right but this is how I signed the provided configuration profile from CrowdStrike. Having said that, even after signing it and uploading it to Jamf (jamf shows it as signed as does the client), I still get prompts for the System Extension but it's not that the System Extension is blocked, it's that it's been updated.
Follow this guide, create a CSR and I used Jamf to sign it.
https://www.macblog.org/post/signing-configuration-profiles/#:~:text=Sign%20in%20to%20the%20Apple,button%20near%20the%20upper%20right.
Search on page for the headings:
Signing Profiles for Trust Only by Jamf-enrolled Clients
Create A CSR on Your Mac
Upload the CSR to your Jamf Pro Server
Once I had the pem file, I loaded it into the keychain, note I didn't get the prompt that they do in their post as to where to install it (10.15 here). It just appeared for me under login. I set the certificate to trusted in the keychain then attempted to sign it while it was in login and it failed for me with the same error as you get. I moved the certificate, private and public key to "System" and ran the security command again. It creates a signed profile but I do get the following warning on create.
Warning: unable to build chain to self-signed root for signer "(null)"
Checking a client with the profile installed, it shows CrowdStrike Inc. Verified and it's signed by my organization (Common name).
I used -N instead of -Z with the security command.
sudo /usr/bin/security cms -S -N COMMON_NAME -i "Falcon Profile.mobileconfig" -o Signed.mobileconfig
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 03:20 PM
Note that CrowdStrike again changed their recommended mobileconfig file last week. They now added com.crowdstrike.falcon.App to the Privacy Preferences Policy Control in addition to com.crowdstrike.falcon.Agent. We're now testing with these new settings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-08-2020 03:51 PM
@DanielHirt I pulled a fresh profile down from CS today and signed it, uploaded it to jamf, snapped my VM back, installed the config profile and then installed CS 6.12. I still get the System Extension prompt as noted above, "A program has updated the system extension...". Now that I look, I see you are correct, a new PPPC addition. Checking the profile I manually created as well I have Socket Filter and a Network Filter in Content Filter whereas the profile from today only seems to have a Network Filter.
I've asked a coworker for a second set of eyes on this to work through the process fresh and see their result.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-09-2020 11:44 AM
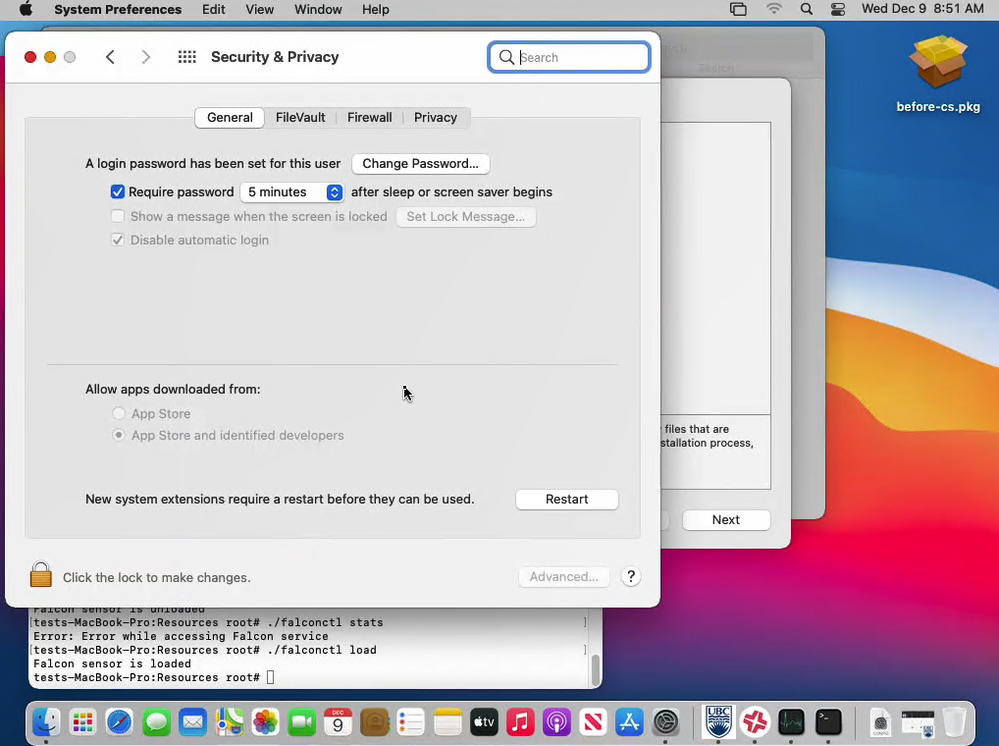
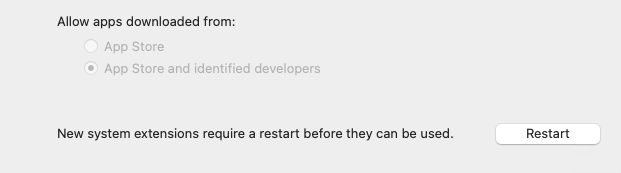
Coworker had the same results I did. CS provided signed profile or building a profile in Jamf, System Extension needs to be approved as it's been updated. My coworker thought of something and tested, disable the network shortly after (10 - 15 seconds) the installation and licensing of CrowdStrike. You'll notice no prompts and CS is running (assuming your profile is correct). If you check System Preferences > Security it will show "New system extensions require a restart before they can be used" but there were no prompts indicating this and CS is running, or appears to be.
