- Jamf Nation Community
- Products
- Jamf Pro
- Re: Cylance and 10.13.4
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on
03-30-2018
07:51 AM
- last edited on
03-04-2025
08:34 AM
by
![]() kh-richa_mig
kh-richa_mig
Hi There,
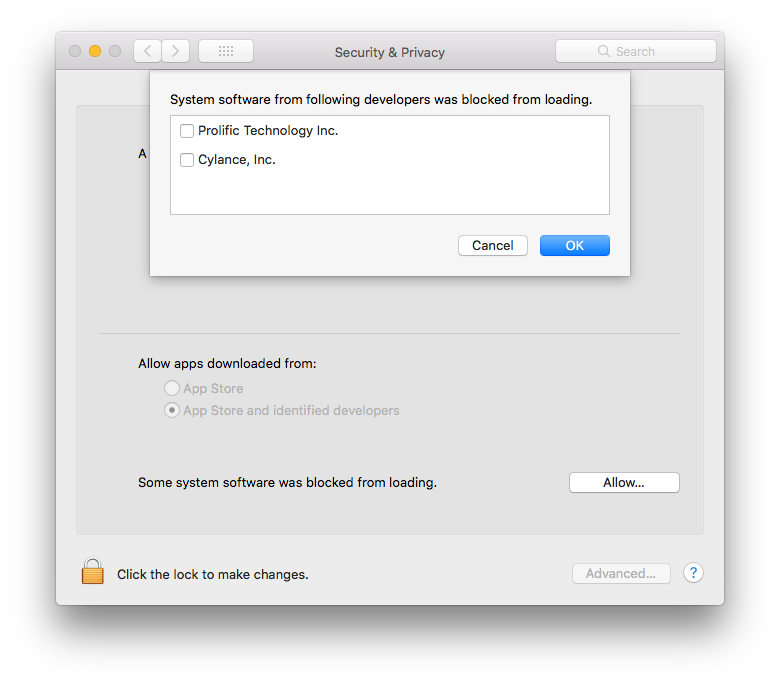
We have computers in our environment that have Cylance installed prior to 10.13.2 when the requirement to consent via System Preferences was Required
Currently all computers get Cylance Protect upon enrollment. If a computer is fresh out of the box it typically comes with 10.13.1, so we haven't had to enable this setting before.
10.13.4. came out today, and the attached error message appears prior to the upgrade.
Is there a way from a root level to consent to this application?
I've already alerted our vendor of Cylance that this issue happens upon upgrade of 10.13.4. Since I have consented to Cylance running on this machine, I have closed and re-opened the application but it still does not function. I have not yet restarted.
Solved! Go to Solution.
- Labels:
-
Jamf Pro
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-03-2018 02:32 PM
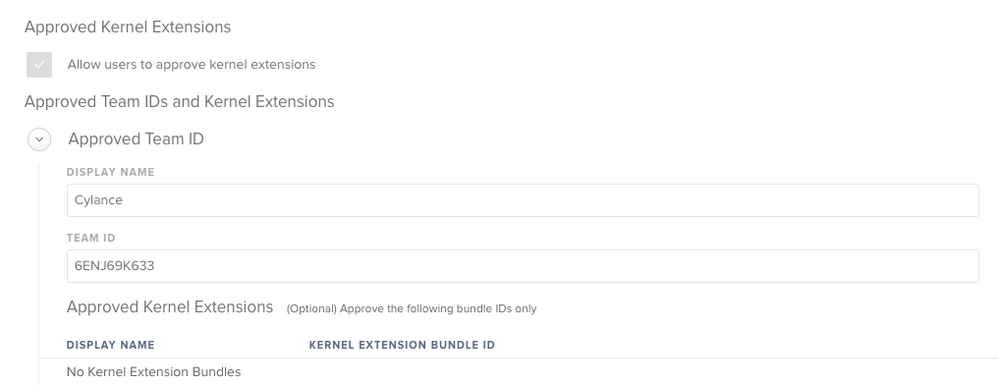
@SDamianoINWK here you go, keep in mind you need to be on Jamf Pro 10.2
https://jumpt.wordpress.com/2018/04/03/approve-kernel-extension-via-profile/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-30-2018 08:16 AM
I believe in 10.13 Kernel Extensions were automatically loaded if a device was enrolled in MDM. This changed with 10.13.4 and you are now required to allow the extensions. These 2 articles might help you.
