- Jamf Nation Community
- Products
- Jamf Pro
- Re: Jamf Configuration Profiles Stuck Pending
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Jamf Configuration Profiles Stuck Pending
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-11-2021 09:18 AM
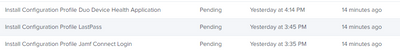
I am having a handful of systems with Configuration Profiles stuck in pending state. Does anyone know of a fix for this?
These systems are all Automatic Device Enrolled, they are checking regularly to jamf. I have tried having them reboot, sending blank push from management commands.
These commands have been pending for months.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-29-2024 01:06 PM
Stuck pending profiles are a symptom of MDM identity or mdm communication errors, not the other way around. The EA simply alerts you of such an issue before you stumble across any related stuck pending profile(s) they create. It at least eliminates this as a variable in troubleshooting (even proactively if you implement a smart group with alert). But it's not going to alert you of stuck profiles in general if that's what you're after.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-29-2024 01:14 PM
Frankly I don't see why Jamf couldn't add a smart group criteria value for 'profile pending'. Then we could at least get crafty with detection. ¯\_(ツ)_/¯
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-29-2024 02:24 PM
It's time for a feature request!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-04-2024 12:43 PM
I created this feature request to give us the smart group criteria to track down Macs with MDM issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-12-2024 09:47 AM
still under Reviewing since March 2024
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-12-2024 07:02 AM - edited 11-12-2024 07:02 AM
Its November 2024 and still no movement on this request.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-14-2024 03:33 AM - edited 03-14-2024 03:35 AM
After I opened a case with Jamf about our MDM communication issues, I got these three extension attributes.
#!/bin/bash
result=$(log show --style compact --predicate '(process CONTAINS "mdmclient")' --last 1h | grep "Unable to create MDM identity")
if [[ $result == '' ]]
then
echo "<result>MDM is communicating</result>"
else
echo "<result>MDM is broken</result>"
fi
#!/bin/bash
APNS_certificate=`/usr/sbin/system_profiler SPConfigurationProfileDataType | awk '/Topic/{ print $NF }' | sed 's/[";]//g'`
if [[ "$APNS_certificate" = "" ]]; then
echo "<result>"NA"</result>"
else
echo "<result>"$APNS_certificate"</result>"
fi
#!/bin/bash
theIDs=$(security find-identity -v | awk '{print $3}' | tr -d '"' | grep -E '^[A-Za-z0-9]{8}-[A-Za-z0-9]{4}-[A-Za-z0-9]{4}-[A-Za-z0-9]{4}-[A-Za-z0-9]{12}$')
echo $theIDs
if [ -z "$theIDs" ]; then
echo "<result>ERROR - There appears to be zero keychain identities matching a UUID on this system.</result>"
exit 1
else
echo "At least one keychain identity found on this system, proceeding..."
fi
for i in $theIDs; do
info=$(security find-certificate -c "$i" | grep issu | awk '{print $3, $4, $5, $6, $7}' | tr -d '"')
echo $info
if [[ $info == *"BUILT-IN CERTIFICATE AUTHORITY"* ]]; then
echo "found you!"
expiry=$(security find-certificate -c "$i" -p | openssl x509 -noout -enddate | cut -f2 -d"=")
echo "<result>$theIDs + $expiry</result>"
fi
done
exit 1
For the first one you may want to change the timeframe. I changed it to "--last 1h". Originally, it was "--last 1d". That may take a while to generate results. I figure 1 hour should be enough time to analyze in the log. These have helped a lot. They basically solve the problem of tracking which Macs are having MDM issues. I created two smart groups, one called "MDM Communication Bad" and another called "MDM Communication Good". If a Mac fails any of the three tests, it is "bad". To be "good", it must pass all three tests. I am a Jamf Now customer. I ran these through CodeRunner on my personal MacBook Pro. They work the same as with a Mac enrolled in Jamf Pro. I hope these help others with MDM issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-03-2024 07:39 AM
This looks like something I'd like to add to my Jamf Pro instance so I can be proactive in detecting MDM communication issues with my fleet. I created the EA's and the two smart groups. Is there a particular value that would be used in those smart groups for reporting?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-12-2024 09:50 AM
re-enroll machine in jamf sudo jamf removeframework , noway around
I have 15 machines with couple of configuration profiles stuck on pending very annoying.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-03-2024 11:00 AM
I made some changes to the EAs that I posted earlier this year to make using them with smart groups easier. They're posted below:
MDM identity certificate check
#!/bin/bash
theIDs=$(security find-identity -v | awk '{print $3}' | tr -d '"' | grep -E '^[A-Za-z0-9]{8}-[A-Za-z0-9]{4}-[A-Za-z0-9]{4}-[A-Za-z0-9]{4}-[A-Za-z0-9]{12}$')
echo $theIDs
if [ -z "$theIDs" ]; then
echo "<result>"Failed"</result>"
exit 1
else
echo "At least one keychain identity found on this system, proceeding..."