Click restart (make sure network is still disabled)
Once back in to Big Sur, confirm cs is running /Applications/Falcon.app/Contents/Resources, falconctl stats and/or falconftl load/unload. In the stats command it will show as not connected. Check System Preferences > security and everything is happy. Let it sit for 10 minutes, nothing. Now enable network. Within a few minutes you'll get the System Extensions updated prompt. So what's changing?
If anyone would like to try the above to confirm that would be great!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-10-2020 09:44 AM
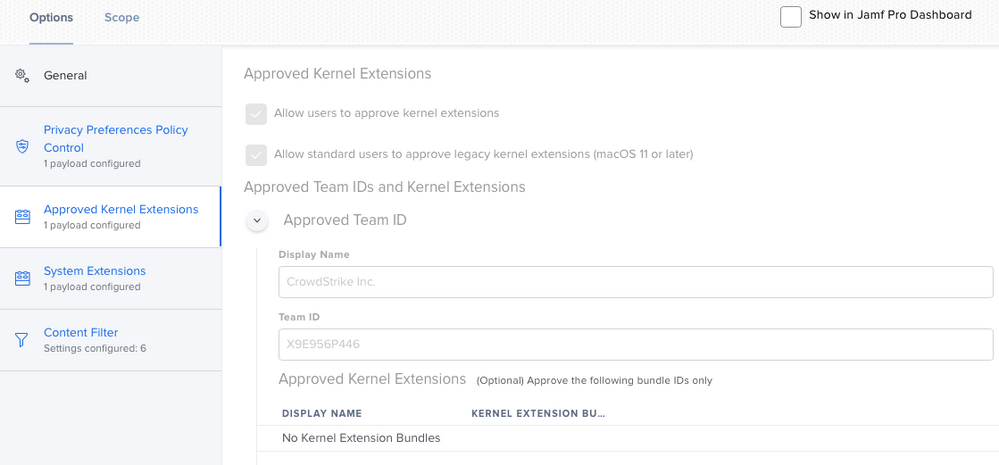
@ubcoit Just my 2 cents... I manually setup the config profile in Jamf pretty much identical to what you have above without the Approved Kernel Extensions and don't receive any prompts for approval/update and don't have to restart because of approved kernel extensions. I've tested this on macOS 10.15 and 11.
If you have Mac's that are below macOS 10.15 I would recommend creating a separate config profile for the Approved Kernel Extensions, anything above 10.15 will use the System Extension. You are seeing the note to restart in Sys Prefs because of the kernel extension approval.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-10-2020 11:52 AM
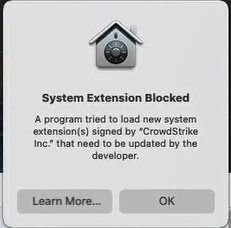
@Joyrex Thanks for the suggestion. I removed the Kernel Extensions portion from my Configuration Profile and tested again. Snapped my VM back, applied the configuration profile and then installed CS (tried both v6.12.125.05 and v6.14.12704.0) and licensed. I still get the "New system extensions require a restart before they can be used" after install. Letting the machine idle for a minute or two, I then get the below prompt which is different than past prompts.
System Extension Blocked
A program tried to load new system extensions(s) signed by "CrowdStrike Inc." that need to be updated by the developer
This sure sounds like a kernel extension trying to load.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-10-2020 12:12 PM
@ubcoit Do you still see the restart note in Sys Prefs after the pop up?
Have you tried testing another VM or Mac?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-10-2020 01:14 PM
@Joyrex "New system extensions require a restart before they can be used" shows up immediately after installation.
This prompt appears within a couple minutes after installation.
All my testing has been done in the same VM, just snapping back to a clean state (enrolled in Jamf but no CS installed). A coworker was doing testing as well (prior to removing the kernel extension) with the same results on actual hardware.
I'll see if I can find hardware to test on.