https://developer.apple.com/library/content/technotes/tn2459/_index.html
[https://support.cylance.com/s/article/Agent-Installation-macOS-High-Sierra-Secure-Kernel-Extension-Loading](lhttps://support.cylance.com/s/article/Agent-Installation-macOS-High-Sierra-Secure-Kernel-Extension-Loading)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-30-2018 08:47 AM
We are seeing this same issue with Avast on the 10.13.4 beta, to be clear Avast is installed by Jamf in our environment, according to Apple's own documentation from https://developer.apple.com/library/content/technotes/tn2459/_index.html (Note this doc hasn't been updated since 2017-09-08)
"For workflows that leverage mobile device management (MDM), all systems with a valid MDM profile installed will not require user approval to load any properly-signed kernel extension."
I take this to mean Avast, Cylance, etc.. should be able to load a kernel extension with Jamf's MDM profile installed on the system but this doesn't appear to be the case in 10.13.4, at least in the beta. Hopefully, Apple will provide a path forward when 10.13.4 is released.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-30-2018 09:15 AM
Kernel Extensions are only automatically loaded if the mac is DEP, Apple changed it's mind.
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-30-2018 10:39 AM
In Jamf Pro 10.3 there is a new Config Profile payload to specifically list approved kernel extensions by team ID. Push it out as a computer level profile prior to the Cylance install and you should be good.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-02-2018 07:47 AM
Can someone share the config profile (or the domain and plist examples) for enabling these, for those of us not yet on 10.3, that can be delivered as a Custom Profile?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-02-2018 02:16 PM
https://developer.apple.com/library/content/featuredarticles/iPhoneConfigurationProfileRef/Introduction/Introduction.html
Search for "Kernel Extension Policy"
C
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-02-2018 02:51 PM
@KSchroeder I have not been able to successfully deploy this MDM payload as a custom setting, which makes sense based on what we know about the strictness of the security framework. Some people say they've done it, but I think they very likely tested it incorrectly. For example, a user approval of a kext will live in the NVRAM and survive a reimage, so a person testing whitelisting on a device might think it's working but it's actually using an old approval from before a wipe/reinstall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-03-2018 02:32 PM
@SDamianoINWK here you go, keep in mind you need to be on Jamf Pro 10.2
https://jumpt.wordpress.com/2018/04/03/approve-kernel-extension-via-profile/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-04-2018 08:29 AM
Thanks...but I need to see how to do it for 10.1.1, we haven't upgraded yet (and are a bit gun-shy, after the 9.98 --> 10.1.1 upgrade completely broke out LDAP configuration, which is admittedly non-standard). We're working to figure this out on the version we're on currently using a Custom payload. Even more urgent now, as 10.13.4 un-approved some of the existing pre-installed KEXTs (our current AV) and now any users will be prompted to approve them again!
Thanks Apple!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-04-2018 08:38 AM
So I am on Jamf Cloud, and I am currently on 10.2, and I was able to successfully push out KEXT profiles using that configuration payload to computers and it resolved my issue with 10.13.4. I'm not sure why I was able to do this in Jamf 10.2.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-04-2018 10:59 AM
@KSchroeder I suggest you either use Profile Manager or setup a test environment for at least 10.2, build the profile there and download it.
Import into your production jamf and push it out. To prevent Jamf Pro from making changes to it make sure to keep it in read only mode.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-14-2019 12:27 PM
Hi All,
Is anybody seeing that the driver gets blocked again even if the config profile is loaded, and then an upgrade to Mojave happens?
We are going from 10.13.3 to 10.14.3 and seeing that Cylance Kernel extensions needs to approved again, and reinstalling Cylance doesn't solve it. I have to uninstall and re-install.
-Peter
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-14-2019 12:45 PM
Interesting. I can test this shortly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-14-2019 01:30 PM
OK, my test wasn't a perfect copy of yours. I just realized that I went from 10.13.6 to 10.14.3. Everything worked for me, but I'm wondering that since you started just before 10.13.4, things got wonky on you. However, with that said, all of my approved kernel extensions (including Cylance) worked just fine in a single test.