fi
for i in $theIDs; do
info=$(security find-certificate -c "$i" | grep issu | awk '{print $3, $4, $5, $6, $7}' | tr -d '"')
echo $info
if [[ $info == *"BUILT-IN CERTIFICATE AUTHORITY"* ]]; then
echo "found you!"
expiry=$(security find-certificate -c "$i" -p | openssl x509 -noout -enddate | cut -f2 -d"=")
echo "<result>"Success"</result>"
fi
done
exit 1
MDM APNS certificate check
#!/bin/bash
APNS_certificate=`/usr/sbin/system_profiler SPConfigurationProfileDataType | awk '/Topic/{ print $NF }' | sed 's/[";]//g'`
if [[ "$APNS_certificate" = "" ]]; then
echo "<result>"Bad"</result>"
else
echo "<result>"Good"</result>"
fi
MDM client communication
#!/bin/bash
result=$(log show --style compact --predicate '(process CONTAINS "mdmclient")' --last 1h | grep "Unable to create MDM identity")
if [[ $result == '' ]]
then
echo "<result>"Good"</result>"
else
echo "<result>"Bad"</result>"
fiI used these to create a smart group called "MDM Communication Bad". If any of the criteria using these EAs is not a positive (good) result, then the Mac will be added to this group. I also added the MDM enrollment status found in a Mac's Jamf inventory record. I hope this helps. In most cases, a re-enroll of a Mac in JAMF Pro is what is needed. Sometimes, I have had to also run a "jamf removeFramework" command first. A Mac that is in Apple Business Manager can be re-enrolled by running "sudo profiles renew -type enrollment".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-17-2024 09:08 AM - edited 09-17-2024 09:09 AM
If the "MDM is broken" its it enough to run sudo profiles renew -type enrollment to get the mac able to get profiles again?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-18-2024 02:53 AM
That command will work as long as the Mac is in Apple Business Manager. If it's not, this command will enroll the Mac:
sudo jamf enroll -prompt
You will be prompted for a username and password of a Jamf Pro user who has enrollment privileges. Sometimes I have had to run sudo jamf removeFramework to remove the Jamf agent and keychain items. If the Mac enrolled through automated device enrollment (PreStage), and your PreStage is set to not allow MDM profile removal, this won't remove the MDM profile. That's OK. Running the profiles renew -type enrollment command will re-enroll.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-18-2024 06:41 AM
Thanks. Yeah had the user run sudo profiles renew -type enrollment and profiles Immediately went through. I wish apple/jamf would fix this issue. It continues to randomly happen on systems here for the last few years and cant seem to figure out why. One Jamf tech suggested that if a computer was not assigned to a prestage after enrollment that they have seen this issue randomly happen on them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-19-2024 08:43 AM
In our case, it think our network policies and likely one or more of the many agents (far too many!) that we install on the Macs is the culprit. Recently I had an inventory problem caused by an extension attribute that was running a command for Symantec Management. The command was causing the recon process to hang. This crappy software from Symantec was at fault! We need a serious reassessment of what is actually needed instead of just dumping all this crapware on Macs the same way we do with Windows PCs. Jamf Pro and Apple's MDM standard are actually very solid. I don't remember having this much trouble when I have managed Jamf Pro servers without all the crapware.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-27-2024 08:06 AM
Howie,
Thanks for updating and posting the EAs. I will be using them to try to track down and resolve all the devices that have stuck 'pending' profiles.
I have identified all of the computers not enrolled via a PreStage. Is it worth the time to go to ASM and assign any identified computers to JSS and then to their appropriate PreStage before running running "sudo profiles renew -type enrollment"?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-27-2024 10:10 AM
If the computers are not assigned to your Jamf Pro server that command won't do anything. Once you have them assigned, make sure that they show up in scope for the PreStage. It can take about 15-20 minutes for Apple and Jamf Pro to sync with each other. If these computers are not in ASM, they can be added but to do so it requires that the Mac be in the new setup state.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-27-2024 10:15 AM
Thanks for the confirmation -- that was my thinking. I'm in the process of assigning them now. Most of these are older systems that were enrolled in the first few years we first brought Jamf online and implemented User Initiated Enrollments vs. PreStage so as not have to wipe devices to get them onboarded.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 09-27-2024 10:19 AM
We restrict user-initiated enrollments. Only a few people are able to do them. I wrote documentation for my team showing them the procedure for adding a Mac to Apple Business Manager and how to assign them to our Jamf Pro server after they are added.