Thanks again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-10-2020 03:53 PM
@Joyrex I did a clean installation of Big Sur on a Mac Mini and tested, same result. I get the prompt "System Extension Blocked" A Program tried to laod new system extension(s) signed by "CrowdStrike Inc." the need to be updated by the developer."
I will mention though that the "New system extensions require a restart before they can be used" appearing in System Preferences > Security is actually a result of the configuration profile applying. This is not a result of the installation of CrowdStrike. On this Mac Mini I noticed this and rebooted the Mac Mini prior to installing CrowdStrike. So to be clear, before I installed CrowdStrike I checked System Preferences > Security and there was nothing to approve there.
I've engaged CrowdStrike support and they are indicating that it's a known problem with Jamf Pro and have documentation on to sign the configuration profile from them. To which I told them I've done but it's still not working. They said to contact Jamf support anyways as perhaps there is a signature problem with the signed and uploaded configuration profile.
I'll be reaching out to Jamf support in the morning.
Cisco AMP is working, we've built the configuration profile and as long as it's sent to the device before AMP is installed, it's all good.
Thanks again for your suggestions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-11-2020 07:51 AM
@ubcoit That doesn't seem right since the config profile is not installing a kernel extension. Maybe try building a new config profile manually in Jamf if you haven't tried that already.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-15-2020 07:06 AM
@ubcoit I am having the same exact issue, and have gone through all the steps in this thread before searching for it on Jamf Nation. I'm both happy and sad that I'm not the only one with this issue (sad because I'm not sure what the issue is). I've built manually, pulled from CS and signed, tried CS unsigned. All attempts unsuccessful. Has Jamf support been able to get back to you with anything on this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-15-2020 08:10 AM
@Joyrex I've rebuilt the profile in Jamf three times now, all the same result.
@lukasindre Still waiting on Jamf support, I'll report back what I find.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-17-2020 11:28 AM
For anyone that has this working after manually configuring the profile in Jamf Pro, can you please post screen shots of your profile?
Also couldn't hurt seeing what the profile looks like on a client in System Preferences > Policies as well.
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-23-2020 01:13 PM
I'm having the same issue except the system extension says it's being updated rather than installed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-23-2020 01:32 PM
@ubcoit Support got back to me saying there is a product issue and they tied my case to it. Any updates from them for you?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-23-2020 01:57 PM
@araney That's the problem I'm having. Either with a signed CS configuration profile uploaded or manually creating it in Jamf, same result.
"A program has updated a system extension(s) signed by CrowdStrike..."
If you disconnect network after you install/license Crowdstrike you won't get a prompt. CS is running, no prompts, reboot and let it sit, with no network life is good. Turn network back on and within a few minutes the prompt comes up. Seems to me CS is getting an update from the cloud.
@lukasindre Yes, Jamf confirmed a known product issue (PI) in regards to this. Still working with Jamf and CS support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-28-2020 11:46 AM
Apologies for all the spam. I had been trying to post for a while but kept getting a notice that my posts were being moderated until they all showed up at once. Doesn't seem to be a delete button...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-28-2020 11:46 AM
See above...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 12-28-2020 11:46 AM
See above...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-07-2021 09:50 AM
@ubcoit Any progress on your cases?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-11-2021 11:25 AM
@CAMarchand Nope, still working (slowly) with support on this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-11-2021 11:32 AM
my experience FYI.. I am 100% sure that the CS provide profile worked on 11.0.1 and before 12/17.. however it's now stopped working on both 11.01 and 11.1. I agree with @ubcoit CS cloud is pushing an update that is conflicting with the profile..
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-15-2021 05:59 AM
I'm using the one CS provided (https://falcon.crowdstrike.com/support/documentation/22/falcon-sensor-for-mac#prerequisite:-using-mdm-to-sync-profiles-before-installing-or-upgrading), and I get the following error filling my Jamf console for all devices: "<Exception> -[__NSCFConstantString objectForKeyedSubscript:]: unrecognized selector sent to instance 0x7fff8ad8b0e0"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-20-2021 11:58 AM
Just tested this today, seeing the same thing as the rest on this thread.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-20-2021 12:14 PM
I'm still working with Jamf and CrowdStrike support on this. The last go I sent CS wireshark data and logs for them to analyze and with Jamf I've sent them demo videos of the process and my CS installer and activation code in hopes that they attempt the process on their end. It's the back and forth email tag. Tag, their it!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-21-2021 07:04 AM
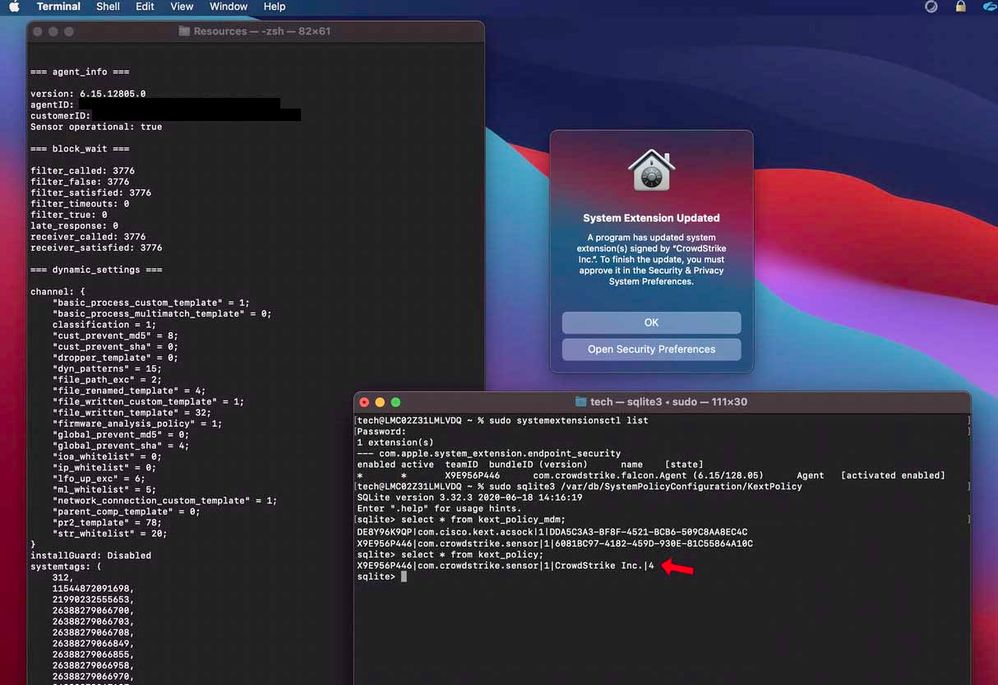
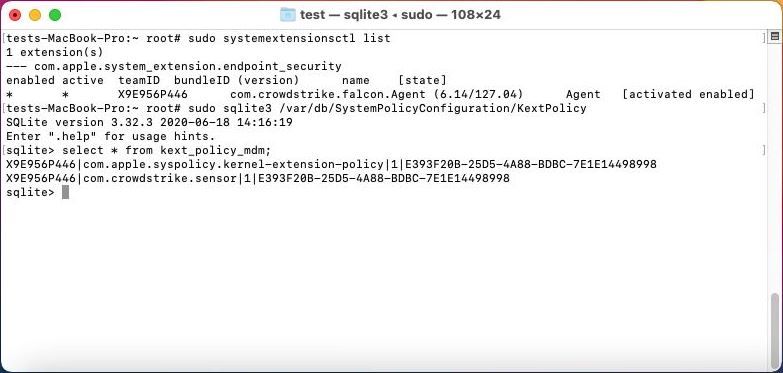
I'm having the same issue.... but only on machines that start on BigSur. -- Machines that have Catalina installed, then upgrade to BigSur, do not receive the prompt for systemextension update.
I suspect it's related to how BigSur is handling kext_extension trust vs. those inherited via MDM, and how CS 'reconfigures its self'
I also used the demo profile from CS as my template...
The Catalina -> BigSur machines do not have this pesky little '4' in the kext_policy table, but those that start on BigSur do...
I've definitely been beating my head against the wall on this 'prompt to allow update' nonsense....
@ubcoit -- I'm anxious to hear what JAMF/CS were able to figure out here...
HALP!!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-21-2021 10:00 AM
Interesting. I haven't testing applying the profile to 10.15 and upgrading. All my testing has been done on Big Sur. I checked mine and I don't have the mystery 4.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-21-2021 10:18 AM
The kext_policy_mdm table doesn't have the mystery '4' -- but the kext_policy table does. ( inherited )
Oddly enough, the upgrade from catalina machines are NOT having any issue as long as they had the config profile ahead of time... it's the ones STARTING on BigSur that do...
There was another post ( https://www.jamf.com/jamf-nation/discussions/37623/falcon-sensor-system-extension-approval )
that suggested completely separating out KEXT from SYSEX from PPPC etc.... which makes perfect sense...
Especially since the M1 machines absolutely HATE LIFE when you have anything legacy in a cfg profile...
I'm going to see if separating out KEXT/SYSEX solves the issue...
If you could share your raw config profile that might be super-helpful as well...
e.g. download .mobileconfig file from JSS, then: security cms -D -i Falcon SYSEX BigSur.mobileconfig
Thanks!